- No category
Information Systems & Security: Intro, Threats, & Technologies
advertisement
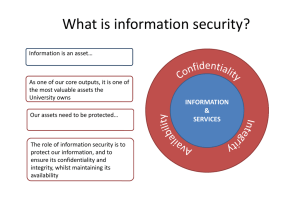
Introduction- Introduction to Information Systems, Types of Information Systems, Development of Information Systems, Introduction to Information Security and CIA triad, Need for Information Security, Threats to Information Systems, Information Assurance and Security Risk Analysis, Cyber Security. Here is a comprehensive introduction and overview of the requested topics related to Information Systems and Information Security: Introduction to Information Systems Information Systems (IS) are integrated sets of components for collecting, storing, and processing data to provide information, knowledge, and digital products. They support decisionmaking, coordination, control, analysis, and visualization in an organization. IS typically includes hardware, software, data, procedures, and people. Types of Information Systems 1. Transaction Processing Systems (TPS): Handle day-to-day business transactions such as sales, receipts, payroll, etc. 2. Management Information Systems (MIS): Provide managers with reports and tools to make routine decisions based on TPS data. 3. Decision Support Systems (DSS): Assist in complex decision-making using data analysis, modeling, and simulations. 4. Executive Information Systems (EIS): Provide top executives with easy access to internal and external information relevant to strategic decisions. 5. Enterprise Resource Planning (ERP) Systems: Integrate core business processes like finance, HR, manufacturing into one system. 6. Knowledge Management Systems: Help with the creation, storage, and dissemination of organizational knowledge. 7. Customer Relationship Management (CRM) Systems: Manage customer data and interactions to enhance sales and service. Development of Information Systems Information Systems development includes: System Planning: Identifying needs and feasibility. System Analysis: Gathering requirements, studying current systems. System Design: Specifying system architecture, interfaces, and data structures. System Implementation: Coding, testing, installing. System Maintenance: Ongoing support, updating, and fixing issues. Development methodologies range from Waterfall to Agile, DevOps, emphasizing different ways to manage the complexity of system creation. Introduction to Information Security and CIA Triad Information Security involves protecting information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction to ensure confidentiality, integrity, and availability. Confidentiality: Ensuring information is accessible only to authorized individuals. Integrity: Guaranteeing accuracy and completeness of information and preventing unauthorized modification. Availability: Ensuring reliable access to information and resources when needed. These three principles form the CIA triad, the foundation of information security. Need for Information Security The need arises from increasing threats such as cyber-attacks, data breaches, and misuse of information that can lead to financial loss, legal consequences, and damage to reputation. Organizations must protect sensitive data, comply with regulations, safeguard intellectual property, and maintain trust. Threats to Information Systems Common threats include: Malware: Viruses, worms, ransomware. Phishing and Social Engineering: Tricking users into revealing information. Denial of Service (DoS) Attacks: Overloading systems to make them unavailable. Insider Threats: Employees misusing access. Unauthorized Access: Hacking and exploitation of vulnerabilities. Physical threats: Theft, natural disasters. Information Assurance and Security Risk Analysis Information Assurance: The practice of managing risks related to the use, processing, storage, and transmission of information. It involves ensuring the CIA triad through policies and controls. Security Risk Analysis: A systematic process to identify, assess, and prioritize risks to information assets, to implement appropriate mitigating controls and response plans. Cyber Security Cyber Security encompasses technologies, processes, and practices designed to protect networks, devices, programs, and data from attack, damage, or unauthorized access. It includes areas such as network security, application security, endpoint security, identity management, and incident response. If you'd like, I can provide detailed explanations or examples for any specific topic from above. Application Security- (Database, E-mail and Internet), Data Security Considerations (Backups, Archival Storage and Disposal of Data), Security Technology (Firewall, VPNs, Intrusion Detection System), Access Control. Security Threats -Viruses, Worms, Trojan Horse, Bombs, Trapdoors, Spoofs, E-mail Viruses, Macro Viruses, Malicious Software, Network and Denial of Services Attack. Here is a detailed