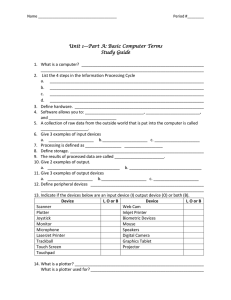
See discussions, stats, and author profiles for this publication at: https://www.researchgate.net/publication/258100839 A taxonomy of biometric system vulnerabilities and defences Article in International Journal of Biometrics · January 2013 DOI: 10.1504/IJBM.2013.052964 CITATIONS READS 27 2,304 2 authors: Yogendra Narain Singh Sanjay Kumar Singh Institute of Engineering & Technology - Lucknow Indian Institute of Technology (Banaras Hindu University) Varanasi 51 PUBLICATIONS 822 CITATIONS 172 PUBLICATIONS 2,511 CITATIONS SEE PROFILE Some of the authors of this publication are also working on these related projects: endometrial innate immunity View project Prognostics and Health Management (PHM) View project All content following this page was uploaded by Yogendra Narain Singh on 21 May 2014. The user has requested enhancement of the downloaded file. SEE PROFILE Int. J. Biometrics, Vol. 5, No. 2, 2013 A taxonomy of biometric system vulnerabilities and defences Yogendra Narain Singh* Department of Computer Science and Engineering, Institute of Engineering and Technology, Gautam Buddh Technical University, Lucknow – 226 021, India E-mail: singhyn@gmail.com *Corresponding author Sanjay Kumar Singh Department of Computer Engineering, Indian Institute of Technology (BHU), Varanasi – 221 005, India E-mail: sks.cse@itbhu.ac.in Abstract: The interest in biometric technology is received much attention in the recent years. However, the security issue still persists the main challenge for the reliable functioning of biometric-based authentication systems. Much has been reported on the vulnerabilities of biometric systems that breach the security and user privacy. We present a high-level classification of biometric system vulnerabilities and discuss the defence techniques of these vulnerabilities. We present a multidimensional threat environment of the biometric systems that includes faults, failures and security attacks. A framework of biometric security attacks on man-machine model is presented and the system vulnerabilities are represented using Ishikawa’s diagram. The provable defence techniques such as biometric vitality detection and biometric template protection are critically evaluated, in particular, a classification of current state-of-the-art of vitality detection techniques of commonly used biometrics is proposed. Our main contributions include: (1) propose a taxonomy of biometric system vulnerabilities; (2) present a framework of biometric security attacks using man-machine model; (3) representation of vulnerabilities using Ishikawa’s diagram; (4) an evaluation of defence techniques of these vulnerabilities. Keywords: biometrics; authentication; vulnerabilities; vitality measures; template protection; security; defences. Reference to this paper should be made as follows: Singh, Y.N. and Singh, S.K. (2013) ‘A taxonomy of biometric system vulnerabilities and defences’, Int. J. Biometrics, Vol. 5, No. 2, pp.137–159. Biographical notes: Yogendra Narain Singh is an Associate Professor in the Department of Computer Science and Engineering at Institute of Engineering and Technology, Gautam Buddh Technical University, Lucknow, India. He teaches courses on pattern recognition, soft computing and machine intelligence. He authored two books: Discrete Mathematical Structures (2010), Wiley, New Delhi and Mathematical Foundation of Computer Science (2005), Copyright © 2013 Inderscience Enterprises Ltd. 137 138 Y.N. Singh and S.K. Singh New Age International, New Delhi. He has published over 20 research articles on information security, biometrics and soft computing. Sanjay Kumar Singh is working as an Associate Professor with Department of Computer Engineering at Indian Institute of Technology, Banaras Hindu University IIT (BHU), Varanasi, India. He is a co-author of more than 50 technical publications. His research interests include image processing, biometrics methods and human computer interaction. 1 Introduction Biometric systems are becoming popular for security and authentication in most of the IT community, but preserving the systems from threats that breach their security is a potential challenge. Commonly used biometric systems authenticate a person by capturing his/her facial or iris images, scanning the fingerprints or recording the voice or speech samples. Persons authentication using biometric is attractive because the authenticate process principally based on those characteristics that are unique and measurable, in addition those are something that cannot be easily stolen and shared to others. A significant difference between the traditional identity management system and the biometric-based authentication system lies on the fact of matching process, i.e., error-free matching or error-tolerance matching. Unlike to a traditional identity management system (e.g., passwords, tokens or PINs) that results the authentication request to a simple ‘yes’ (completely matched) or ‘no’ (non-matched) outcome, a biometric security system results the authentication request to how much similar or dissimilar the biometric query is to its counterpart stored in the database. Although the biometrics are unique among individuals but their representation may vary during measurements. The variations in the biometric sample can be resulted due to the acquisition environment or users interaction to the acquisition device. That yields the inter-users similarity or intra-users dissimilarity. In order to fix the variability level of the biometric data such that not to reject many authorised users or not to accept many unauthorised users may open the space to intruders to making the system vulnerable and circumvent its security. Instead, the framework of a biometric system that includes data acquisition, processing, storing of templates and matching can also be threaten by an adversary that result the problems of authentication accuracy, reliability, robustness against fraudulent attacks, secrecy of biometric data and privacy protection. A practical biometric system which is employed to different applications can perform better and achieve the desired accuracy, but it is highly vulnerable to simple methods that can circumvent the security (Dunstone and Poulton, 2011). The methods includes the synthetic reproduction of anatomical identities, e.g., acquisition of facial images or lifting of latent fingerprints; and the imitation of behavioural identities, e.g., reproduction of handwritten signature or producing similar voices. Further, a replay of stored information or false data can also be injected in the processing chain whereas the biometric features extracted from the raw data can be copied as input to the biometric process and spoof the system. The biometric system vulnerabilities that are resulted from spoof attacks are shown in Figure 1. A taxonomy of biometric system vulnerabilities and defences Figure 1 139 A vulnerable biometric system resulting from spoof attacks (see online version for colours) Most often a practical biometric system suffers some degree of security threats, therefore the likelihood of success to make the system vulnerability resistance depends on analysing what kind of attacks it may be faced and what are their nature. Maltoni et al. (2009) have presented a typical threat framework of a fingerprint recognition system. It includes the following threat vectors: denial-of-service (DoS) that restricts the access right of the privileged users. Circumvention refers the misleading of access rights and gaining access by the unauthorised users. Repudiation includes the threats where a malicious user deliberately denies having accessed the system. Collusion and coercion threats refer the situation where an attacker is being helped by the privileged user like an administrator and the legitimate user are forced to help the attackers, respectively. Roberts (2007) has reported the attack vectors of a biometric system in the context of a risk-based approach. Most of the studies including the cited ones have presented the attacks concerning to spoof approaches and a limited work has been found to biometric system faults and