Literature Review: Team 21 Low Cost Corneal Identifier Table of
advertisement

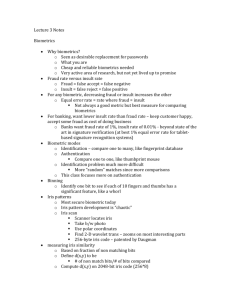
Literature Review: Team 21 Low Cost Corneal Identifier Page | 1 Table of Contents: Introduction…………………………………………………..…………….3 History………………………………………………............................3 Techniques……………………………………………………..……………3 Typical Statistics………………………………………………………..…6 Current System Capabilities………………………………………….6 Corneal Mapping………………………………………………..………..8 Laser and LED Safety and Standards………………………..……9 Design Obstacles and Considerations……………………….….11 Current Biometric Algorithms……………………………………...14 Summary……………………………………………………………….…….16 References……………..………………………………………..……….…17 Page | 2 Introduction: The corneal identifier is a new biometric technique that will differentiate individuals for identification purposes. This literature review will discuss the history of biometrics and techniques that have been and are currently in use today. It will then delve into the statistics of biometrics, corneal mapping, and current capabilities of biometric systems. Moving onto the safety aspects of this new method the topics of laser and LED standards and safety will be discussed followed by the sections covering problems and complications including corneal disease and corrective lenses. Finally algorithms, loopholes, and levels of security will show how to compensate for false positive identifications. History Biometrics is defined as “the measurement and analysis of unique physical or behavioral characteristics (as fingerprint or voice patterns) especially as a means of verifying personal identity” [1]. It comes from the Greek words “bio” meaning life and “metric” meaning to measure. From the earliest civilizations there has always been a need to tell one person from another. As time has progressed people have developed more sophisticated ways of identifying people. The oldest method of biometrics used was facial recognition but as populations became larger and people could travel longer distances this became a less accurate way of identifying individuals. Two examples of past biometric techniques follow: In early Egyptian history, traders were identified by their physical descriptors to differentiate between trusted traders of known reputation and previous successful transactions, and those new to the market [2]. Joao de Barros, a Spanish explorer and writer, wrote that early Chinese merchants used fingerprints to settle business transactions. Chinese parents also used fingerprints and footprints to differentiate children from one another [2]. These techniques were used until the mid-1800s, when Azizul Haque developed a new system of indexing fingerprints for Edward Henry, Inspector General of Police, and Bengal, India. This system, called the Henry System, and variations of it are still in use for classifying fingerprints [3]. Since the invention of the microchip, biometrics identification has progressed very rapidly. The use of microchips and programming languages have made biometrics a more effective and efficient way of identifying different people. Techniques Page | 3 As microchip technology has advanced, certain biometric techniques have become more common. The following is a list of several modern day biometric techniques: Fingerprint Recognition Palm Print Recognition Hand Geometry Vascular Pattern Recognition Iris Recognition Retinal Recognition Face Recognition Fingerprint recognition is the most common technique used today. Almost everyone has a unique fingerprint. A fingerprint is made of a series of ridges and gullies on the surface of the finger as seen in Figure 1. The ridges appear as the dark lines, and gullies appear as white lines. The uniqueness of a fingerprint can be determined by the pattern of ridges and gullies as well as the minutiae points. Minutiae points are where ridges end or where two ridges split or join together. Figure 1 Based on those specific points and the flow of ridges, identification can be made. There are a few different sensors in use today that capture a digitized image. An optical sensor takes an image of the fingerprint and is the most common sensor. The capacitive sensor determines each pixel value based on the capacitance measured. When there is a gully there is less capacitance as opposed to when there is a ridge and capacitance is high. Thermal scanners measure the difference in temperature over time of a finger swiped across the sensor. Ultrasound sensors employ prisms that can detect the change in light reflected back to the sensor from the fingerprint [4]. Page | 4 Palm print recognition is