overview of the specified topics related to Application Security, Data Security, Security Technologies, Access Control, and Security Threats: Application Security Application security focuses on protecting software applications from vulnerabilities and attacks throughout their lifecycle. Database Security: Safeguards databases from unauthorized access, misuse, or corruption. Techniques include authentication, encryption, access controls, and auditing. E-mail Security: Protects email communication from interception, spoofing, phishing, and malware attacks using encryption, spam filtering, and secure protocols (e.g., SSL/TLS). Internet Security: Involves protecting web applications and online transactions from threats like cross-site scripting (XSS), SQL injection, and unauthorized data access using secure coding practices, HTTPS, and firewalls. Data Security Considerations Backups: Regularly creating copies of data to recover information in case of data loss, corruption, or ransomware attacks. Archival Storage: Storing historical or infrequently accessed data securely for long-term retention and compliance. Disposal of Data: Securely destroying data that is no longer needed, using methods like shredding physical media or applying data wiping/overwriting on digital storage to prevent data recovery. Security Technology Firewall: A network security device or software that monitors and controls incoming and outgoing traffic based on pre-established security rules; it acts as a barrier between trusted and untrusted networks. VPNs (Virtual Private Networks): Create secure, encrypted connections over the internet, allowing remote users or offices to safely access private networks. Intrusion Detection System (IDS): Monitors network or system activities for malicious actions or policy violations, alerting administrators of possible security breaches. Access Control Access control mechanisms regulate who or what is allowed to access resources in a computing environment to ensure only authorized users can reach sensitive information. Types include: Discretionary Access Control (DAC): Owner defines access rights. Mandatory Access Control (MAC): System-enforced policies restrict access based on classifications. Role-Based Access Control (RBAC): Access permissions assigned based on user roles within an organization. Attribute-Based Access Control (ABAC): Access decisions based on attributes like user characteristics, resource type, and environment conditions. Security Threats Viruses: Malicious software that attaches to legitimate programs and replicates, causing damage or disruption. Worms: Self-replicating malware that spreads across networks without user intervention. Trojan Horse: Malware disguised as legitimate software that enables unauthorized access or damage. Bombs: Malicious code triggered by specific events or conditions, such as logic bombs. Trapdoors (Backdoors): Hidden methods to bypass normal authentication to gain unauthorized access. Spoofs: Deceptive attacks where a malicious entity impersonates another to gain access or steal information. E-mail Viruses: Viruses spread via email attachments or links. Macro Viruses: Malware embedded in documents using macros (like MS Office), activated when the document is opened. Malicious Software (Malware): A broad term including viruses, worms, Trojans, ransomware, spyware, etc. Network Attacks: Exploits targeting network vulnerabilities to intercept, redirect or disrupt communication. Denial of Service (DoS) Attack: Attempts to make a machine or network resource unavailable to its intended users by overwhelming it with traffic or triggering crashes. If needed, I can provide explanations or examples for any specific category or defense mechanisms against these threats.Here is a detailed overview of the topics you requested on Application Security, Data Security Considerations, Security Technologies, Access Control, and Security Threats: Application Security Database Security: Protects databases against unauthorized access, breaches, and data corruption by implementing access controls, encryption, and auditing. E-mail Security: Involves protecting electronic mail from interception, phishing, spam, and malware using encryption (SSL/TLS), spam filters, and secure email gateways. Internet Security: Focuses on securing web applications and internet communications against threats like data breaches, injection attacks, and unauthorized access through HTTPS, firewalls, and secure coding practices. Data Security Considerations Backups: Regularly copying data to offsite or cloud storage to enable recovery in case of data loss, corruption, or ransomware attacks. Archival Storage: Safely storing inactive or historical data for long-term retention, compliance, or legal reasons by using cost-effective but secure storage media. Disposal of Data: Securely destroying data no longer needed