failures. We present a comprehensive look on the biometric system vulnerabilities including the faults, failures and security attacks. In this paper we present a high-level categorisation of security threats of a biometric system and discuss the provable defences of these security threats. We present a taxonomy of the biometric system vulnerabilities in a holistic and systematic manner. We discuss the threat vectors of a biometric system in the context of faults, failures and security attacks. We present a multidimensional threat environment of a biometric system and representing their effects using Ishikawa’s diagram. As a countermeasure of biometric system vulnerabilities, different techniques have been proposed in the literature that is for the need of a reliable vitality testing and secrecy of the biometric data. We critically evaluate each of these defence techniques and discuss their effectiveness in protecting the biometric system from threats and preserving individual’s privacy. In particular, a classification of the current state-of-the-art of the vitality detection techniques of commonly used biometrics such as, fingerprint, face and iris is given. We examine biometric template protection techniques such as template transformation and biometric-cryptosystem used by different biometrics and estimate their performances on the datasets and the test conditions that have used for the experiment. 140 Y.N. Singh and S.K. Singh The rest of the paper is structured as follows: a taxonomy of biometric system vulnerabilities are given in Section 2. To effectively guard against vulnerabilities, the probable defences are described in Section 3. In Section 4, a discussion on the effectiveness of different defence techniques is presented. Finally, the conclusions are drawn at the end, in Section 5. 2 Biometric system vulnerabilities The biometric security systems operate on different scenarios. It authenticates individuals during the online (offline) access of the system like network (non-networked) applications or within a security perimeter like inside home or office. Other scenarios of these security systems are to authenticate individuals at physical entry with non-repudiation like restricted area of airport or the remote access with non-repudiation like web-based e-commerce applications. Depending upon the different scenarios, various types of vulnerabilities occur in the biometric systems. The likelihood of biometric system vulnerabilities, their nature and effects that breach the security of the authentication process have been analysed (Maltoni et al., 2009; O’Gorman, 2003; Ratha et al., 2001; Uludag and Jain, 2004; Jain et al., 2008; Roberts, 2007). Mainly, the security of a biometric system can be breached at one or more levels of its system design such as data acquisition, transmission channel or at the database where biometric templates are stored. In general, vulnerabilities cause failure to a biometric system primarily due to threats that can affect a system during its entire life. The life cycle of a typical security system consists of a development phase and a use phase (Laprie et al., 2004). The development phase of a biometric system includes all activities from starting to their ends, e.g., pre-processing of acquired biometric sample, data representation, feature extraction, and matching such that it has passed all tests successfully and ready to use. During development phase, development faults may be introduced into the system due to the system interaction with the development environment (e.g., lacking competence or having malicious objectives of developers, inadequate availability of development or testing tools, etc.). The use phase starts when the system is ready to use and starts servicing to the users. During the use phase, a biometric system interacts with its use environment (e.g., users, administrators and intruders) and may be adversely affected by faults originating in it. During service delivery, a service failure like incorrect or no service is delivered at the service interface. An intentional shutdown of the service or a service without results are some of the other common threats that need to be addressed. At the highest level, the threats that result the vulnerabilities in a biometric system can be classified as: 1 faults 2 failures 3 security attacks. A tree representation of the threats of a biometric system that breaches its security is shown in Figure 2. A taxonomy of biometric system vulnerabilities and defences Figure 2 141 A tree representation of security threats of a typical biometric system (see online version for colours) 2.1 Biometric system faults Biometric system faults include development faults (e.g., faults occurring during its development phase), physical faults (e.g., faults that affect the hardware components) and the external faults that are resulted from interaction with the use environment. The examples of some developments faults are software aging (Grottke et al., 2008), data corruption and storage space fragmentation (Bairavasundaram et al., 2008). There are some faults that result from human actions such as the absence of actions when the actions are required or performing wrong actions deliberately, these faults are human-made faults. The objectives of human-made faults are: DoS, accessing of secure information, improperly modify the system life cycle and disruption of services. Depending upon the objectives of manager or users these faults may be malicious or non-malicious. The objective of malicious faults is causing harm to system while the non-malicious faults are resulted from the mistakes such as unintended actions of which manager and user is not aware or deliberate faults that are resulted from wrong decisions. Trojan horses, trap doors, logic bombs, viruses or worms are some of the examples of malicious faults. Since the interaction faults occur during the use phase of a system, therefore they are all operational faults such as wrong setting of system parameters that may affect performance, storage, networking, security and privacy (Gray, 2001). 142 Y.N. Singh and S.K. Singh 2.2 Biometric system failures Biometric system failures can be characterised as the deviation from implementation of correct system functions. Generally, a system failure includes service failures, development failures and security failures (Laprie et al., 2004). A service failure occurs when the delivered service deviates from the correct service. The development failures result from the development faults. A development failure causes the development process to be terminated before the system is accepted for use and placed into service. It can occur at any level of system design due to inefficient imaging, improper data representation or improper matching. The development failures are primarily occur due to unclear or misleading estimate of the complexity of the system to be developed. It includes: inadequate design with respect to the functionality or performance goals, faulty or incomplete specifications, inadequate fault removal capability and faulty estimates of development costs. For example, the Unique Identification Authority of India (UIDAI) programme of the Government of India aims to provide biometric-based unique identification (UID) number to all its citizen is now struggling from the challenges. The success of UID programme is questioned because the complexity (e.g., technical, social or financial) of such a mega project have not been estimated in depth. The UID authority always underestimated the complexity of this project (Singh, 2011). Therefore, we should not surprise if an ambitious project like UIDAI fails to achieve their objectives. If it happens, then the most severe part of this project failure would be the loss of money that will cross 30 US$ billion which is more than the cost of AAS system that had been ended due to complete development failure (US Department of Transportation, 1998). A security failure occurs when a system suffers service failures more severely than acceptable. It may be due to the setting of very high attributes such as efficiency, reliability, integrity, confidentiality, safety and maintainability. The security failures are the serious issues to a system when the probability of false accepts and the probability of false rejects become high. The limited individuality of a biometric features also leading to incorrect authentication and thus the systems are vulnerable to security failures. The interclass similarity and intraclass dissimilarity of biometric features cause a failure to the system due to fraudulent match and fraudulent non-match, respectively. In addition, the presence of inherent noise and artefact at sensors can also lead to security failures. 