basically an extension of fingerprint recognition. The main difference is that the entire palm is also scanned or digitized. A correlation match is then found which is simply lining up the two different palm prints and subtracting one from the other to see if they match. Hand geometry devices measure and record the hands actual dimensions; the length, width, thickness, and surface area. Since a person’s hand shape and dimension is not unique this is often used with another technique for identification. The system captures an image of the back of a hand set in place by five pegs while a mirror creates a silhouette of the hand. Once this is done the measurements are recorded and a template is created and put into the system. The template can then be used to match the hand geometry when the system is used again [5]. Vascular pattern recognition is a method that uses near infrared rays generated from a bank of LED’s to penetrate a person’s hand while a Charged Coupled Device (CCD) camera takes an image of the hand. The image shows the difference in light absorbance between blood vessels and other tissues. The blood vessels produce a unique vascular pattern, which is then stored as a template. The template can then be used to match their vascular pattern in future uses of the system [5]. Iris recognition is the process of identifying a person by the unique pattern of their iris. The first step is taking a high-resolution image of the eye typically illuminated with infrared light. The image is then encoded with mathematical algorithms called Iris Code that is then used to form a unique code for the individual and stored in a database. Their code then has to be matched by a future scan for verification of identity [6]. Retinal scanners are used to map the unique patterns of a person’s retina. The blood vessels in the retina absorb more light than the other tissues of the retina and can be easily recognized with the infrared light. Because retinal blood vessels are more absorbent of infrared light than the rest of the eye, the amount of reflection varies during the scan. The pattern is converted to a template and stored. The template can then be used to match retinal scans when the system is used [7]. Face recognition employs digital images of faces. Every persons face has distinguishable landmarks such as distance between eyes, width of nose, length of jaw line, shape of cheekbones, and depth of eye sockets. By taking all those measurements and types into consideration, a mathematical algorithm is used to create a unique code for every face. That code then has to be matched in order to confirm identity. Page | 5 All of these techniques rely on two main things; a microchip and a program to run the microchip. Two manufacturers of microchips currently are Sun Microsystems and Microchip. Both of these companies make Peripheral Interface Controllers (PIC). These are used for several applications and in most biometrics systems at least one is used. A programming language is needed In order to program a PIC. One of the most common programming languages used today is C++. It is readily available and can be run in a simulation before it is actually programmed into a PIC. Doing this allows the programmer to find bugs in the code and correct them. Once a simulation can be run without incident it can be downloaded onto the PIC and tested with the actual system. When all bugs are fixed and the system is able to run correctly the biometric system can then become a stand-alone system, which makes it more secure from being defeated. This is the main purpose of any biometric system; to be able to identify different people without someone being able to deceive the main system and allow them access beyond the biometric system. Typical Statistics Facial recognition currently has the highest reliability with regards to identifying uniqueness [8]. Although facial recognition has a false match rate (FMR) of one in one thousand, which is relatively high when compared to other biometric systems [9]. The FMR is defined as the fraction of compared biometric samples from different users exceeding the threshold (h), where h is unique to each system [3, pg.8]. Typical retina biometric systems have an error rate around one in ten million compared to the typical fingerprint scan error being as high as one in five hundred [10]. The FMR for Iris recognition ranges anywhere from one in one million to zero (theorized at 1 in 5e15) that vary according to HD criterion constants 0.317 to 0.220 respectively. These statistics are based on single-eye iris recognition with two hundred billion