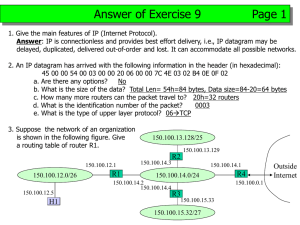
Address Resolution Protocol (ARP) & RARP The mechanism of mapping high-level addresses to Physical addresses is called as the Address Resolution 1 Overview • • • • • • • • Introduction When ARP is used? Types of ARP message ARP Message Format Example use of ARP ARP cache ARP Types RARP Introduction • low level network protocol • operates at Layer 2/3 of the OSI model which is usually implemented in the device drivers of network operating systems. • used by the Internet Protocol (IP), specifically IPv4, to map IP network addresses to the hardware addresses used by a data link protocol. LAN Address • MAC address allocation administered by IEEE • manufacturer buys portion of MAC address space (to assure uniqueness) • Analogy: (a) MAC address: like Social Security Number (b) IP address: like postal address • MAC flat address => portability – can move LAN card from one LAN to another • IP hierarchical address NOT portable – depends on network to which one attaches ARP and RARP • The ARP and RARP protocols perform the translation between IP addresses and MAC layer addresses • We will discuss ARP for broadcast LANs, particularly Ethernet LANs IP address (32 bit) ARP RARP Ethernet MAC address (48 bit) 5 ARP (RFC826) and RARP (RFC903) • ARP – ARP provides a dynamic mapping from an IP address to the corresponding hardware address. – It is dynamic since it happens automatically and is normally not a concern of either the application user or the system administrator. • RARP (Reverse Address Resolution Protocol) – RARP is used by systems without a disk drive but requires manual configuration by the system administrator. Address Resolution Techniques • Depends on protocol and hardware addressing scheme • Table look-up – Binding or mappings are stored in a table in memory, which the software searches when it needs to resolve an address • Closed-form computation – Computer’s hardware address can be computed from the protocol address using basic Boolean and arithmetic operations • Message exchange – Computers exchange messages across a network to resolve an address Address Translation with ARP (uses table look-up) ARP Request: Broadcasts an ARP request to all stations on the network: “What is the hardware address of Router137?” Argon 128.143.137.144 00:a0:24:71:e4:44 Router137 128.143.137.1 00:e0:f9:23:a8:20 ARP Request: What is the MAC address of 128.143.71.1? 8 Address Translation with ARP ARP Reply: Router 137 responds with an ARP Reply which contains the hardware address Argon 128.143.137.144 00:a0:24:71:e4:44 Router137 128.143.137.1 00:e0:f9:23:a8:20 ARP Reply: The MAC address of 128.143.71.1 is 00:e0:f9:23:a8:20 9 ARP operation Types Of Message • • • • There are four types of ARP messages: ARP request ARP reply RARP request RARP reply These are identified by four values in the “operation" field of an ARP message. Encapsulation of ARP packet ARP Packet Format Ethernet II header Destination address Source address Type 0x8060 6 6 2 ARP Request or ARP Reply 28 10 Hardware type (2 bytes) Hardware address length (1 byte) Padding CRC 4 Protocol type (2 bytes) Protocol address length (1 byte) Operation code (2 bytes) Source hardware address* Source protocol address* Target hardware address* Target protocol address* * Note: The length of the address fields is determined by the corresponding address length fields 13 ARP Packet fields • HARDWARE TYPE: specifies type of hardware interface for which the request is made (e.g., 1 for Ethernet) • PROTOCOL TYPE: specifies high level protocol address supplied in message (e.g. 0800 hex for IP) • HLEN and PLEN: specify length of fields for hardware address and protocol address respectively • OPERATION: specifies if this is an ARP request or reply message (1 for ARP request, 2 for ARP response, 3 for RARP request and 4 for RARP response) • HA and IP: hardware and IP addresses respectively 14 Use of ARP in four cases •Address mapping must be performed at each step along a path from the original source to the ultimate destination. 16 Example •A host with IP address 130.23.43.20 and physical address B2:34:55:10:22:10 has a packet to send to another host with IP address 130.23.43.25 and physical address A4:6E:F4:59:83:AB. The two hosts are on the same Ethernet network. Show the ARP request and reply packets encapsulated in Ethernet frames. Solution ARP request and reply Caching ARP Responses • Three packets traverse the network for each ARP transmission • Since sending an ARP request/reply for each IP datagram is inefficient and to reduce network traffic, ARP software on hosts maintain a table of current entries. The entries expire after specified time period so that no stale entries are found. Soft state (???) (adv and disadv???) • ARP manages the table as a cache • ARP uses the binding( if present ) without transmitting a request • If binding is not present – ARP broadcasts a request – Waits for a response – Updates the cache – Proceeds to use the binding ARP Cache • Essential to the efficient operation of ARP is the maintenance of an ARP cache on each host. • arp command: The –a option displays all entries in the cache. ARP MODULE •ARP Module involves five modules: a cache table, queues, an output module, an input module, and a cache-control module. •Cache Table •Queues •Output Module •Input Module •Cache-Control Module 21 ARP components QUEUES • ARP maintains a set of Queues – one for each destination, to hold the IP packets while ARP tries to resolve the Hardware address. • Packets for the same destination are enqueued in the same queue. 