2.3 Biometric security attacks A biometric security system typically works in a man-machine model. Here machine refers an auxiliary system comprising hardware and software components of a biometric system including its infrastructural components. The man refers one or more person(s) that are responsible for the proper functioning or supervising the system. An adversary can attempt to harm a biometric system by targeting on the machine or targeting on the man supervising the system in a number of ways. Ratha et al. (2001) have highlighted different sources of adversarial attacks on a machine of a biometric system. We present a modified framework of attack points in a man-machine model of a typical biometric system as shown in Figure 3. A taxonomy of biometric system vulnerabilities and defences Figure 3 143 Modified framework of attack points in a man-machine model of a typical biometric authentication system (see online version for colours) Notes: The attacks type (1) are user level attacks, attacks type (2) to (6) and (8) to (9) are on components and their interfaces while attacks on biometric templates are depicted by type (7). Attacks of type (10) are on supervisory bench. Martinez-Diaz et al. (2011) have classified the biometric system attacks into direct and indirect attacks. Former refers the attacks of fake biometric samples with an aim to spoof the sensor and trying to impersonate a real user. It is worth noting that the attackers classified under direct attacks require any specific knowledge of the targeted biometric system such as its development phase, e.g., data representation or matching. Indirect attacks include the rest of types reported by Ratha et al. (2001) such as the attacks on communication channel and the attacks on template database. In order to perform the indirect attacks, attacker must know the specific information about the system such as the communication protocol, template format or matching algorithm. Moreover, the attackers need physical or logical access to internal parts of the system that is not available to the user. We can classify the attacks on machine that are concerning to development phase and use phase of a biometric system as: 1 user level attacks 2 attacks on components and their interfaces 3 attacks on biometric templates. 144 Y.N. Singh and S.K. Singh 2.3.1 User level attacks The user level attacks occur mainly due to presenting of fake biometric samples to a biometric system for identity verification. These attacks correspond to the attack type (1) as shown in Figure 3. A fake biometric sample can be a fake finger made of gelatine, a digital facial image or a replay of recorded voice. The commonly used biometrics, e.g., face, fingerprint, iris and voice are not secrets. People leave their physical prints of finger on everything they touch, iris patterns can be observed anywhere they look, faces are visible and voices are being recorded. The presence of biometric prints publicly, offer an opportunity to intruders to lift these prints and copy them as real. The digital sample of a biometric identity can be obtained covertly from the system and replay the forge sample at the acquisition sensor. These attacks are common on the systems that do not have sufficient security measure to distinguish between fake and genuine biometric prints and thus deceived by intruders. 2.3.2 Attacks on components and their interfaces The components of a biometric system that are highly susceptible to adversarial attacks include quality checker (preprocessing), feature extractor, template database and matcher. The examples of these attacks are the replay of raw biometric print or the injection of false data in the processing chain of a system as depicted by attacks type (2) and (3), respectively (see for instance Figure 3). At the feature extractor component the biometric features extracted from the raw data can be overridden [attacks type (4)] or a synthetically prepared feature vector can be injected as a test vector for matching [attacks type (5)]. One approach that produces the synthesised templates is described as hill-climbing (Adler, 2003). This technique works iteratively and improve the synthesised features until it matches falsely to the stored template. While these attacks are taken on the system a legitimate user neither noticed any exception nor presage from the system, however it continues to provide them access. Attacks on matcher to override the match scores in order to change an impostor’s score to a higher passing score are avenues of attacks of type (6). The attacks type (7) target the template database with an aim to add, modify or delete user information, we will discuss these attacks separately. The attacks type (8) intercept the transmission channel to control the flow of template information and override with tempered information. Finally, attacks type (9) aim to override the matching decision that can result acceptance to an impostor and rejection to a genuine user. The interfaces of different components are attacked with an aim to hide the intermediate code of a component and intercept the information reaching to the next component. For example, the code generated at feature extractor can be intercepted by the malicious programs like Trojan horses or logic bombs and a new (forge) set of features as desired by an adversary is produced. Similarly, a matcher can be attacked by trap doors or viruses so that it bypasses the matching process or it always produces the higher matching scores and thus circumvent the system. 2.3.3 Attacks on biometric templates Templates are the key samples of a biometric identity collected from the enrolled population for their authentication. The biometric identity of an individual is not a digital certificate that can be issued by a third party when the templates are stolen form the A taxonomy of biometric system vulnerabilities and defences 145 database. For example, an iris-based recognition system authenticates individuals using their iris codes. If someone steals the templates of iris codes then the only possibility left to the users is to use the iris of other eye, nothing else. In case of voice recognition system, if the voice print is stolen by an adversary then it remains stolen for whole life and the user’s identity can never return to a secure situation. Different scenarios are reported when the template of a legitimate user is attacked by an adversary. An adversary can replace the genuine template from fake template that results an adversary got access to the system. An adversary can modify or corrupt a genuine template that results a DoS to a legitimate user. In addition to non-secure infrastructure, a biometric system is also vulnerable to various attacks that exploit the administrative loopholes. The administrative bench that is responsible for efficient functioning of a biometric system can be targeted by an adversary. We classify these attacks as the attacks on supervisory bench. Figure 4 Ishikawa’s diagram for representing biometric system vulnerabilities (see online version for colours) Integrated System Failure Security Failures Individuality of biometric Overestimation of attributes Mailfunctioning Service Failures System Failures Enrollment Fraud Development faults Attacks on Supervisory Bench Development Failures External Faults Incorrect interaction Physical Faults of the user Attacks on Components and their Interfaces Operational faults DoS Human-made faults Replay Synthesized Template Non-malicious faults System Faults Trojan horse Malicious faults