comparisons, using the UAE database [11]. Using two eyes drastically improves the above-mentioned results [9]. These results are comparable to leading single finger fingerprint matching systems. Stephen Mason filed an application with WIPO (World Intellectual Property Organization) in 2005 where he wrote, “The most optimistic of claims for iris recognition systems are around 94 to 99 percent accuracy - so for every 100 scans there will be at least one false match. This poses a significant problem for managing large databases where for example in a database of 60 million each person's scan will match 600,000 records in the database making it impossible to prevent someone claiming multiple identities “[8] . Current System Capabilities Page | 6 Panasonic advertises High Precision, Quick Recognition, Up to 5,000 Users, and a Flexible interface for their Iris Recognition Camera System. Panasonic’s unit is the BM-ET330 and its major design qualities include: • Built-in (COTS) off the Shelf Support for 13.56 MHz HID iClass(tm) Readers • High Speed Processor - Recognition in 0.8 seconds • 1,000 Local User Cache, 5,025 User Base Server Capacity • Wiegand Input and Output - supports 125 KHz Proximity Cards • Encrypted TCP/IP Interface • SDK Availability for Custom Integration • Enhanced RS-485 Interface • Integrated Analog CCTV Camera - Connect to DVR • Additional Language Support - Custom Audio prompts • Built-in Real-time Clock for Time & Attendance Applications • Supported by a Global Network of Access Control Manufacturers & Solution Providers • Tamper Proof Design Panasonic’s BM-ET330 Figure 2 Page | 7 Figure 2 shows the small wall mounted unit [12]. Panasonic also allows the user to store the biometric information on a card and take it with them. This insures further assurance for those with concerns of privacy. If the user allows their data to be stored in a database, it is stored in 3DES-encrypted files and cannot be used to reconstruct images of the iris. Pleasant voice prompts and visual aids help guide the user through enrollment and daily use. This includes telling the user where to look, distance, and help with alignment [13]. This particular Panasonic system retails for over four thousand dollars and is priced to be competitive with other similar systems. Corneal Mapping Corneal topographers that are commonly used in clinical practices employ a Placido target. The targets consist of alternating concentric rings (black, clear, black, etc.) with a light source behind the rings used to project an image onto the cornea. This image is reflected back to a detector that records the reflected image. The tear film on the eye makes the cornea an ideal surface for gathering data. This process is almost non-contact (the patient touches the chin rest and forehead strap) and is completely painless. Software is then used to create a topographic mapping of the cornea. Two corneal topographers are shown in figure 3 and some possible corneal mappings that would be created are shown in figure 4. Corneal Topographers [14] Figure 3 Page | 8 Corneal topographies [15] Figure 4 Once the cornea has been analyzed and mapped the resulting data is used for various optical applications, including but not limited to diagnosis and treatment, Lasik eye surgery, biometrics, and contact lens fitting [16]. Laser and LED Safety: Safety Standards and Associated Terms and Equations. With the advent of lasers and LED’s, safety standards have inevitably been developed and implemented in order to protect manufacturers, users, and even bystanders. Since the hazards to humans can be quite significant, standards have been mandated on international, national, state, and organizational levels. Before jumping into the current safety standards, some terms and equations used to describe such safety measures and values should be understood, as well as some fundamentals of light properties. When considering light and the hazards to the eye and skin involved with light emitting devices, three main factors are used to determine the safe or allowable exposure levels; exposure time, irradiance, and beam size [17]. Exposure time is the duration of continuous exposure to a light source. Exposure time can be controlled by the source configuration, such as having a continuous wave or a pulsed wave system setup. Accumulation of damaging radiation effects such as heat can sometimes be avoided by having a pulsating source so that the heat has time to dissipate [18]. Page | 9 Irradiance is a measure of the incident power of electromagnetic radiation (light) on a surface and is expressed in the SI