Rainbow Tables Presentation
advertisement

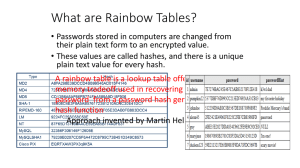
by Wild King Generally speaking , a rainbow table is a lookup table which is used to recover the plain-text password that derives from a hashing or cryptographic function. Rainbow Tables offer a TIME-MEMORY trade-off for the above process. Rainbow Tables consist of a set of arrays. Each array includes data which is there for later use (lookups) . A hashing function is a very deterministic and well defined procedure which is usually a mathematical function which is used to convert a series of data ( e.g. plain text, passwords , phone numbers , file names etc.) into a datum of our liking. Reasons : •Encryption •Data Transmission Correction •Data Compression •Other Useful Terms : •Hash values, hash codes, hash sums, checksums or simply hashes. •Hashing •Collision In the field of Computer Security , hashes are widely used as a method to protect the data that is transmitted between computer systems , from outside attacks such as a “Man in the Middle Attack”. Hello I’m John Give me your pass My pass is : lamepass Now I know too! Hello, I’m E234BC59984CD Give me your pass My pass is : FF3451100C ?!?!?!?!?!?! First of all to crack the Hash back to it’s original plain text we need to know the Hashing Function ( algorithm) that was used to generate the Hash. Then we usually use the most common way of cracking , that is called “Brute Forcing”. Generally Brute Forcing a hash consists of us trying every single option of the original unknown plain text , through the hashing function. If there is a match then we have found our original text. Hashing functions most of the times consist of many , time consuming , processor hungry mathematical calculations . This is done very quickly of course for one hash. But it gets really slow when the original text: •Is long •Uses alphanumeric characters •Uses special characters (e.g. : “” $ % &) This way calculations can easily take hours, days , months , even years. And this is something not efficient. The solution to this problem are the Rainbow tables. The general idea of the Rainbow Tables is that we pre compute a great deal of the hashes , and then we store them into tables , so that we can look up the hashes later. In fact , what we really do to create a Rainbow Table , is the calculation of multiple hash chains . For the creation of the pre computed hash chain we use two Functions : •The main Hashing Function (H) •A Reduction Function (R) Then we start passing random words (that could be the original text we are looking for ) in turn through the Hash Function and the Reduction Function , thus creating a chain Example : aaaaaa —H→ 281DAF40 —R→ sgfnyd —H→ 920ECF10 —R→ kiebgt aaaaab—H→ 8676FDE1 —R→ gfirjd —H→ 6573FAC2 —R→ vhridt After the computation of each chain we store only the First and the Last Passwords into the table. The first Password is the Starting Point and the last one is the End Point. After we finish computing the whole table we sort it for faster look ups. Increasing the length of the chain decreases the size of the table. It also increases the time required to perform lookups, and this is the time-memory trade-off of the rainbow table. In a simple case of one-item chains, the lookup is very fast, but the table is very big. Once chains get longer, the lookup slows down, but the table size goes down. Now to crack the Hash we need to do the following : aaaaaa —H→ 281DAF40 —R→ sgfnyd —H→ 920ECF10 —R→ kiebgt Lets say we are given the hash : 920ECF10 First we will use the Reduction Function on this hash then the Hashing Function and so on, thus computing again a hash chain . Every time we get a product out of the Reduction Function we look it up in the End Point Array of the pre computed Rainbow tables . If we find a match then we start calculating the hash chain from the Starting Point till we get to the given Hash . Then the product prior to the given hash in the computed chain will be the password we are looking for. Back to our example : Hash = 920ECF10 —R→ kiebgt kiebgt is in our table with a Starting point of : aaaaaa Now computing the aaaaaa hash chain we get : aaaaaa —H→ 281DAF40 —R→ sgfnyd —H→ 920ECF10 So the password we are looking for is : sgfnyd While the whole idea behind the Rainbow Tables is working , and gets the desired password much much faster than a Brute Force attack it still has some problems : • • • It is quite useless against salted Hashes. Each pre computed Rainbow Table is attached to a specific Hashing Function and can’t be used for other Functions unless recomputed . It still needs quite a lot of time to compute and sort the Table (despite some faster and improved algorithms ). The first two problems come together with the way Rainbow tables are created and the logic behind their use, and we cannot do anything to solve them but to use either another cracking method (case 1), or specific Tables (case 2). What we can do, is improve the rate at which the Tables are produced. And that we can do with the help of multiprocessor or clustered computing. The general idea for creating fast an accurate Rainbow Table would be the following : The Master Server aaaaaa aaaaab aaaaac aaaaad aaaaae N Number of Workers aaaaaf aaaaag The general idea for creating fast an accurate Rainbow Table would be the following : Storage The Master Server 2FA354 7BCA72 CCCAAA 145CBD FF1903 Calculating… N Number of Workers BA5423 CF65AB The general idea for creating fast an accurate Rainbow Table would be the following : The Master Server Sorting N Number of Workers When everything is finished and the Rainbow tables are created and sorted we can access them from any computer and query the Tables for the Hash we want to crack . What is the password for : 920ECF10 ? The speed offered by the Rainbow Tables for cracking the Hashes , combined with the computing power of a multiprocessor computer , a Cuda VGA or a Computer cluster for the creation of the Rainbow Tables , can be a very powerful tool for everyone associated with Security Auditing and Computer Security in general as a science. Just imagine that passwords that are announced as “Complicated” , “Tough” or “Hard to Crack” by multiple programs , and someone trying to brute - force them would require months or years to crack, now can be broken in a matter of minutes (through pre computed Rainbow Tables) or hours (including the time we need to compute the Tables ). But don’t forget that Rainbow Tables are : Once Compute , Use Forever as long as the Hashing algorithm remains the same . http://www.ethicalhacker.net/content/view/94/24/ http://en.wikipedia.org/wiki/Rainbow_table http://en.wikipedia.org/wiki/Hash_function
![Rainbow Sandals[1]](http://s2.studylib.net/store/data/005415944_1-86d746c06518ebd8de8a03e56a4931b4-300x300.png)