Inherent noise and artifact Inefficient feature extraction Incorrect decision making Inefficient sensing Inefficient matching Development Faults Steal Modify Fake biometric Sample Attacks on Biometric Templates Attacks on Machine User Level Attacks 2.3.4 Attacks on supervisory bench The attacks of type (10) are shown in Figure 3 target the administrative bench or the group of persons that are responsible for safe and secure functioning of the system. If a 146 Y.N. Singh and S.K. Singh system is functioning under inadequate administrative measures then it is vulnerable and recumbent to adversarial attacks. For example, the users can be frightened and forced by an adversary to provide their biometric samples. An authority can itself do malfunctioning such as to modify the system parameters or to make them available to adversaries for incursion by a hidden agreement between them. One of the harmful effect of these attacks is being on the privacy of the individuals. While accessing the personal data of individuals illegally, the adversary can disclose their privacy that may sickening their personal and social life. Last but not the least, the administrative bench can change the access rights of an individual in their interest. For example, when rights are curtailed that may cause false rejects or DoS. When the rights are increased that may cause false accepts. Alternatively, the security of the biometric system breaches in both ways. The vulnerabilities of a biometric system discussed in this section can be represented pictorially by Ishikawa’s (1986) diagram. Using this diagram, the multiple threat vectors that can make the system vulnerable are represented and shown in Figure 4. It shows the cause and effect of various security threats of a generic biometric system that leads to integrated system failure. 3 Biometric system defences Biometrics are unique among individuals but they are not secrets. Biometric information is irrevocable and hard to regain identity (Watson, 2007). Therefore, the challenge is to design a secure and robust authentication system from the system components that are neither secrets nor revocable. A typical biometric system works by first storing the features extracted from an enrolled biometric identity as templates in the system database and then matching the template features with those extracted from the biometric information presented during subsequent authentication attempts. A biometric security system works perfectly if the system guaranteed that the biometric features are extracted from a person to be authenticated and then it matches the template features in the database (Schneier, 1999). Ideally, no electronic authentication (eID) system is completely secured and no single protection mechanism is sufficient to protect the system comprehensively. But the sensible and practical measures can effectively reduce the risk of security threats to an acceptable level. There are a number of proved defensive techniques in practice that are effectively guard or reduce the risk of security threats and vulnerabilities of the biometric systems. The security techniques of a generic biometric system that are effective against system attacks can be grouped in two classes: 1 vitality detection 2 biometric template protection, whereas each class has its own appropriate security mechanisms. Designing of salient feature detectors and robust matchers are other effective countermeasures that can reduce the faults and failures of a biometric system. In addition, practical approaches like use of multiple biometrics, good governance practices and physical security can also effective in reducing the security threats of the biometric systems. A taxonomy of biometric system vulnerabilities and defences 147 3.1 Vitality detection Vitality detection is a potential countermeasure against the spoof attacks of a biometric system. It insures that the presented biometric sample is live not fake. In addition, it insures that the presented biometric belongs to a live individual who was originally enrolled in the system and not just any live person with or without fake biometric. The objective of vitality detection is an actual measurement of biometric sample that is being taken from a legitimate and live individual, who is indeed present at the time of enrolment. The successful functionality of vitality detection techniques essentially improve the reliability of a biometric system because it enables the system to reluctance against artefact to be enrolled and ensuring that no non-live sample is accepted. Although, biometric systems use individual’s physiological information for his/her authentication, that hardly detects its vitality. It has however shown that the biometric systems can be spoofed using fake samples, e.g., a fingerprint system can be spoofed by an artificial finger prepared from gelatine, silicon, latex or Play-Doh (van der Putte and Keuning, 2000; Matsumoto et al., 2002). The static and high resolution images of face and irises can spoof the face recognition system (Schuckers, 2002; Adler, 2003; Kollreider et al., 2005) and iris recognition system (Matsumoto, 2004, 2007), respectively. Figure 5 Proposed classification of current state-of-the-art vitality detection techniques of commonly used biometrics (see online version for colours) In order to assure the vitality signs from biometric samples, different techniques have been proposed in literature. Singh and Singh (2011) have proposed a classification of current state-of-the-art vitality detection techniques of commonly used biometrics (e.g., fingerprint, face and iris) which is shown in Figure 5. The existing techniques can broadly be divided into two classes: 1 hardware-based techniques 2 software-based techniques. Hardware-based techniques detect the vitality signs from the available biometric sample during the acquisition stage. These methods use an extra hardware to acquire the life signs from presented biometric data. For example, the techniques used to measure the vitality signs from fingertip placed on sensor include temperature (Kallo et al., 2001), 148 Y.N. Singh and S.K. Singh odour (Baldissera et al., 2006), pulse oxiometry (Reddy et al., 2008), blood flow (Lapsley et al., 1998) and spectral information (Coli et al., 2007). An integration of specific device at the sensor increases the cost of the system while the additional circuitry could make it invasive to the users. Figure 6 (a) Fingerprints: real, silicon and gummy (Matsumoto et al., 2002) (b) Faces: fake and live (Jee et al., 2006) (c) Irises: real and fake (Daugman, 1999) (see online version for colours) (a) (b) (c) Note: All from left to right. Software-based techniques detect vitality signs from biometric samples during processing stage. The rationale behind those techniques are to extract any one peculiarity of live signs from a single sample (static techniques) or from multiple samples (dynamic techniques) that differ from artificial reproduction. In a fingerprint recognition system, the vitality signs of a biometric sample can be detected by analysing a single image of fingerprint using skin perspiration (Parthasaradhi et al., 2005), morphology characteristics (Moon et al., 2005), spectrum analysis (Chang et al., 2011) and quality related features (Galbally et al., 2012); or multiple images of a fingerprint using skin distortion analysis (Antonelli et al., 2006). Similarly, a live sample of face or iris can be distinguished from their fake images by analysing the Fourier spectrums (Li et al., 2004; Daugman, 1999), statically. An image sequence of face is used to detect the live signs by analysing the movement of eyes (Jee et al., 2006) and spatial 2D motions on the face (Kollreider et al., 2005), dynamically. The image sequence of iris can detect the life signs using pupillary movements and the triggering of pupils with illumination (Daugman, 1999). 