unit of Watts per square meter. A common misconception is that irradiance is the same as intensity (power per unit solid angle), which is interchangeable with irradiance in some fields of physics. Beam size is the diameter of the beam that contacts the surface and is mainly a factor when considering hazards involving lasers. A larger beam diameter results in more light radiation exposure and thereby increases the possibility of damage to the exposed surface. This may seem counterintuitive when considering LED’s since they tend to have a large beam size, but the irradiance (W/m^2) must also be factored in with regard to beam diameter. Most LED’s lack a concentrated irradiance at low power therefore beam width can be a negligible parameter when evaluating potential safety hazards. Standards that are in place and frequently referenced are the ANSI (American National Standards Institute) Z136 series, and the IEC (International Electrotechnical Commission) 60825. According to OSHA (Occupational Safety and Health Administration), adherence to ANSI standards is voluntary unless noted otherwise by an organization. The United States Department of Energy requires all associated bodies to comply with ANSI Z136.1 standard [10]. Although ANSI is not a required standard to follow, many other standards and organizational regulations are developed using the Z136 series. The Food and Drug Administration (FDA) govern US standards. They cover regulations on manufacturers under the Laser Product Performance Standard and classify lasers under the ANSI laser classification system. Some states have their own regulatory bodies that determine standards in addition to those set forth by the FDA such as the Illinois Department of Nuclear Energy [4]. Maximum Permissible Exposure (MPE) is an important value determined by equations set forth in the ANSI Z136 series that come into play when determining safe exposure levels to light. MPE values will vary depending on the exposure time and the spectrum the source operates in (λ). Appropriate values can be found in the ANSI Z136.1 table 5a. Correction factors are listed for special cases to increase or decrease the MPE value depending on the evaluated system in the ANSI Z136.1 table 6 with a few examples as follows: CA. Correction factor which increases the MPE in the near infrared (IR-A) spectral band (0.7-1.4 μm) based upon reduced absorption properties of melanin pigment granules found in the skin and in the retinal pigment epithelium. CB. Correction factor, which increases the MPE in the red end of the visible spectrum (0.45-0.60 μm), because of greatly reduced photochemical hazards. Page | 10 CC. Correction factor, which increases the MPE for ocular exposure because of preretinalabsorption of radiant energy in the spectral region between 1.15 and 1.40 μm. CE. Correction factor used for calculating the extended source MPE for the eye from the pointsource MPE, when the laser source subtends a visual angle exceeding αmin. CP. Correction factor, which reduces the MPE for repetitive-pulse exposure of the eye.[20] To more clearly demonstrate the use of correction factors, a sample calculation for MPE involving a source operating in the NIR wavelengths (830 nm in this case) and a C A value (not all associated parameters listed for brevity) derived from ANSI Z136.1 tables is shown below. MPEN(0.83) = CA(0.83) mW cm-2 A cm2 = 1.82 mW cm-2 0.3848 cm2 = 0.70 mW MPE levels can also differ upon application such as direct laser exposure to skin or extended source ocular exposure. Separate tables regarding situational variances can be found in the ANSI Z136.1 section. Wavelengths of the light source are required information when considering maximum exposure duration. For example, maximum exposure durations for wavelengths greater than 0.7 micrometers (infrared range) are much less than for those of shorter wavelengths due to the potential hazards involved (30,000 sec drop to 100 sec for class 1 and 1M lasers).