EVALUATE VENDOR PRODUCTS AND EQUIPMENT
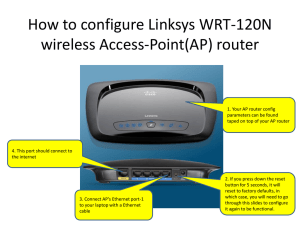
advertisement

EVALUATE VENDOR PRODUCTS AND EQUIPMENT ABC COLLEGE: The number of computers connected to the wireless router at ABC college has increased significantly therefore network speed has decreased dramatically. TASK: control network access from student computer to internet increase the bandwidth of wireless network Prioritise the traffic flow from staff member computers. THIS CAN BE DONE BY: NETWORK ACCESS CONTROL (NAC): is an approach to computer network security that attempts to unify endpoint security technology (such as antivirus, host intrusion prevention, and vulnerability assessment), user or system authentication and network security enforcement USE A NETWORK SECURITY KEY If you have a home or office wireless network, you should set up a network security key, which turns on encryption. With this, other people (except authorise users) can't connect to your network without the security key. Also, any information that is sent across your network is encrypted so that only computers that have the key to decrypt the information can read it. This can help avert attempts to access your network and files without your permission. Known Wireless network encryptions are: Wired Equivalent Privacy (WEP) Wi-Fi Protected Access (WPA) WPA-2. CHANGE THE ADMINISTRATOR NAME AND PASSWORD If you have a router or access point, you probably used a default name and password to set up the device. Most manufacturers use the same default name and password for all of their equipment, this enables anyone to gain access your router or access point without you knowing it. To secure your network, change the default administrator user name and password for your router. Check the information that came with your device for instructions about how to change the name and password. CHANGE THE DEFAULT SSID: Routers and access points use a wireless network name called a service set identifier (SSID). Most manufacturers use the same SSID for all of their routers and access points. Changing the default SSID helps to keep your wireless network from overlapping with other wireless networks that might be using the default SSID. It makes it easier for you to identify which wireless network is yours, if there are wireless network(s) nearby, because the SSID is typically shown in the list of available networks. Check the information that came with your device for instructions about how to change the default SSID. RAFIA SAFI ID#C62988 Page 1 of 5 EVALUATE VENDOR PRODUCTS AND EQUIPMENT USE STANDARD OR USER ACCOUNT: The standard account can help protect your computer by preventing users from making changes that affect everyone who uses the computer. A very good recommendation is for you to create a standard account for each user. When you are logged on to Windows with a standard account, you can do anything that you would do with an administrator account, but if you want to do something that affects other users of the computer, such as installing software or changing security settings, Windows might ask you to provide a password for an administrator account. INSTALLING SOFTWARE FOR NETWORK: SPYWARE Some NAC software, such as Impulse Safe Connect, require the installation of a client agent. This agent is used to verify that the user is in compliance with the site network access agreement. This allows for locking down network access to any client running unauthorized software, unmaintained updates, or for any other violation detected. FILE SHARING Some colleges and universities used NAC systems in order to ban legal, as well as illegal, file sharing applications. BY USING PROXY SERVER: An anonymous Web proxy is a type of proxy server that works through a Web form (also often called a CGI proxy). Instead of configuring the address of the server in the browser as is done for HTTP or SOCKS proxies, you simply navigate to the home page of the Web / CGI proxy, where proxy functionality is then enabled for each browsing session. The top free anonymous Web proxy servers are described below. PROXIFY Unlike most other anonymous Web proxies, Proxify supports encryption via the SSL and HTTPS network protocols. Proxify also handles the basic functions of an anonymous proxy server well including hiding your IP address and filtering of cookies. NETWORK SPEED Implementing a NAC requires additional resources and expenses. This reduces access times and uses bandwidth. TO SECURE NETWORK WITH WINDOWS FIREWALL: A firewall is a hardware or software that monitors the traffic moving through a network gateway. Firewall can be configured to block or allow traffic based on defined criteria (ACLs). Firewalls blocks or allows random pings from a remote site to your computer or programs from your computer that attempts to access remote sites without your knowledge. Most if not all windows software comes with inbuilt firewall. To view and configure your firewall on windows, follow these steps: RAFIA SAFI ID#C62988 Page 2 of 5 EVALUATE VENDOR PRODUCTS AND EQUIPMENT If your using XP Single-click on the wireless connection icon in your system tray Click Network and sharing centre Click windows firewall If you are using VISTA: Click on start button Right click on Network Select Properties USING HARDWARE: ROUTER: Wireless routers are equipped with modem, network switch (a device that has multiple connection ports for connecting computers and other network devices), wireless access