by physical destruction of media or digital wiping to prevent data recovery. Security Technology Firewall: A device or software that controls network traffic based on security rules to block unauthorized access while permitting legitimate communication. VPNs (Virtual Private Networks): Securely connect remote users or offices over the internet by encrypting data traffic between endpoints. Intrusion Detection System (IDS): Monitors network or system activities for suspicious behavior or known attack patterns and alerts administrators on potential breaches. Access Control Access control restricts access to resources based on authorization policies: Discretionary Access Control (DAC): Owners control access to their resources. Mandatory Access Control (MAC): Strict policies assigned by system rules based on classifications. Role-Based Access Control (RBAC): Access depends on user roles within the organization. Attribute-Based Access Control (ABAC): Access decisions are based on user attributes, resource types, and environmental conditions. Security Threats Viruses: Malicious programs that attach themselves to clean files and spread to damage or disrupt systems. Worms: Standalone malware that replicates itself to spread across networks without user intervention. Trojan Horse: Malware disguised as legitimate software to trick users into executing it. Bombs (Logic Bombs): Malicious code triggered by specific conditions or dates. Trapdoors (Backdoors): Hidden vulnerabilities that allow bypassing security controls. Spoofs: Impersonating another device or user to gain unauthorized access. Email Viruses: Malicious software spread via infected email attachments or links. Macro Viruses: Embedded in documents using macros, spreading when files are opened. Malicious Software (Malware): Includes viruses, worms, ransomware, spyware, and more, intended to harm systems or steal data. Network Attacks: Exploits targeting networks to intercept or disrupt communications. Denial of Service (DoS) Attack: Overwhelms a system to make it unavailable to legitimate users. Introduction to E-Commerce- Threats to ECommerce, Electronic Payment System, e-Cash, Credit/Debit Cards. Digital Signature, Cryptography Developing Secure Information Systems, Application Development Security, Information Security Governance & Risk Management, Security Architecture & Design Security Issues in Hardware, Data Storage & Downloadable Devices, Physical Security of IT Assets Access Control, CCTV, Backup Security Measures. Here is a comprehensive overview of the topics related to E-Commerce, Electronic Payment Systems, Security Technologies, and Information Security Governance: Introduction to E-Commerce E-Commerce refers to buying and selling goods and services over electronic networks like the internet. It includes various business models like B2B, B2C, C2C, and C2B. E-commerce depends heavily on secure and reliable information systems to protect sensitive data and ensure smooth transactions. Threats to E-Commerce Phishing and Fraud: Deceptive attempts to steal credentials or payment data. Data Breaches: Unauthorized access to customer or company data. Identity Theft: Using stolen identity information to make fraudulent purchases. Denial of Service (DoS) Attacks: Disrupting the availability of e-commerce sites. Man-in-the-Middle Attacks: Intercepting communication between customers and ecommerce platforms. Credit Card Fraud: Unauthorized use of payment card information. Electronic Payment System These systems facilitate electronic transactions for e-commerce, ensuring speed and security. e-Cash: Digital currency stored electronically that allows anonymous, secure payments online. Credit/Debit Cards: Widely used payment instruments enabling electronic transfers through payment gateways and banks. Digital Signature A digital signature is an electronic, encrypted stamp of authentication on digital documents. It ensures: Authentication: Verifies the sender’s identity. Integrity: Confirms the message was not altered. Non-repudiation: Prevents the sender from denying the transaction. Cryptography Cryptography is the science of encrypting information to secure data transmission and storage. Common techniques include: Symmetric Encryption: Same key for encryption and decryption. Asymmetric Encryption: Uses a public key for encryption and a private key for decryption. Hashing: One-way cryptographic function converting data into a fixed-size string. Developing Secure Information Systems Secure systems are developed by integrating security throughout the development lifecycle— planning, design, coding, testing, deployment, and maintenance—by following best practices like threat modeling, code audits, and secure coding standards. Application Development Security Focuses on identifying and mitigating vulnerabilities in software applications such as injection