3.1.1 Multimodal techniques of vitality detection The measures of vitality detection can be enhanced by acquiring multimodal data for identity verification. It has been shown that inclusion of more than one biometric information complementing each other for robust authentication (Chetty and Wagner, 2004; Bredin and Chollet, 2007). Chetty and Wagner (2004) have proposed a system that combines the face information with the voice information. The combined system of face and voice can be able to verify the vitality of biometric samples through synchronisation between movements of lips and the voice prints recorded in the system. Bredin and Chollet (2007) have proposed a technique that fuses voice and visual biometrics after their analysis at classification level. The two systems of face and voice recognition are run independently and verify the correspondence between visemes and phonemes for vitality detection. Singh et al. (2012) have proposed a multibiometric system that fuses the face and the fingerprint biometrics with the electrocardiogram (ECG). The ECG has suggested a vitality-enabled biometric (Singh and Gupta, 2009, 2011) that may provide a good check against fake enrolments. The reported performance of the aforementioned system is optimum and claimed to be robust against spoof attacks. A taxonomy of biometric system vulnerabilities and defences 149 3.1.2 Performance evaluation of vitality detection techniques Despite a variety of vitality detection techniques are known but the problem of assuring vitality from biometric samples is practically harder (Toth, 2005). Independent measure of vitality detection shows that the matching difference of distribution between live and fake samples is smaller than the matching difference of distribution between genuine and impostor samples. Therefore, spoofing the system in absence of vitality detection technique causes a false match without doing the adversary effort. Moreover, the performance of vitality detection techniques can be measured by computing the proportion of transactions with a fake sample that are incorrectly matched (FMRNL) and the proportion of transactions with a live sample that are incorrectly non-matched (FNMRL). Equal error rate (ERR) between FNMRNL and FMRL can also be used for this purpose. The testing results obtained from the methods associated with different biometrics cited are shown in Table 1. However, it is harder to ascertain any conclusion to the effectiveness of one vitality detection technique to another. Table 1 Biometrics Fingerprint Performance estimates of vitality detection techniques associated to different biometrics Techniques and datasets used Power spectrum (Coli et al., 2007) – 720 live and fake fingerprints (36 subjects). EER: 0.6–6.3% Perspiration (Parthasaradhi et al., 2005) – 33 Play-Doh fingerprints (33 subjects). Classification accuracy ~90% Fingertip morphology (Moon et al., 2005) – 23 live and 34 fake fingertips. Face Performance EER: N/R Skin deformation (Antonelli et al., 2006) – 90 live and 40 fake fingerprints (45 subjects). EER: 11.24–19.63% 3D head movements (Kollreider et al., 2005) – 200 live and fake images. Classification error: 0.75% Facial micro-movements (Jee et al., 2006) – 100 live and fake faces. Multimodal Face and voice (Chetty and Wagner, 2004) – 19 female and 24 male (43 subjects). Audio-visual sequences (Bredin and Chollet, 2007) – 624 synchronised and 14,352 unsynchronised audiovisual sequences (26 subjects). Face, fingerprint and ECG (Singh et al., 2012) (78 subjects). FMRNL: 0.01%, FNMRL: 0.08% EER: 1–5.1% EER:17–32% EER: 0.2% Notes: EER: equal error rate, FMRNL: false match rate of non-live sample, FNMRL: false non-match rate of live sample and N/R: not reported. 3.2 Biometric template protection To effectively guard against biometric system vulnerabilities, it is important to protect the biometric templates stored in the database. Biometric templates are the key documents used for establishing authenticity of the individuals. Therefore, templates are essentially kept secure and protected from the reach of intruders. If the security of database templates is breached then security of the system is compromised adversely. 150 Y.N. Singh and S.K. Singh Ideally, a template protection scheme should satisfy a number of requirements (Jain et al., 2008). First, the stored template should not exhibit the original sample that can be replayed to the system. It should be computationally harder for an adversary to guess and revoke the original sample or any close replica from the stored data. Secondly, template database must be anonymous, i.e., the biometric data of an individual can be used as multiple and varied identifiers for different applications without correlating with one other. For example, if the biometric sample of an individual is compromised then a fresh and new sample can be generated from the same biometric identity of that individual. Finally, the template protection mechanism should not lead any significant degradation in matching performance, i.e., increase of EER of the biometric system. A number of hardware- and software-based techniques have been proposed to protect the stored template present in the system (PlusID, Ratha et al., 2007; Wang and Hatzinakos, 2009; Chin et al., 2006; Teoh and Chong, 2010; Bolle et al., 2002; Soutar et al., 1998; Juels and Sudan, 2002; Hao and Chan, 2002; Clancy et al., 2003; Hao et al., 2006). Hardware-based techniques use smart cards or stand-alone biometric system-ondevices as shown in Figure 7(a). An example of such a solution is a commercial product called privaris PlusID. The main limitations of the hardware-based techniques are that they are expensive and inconvenient mainly because a user has to carry them always and are prone to being lost. In the software-based techniques, the biometric features are integrated with some external key and the resultant data is stored in the system database instead of the original biometric template. The software-based template protection techniques include feature transformation and biometric cryptosystems. Former technique transforms the biometric features of an individual sample using a user specific key such that the matching is being performed in the transformed domain. Latter technique associates a cryptographic key with the biometric template of an individual to generate biometrically-encrypted data which does not reveal any information about the original template or the cryptographic key. 3.2.1 Template transformation Consider F is a transformation function applied to a biometric template T which generates its transformed information Fk(T), where k is a user’s specific key. Let Q be a biometric query then using the transformation function F its transformed information Fk(Q) is generated. Let M be a matching algorithm that performs matching between biometric samples T and Q and returned a match score. A matching decision either accept (1) or reject (0) can be taken on the basis of decision threshold λ, i.e., ⎧accept, if M ( Fk (T ), Fk (Q) ) ≥ λ Decision = ⎨ ⎩reject, otherwise. The schematic diagram of template transformation process is shown in Figure 7(b). The choice of function F should be non-invertible. Because, the non-invertible transform is strictly a one-way function. It means that for a given transformed information Fk(T) with an user’s key k, the original template T should not be revoked in a reasonable amount of time. Consequently, it is computationally harder for an adversary to invert a transformed template to its original form even if the user’s key is compromised. The key issues of a template transformation techniques are the selection of a transformation function that A taxonomy of biometric system vulnerabilities and defences 151 conserved the discriminability of template or query data and maintained the secrecy of user specific key utilised in the transformation process. Practically, it is harder to design a transformation function that meets both the requirements of discriminability and non-invertibility, simultaneously. Figure 7 (a) (a) The PlusID is a portable device with a built in fingerprint sensor (b) Schematic diagram of template transformation technique used for template protection in biometric security system (see online version for colours) (b) Note: Upon scanning a finger and matching it with the stored template, the device wirelessly transmits a secure key that can be used for