[20] Note that the energy (E) of a photon is inversely proportional to the wavelength via the quantum mechanical formula, E = hc/ λ, thereby giving shorter wavelengths higher energy properties. This follows with the shorter maximum exposure durations for smaller λ. Wavelengths in the visible light spectrums are approximately as listed in figure 5 based on color. Color Red Orange Yellow Green Blue Violet Wavelength (λ in nm) 780 – 622 622 – 597 597 – 577 577 – 492 492 – 455 455 – 390 Figure 5 Frequency (THz) 384 – 482 482 – 503 503 – 520 520 – 610 610 – 659 659 – 769 In addition to the visible wavelengths, some lasers and LED’s operate in frequencies outside of this range and the hazards involved with those must also be considered such as the Ultraviolet (UV), Near Infrared (NIR), and Infrared (IR) ranges. The associated wavelengths are listed in figure 6. Page | 11 Name Designation Ultraviolet Infrared Near Infrared Wavelength (λ in nm) 10 – 400 400 – 700 800 – 2500 Figure 6 Most commercial lasers used are red lasers that operate with a wavelength of approximately 630 – 635 nanometers. LED wavelength is more varied since they are manufactured in every color including the UV, IR, and NIR spectrums. Design Problems and Considerations Biometric devices that rely on the eye as a biometric means pose certain problems. Glasses and contact lenses can alter the image that the capture device sees. Iris scan biometric devices sometimes have a hard time identifying the iris through contact lenses. Most devices have no trouble identifying an iris through glasses. Corneal topography cannot be scanned while a subject is wearing glasses [21]. Contact lenses pose a different set of problems when corneal topography is concerned. According to the Vision Council of America (2006), 19% of the population of the United States wears contact lenses part of the time. Over a period contacts can alter the shape of the cornea by causing divots from pressure points on the surface of the cornea. These deformations are usually not permanent. Upon removing the contact lens the cornea will relax to its normal state. During preparation for Lasik surgery the contacts lenses cannot be worn for 10 days prior to the pre-op topological scan [22]. A topological scan can be done of contact lenses while in place. Topographic scans of soft contacts in place are used to evaluate the condition of used contacts. Deposits on the lens as well as deformation in shape of the lens can be detected using videokeratoscopy. Contact lenses can be assessed for irregular central patterns, abnormal central steepening, abnormal central flattening, and abnormal asymmetry. All of these parameters can be easily determined using a common videokeratoscope. Contact lenses last for a varying length of time depending on how the individual takes care of them. New contacts that have been poorly taken care of can appear much older than they are [23]. Contact lenses have a set of parameters that are unique to the person’s eye and prescription. Some of the parameters describing contact lenses are radius of curvature, back vertex power, lens diameter, and lens thickness. From a biometric identification standpoint, uniqueness can stem from the contacts ability to form to the shape of the individuals eye, yet be a slight degree different from the naked eye and the basic parameters of a contact lens prescription due to the inherent modifications to the reflective surface of the eye such as an Page | 12 increased radius of curvature (lens thickness considered) and lesser degree of tear fluid uniformly coating the cornea. A corneal topographer can easily determine the lens radius of curvature and the lens diameter. The radius of curvature is only constant in hard contact lenses while soft lenses take on a different shape when in situation. Soft contacts diameter can vary in size slightly according to the temperature [24]. Other possible problems when implementing a corneal topography based authentication system can include any disease that quickly alters the shape of the cornea. Since correct identification of an individual relies on a cornea that retains its shape over a period of time. Some diseases and dystrophies that are known to alter the shape of the cornea are corneal infections, Fuch’s dystrophy, keratoconus, lattice dystrophy, Map-Dot-Fingerprint dystrophy, ocular herpes, pterygium, and Stevens - Johnson syndrome. Corneal infections can alter the shape of the cornea’s surface. Corneal infections can be caused from a range of sources. These can include getting a foreign object in the eye or improperly cared for contact lenses. An untreated infection can lead to permanent corneal erosion. Corneal scaring can result from untreated infections [25]. Fuchs’ Dystrophy can alter the shape of the cornea. Fuchs’ Dystrophy is a disorder in which the endothelial cells gradually deteriorate over time. Endothelial cells are those located at the outer most regions of the cornea and serve to absorb liquid and nutrients for distribution to the rest of the cornea. As more cells deteriorate the endothelium becomes less efficient at moving fluid out of the stroma, an inner layer of the cornea composed primarily of water. Epithelial swelling causes the cornea’s