flaws, authentication weaknesses, and insecure configurations through secure design principles, code reviews, and penetration testing. Information Security Governance & Risk Management Governance establishes policies, roles, and responsibilities to protect information assets. Risk management involves identifying, assessing, and controlling risks to minimize impact on business objectives. Security Architecture & Design Security architecture involves designing robust systems with layered defenses including firewalls, access controls, encryption, and intrusion detection. It ensures confidentiality, integrity, and availability at all levels. Security Issues in Hardware, Data Storage & Downloadable Devices Hardware can be physically tampered with or stolen. Data storage devices risk data leakage if lost or improperly disposed of. Downloadable devices like USB drives can introduce malware or be used for data exfiltration. Physical Security of IT Assets Physical security measures protect hardware and infrastructure against theft, damage, or unauthorized access: Access Control: Mechanisms like biometric scanners, key cards to restrict physical entry. CCTV: Video surveillance for monitoring premises and deterring intrusions. Backup Security Measures: Secure storage of backup data, sometimes offsite, with encryption and access controls to ensure data recoverability and confidentiality. Security Policies- Why policies should be developed, Policy Review Process, Publication and Notification Requirement of policies, Types of policies – WWW policies, Email Security policies, Corporate Policies, Sample Security Policies. Case Study – Corporate Security Here is a detailed overview of Security Policies, their development, review, types, and a case study example on Corporate Security: Why Security Policies Should Be Developed Establish Responsibilities: Define roles and duties for safeguarding information and systems. Provide Direction and Consistency: Ensure uniform standards for security practices across the organization. Support Compliance: Help meet legal, regulatory, and contractual security requirements. Mitigate Risks: Identify acceptable use and controls to reduce security incidents. Create Awareness: Educate employees on their security obligations and organizational expectations. Policy Review Process Regular Reviews: Policies should be reviewed periodically (e.g., annually) to remain relevant with evolving threats and technologies. Stakeholder Involvement: Include IT, management, legal, and end-users in the review process for comprehensive updates. Risk and Compliance Assessment: Ensure the policy meets current compliance requirements and addresses new risks. Update and Approval: Incorporate necessary changes, then get management approval for the revised policy. Communication: Disseminate the updated policies to users promptly. Publication and Notification Requirements of Policies Accessibility: Policies should be easily accessible to all employees, often via an intranet or employee handbook. Formal Notification: Notify all users of new or updated policies through emails, meetings, or training sessions. Acknowledgment: Employees should acknowledge understanding and acceptance of policies to demonstrate compliance. Training: Incorporate policy understanding into periodic security awareness training. Types of Policies World Wide Web (WWW) Policies: Define acceptable use of internet resources, block access to harmful or non-work-related sites, and outline monitoring procedures. Email Security Policies: Include rules on appropriate use of email, handling of attachments, phishing awareness, and encryption requirements. Corporate Policies: Broader policies encompassing acceptable use, data protection, remote access, incident reporting, and disciplinary actions related to security. Sample Security Policies (Examples) Acceptable Use Policy: Rules governing users’ access and use of company IT resources. Password Policy: Guidelines on password complexity, expiration, and management. Data Protection Policy: Procedures for handling sensitive data and ensuring confidentiality. Incident Response Policy: Steps to detect, report, and respond to security incidents. Case Study – Corporate Security A multinational corporation faced recurrent data breaches due to weak user practices and uncoordinated security efforts. The company implemented a comprehensive security policy framework that included: Formalized acceptable use and password policies, reducing weak credential use. Regular employee awareness training aligned with email and web security policies to reduce phishing success. Clear incident response procedures enabling faster breach detection and containment. Periodic policy reviews to adapt to emerging threats and regulatory changes. Deployment of physical security controls like access cards and CCTV to protect IT infrastructure. Result: The