points. Wireless Router can be connected to / from anywhere in your immediate environment or house. That means you can log on and surf the Internet from anywhere around your surroundings. Some of the wireless routers are equipped with a built in firewall to ward of intruders. The configuration options of the firewall are an important consideration when buying a router. Virtually everyone buys and sell online one way or the other, buying a wireless router with good firewall configuration options can be helpful for security and privacy. The broadband router wireless VoIP technology enables you to can connect to the Internet, using any ordinary phone device. You can then make calls to anybody in the world via your Internet connection. Wireless router provides strong encryption (WPA or AES) and features the filters MAC address and control over SSID authentication. DISADVANTAGES: The wireless connection will be slightly slower than the wired connection. Simply put, wireless or WI-FI transmits through the air and can be blocked interfered with by other waves from the surrounding. Security is one of the main concern when it comes to networking generally, wired network provides for more regid security to wireless. This means that all of your private data stored in your laptop or PDA could be exposed to anyone in the same vicinity. It's possible that an unscrupulous person could obtain passwords and important personal information easily from wireless networks if not properly configured. There is over congestion of WI-FI, especially in the cities where you have a large population of stores and big organisations that transmits over the same channel, causing much interference. Other devices can be a problem too. Blue tooth devices, cordless telephones and microwaves ovens do cause interference sometimes. These are some of the known disadvantages, but it doesn’t hinder yours truly from using wireless; basically, because of the freedom and manageability I get. One could work anywhere in their surroundings. RAFIA SAFI ID#C62988 Page 3 of 5 EVALUATE VENDOR PRODUCTS AND EQUIPMENT POSITION YOUR ROUTER OR ACCESS POINT : Wireless signals can transmit a few hundred feet, so the signal from your network could be broadcast outside of your home. You can help limit the area that your wireless signal reaches by positioning your router or access point close to the centre of your home rather than near an outside wall or window. NETWORK SWITCHES: A Network switch is a device that filters, forwards, or floods frames based on the destination address of each frame . A switch is a very adaptable Layer 2 device; it replaces a hub as the central point of connection for multiple hosts. In a more complex role, a switch may be connected to one or more other switches to create, manage, and maintain redundant links and VLAN connectivity. A switch processes all types of traffic in the same way, regardless of how it is used. Switches moves traffic base on MAC addresses. Each switch maintains a MAC address table in high-speed memory, called content addressable memory (CAM). The switch recreates this table every time it is activated, using both the source MAC addresses of incoming frames and the port number through which the frame entered the switch. Switches perform their routing functions at the layers 2 model of the OSI. Some switches process data at the Network Layer (layer 3), This types of switches are referred to as layer 3 switches or multilayer switches. Switches form an integral parts in networking LAN or WANs . Small office, Home office ( SOHO) applications normally, use a single or an all purpose switches . As mentioned earlier, switches operates at the data-link layer of the OSI model, switch function is to create a different collision domain per switch port. Let take an example, Four computers PC 1, PC 2, PC 3, PC 4 attached to switch ports, then PC 1 and PC 2 can transfer data between them so as PC 3 and PC 4, simultaneously without interfering with each other's conversations. Unlike a hub, which allows the sharing of bandwidth by all port, run in half-duplex and is prone to collisions of frames and retransmissions. With some ISPs and other networking environments where there is a need for much analysis of network performance and security, switches may be connected between WAN routers as places for analytic modules. Some switches provide in built firewall, network intrusion detection and performance analysis modules that can plug into switch ports. HUBS: Hubs are used to connect computers on a network so as to communicate with each other. Each computer plugs into the hub with a cable, and information sent from one computer to another passes through the hub. RAFIA SAFI ID#C62988 Page 4 of 5 EVALUATE VENDOR PRODUCTS AND EQUIPMENT 4 DIFFERENT BRANDS OF SERVER: IBM HP(HEWLETT-PACKWARD) DELL ACER ROUTERS: CISCO AXION GENERIC NETGEAR SERVER OPERATING SYSTEM MAC OS X MICROSOFT WINDOW SERVER 2003 UNIX LINUX BSD NOVELL NETWARE ADSL MODEM: NETGEAR DM111P CISCO SPP527W LENOVO 43R1814 LINKSEYS AM300 NAS: RAIDIX HP NETAPP DELL QNAP COMMON BETWEEN BSD AND LINUX: BSD and Linux are two families of open-source computer operating systems. Both are classed as Unix-like because they have a kernel, internals, and libraries, programmed using algorithms and data structures derived from historic AT&T Unix. The most significant non-technical aspect of both families is their availability as free software. RAFIA SAFI ID#C62988 Page 5 of 5