I/UCRC Executive Summary
advertisement
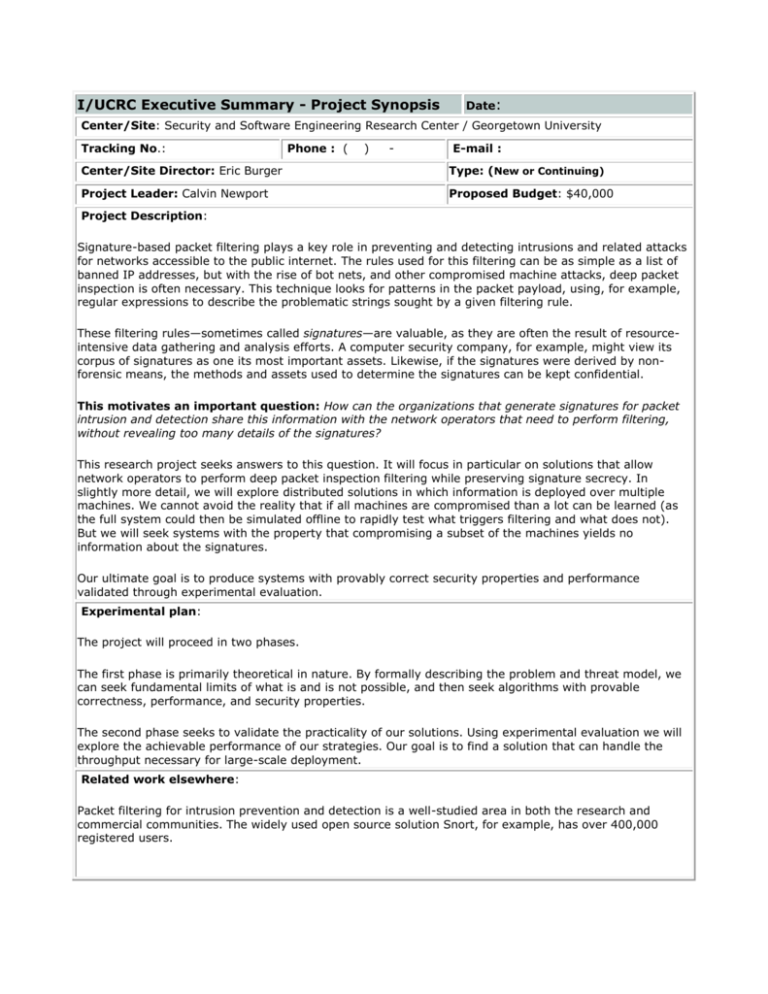
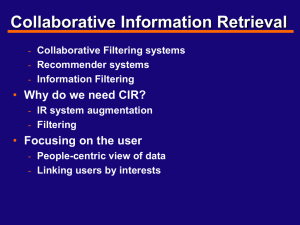
I/UCRC Executive Summary - Project Synopsis Date: Center/Site: Security and Software Engineering Research Center / Georgetown University Tracking No.: Phone : ( ) - E-mail : Center/Site Director: Eric Burger Type: (New or Continuing) Project Leader: Calvin Newport Proposed Budget: $40,000 Project Description: Signature-based packet filtering plays a key role in preventing and detecting intrusions and related attacks for networks accessible to the public internet. The rules used for this filtering can be as simple as a list of banned IP addresses, but with the rise of bot nets, and other compromised machine attacks, deep packet inspection is often necessary. This technique looks for patterns in the packet payload, using, for example, regular expressions to describe the problematic strings sought by a given filtering rule. These filtering rules—sometimes called signatures—are valuable, as they are often the result of resourceintensive data gathering and analysis efforts. A computer security company, for example, might view its corpus of signatures as one its most important assets. Likewise, if the signatures were derived by nonforensic means, the methods and assets used to determine the signatures can be kept confidential. This motivates an important question: How can the organizations that generate signatures for packet intrusion and detection share this information with the network operators that need to perform filtering, without revealing too many details of the signatures? This research project seeks answers to this question. It will focus in particular on solutions that allow network operators to perform deep packet inspection filtering while preserving signature secrecy. In slightly more detail, we will explore distributed solutions in which information is deployed over multiple machines. We cannot avoid the reality that if all machines are compromised than a lot can be learned (as the full system could then be simulated offline to rapidly test what triggers filtering and what does not). But we will seek systems with the property that compromising a subset of the machines yields no information about the signatures. Our ultimate goal is to produce systems with provably correct security properties and performance validated through experimental evaluation. Experimental plan: The project will proceed in two phases. The first phase is primarily theoretical in nature. By formally describing the problem and threat model, we can seek fundamental limits of what is and is not possible, and then seek algorithms with provable correctness, performance, and security properties. The second phase seeks to validate the practicality of our solutions. Using experimental evaluation we will explore the achievable performance of our strategies. Our goal is to find a solution that can handle the throughput necessary for large-scale deployment. Related work elsewhere: Packet filtering for intrusion prevention and detection is a well-studied area in both the research and commercial communities. The widely used open source solution Snort, for example, has over 400,000 registered users. How this project is different: To the best of our knowledge, what is new about this project is that: (a) our goal is to maintain the secrecy of signatures while a third-party performs filtering; and (b) that we seek solutions with practical performance even when focused on deep packet inspection. Milestones for the current proposed year: The first milestone is a formal model of our system and threats. We will motivate the details of this model by arguing that they adequately capture the key properties of real networks. The second milestone is a series of results on the fundamental power of this model. That is, proofs of what is and is not possible. Such impossibility results will help understand what solutions to seek, and whether new features to the model, as can be delivered through the introduction of new hardware, for example, are needed. The third milestone would be the initial system proposals with provable correctness, performance, and security properties. Beyond the current year, we would turn our attention to honing the complexity of our solutions then performing experimental evaluation. Deliverables for the current proposed year: For the first year, the main set of deliverable would be our initial algorithms with corresponding proofs. How the project may be transformative and/or benefit society: Packet filtering is an important defense against network attacks. The ability to more widely deploy signatures (because organizations need not fear revealing the intellectual property contained in their filtering rules) will lead to better network performance and security for everyone. Research areas of expertise needed for project success: This project will require a mix of experience with network security, cryptography, and distributed algorithm theory. Potential Member Company Benefits: This technology can lead to new products and markets, as well as improve the performance of existing products. Progress to Date: To date, we have explored existing packet filtering solutions and begun exploring the difficulties of secrecypreserving deep packet inspection, and the types of strategies that might yield solutions. Estimated Start Date: Estimated Knowledge Transfer Date: The Executive Summary is used by corporate stakeholders in evaluating the value of their leveraged investment in the center and its projects. It also enables stakeholders to discuss and decide on the projects that provide value to their respective organizations. Ideally, the tool is completed and shared in advance of IAB meetings to help enable rational decision making.