authentication (http://www.privaris.com). In the literature, different non-invertible transformation functions have been proposed for different biometrics, i.e., fingerprint (Ratha et al., 2007), face (Wang and Hatzinakos, 2009), iris (Chin et al., 2006) speech (Teoh and Chong, 2010), etc. In general, the suitability of a transformation function depends on the selected biometric, characteristics of the feature set and the application area. The concept of cancellable biometric perpetrated by Bolle et al. (2002) as a security enhancing technique to produce anonymous biometric data is of great interest among biometric researchers. It protects the biometric system from unauthorised tracking of the individuals and restricting the possibility of cross-matching among different biometric databases, thus preserving an individual’s privacy. Ratha et al. (2007) have generated cancellable fingerprint templates using non-invertible transforms. They have proposed Cartesian, polar and surface folding transforms for minutiae data. Wang and Hatzinakos (2009) have addressed the problem of changeable face and privacy preserving face recognition. They have proposed a technique for generating cancellable faces using random projection in conjunction with a sorted index numbers. A cancellable iris biometrics, coined as S-iris encoding has been proposed by Chin et al. (2006). S-iris encoding combines iris feature and tokenised 152 Y.N. Singh and S.K. Singh pseudo-random number via iterated inner product and render a set of cancellable bit string. Teoh and Chong (2010) have presented a two factor cancellable formulation for speech biometric using probabilistic random projection. The method offered the protection of speech signal by hiding the actual speech feature through the random subspace projection process. The practical utilisation of biometric template security are reported in TURBINE (http://www.turbine-project.eu) and UIDAI (http://www.uidai.gov.in) projects. The aim of Trusted Revocable Biometric Identities (TURBINE) project is to commercialise eID through fingerprint biometrics and enhanced privacy protection. The research interest of the project is to do the identity verification in the transformed domain so that the data for authentication cannot be used to restore the original biometric information. In addition, anonymous data is to be created for different applications from an individual’s fingerprint whilst ensuring that these identities cannot be linked to each other. In UIDAI project the templates are secured using encryption-decryption criterion. The original biometric images of fingerprints, irises and face are archived and stored offline while only the encrypted information is stored on the server for verification purpose. Therefore, data used by automatic biometric identification system is anonymised as claimed by the authority. 3.2.2 Biometric cryptosystems In the recent past, researchers have drawn their attention on the fusion of two most latent security technologies, biometrics and cryptography. Biometrics is a security technology used to authenticate individuals using their body mark with a high degree of assurance while cryptography is used to assure the secrecy and authenticity of information in the communication channel. A fusion of biometrics and cryptography is referred as biometric cryptosystems (Soutar et al., 1998). A biometric cryptosystem associates a cryptographic key (k) to an individual biometric template (T) and generates the biometrically-encrypted data H = F(T, k). Biometrically-encrypted data is the helper data (H) that may not reveal any relevant information about the template sample or the cryptographic key. While the cryptographic key is being recovered at the time it matches to the query sample (Q), i.e., k = M(F(T, k), Q). The schematic diagram of biometric-cryptosystem process is shown in Figure 8. The key advantage of using biometric cryptosystem is that it stores the digital signature of an individual in the database instead of storing the original biometric template. Therefore, it creates anonymous database that eliminates the security and privacy concerns of the users. The critical issue of biometric cryptosystem is the evolvement of an optimal encryption technique that is being capable to handle the intra-individual variability of the biometric data. That is, we have to devise the error-tolerant encryption technique for the implementation of biometric cryptosystems for robust identity verification. In order to bridge the gap between the impreciseness of biometric data and the exactness of cryptography, different studies have been proposed in the literature (Soutar et al., 1998; Juels and Sudan, 2002; Hao and Chan, 2002; Clancy et al., 2003; Hao et al., 2006). A taxonomy of biometric system vulnerabilities and defences Figure 8 153 Schematic diagram of biometric cryptosystem technique used for template protection in biometric security system (see online version for colours) Soutar et al. (1998) have among the first who developed an earliest biometric encryption system that linked and retrieved a digital key using the interaction of fingerprint images. Juels and Sudan (2002) have proposed a cryptographic construction called a fuzzy vault that is capable to handle the intraclass variations present in the biometric data. It is operated in a key binding mode where users place a secret value in a fuzzy vault and lock it using an unordered set (e.g., minutiae in fingerprints). The ability of fuzzy vault is to work with the unordered sets and handles the intraclass variations making it a favourable solution for biometric cryptosystems. Hao and Chan (2002) have proposed a cryptosystem that generates the secret keys from online signatures. On the database of 25 subjects, they have collected ten signatures for each subject. For each signature they have defined 43 features like pressure, stroke, direction and speed etc. Feature coding is used to quantise each feature into bits that are concatenated to generate a strings of 0’s and 1’s. On an average 40-bits key entropy the system achieved the false non-match rate of 28%, false match rate of 1.2% and an equal error rate of 8%. Clancy et al. (2003) have proposed a fuzzy vault scheme for fingerprint and given the name fingerprint vault. The scheme is based on the location of minutia points which are recorded as real points form a locking set. A secret key is derived from these minutia points using polynomial reconstruction. Hao et al. (2006) have proposed a method to integrate the iris code into cryptographic application. They have shown that the keys are generated from iris biometric using error-correction that can be changed to produce different keys. The advantage of producing different keys for different applications is to make infeasible for an adversary to circumvent all systems simultaneously. The technique has evaluated on iris images of 70 subjects, with ten images from each eye. On a key length of 140-bits, an error free key can be reproduced reliably from genuine iris codes with a 99.5% success rate. 154 Y.N. Singh and S.K. Singh 3.2.3 Performance evaluation of template protection techniques The performance of template protection techniques such as template transformation and biometric-cryptosystem associated to different biometrics are shown in Table 2 and Table 3, respectively. The performance of template protection techniques is estimated on different datasets and different test conditions. Analysing the advantages and disadvantages of each methods it can be observed that the success of the cited template protection techniques have been limited due to the conditions imposed by many real applications. This is because the modified template based on the existing schemes increases the authentication error rate and demands more computation during matching, which is further compounded by the lack of standards for defining and storing modified templates. All of the presented techniques have just emerged and it is obvious that time is required until these techniques are truly applied. Table 2 Performance estimates of template transformation techniques associated to different