curvature to change as well as producing tiny blisters on the cornea [25]. Keratoconus is the progressive thinning of the cornea. As a result of there being less corneal cells the center of the cornea begins to bulge. Keratoconus is the most common dystrophy in the US affecting about one in every 2000 Americans. In some cases corneal bulging will stabilize over a period of time. In other cases the cornea gradually deformed more as the dystrophy progresses [25]. Lattice Dystrophy occurs when the eye develops protein deposits that resemble a lattice structure. In some cases erosion of the cornea can occur, permanently altering the corneal shape. A similar disease, Map-Dot-Fingerprint Dystrophy, alters the curvature of the cornea due to erosion [25]. Map-Dot-Fingerprint dystrophy occurs when the epithelium’s membrane develops abnormally. This disease causes chronic epithelial erosions on the cornea [25]. Page | 13 Pterygium is a disease that causes triangular shaped growths on the cornea. In some cases the pterygia grow slowly while in others the pterygia stop growing completely [25]. Ocular herpes can cause inflammation of the cornea, hence distorting its shape. Stevens-Johnson syndrome can cause serious corneal erosions and blisters [25]. Corneal identification relies on an individual to keep their gaze in a constant direction. A relatively stable eye results in a more accurate topological scan of the cornea [26]. Disorders such as Nystagmus and amblyopia make for difficult and inaccurate videokeratoscopy. Nystagmus is an involuntary rhythmic shaking or wobbling of the eyes [27]. Amblyopia is commonly referred to as “lazy eye” and results from a neurological disorder [28]. Current methods for dealing with such disorders are high speed-speed videokeratoscopy and a method of measuring tilt, displacement, and cyclotorsion of multiple videokeratographs to reconstruct an accurate representation. A method for dealing with Nystagmus is using high-speed videokeratoscopy. A typical videokeratoscope samples data at a frequency of 1Hz, while a high speed system can sample data at a rate of up to 50Hz. In using a high speed system the eye need only be stable for a short period of time. Many samples can be taken to determine which sample provides an accurate representation. With high speed videokeratography a range finder is essential to verify position [26]. The second method for compensating for an unstable eye is measuring tilt of the eye, displacement of the cornea from a central point, and cyclotorsion which is the rotation of the eye about its visual axis. Multiple samples are taken from the same cornea and then adjusted as per measurements taken. Samples are adjusted to reflect the average sample taken. This method has been shown to reduce the root mean square error by 24.6% compared to single samples [29]. Current Biometric Algorithms: Biometric algorithms exist to interpret data from a unique source and compare it against a template. This data generally includes input from various sensors, biometric samples, templates, or scores. This information that is collected during the enrollment, verification, or identification process is analyzed and an algorithm performs computations that determine whether the biometric sample is a match to a particular template. Biometric algorithms solve these computations with a finite sequence of instructions and can be implemented with various computer languages such as C/C++, C#, Java, and JavaScript [30]. Current algorithms in the biometric field can vary greatly and they can also affect a biometric system’s efficiency and accuracy. For example, several different algorithms may Page | 14 perform the same operation in more or less time with different sets of instructions and space requirements. Some fingerprint recognition systems implement a k-nearest neighbor algorithm along with several other extraction and enhancement algorithms to enhance performance [31]. Many iris recognition systems deploy the Daugmanalgorithm that incorporates an integrodifferential operator to recognize both the pupil and iris outline [32]. This algorithm is claimed to be highly efficient and has been rigorously tested and proven. This algorithm was compared to more than two million samples and produced no false matches [33]. Just as different algorithms can provide different results with their own set of strengths and weaknesses, so can different biometric technologies. Biometrics are based upon sensitive personal information and as a result that information must be safeguarded. Unfortunately, this information can present itself as a