company significantly reduced incidents, improved compliance, and built a securityaware culture. Information Security Standards-ISO, IT Act, Copyright Act, IPR. Cyber Crimes, Cyber Laws in India; IT Act 2000 Provisions, Intellectual Property Law, Copy Right Law, Semiconductor Law and Patent Law, Software Piracy and Software License. Here is a comprehensive overview of Information Security Standards, relevant laws, and regulations concerning cybercrime and intellectual property in India: Information Security Standards: ISO ISO/IEC 27001: The internationally recognized standard that specifies requirements for establishing, implementing, maintaining, and continually improving an Information Security Management System (ISMS). It focuses on managing information security risks systematically and protecting organizational information assets. The ISO 27000 series includes related standards such as ISO 27002 (code of practice for information security controls) and ISO 27005 (risk management). This framework helps organizations globally implement effective security policies and controls [1] [2] [3] [4] . IT Act, 2000 (Information Technology Act) India Enacted to provide a legal framework for electronic governance, digital signatures, and cybercrime regulation. Grants legal recognition to electronic records and digital signatures. Defines and penalizes cybercrimes such as hacking, data theft, identity theft, and cyber terrorism. Establishes regulatory authorities like the Controller of Certifying Authorities and Cyber Appellate Tribunal (later merged with Telecom Dispute Settlement Appellate Tribunal). Important provisions include blocking online content (Section 69A), penalties for hacking (Section 66), identity theft (Section 66C), and cyber terrorism (Section 66F). The Act was amended in 2008 to strengthen cybersecurity, address privacy concerns, and include provisions against child pornography and offensive content [5] [6] [7] [8] . Copyright Act, 1957 Protects original works of authorship including literary, musical, dramatic, and artistic works, as well as cinematographic films and sound recordings. Provides exclusive rights to creators over reproduction, adaptation, public performance, and distribution of their work. Defines infringement and legal remedies including civil and criminal penalties. Establishes Copyright Boards and Copyright Offices for registration and dispute resolution [9] [10] . Intellectual Property Rights (IPR) in India IPR covers patents, trademarks, copyrights, industrial designs, geographical indications, and layout designs of integrated circuits. Several laws govern IPR including the Patents Act (1970), Trade Marks Act (1999), Copyright Act (1957), Designs Act (2000), Semiconductor Integrated Circuits LayoutDesign Act (2000), and Protection of Plant Varieties and Farmers’ Rights Act (2001). Administered by various government bodies such as the Controller General of Patents, Designs, and Trademarks; Ministry of Human Resource Development for copyrights [11] [12] [13] . Cyber Crimes in India Include offences like hacking, identity theft, online fraud, cyberstalking, publishing obscene content, cyber terrorism, and data breaches. India has set up a National Cyber Crime Reporting Portal to empower citizens to report cyber crimes securely and anonymously. The Indian Cybercrime Coordination Centre (I4C) assists law enforcement agencies in addressing cybercrime through coordination and resource sharing [14] [15] . Cyber Laws in India Mostly encompassed under the Information Technology Act, 2000, supplemented by rules and guidelines such as intermediaries' regulations and data protection laws. Cyber laws govern electronic transactions, digital signatures, data protection, intermediary liability, and punish cyber offences with imprisonment and fines. The Digital Personal Data Protection Act, 2023, further strengthens privacy and data protection requirements in the online ecosystem [6] [7] [16] . Software Piracy and Software Licensing Software piracy is illegal copying, distribution, or use of software without proper licensing. It violates copyright laws protecting software as intellectual property. Software licenses specify how software can be used, distributed, and installed—types include proprietary, open-source, freeware, and shareware licenses. Semiconductor Law and Patent Law Semiconductor Integrated Circuits Layout-Design Act, 2000 protects layout designs of integrated circuits. Patent Law protects inventions and technical innovations, granting exclusive rights for exploitation and preventing unauthorized use.
 0
0
advertisement
Download
advertisement
Add this document to collection(s)
You can add this document to your study collection(s)
Sign in Available only to authorized usersAdd this document to saved
You can add this document to your saved list
Sign in Available only to authorized users