transmission f
advertisement
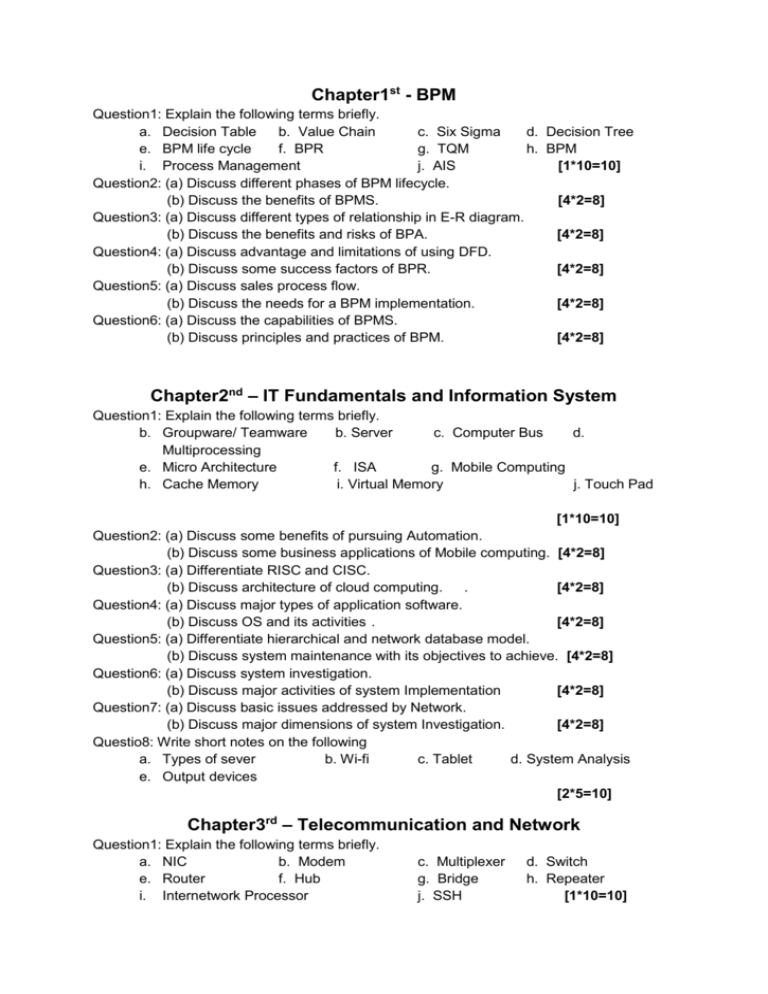
Chapter1st - BPM Question1: Explain the following terms briefly. a. Decision Table b. Value Chain c. Six Sigma d. Decision Tree e. BPM life cycle f. BPR g. TQM h. BPM i. Process Management j. AIS [1*10=10] Question2: (a) Discuss different phases of BPM lifecycle. (b) Discuss the benefits of BPMS. [4*2=8] Question3: (a) Discuss different types of relationship in E-R diagram. (b) Discuss the benefits and risks of BPA. [4*2=8] Question4: (a) Discuss advantage and limitations of using DFD. (b) Discuss some success factors of BPR. [4*2=8] Question5: (a) Discuss sales process flow. (b) Discuss the needs for a BPM implementation. [4*2=8] Question6: (a) Discuss the capabilities of BPMS. (b) Discuss principles and practices of BPM. [4*2=8] Chapter2nd – IT Fundamentals and Information System Question1: Explain the following terms briefly. b. Groupware/ Teamware b. Server c. Computer Bus d. Multiprocessing e. Micro Architecture f. ISA g. Mobile Computing h. Cache Memory i. Virtual Memory j. Touch Pad [1*10=10] Question2: (a) Discuss some benefits of pursuing Automation. (b) Discuss some business applications of Mobile computing. [4*2=8] Question3: (a) Differentiate RISC and CISC. (b) Discuss architecture of cloud computing. . [4*2=8] Question4: (a) Discuss major types of application software. (b) Discuss OS and its activities . [4*2=8] Question5: (a) Differentiate hierarchical and network database model. (b) Discuss system maintenance with its objectives to achieve. [4*2=8] Question6: (a) Discuss system investigation. (b) Discuss major activities of system Implementation [4*2=8] Question7: (a) Discuss basic issues addressed by Network. (b) Discuss major dimensions of system Investigation. [4*2=8] Questio8: Write short notes on the following a. Types of sever b. Wi-fi c. Tablet d. System Analysis e. Output devices [2*5=10] Chapter3rd – Telecommunication and Network Question1: Explain the following terms briefly. a. NIC b. Modem e. Router f. Hub i. Internetwork Processor c. Multiplexer g. Bridge j. SSH d. Switch h. Repeater [1*10=10] Question2: (a) Discuss different layers of OSI Model. (b) What are the popular ways to connect to an ISP? [4*2=8] Question3: (a) Discuss different types of risks involved in E-Commerce. (b) Discuss the benefits E-Commerce . [4*2=8] Question4: (a) What are the various ways in which users can use internet in effective manner? (b) What are the tools and technologies are now available to protect information against intrusion, misuse and compromise?. [4*2=8] Question5: (a) Write advantages and disadvantages of star Topology. (b) Discuss the characteristics of Client Server architecture [4*2=8] Question6: (a) Discuss the Network Management.. (b) Discuss stages of Security Programs [4*2=8] Question7: Differentiate the followings: a. C2C and C2B b. HID AND NID c. Synchronous and Asynchronous Transmission d. Circuit and Message Switching e. Serial and Parallel Transmission f. Centralized and Decentralized Computing g. Guided and Unguided Media h. Client server and peer-to-peer Networking i. Public and Private Network j. Two Tier and Three Tier Architecture [3*10=30] Chapter4th- BIS Question1: Explain the following terms briefly. c. System b. Info. System f. Dashboard f. EIS i. Strategic Level Users c. BIS d. TPS g. KMS h. Data Mining j. Knowledge Level System [1*10=10] Question2: (a) Discuss roles of IS in business. (b) Discuss capabilities of IS. Question3: (a) Discuss ACID test for TPS. (b) Discuss the attributes of TPS . Question4: (a) Differentiate Explicit and Tacit Knowledge. (b) Discuss the components of EIS. Question5: (a) Discuss the components of SCM. (b) Discuss the key components of ES. Question6: (a) Discuss the smart cards. (b) Discuss access control functions. [4*2=8] [4*2=8] [4*2=8] [4*2=8] [4*2=8] Chapter5th - BPA Question1: Explain the following terms briefly. a. Business Application b. BPA c. Controls in BPA d. Grid Computing i. Application Controls f. Network Virtualization g. Edit Checks i. Exception Report i. Validation Controls j. Limit Checks [1*10=10] Question2: (a) Discuss some applications that help entity to achieve BPA. (b) Discuss basis on which business applications can be categorized. [4*2=8] Question3: (a) Differentiate Manual information processing cycle and Computerized Information cycle. (b) Discuss major control objectives. . [4*2=8] Question4: (a) Discuss characteristics of cloud computing.. (b) Discuss Boundary Controls . [4*2=8] Question5: (a) Discuss advantages of cloud computing. (b) Discuss disadvantages of cloud computing. [4*2=8] Question6: (a) Discuss the need of grid computing. (b) Discuss major applications of virtualization [4*2=8]