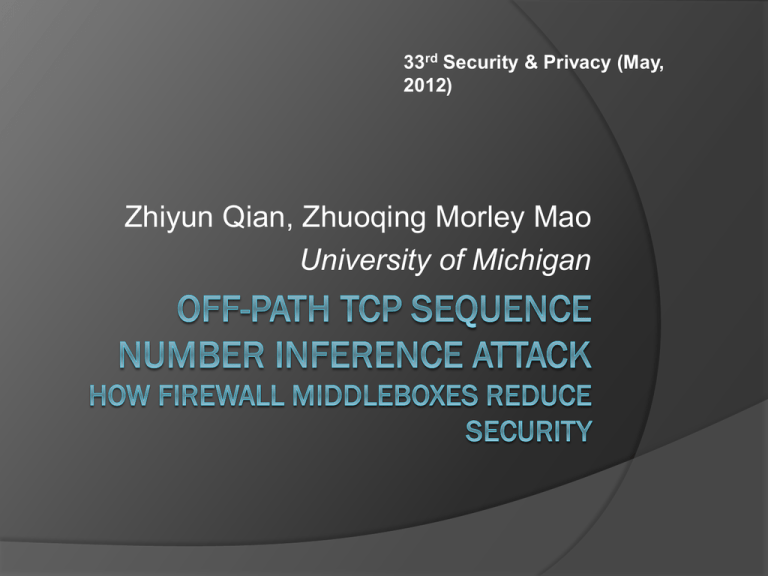
33rd Security & Privacy (May,
2012)
Zhiyun Qian, Zhuoqing Morley Mao
University of Michigan
Outline
Introduction
Fundamentals of the TCP Sequence
Number Inference Attack
TCP Attack Analysis and Design
Attack Implementation and Experimental
Results
Vulnerable Networks
Discussion
2012/4/30
A Seminar at Advanced Defense Lab
2
Introduction
TCP was initially designed without many
security considerations.
4-tuple: local IP, local Port, foreign IP, foreign
Port
Off-path spoofing attacks
2012/4/30
A Seminar at Advanced Defense Lab
3
Off-Path Spoofing Attacks
One of the critical patches is the
randomization of TCP initial sequence
numbers (ISN)
RFC 6528 [link]
Firewall vendors soon realized that they
can in fact perform sequence number
checking at network-based firewalls and
actively drop invalid packets even before
they can reach end-hosts
2012/4/30
A Seminar at Advanced Defense Lab
4
Fundamentals of the TCP Sequence
Number Inference Attack
Sequence-Number-Checking Firewalls
2012/4/30
A Seminar at Advanced Defense Lab
5
Sequence-Number-Checking
Firewalls
Window size
Fixed
64K x 2N, N is the window scaling factor in SYN
and SYN-ACK packet.
Left-only or right-only window
Window moving behavior
Window advancing
Window shifting
2012/4/30
A Seminar at Advanced Defense Lab
6
Threat Model
On-site TCP injection/hijacking
An unprivileged malware runs on the client
with access to network and the list of active
connections through standard OS interface.
Off-site TCP injection
only when the target connection is long-lived
Establish TCP connection using spoofed
IPs
2012/4/30
A Seminar at Advanced Defense Lab
7
Obtaining Feedback – Side
Channels
OS packet counters
IPIDs from responses of intermediate
middleboxes
An attacker can craft packets with TTL
values large enough to reach the firewall
middlebox, but small enough that they will
terminate at an intermediate middlebox
instead of the end-host, triggering the TTLexpired messages.
2012/4/30
A Seminar at Advanced Defense Lab
8
Sequence Number Inference
2012/4/30
A Seminar at Advanced Defense Lab
9
Timing of Inference and
Injection — TCP Hijacking
For the TCP sequence number
inference and subsequent data injection
to be successful, a critical challenge is
timing.
To address the challenge, we design
and implement a number of TCP
hijacking attacks.
2012/4/30
A Seminar at Advanced Defense Lab
10
TCP Attack Analysis and Design
Two base requirements for all attacks
The ability to spoof legitimate server’s IP
A sequence-number-checking firewall
deployed
2012/4/30
A Seminar at Advanced Defense Lab
11
Attack Requirements
2012/4/30
A Seminar at Advanced Defense Lab
12
On-site TCP Hijacking
Reset-the-server
2012/4/30
A Seminar at Advanced Defense Lab
13
On-site TCP Hijacking
Preemptive-SYN
Hijacking
2012/4/30
A Seminar at Advanced Defense Lab
14
On-site TCP Hijacking
Hit-and-run
Hijacking
2012/4/30
A Seminar at Advanced Defense Lab
15
Off-site TCP Injection/Hijacking
URL phishing
An attacker can also acquire target four
tuples by luring a user to visit a malicious
webpage that subsequently redirects the
user to a legitimate target website.