23 Original cache table used for examples Proxy ARP - Process where one system responds to the ARP request of another system. • Proxy ARP: Host or router responds to ARP Request that arrives from one of its connected networks for a host that is on another of its connected networks. •Advantage : simplicity; Disadvantage: scalability & security. Proxy ARP • Proxy ARP lets a router answer ARP requests on one of its networks. – This fools the sender of the ARP request into thinking that the router is the destination host, when in fact the destination host is "on the other side" of the router. – The router is acting as a proxy agent for the destination host, relaying packets to it from other hosts. Gratuitous ARP - occurs when a host sends an ARP request looking for its own IP address. – This is usually done when the interface is configured at bootstrap time or for detecting if an IP address has already been assigned. – Used when a host machine’s network interface corrupts, and need to be changed, the machine informs the other machine to let them update the change in their table. – Used by host to determine whether another host is also configured with its IP address. – Sent with S and D address being the same. The other machines respond as if it was a normal ARP request. TTL value of cache entry • The TTL period varies from system to system, usually from 2 to 20 minutes, and will increase to a greater number of minutes if more data from these temporary entries is requested within the allotted TTL period. The TTL period for • windows NT has a default of two minutes, • windows 2000 has a default of 10 minutes, • and solaris has a default of 5 minutes. • ARP caches of routers can be much longer -The cisco IOS router having a cache time of 4 hours. • For some computers, entries that are static usually remain on the cache table permanently or until the computer is rebooted. The TTL periods can be adjusted on most systems as well. Summary • Used to find the physical address of a target device on the local physical network, given only the target’s IP address • Mechanism: – The source broadcasts a special packet asking the device with target IP address to respond with a message carrying the (IP address, physical address) mapping – All devices on the local physical network receive the broadcast, but only the target recognizes its IP address and responds to the request. The other devices updates the information about the source machine in their cache. – When the source receives the reply, it sends the packet to the target using the target’s physical address and places the mapping in its cache (a cache is used to prevent repeated broadcasts for the same destination) 29 Summary • ARP refinements – Source includes its <IP address, physical address> mapping in the ARP request anticipating the target’s need for it in the near future. This avoids extra network traffic • When all machines receive the ARP request broadcast, they can store the address mapping in their cache. ?(Do they? And Why?) • ARP is used when an IP to physical address mapping changes to notify hosts on the network of the change • ARP messages are encapsulated in MAC frames. A special value in the type field of the frame is used to indicate that it is carrying an ARP message (0806h is used for ARP) • Entries in the local ARP cache for each host time out after a certain period 30 Summary • ARP is a basic protocol in almost every TCP/IP implementation, but it normally does its work without the application or the system administrator being aware. • Hides the physical layer addressing. • ARP along with specialized versions – Proxy ARP – Gratuitous ARP Vulnerabilities of ARP • • • Since ARP does not authenticate requests or replies, ARP requests and replies can be forged. ARP is stateless. ARP replies can be sent without a corresponding ARP request. According to ARP protocol specification, a node receiving an ARP packet ( REQUEST or Reply) must update its local ARP cache with the information in the source fields, if the receiving node already has an entry for the IP address of the source in its ARP cache. (This applies for ARP request packets and for ARP reply packets) Typical exploitation of these vulnerabilities: • • A forged ARP request or reply can be used to update the ARP cache of a remote system with a forged entry( ARP poisoning) This can be used to redirect IP traffic to other hosts. 32 ? 1. What happens if an ARP Request is made for a non existing host? 2. Where is ARP cache table stored? ANS: 1.Several ARP requests are made with increasing time intervals between requests. Eventually, ARP gives up. 2.Stored in RAM and are lost at restart/shutdown but not at logoff. 33 RARP •The RARP request packets are broadcast; the RARP reply packets are unicast. RARP packet •Encapsulation of RARP packet Alternative Solutions to RARP •When a diskless computer is booted, it needs more information in addition to its IP address. It needs to know its subnet mask, the IP address of a router, and the IP address of a name server. RARP cannot provide this extra information. New protocols have been developed to provide this information. Protocols BOOTP and DHCP can be used instead of RARP.