biometrics Biometrics Techniques Datasets EER (%) Face (Wang and Hatzinakos, 2009) Random projection and Sorted index numbers FERET (Phillips et al., 1998) (1,020 subjects) 6.52–9.46 (10.41–18.20) Fingerprint (Ratha et al., 2007) Cartesian, polar and surface folding transformations IBM-99 optical (188 pairs) N/R Iris (Chin et al., 2006) S-iris encoding and pseudo-random number CASIA* (108 subjects) 1.00 (2.59) Speech (Teoh and Chong, 2010) Probabilistic random projection and text independent verification YOHO (Higgins et al., 1991) (138 subjects) LT – 2.98 (5.36) ST – 4.83 (3.98) Notes: LT: legitimate-token, ST: stolen-token and N/R: not reported. Equal error rate (EER) values in brackets show the performance on original samples. *http://www.sinobiometrics.com/casiairis.htm Table 3 Performance estimates of biometric cryptosystem techniques associated to different biometrics Biometrics Datasets Key size Fingerprint (Soutar et al., 1998) N/R 128-bits EER: N/R Fingerprint vault (Clancy et al., 2003) N/R 69-bits EER: N/R, FNMR: 30% Ten images of each eye (70 subjects) 140-bits FNMR: 0.5% Ten signatures each (25 subjects) 40-bits EER: 8%, FNMR: 28% and FMR: 1.2% Iris (Hao et al., 2006) Online signature (Hao and Chan, 2002) Performance Notes: EER: equal error rate, FNMR: false non-match rate and N/R: not reported. 4 Discussion Biometric systems are being widely used for reliable identity management, but the systems themselves are vulnerable to a number of security threats. Biometric security A taxonomy of biometric system vulnerabilities and defences 155 systems are recumbent to deliberate or inattentive security lapses that can lead to illegitimate intrusion, DoS or theft of individual’s sensitive information enrolled in the system. Among the described vulnerabilities that are related to the development and use phase of a biometric system, attacks on the stored biometric templates is a major concern. Because there is a strong linkage between an individual’s template and his/her identity, in addition the biometric templates are irrevocable. We believe that the available template protection techniques are not yet matured for handling large scale security applications. However, the choice of a template protection technique depends on the application scenario and its requirements. The vulnerabilities of a biometric system are mainly related to the apparent nature of the relevant information and limited vitality detection mechanisms incorporated in the system. It is not hard for an adversary to create a spoof biometric from a biometric sample of a genuine user or even a stored template is stolen and gain illegitimate access. Many state-of-the-art vitality detection techniques are known for different biometrics but it has been suggested that the simultaneously acquisition of multiple biometric identities from people during enrolment can be a good solution for detecting the vitality signs from biometric samples. On the other hand, bioelectrical signals such as the ECG or electroencephalogram (EEG) are emerging as new biometrics for individual authentication. Study suggests that the impulses of cardiac rhythm and the electrical activity of brain recorded in the ECG and EEG, respectively show unique features among individuals, therefore they can be suggested to use as biometric (Singh and Singh, 2012). The favourable characteristic to use the ECG or EEG as biometric is their inherent feature of vitality that signify the life signs which is a strong protection against spoof attacks. To effectively guard against vulnerabilities, different techniques have been proposed to protect the stored template. Moreover, the design of a template protection technique depends entirely on the representation of the biometric features. For example, a non-invertible transform is a good choice for minutia-based fingerprint features while biometric cryptosystem can be a good choice for a fixed-length binary representation of iris code. However, if the biometric samples have large intraclass variations then neither non-invertible transform nor biometric cryptosystem techniques are possible to apply. Despite the advantages of different template protection techniques, there is no sustained efforts have been seen for the adoption of such security technologies by the biometric industry. The reason may be due to lack of standards for designing and storing modified templates, computationally expensive matching process and increase in authentication error using modified templates. However, we believe that more secure techniques will weaken the security threats and provide confidence about the integrity of the system. 5 Conclusions As the use of biometric-based authentication become more popular, the security issue probably represents the most important concern that has to be addressed during the design of a biometric authentication system. Biometric systems are vulnerable against a number of threats. We have classified the threats of a biometric system as faults, failures and security attacks. A high-level categorisation of the biometric systems vulnerabilities is presented, in particular a multidimensional environment of vulnerabilities are represented by Ishikawa’s diagram. To guard against vulnerabilities, the defence 156 Y.N. Singh and S.K. Singh techniques such as vitality detection and biometric templates protection are critically reviewed. In particular, a classification of current state-of-the-art of vitality detection techniques of commonly used biometrics (e.g., face, fingerprint and iris) is given. We have critically reviewed the vitality detection techniques and evaluated their performances on the datasets and the test conditions used for the experiment. A template protection technique with provable security and acceptable recognition performance remains to be puzzled. The commonly used template protection techniques proposed in the literature such as biometric template transformation and biometric cryptosystem are discussed. The performance of template protection techniques are estimated on the datasets and the test conditions used in the experiment. We believe that the available template protection techniques are not yet sufficiently matured for large scale applications. References Adler, A. (2003) ‘Sample images can be independently restored from the face recognition templates’, Proc. Can. Conf. Elect. Comput. Eng. (CCECE), Montral, QC, Canada, pp.1163–1166. Antonelli, A., Capelli, R., Maio, D. and Maltoni, D. (2006) ‘Fake finger detection by skin distortion analysis’, IEEE Transactions on Information Forensics Security, Vol. 1, No. 3, pp.360–373. Bairavasundaram, L.N., Goodson, G.R., and Schroeder, B., Dusseau, A.C.A. and Dusseau, R.H.A. (2008) ‘An analysis of data corruption in the storage space’, Proc. 6th USENIX Conference on File and Storage Technologies, pp.223–238. Baldissera, D., Franco, A., Maio, D. and Maltoni, D. (2006) ‘Fake fingerprint detection by odor analysis’, Proc. International Conference on Biometric, ICB 2006, LNCS, Vol. 3832, pp.265–272. Bolle, R.M., Connell, J.H. and Ratha, N.K. (2002) ‘Biometric perils and patches’, Pattern Recognition, Vol. 35, No. 12, pp.2727–2738. Bredin, H. and Chollet, G. (2007) ‘Audiovisual speech synchrony measure: application to biometrics’, EURASIP Journal on Advances in Signal Processing, Article ID 70186, pp.1–11. Chang, S., Secker, J., Xiao, Q., Reid, B., Bergeron, A. and Almuhtadi, W. (2011) ‘Arficial finger detection by spectrum analysis’, Int. J. Biometrics, Vol. 3, No. 4, pp.376–389. Chetty, G. and Wagner, M. (2004) ‘Liveness verification in audio video speaker authentication’, Proc. 10th Australian International Conference on Speech Science & Technology, Sydney, pp.358–363. Chin, C.S., Jin, A.T.B. and Ling, D.N.C. (2006) ‘High security iris verification system based on random secret integration’, Computer Vision and Image Understanding, Vol. 102, pp.169–177. Clancy, T.C., Kiyavash, N. and Lin, D.J. (2003) ‘Secure smartcard-based fingerprint authentication’, Proc. 2003 ACM SIGMM Workshop Biometrics Method and Application (WBMA), pp.1–10. Coli, P., Marcialis, G.L. and Roli, F. (2007) ‘Power spectrum-based fingerprint