target for attacks. False biometric information can be intentionally submitted to defeat the system. Repetitive, hill climbing, or signal jamming attacks can also be exercised at module interfaces. In addition, weaknesses in the algorithms can be exploited to grant access to the system. Finally, attacks on the template database can provide attackers with the necessary information to create a biometric sample, such as a fingerprint [34]. Attacks on biometric systems can have disastrous results and entire systems can become inoperable. Stored data templates can be compromised or destroyed. Loss of privacy is another concern as biometric information can be used multiple times and individuals can be tracked across different databases [34]. Preventative measures can be implemented to guard against misuse, however. Liveness detection is an acquisition technique in which the system verifies if the sample is from a valid, living user. This technique can help protect against spoofing attacks. Living tissue has distinct spectrographic signatures as well as absorption, which can be used as a countermeasure. For optical biometric systems, reflections on the four optical surfaces of the human eye can be tracked to ensure legitimacy. Biometric systems can also search for involuntary responses, such as pupil dilation, or voluntary responses such as eye movements on command. One iris recognition system can detect a fake iris pattern printed on a contact lens by a 2D Fourier spectrum as shown in Figure 1 [35]. Natural Iris Page | 15 Fake Iris 2D Fourier spectrum of natural Iris 2D Fourier spectrum of fake Iris Figure 7 In addition to liveness detection, multiple biometric systems are used in conjunction with each other to provide a more robust system with an increased level of security. For instance, a system can implement a retinal scan along with a hand scan for increased sensitivity. Quite often, a unique identifier is used as well. A unique identifier is a code or number that is associated exclusively with a specific person, such as a pin number [36]. Conclusion: Biometric identification has been realized since the civilization of man and throughout time the complexity of systems has increased. There are a number of biometric systems available today that utilize different methods of identification. Biometric identification systems lend themselves to attack and each method has its own vulnerabilities. Outside attackers have manipulated samples, database templates, and computer algorithms to gain unauthorized access. Certain techniques can be utilized to counter these attacks but the most effective method is to use a combination of biometric systems. Fingerprint recognition is by far the most common biometric identification technique. With the advent of today’s technology, however, corneal topology is fast becoming another reliable identification technique. Every person’s cornea has a unique contour and as a result, corneal topology is emerging in the biometric security market. Presently, there is only one biometric system using corneal topology as an identifier. Current systems used in clinical applications employ different methods to map the surface of the cornea with the most popular being a Placido target. Page | 16 There are several corneal diseases as well as corrective lenses that may hamper the effectiveness of such a corneal biometric system. Because of this, different considerations need to be made to address these anomalies. Page | 17 References: [1] Merriam-Webster Dictionary http://www.merriam-webster.com/dictionary/biometry [2] Z. McMahon, Biometrics: History, Indiana University, Indiana University Computer Science Department, 24 January 2005. [3] J.L. Wayman, “Biometrics – Now and Then: The development of biometrics over the last 40 years,” H. Daum (ed.) Biometrics in the Reflection of Requirements: Second BSI Symposium on Biometrics 2004. SecuMedia, Bonn, 2004. [4] Maltoni, Davide, Maio, Jain, and Prabhakar, Handbook of Fingerprint Recognition (Springer: New York, 2005) [5] Biometrics.gov, http://www.biometrics.gov/Documents/HandGeometry.pdf [6] Daugman, John, “New Methods in Iris Recognition”, IEEE Transactions on Systems, Man, and Cybernetics—Part B: Cybernetics, Vol. 37, No. 5, October 2007 [7] Wikipedia, http://en.wikipedia.org/wiki/Retina_scan [8] Title: (WO/2006/034527) CORNEAL BIOMETRY Date: 12/09/2005 Applicants: POSITIVE EYE-D LTD [AU/AU]; Suite 7, Level 1, 3 Spring Street, Sydney, NSW 2000 (AU) (All Except US). MASON, Stephen Archer [AU/AU]; (AU) (US Only). URL: http://www.wipo.int/pctdb/en/wo.jsp?wo=2006034527&IA=AU2005001386&DISPLAY=DESC