Here is her PPT presentation
advertisement
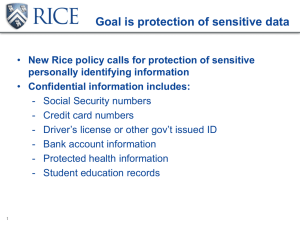
UNIVERSITY OF UTAH FINANCIAL AND BUSINESS SERVICES INCOME ACCOUNTING AND STUDENT LOAN SERVICES Kim Stringham Objectives • Understand PCI requirements. • Identify the roles and responsibilities of the many players. • Identify what needs to be done to reach & maintain compliance. • Introduce new technologies. 2 Payment Card Industry Data Security Standard What is PCI DSS? PCI DSS stands for Payment Card Industry Data Security Standard. This standard is a set of controls to protect cardholder data by mitigating data breaches and preventing cardholder data fraud. Defined by the Payment Card Industry Security Standards Council (PCI SSC) , the standard was created to increase controls around cardholder data to reduce credit card fraud. All merchants, processors, acquirers, issuers, service providers, and other entities that store, process or transmit cardholder information are required to comply with the PCI DSS. PA-DSS vs. PCI DSS? The Payment Application Data Security Standard (PA-DSS) requires vendors who supply payment application software to validate the application with the PCI Council. The validated application must be placed or used in a PCI DSS compliant environment for full compliance to be achieved. The merchant is responsible for the compliant environment. 3 12 PCI DSS Requirements 4 PCI DSS Merchant Levels For Visa, MasterCard and Discover Network PCI levels 1 Merchant levels • Over 6 million Visa, MasterCard or Discover transactions per year (all channels) • Annual Report on Compliance (ROC) completed by a Qualified Security Assessor (QSA) or internal auditor if signed by officer of the company* • Global merchants meeting the Level 1 criteria of another payment card brand • Quarterly network scan by an Approved Scan Vendor (ASV) • Attestation of Compliance Form 1 million to 6 million Visa, MasterCard or Discover transactions per year (all channels) • Annual Self-Assessment Questionnaire (SAQ) completed by an Internal Security Assessor (ISA) or a Report on Compliance (ROC) must be completed by a Qualified Security Assessor (QSA) • Quarterly network scan by an Approved Scan Vendor (ASV) • Attestation of Compliance Form 20,000 to 1 million e-commerce Visa, MasterCard or Discover transactions per year • Annual SAQ • Quarterly network security scan by an ASV • Annual signed Attestation of Compliance Form • All other businesses • Annual SAQ recommended • Less than 20,000 e-commerce Visa, MasterCard or Discover transactions per year • Quarterly network security scan by an ASV if applicable • Compliance validation requirements set by acquirer • 2 • 3 4 Compliance validation requirements More information available at the PCI Security Council website: www.pcisecuritystandards.org Abbreviations: ROC = Report on Compliance, QSA = Qualified Security Assessor, ASV = Approved Scanning Vendor, SAQ = Self Assessment Questionnaire, PCI SSC = Payment Card Industry Security Standards Council *For non-compliant businesses only, an annual signed “Attestation of non-storage of non-compliant data” is required 5 Self-Assessment Questionnaires V 3.0 • A – Card-not-Present, All Cardholder Data Functions Fully Outsourced • A-EP – Partially Outsourced E-Commerce Merchants Using a Third-Party Website for Payment Processing • B – Only Imprint Machines or Only Standalone, Dial-out Terminals. No Electronic Cardholder Data Storage • B-IP – Standalone, IP-Connected Terminals. No Electronic Cardholder Data Storage • C – Payment Application Connected to Internet, No Electronic Cardholder Data Storage • C-VT – Web-Based Virtual Payment Terminals, NECDS (key: no payment application • D – Full Standard for all other SAQ-Eligible Merchants 6 Roles and Responsibilities Merchant • Adhere to the PCI DSS standard. • Create a corporate security strategy to become and stay PCI compliant. • Create and maintain a compliant infrastructure. Acquiring Bank • Provide support, advice, and general guidance on PCI. • Ensure any products, software, or gateways added or in use are certified as PCI compliant. • Quarterly reporting to the card brands on a merchant’s compliance status. – This reporting reflects date and status of the SAQ/ROC, scan date(s) and results, information from the merchant completed Prioritized Approach containing the areas of non-compliance with current percentage completed and expected completion dates for full compliance. Card Networks/Brands • Enforcement of compliance with the PCI DSS and determination of any non-compliance penalties are carried out by the individual payment brands and not by the Council or WFMS. PCI Data Security Council • An open global forum, launched in 2006, is responsible for the development, management, education, and awareness of the PCI Security Standards, including the Data Security Standard (PCI DSS), Payment Application Data Security Standard (PA-DSS), and PIN Transaction Security (PTS) requirements. • The Council's five founding global payment brands -- American Express, Discover Financial Services, JCB International, MasterCard Worldwide, and Visa Inc. -- have agreed to incorporate the PCI DSS as the technical requirements of each of their data security compliance programs and have equal input. Each founding member also recognizes the QSAs, PA-QSAs and ASVs certified by the PCI Security Standards Council. • Website, https://www.pcisecuritystandards.org/ 7 Don’t Delegate Compliance • Never assume your software vendor or service provider is maintaining your PCI Compliance • You should be able to answer the following questions: – What equipment, software, and services do we use for processing and where are they located? – Do we have a complete inventory? – Do we have a hardware based firewall? – What anti-virus software do we use and who updates it? – Do we have remote access software on our system? – Is it always turned on? – Is 2 factor authentication used? – Is there one id and password per individual user? – Are passwords changed regularly? – Who reviews our log files? – Who trains the employees to follow guidelines & how? – Can we document everything PCI related? 8 Know what you have... Possible components at point of sale 9 What Data Are You Storing? 