vitality detection’, Proc. IEEE Workshop on Automatic Identification Advanced Technologies, AutoID, pp.169–173. Daugman, J. (1999) ‘Recognizing persons by their iris patterns: countermeasures against subterfuge’, in Jain, A.K., Bolle, R. and Pankanti, S. (Eds.): Biometrics: Personal Identification in Networked Society, Kluwer, Cambridge University, Cambridge. Dunstone, T. and Poulton, G. (2011) ‘Vulnerability assessment’, Biometric Technology Today, No. 5, pp.5–7. A taxonomy of biometric system vulnerabilities and defences 157 Galbally, J., Alonso-Fernandez, F., Fierrez, J. and Ortega-Garcia, J. (2012) ‘A high performance fingerprint liveness detection method based on quality related features’, Future Generation Computer Systems, Vol. 28, No. 1, pp.311–321. Gray, J. (2001) ‘Functionality, availability, agility, manageability, scalability – the new priorities of application design’, available at http://www.research.microsoft.com/ (accessed on June 2011). Grottke, M., Matias, R. and Trivedi, K.S. (2008) ‘The fundamentals of software aging’, Proc. IEEE Int’l. Symposium on Software Reliability Engineering, pp.1–6. Hao, F. and Chan, C.W. (2002) ‘Private key generation from online handwritten signatures’, Information Management & Computer Security, Vol. 10, No. 2, pp.159–164. Hao, F., Anderson, R. and Daugman, J. (2006) ‘Combining crypto with biometrics effectively’, IEEE Trans. on Computers, Vol. 55, No. 9, pp.1081–1088. Higgins, A., Bahler, L. and Porter, J. (1991) ‘Speaker verification using randomized phrase prompting’, Digital Signal Process., Vol. 1, pp.89–106. Ishikawa, K. (1986) ‘Guide to quality control’, Asian Productivity Organization, 2nd ed., White Plains, New York. Jain, A.K., Nandkumar, K. and Nagar, A. (2008) ‘Biometric template security’, EURASIP Journal of Advances in Signal Processing, Article ID 579416, pp.1–17. Jee, H.K., Jung, S.U. and Yoo, J.H. (2006) ‘Liveness detection for embedded face recognition system’, International Journal of Biomedical Sciences, Vol. 1, No. 4, pp.235–238. Juels, A. and Sudan, M. (2002) ‘A fuzzy vault scheme’, ISIT 2002, Lausanne, Switzerland, 408p. Kallo, P., Kiss, I., Podmaniczky, A. and Talosi, J. (2001) ‘Detector for recognizing the living character of a finger in a fingerprint recognizing apparatus’, Dermo Corporation, U.S. Patent No. 6,175,64. Kollreider, K., Fronthaler, H. and Bigun, J. (2005) ‘Evaluating liveness by face images and the structure tensor’, Proc. Fourth IEEE Workshop on Automatic Identification Advanced Technologies, pp.17–18. Laprie, A.J.C., Randell, B. and Landwehr, C. (2004) ‘Basic concepts and taxonomy of dependable and secure computing’, IEEE Transactions on Dependable and Secure Computing, Vol. 1, No. 1, pp.11–33. Lapsley, P., Less, J., Pare, D. and Hoffman, N. (1998) ‘Anti-fraud biometric sensor that accurately detects blood flow’, SmartTouch, LLC, US Patent #5,737,439. Li, J., Wang, Y., Tan, T. and Jain, A.K. (2004) ‘Live face detection based on the analysis of Fourier spectra’, Biometric Technology for Human Identification, Vol. 5404 of Proceedings of SPIE, Orlando, Fla, USA, pp.296–303. Maltoni, D., Maio, D., Jain, A.K. and Prabhakar, S. (2009) Handbook of Fingerprint Recognition, 2nd ed., Springer Professional Computing. Martinez-Diaz, M., Fierrez, J., Galbally, J. and Ortega-Garcia, J. (2011) ‘An evaluation of indirect attacks and countermeasures in fingerprint verification systems’, Pattern Recognition Letters, Vol. 32, No. 12, pp.1643–1651. Matsumoto, T. (2004) ‘Artificial fingers and irises: importance of vulnerability analysis’, Proc. 7th Int’l.. Biometrics Conference, London. Matsumoto, T. (2007) ‘Assessing the security of advanced biometric systems: finger, vein and iris’, Proc. 10th Int’l. Biometrics Conference, London. Matsumoto, T., Matsumoto, H., Yamada, K. and Hoshino, S. (2002) ‘Impact of artificial gummy fingers on fingerprint systems’, Proc. SPIE, Optical Security and Counterfeit Deterrence Techniques IV, San Jose, USA, Vol. 4677, pp.275–89. Moon, Y.S., Chen, J.S., Chan, K.C., So, K. and Woo, K.C. (2005) ‘Wavelet based liveness detection’, Electronics Letters, Vol. 41, No. 20, pp.1112–1113. O’Gorman, L. (2003) ‘Comparing passwords, tokens, and biometrics for user authentication’, Proceedings of the IEEE, Vol. 91 No. 12, pp.2021–2040. 158 Y.N. Singh and S.K. Singh Parthasaradhi, S.T.V., Derakhshani, R., Hornak, L.A. and Schuckers, S.A.C. (2005) ‘Time-series detection of perspiration as a liveness test in fingerprint devices’, IEEE Transactions on Systems Man and Cybernetics C, Vol. 35, No. 3, pp.335–343. Phillips, P.J., Wechsler, H., Huang, J. and Rauss, P.J. (1998) ‘The FERET database and evaluation procedure for face recognition algorithms’, Image and Vision Computing Journal, Vol. 16, No. 5, pp.295–306. Ratha, N.K., Chikkerur, S., Connell, J.H. and Bolle, R.M. (2007) ‘Generating cancelable fingerprint templates’, IEEE Trans. Pattern Analysis and Machine Intell., Vol. 29, No. 4, pp.561–572. Ratha, N.K., Connell, J.H. and Bolle, R.M. (2001) ‘An analysis of minutiae matching strength’, Paper presented at the International Conference of Audio and Video based Biometric Authentication, 6–8 June, Halmstad, Sweden. Reddy, P.V., Kumar, A., Rahman, S.M.K. and Mundra, T.S. (2008) ‘A new antispoofing approach for biometric devices’, IEEE Transactions on Biomedical Circuits and Systems, Vol. 2, No. 4, pp.328–337. Roberts, C. (2007) ‘Biometric attack vectors and defenses’, Computers and Security, Vol. 26, No. 1, pp.14–25. Schneier, B. (1999) ‘The uses and abuses of biometrics’, Communication to ACM, Vol. 42, No. 8, 136p. Schuckers, S.A.C. (2002) ‘Spoofing and anti-spoofing measures’, Information Security Technical Report, Vol. 7, No. 4, pp.56–62. Singh, Y.N. (2011) ‘The challenges of UID environment’, Proc. of National Conference UID-2011, Impact of Aadhaar in Governance, Computer Society of India, Lucknow, pp.153–161. Singh, Y.N. and Gupta, P. (2009) ‘Biometric method for human identification using electrocardiogram’, Proceedings of ICB 2009, Lecture Notes of Computer Science, Vol. 5558, pp.1270–1279. Singh, Y.N. and Gupta, P. (2011) ‘Correlation-based classification of heartbeats for individual identification’, Journal of Soft Computing, Vol. 15, No. 3, pp.449–460, Springer. Singh, Y.N. and Singh, S.K. (2011) ‘Vitality detection from biometrics: state-of-the-art’, Proc. World Congress on Information and Communication Technology (WICT), Mumbai, pp.106–111. Singh, Y.N. and Singh, S.K. (2012) ‘Bioelectrical signals as emerging biometrics: issues and challenges’, ISRN Signal Processing, Article ID 712032, 13p, doi:10.5402/2012/712032. Singh, Y.N., Singh, S.K. and Gupta, P. (2012) ‘Fusion of electrocardiogram with unobtrusive biometrics: an efficient individual authentication system’, Pattern Recognition Letters, Vol. 33, pp.1932–1941. Soutar, C., Roberge, D., Stoianov, A., Gilroy, R. and Kumar, B.V. (1998) ‘Biometric encryption: enrollment and verification procedures’, Proc. SPIE, Optical Pattern Recognition IX, Vol. 3386, pp.24–35. Teoh, A.B.J. and Chong, L.Y. (2010) ‘Secure speech template protection in speaker verification system’, Speech Communication, Vol. 52, pp.150–163. Toth, B. (2005) ‘Biometric liveness detection’, Information Security Bulletin, Vol. 10, pp.291–297. Uludag, U. and Jain, A.K. (2004) ‘Attacks on biometric systems: a case study in fingerprints’, Paper presented at the SPIE-EI Security, Steganography and Watermarking of Multimedia Contents VI, 18–22 January, San Jose, CA. US Department of Transportation (1998) ‘Audit report: advance automation system’, Report AV-1998-113. van der Putte, T. and Keuning, J. (2000) ‘Biometrical fingerprint recognition: don’t get your fingers burned’, Proc. Fourth Working Conference on Smart Card Research and Advanced Applications, Kluwer Academic Publishers, pp.289–303. A taxonomy of biometric system vulnerabilities and defences 159 Wang, Y. and Hatzinakos, D. (2009) ‘Sorted index numbers for privacy preserving face recognition’, EURASIP Journal on Advances in Signal Processing, Article ID 260148, pp.1–16. Watson, A. (2007) ‘Biometrics: easy to steal, hard to regain identity’, Nature, Vol. 449, 535p. View publication stats