taken from the web on Oct 11, 2009. [9] Article: Biometrics, identification and verification URL: http://openlearn.open.ac.uk/mod/resource/view.php?id=211235 taken from the web on Oct 12, 2009. [10] Title: Retina biometrics URL: http://www.biometricnewsportal.com/retina_biometrics.asp taken from the web on Oct 12, 2009. [11] Authors: Anil K. Jain, Patrick Flynn, Arun A. Ross Book Title: Handbook of Biometrics Publisher: Springer Science + Business Media, LLC. Page | 18 Year: 2008 City, state, country: New York, NY, USA Pages: (8, 89) [12] Name of article: All Access Control Systems URL:http://catalog2.panasonic.com/webapp/wcs/stores/servlet/ModelDetail?displayTab=O&st oreId=11201&catalogId=13051&itemId=88595&catGroupId=21552&surfModel=BM-ET330 taken from the web on Oct 13, 2009. [13] Panasonic Iris Reader: The Biometric For Identity Management and Access Control ftp://ftp.panasonic.com/pub/Panasonic/cctv/SpecSheets/BM-ET330II.pdf taken from the web on Oct 14, 2009 [14] Issue: August 2007 Title of article: Focus on Corneal Topographers http://www.ophmanagement.com/archive%5C2007%5CAugust%5COMD_August_A22_Fig03.jp g . Figure taken from the web on Oct 14, 2009 [15] Title: Corneal Topography and 3D Software http://images.google.com/imgres?imgurl=http://www.hlth.qut.edu.au/opt/graphics/clvol3.jpg &imgrefurl=http://www.hlth.qut.edu.au/opt/research/contacts/measurements.jsp&usg=__w5 qsrtGYw7UN6UtBRHZEB9bNq3k=&h=181&w=430&sz=23&hl=en&start=10&tbnid=BGJdS7Komz 9xvM:&tbnh=53&tbnw=126&prev=/images%3Fq%3D3d%2Bcorneal%2Btopography%26gbv%3 D2%26hl%3Den%26sa%3DG. Figure taken from the web on Oct 14, 2009 [16] Title: Corneal topography http://en.wikipedia.org/wiki/Corneal_topography taken from the web on Oct 14, 2009 [17] Laser Safety and the Eye: Hidden Hazards and Practical Pearls. 1996. Lions Laser Skin Center Vancouver Hospital and Health Sciences Centre.24 Dec. 1996 <http://www.dermweb.com/laser/eyesafety.html#What>. [18] http://en.wikipedia.org/wiki/Laser_safety. [19] www.osha.gov/dts/osta/otm/otm_iii/otm_iii_6.html. [20] Institute ANS. American National Standard on the Safe use of Lasers ANSI Z136.1-2007.: American National Standards Institute, 2007 [21] K. Bowyer, P. Flynn, K.Hollingsworth, S. Baker, and S. Ring. "Toward the next generation of iris Biometrics science," SPIE Newsroom, www.spie.org, May. 2009. [22] R. B. Vajpayee, N. Sharma, L. Sullivan, Step by step Lasik surgery,Informa Healthcare, 2005. Page | 19 [23] N. Maeda, S. D. Klyce, M.K. Smolek, H. Hamano, S. Mitsunga and K. Watanabe, Videokeratography for Quantitative Analysis of Used Soft Contact LensesJpn J Ophthalmol, pp. 235-239, August. 1996. [24] Contamac Ltd, “Contact Lens Parameters,” http://www.contamac.com/assets/productdocs/Contact%20Lens%20Parameters.pdf, 09/01/08 [9/23/09]. [25] The Cleveland Clinic, “The Cornea and Corneal Disease,” http://my.clevelandclinic.org/disorders/Herpes/hic_The_Cornea_and_Corneal_Disease.html, 7/7/09 [10/12/09]. [26] D. R. Iskander, M. J. Collins. “Applications of High-speed Videokeratoscopy,” [27] R. L. Windsor, L. K. Windsor, “Understanding Nystagmus,” http://www.lowvision.org/nystagmus.htm, [10/5/09]. [28] “All About Amblyopia (Lazy Eye).” Internet: http://www.lazyeye.org/, [10/10/09]. [29] T. Buehren, J. B. Lee, M. J. Collins, D. R. Iskander. (2002, May). “Ocular Microfluctuations and Videokeratoscopy.” Cornea. [Print] 21(4), pp. 346-351. [10/5/09] [30] “Biometrics Algorithm.” [online]. Available: http://www.technovelgy.com/ct/TechnologyArticle.asp?ArtNum=72. [Accessed: Oct. 2, 2009]. [31] A. Jain and S. Prabhakar, “Fingerprint Identification,” [Online]. Available: http://biometrics.cse.msu.edu/fingerprint.html. [Accessed: Oct. 2, 2009]. [32] M. A. Hebaishy, “Optimized Daugman’s Algorithm for Iris Localization,” National Authority for Remote Sensing and Space Science. [Online]. Available: http://wscg.zcu.cz/wscg2008/Papers_2008/poster/A11-full.pdf. [Accessed: Oct. 5, 2009]. [33] B. Fox, “For Secure ID, the Eyes Have It,” biometricgroup.com. [Online]. Available: http://www.biometricgroup.com/in_the_news/02_25_04.html. [Accessed: Oct. 16, 2009]. [34] A. Nagar, “Secure Biometric Recognition,” Oct. 24, 2008. [Online]. Available: http://www.cse.msu.edu/~nagarabh/SecureBiometricRecognitionPart1.pdf. [Accessed: Oct. 16, 2009]. Page | 20 [35] J. Daugman, “How Iris Recognition Works,” IrisBiometrics.net. [Online]. Available: http://www.teachplanet.net/irisbiometrics/index.html. [Accessed: Oct. 14, 2009]. [36] S. Nanavati, R. Nanavati, and M. Thieme, Biometrics: Identity Verification in a Networked World. New York: John Wiley and Sons, 2002. Page | 21