10 Understand your Network and Data Storage 11 12 Steps to Information Security 12 Only 5 Steps for Dial-up Terminals 13 Don’t Skimp on POS / Upgrades 14 Train your Staff Monitor your Staff 15 Maintenance is Key • Data security is more than completing a SAQ every 12 months • Begin SAQ at least three months before its due • Stay up to date – PCI council changes – Payment network mandates – The latest trends in data compromise • Scan – – – – Complete a passing external scan at least quarterly And every time changes are made to the system Use internal scans to detect and correct vulnerabilities Daily review that Anti-Virus, File Integrity Monitoring, and Logging are running 16 Chip & PIN– a.k.a EMV • Near Field Communication (NFC) • Required vs. Encouraged – Liability Shift in the U.S. effective October 1, 2015 – Merchants not using EMV will take the financial hit on fraudulent, card-present transactions. • Benefits – Physical Cards are less likely to be used fraudulently. • Compliance – No changes in compliance requirements. • Disclaimer – E-Commerce/Phone transactions not affected.17 PCI Compliance Changes/Dates 2013 October • • • 2015 2017 • U.S. Liability Shift for domestic and cross-border counterfeit card-present point of sale (POS) transactions to merchant. • U.S. Liability Shift for domestic and cross-border counterfeit card-present Automated Fuel Dispensers U.S. Liability Shift for counterfeit fraud ATM Transactions October October PCI Council introduced PCI DSS 3.0 Standard* Release 3.0 will also include updated PIN Transaction Security v4.0 You may validate to version 2.0 through the end of the year. Mandatory use of 3.0 for validations in 2015 • *Standards are updated due to the need for additional guidance, clarification, or evolving requirements for strong security standards. For more information on PCI updates, visit www.pcisecuritystandards.org 18 End to End Encryption • Point to Point Encryption ≠ E2EE – PCI DSS terminology – Must be an approved hardware/software combination • Scope Reduction – SAQ D – most requirements are not applicable • Hardware Encryption is VITAL! – Integration with Gateway, Software, Hardware • Always seek Acquiring Bank & QSA approval 19 Mobile Payments – PCI DSS Mobile Payments February 2013 - The PCI Security Standards Council has published the PCI Mobile Payment Acceptance Security Guidelines for Merchants as End Users. This guide educates merchants on the risk factors that need to be addressed in order to protect card data when using mobile devices to accept payments. Guidelines to Consider – Single purpose tablets, iPads – Hot Spot vs WiFi – Reduced functionality (browsing) – End to End Encryption Devices – Acquiring Bank products – Banking Policy Please visit: https://www.pcisecuritystandards. org/security_standards/documents .php?document=pcidss_mobile_pa yment_sec_guidelines 20 Consequences and Penalties for Non-Compliance or Breach The consequences and costs of non-compliance and of a data compromise can be devastating and may include: • Loss of the ability to process card payments. • Loss of consumer confidence and brand reputation. • Drop in revenues. • Heavy fines, penalties and expenses. - Up to $500,000 a month per violation (payment network imposed fines). - Actual damages to cardholders. - Attorneys’ fees. - Potential state and federal fines. Notification and Remediation Process • Merchant reports suspected or known breach to Bank upon findings and card brands are notified. • Card brands notify Bank of Common Point of Purchase investigation. • Remediation requires demonstration, documentation, and deadlines. Costly forensic investigation may be required. • In some cases, you may be required to shut down all POS, gateways, or IP connected terminals and install “dial-up” terminals until the environment is remediated and deemed safe. Data breaches now cost $194 per compromised record and averaged $5.5 million per data breach event.* *From a March 2012 Ponemon Institute study (www.ponemon.org) 21 PCI Resources 22 Payment Card Industry Glossary ASV Acronym for “Approved Scanning Vendor.” Company approved by the PCI SSC to conduct external vulnerability scanning services. Cardholder Data At a minimum, cardholder data consists of the full PAN. Cardholder data may also appear in the form of the full PAN plus any of the following: cardholder name, expiration date and/or service code See Sensitive Authentication Data for additional data elements that may be transmitted or processed (but not stored) as part of a payment transaction. Environment The people, processes and technology that store, process or transmit cardholder data or sensitive authentication data, including any connected system components. Compensating Controls Compensating controls may be considered when an entity cannot meet a requirement explicitly as stated, due to legitimate technical or documented business constraints, but has sufficiently mitigated the risk associated with the requirement through implementation of other controls. Compensating controls must: • (1) Meet the intent and rigor of the original PCI DSS requirement; (2) Provide a similar level of defense as the original PCI DSS requirement; (3) Be “above and beyond” other PCI DSS requirements (not simply in compliance with other PCI DSS requirements); and (4) Be commensurate with the additional risk imposed by not adhering to the PCI DSS requirement. Network Segmentation Network segmentation isolates system components that store, process, or transmit cardholder data from systems that do not. Adequate network segmentation may reduce the scope of the cardholder data environment and thus reduce the scope of the PCI DSS assessment. P2PE Point to Point Encryption. Penetration Test Penetration tests attempt to exploit vulnerabilities to determine whether unauthorized access or other malicious activity is possible. Penetration testing includes network and application testing as well as controls and processes around the networks and applications, and occurs from both outside the network trying to come in (external testing) and from inside the network. QSA Acronym for “Qualified Security Assessor,” company approved by the PCI SSC to conduct PCI DSS on-site assessments. Sensitive Authentication Data Security-related information (including but not limited to card validation codes/values, full magnetic-stripe data, PINs, and PIN blocks) used to authenticate cardholders and/or authorize payment card transactions. https://www.pcisecuritystandards.org/documents/pci_glossary_v20.pdf 23