But it is not implemented in this paper.
2012/4/30
A Seminar at Advanced Defense Lab
16
Off-site TCP Injection/Hijacking
Long-lived connection inference
An approach we discover is through sending
a single ICMP error message (e.g., network
or port unreachable) to query a four-tuple.
Pass through firewall and trigger TTL-
expired message
2012/4/30
A Seminar at Advanced Defense Lab
17
Establish Spoofed Connections
We found that there are many such
unresponsive IPs in the nation-wide
cellular network that we tested.
2012/4/30
A Seminar at Advanced Defense Lab
18
Attack Implementation and
Experimental Results
Client platform
Android 2.2 and 2.3.4
TCP window scaling factor: 2 and 4
Vendors: HTC, Samsung, and Motorola
Network
An anonymized nation-wide carrier that
widely deploys firewall middleboxes at the
GGSN-level
2012/4/30
A Seminar at Advanced Defense Lab
19
Side-channel
/proc/net/snmp: InSegs
the number of incoming TCP packets
received
/proc/net/netstat: PAWSEstab
packets with an old timestamp is received
IPID side-channel
the noise level is quite tolerable.
2012/4/30
A Seminar at Advanced Defense Lab
20
Sequence Number Inference
Assuming a cellular RTT of 200ms
32 times for binary search (4G)
About 10s in practice
N-way search
Mix all methods
It takes only about 4–5 seconds to complete
the inference
2012/4/30
A Seminar at Advanced Defense Lab
21
On-site TCP Hijacking
Android 2.3.4 + m.facebook.com +
Planetlab server [link]
2012/4/30
A Seminar at Advanced Defense Lab
22
Reset-the-server [Demo]
We leverage requirement C4 which tells
the attacker that the victim connection’s
ISN is at most 224 away from the ISN of
the attacker-initiated connection.
Since RST packets with any sequence
number that falls in the receive window
can terminate the connection.
P. A. Watson. “Slipping in the Window: TCP
Reset Attacks,” 2004.
2012/4/30
A Seminar at Advanced Defense Lab
23
Reset-the-server
The max number of required RST
server_init_window
m.facebook.com: 4380 require 7661 RST
twitter.com: 5840 require 5746 RST
chase.com: 32805
2012/4/30
A Seminar at Advanced Defense Lab
24
Reset-the-server
Bandwidth requirements
327 Kbps ~ 12 Mbps
2012/4/30
A Seminar at Advanced Defense Lab
25
Hit-and-run
Bandwidth requirements
WIN is 64K x 2window_scaling_factor
For the two Oses is 26Mbps and 6.6Mbps
2012/4/30
A Seminar at Advanced Defense Lab
26
On-site TCP Hijacking
2012/4/30
A Seminar at Advanced Defense Lab
27
Off-site TCP Injection
URL phishing
No implement
Because NAT is deployed.
long-lived connection inference
a particular push server IP 74.125.65.188
and port 5228
About 7.8% of the IPs have a connection
with the server
2012/4/30
A Seminar at Advanced Defense Lab
28
Establish Spoofed Connections
Find unresponsive IP
We send a SYN packet with a spoofed IP
from the attack phone inside the cellular
network to our attack server which responds
with a legitimate SYN-ACK back.
There are 80% of IPs are unresponsive.
We can make about 0.6 successful
connection per second on average with
more than 90% success rate
2012/4/30
A Seminar at Advanced Defense Lab
29
Vulnerable Networks
We deployed a mobile application
(referred to as MobileApp) on the
Android market.
The data are collected between Apr
25th, 2011 and Oct 17th, 2011 over 149
carriers uniquely identified
2012/4/30
A Seminar at Advanced Defense Lab
30
Firewall Implementation Types
Overall, out of the 149 carriers, we
found 47 carriers (31.5%) that deploy
sequence-number-checking firewalls.
2012/4/30
A Seminar at Advanced Defense Lab
31
Intermediate Hop Feedback
24 carriers have responsive
intermediate hops that reply with TTLexpired ICMP packets.
8 carriers have NAT that allow single
ICMP packet probing to infer active four
tuples.
2012/4/30
A Seminar at Advanced Defense Lab
32
Discussion
Firewall design
Side-channels
HTTPS-only world
2012/4/30
A Seminar at Advanced Defense Lab
33
2012/4/30
A Seminar at Advanced Defense Lab
34