Networking Fundamentals Exam Practice
advertisement

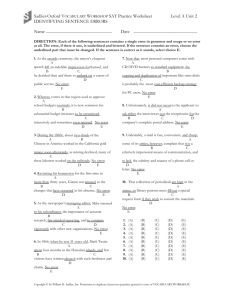
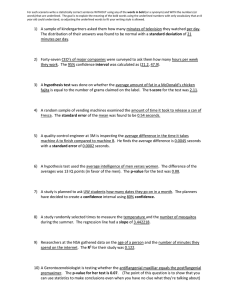
Networking Fundamentals As you go through the Training Mode of the Networking Fundamentals exam practice, type the correct answers on this doc. Save the doc as Networking Last name and turn in to drop box when completed. 1. Which protocol in IPsec provides both authentication and encryption? 2. What is the main criteria used by firewalls to filter traffic? Choose two answers. 3. You need to connect a network adapter to a switch. You need the connection to be able to send and receive data at the same time. What type of connection should you use? 4. Your ISP recently installed a T1 line. What is the maximum throughput of a T1 line? 5. You are needing to set up a VPN between two companies that are collaborating on a project. Which type of VPN will you set up? 6. Which are examples of leased lines? Choose two answers. 7. Your purchasing department has purchased new 802.11ac wireless routers. You want to make sure all of your wireless devices are compatible with this new router. Besides 802.11ac, which wireless standards will work with these wireless routers? Choose two answers. 8. You need to connect three wireless networks together: an 802.11a, an 802.11g, and an 802.11n. Which wireless tool should you use to accomplish this task? 9. Connecting several computers together in a circle without the use of a hub or switch is using a ____ Topology. 10. In a _____ topology, every single computer is connected to every other computer on the network. 11. A _____ is a device that sets up different collision domains for each device connected to it, allowing the networked devices to run in Full Duplex without collisions. 12. Which role needs to be added to Windows Server 2016 in order to enable routing through the server? 13. Which type of network cables can carry signals over the longest distances? 14. You need to find the MAC address of the network adapter for the computer you are currently working on. What command line command will give you the information you need? 15. You need to set up 750 computers on the same network. Which IP class is the best option? 16. You need to subnet a 192.168.1.0 network using a class C network. What will be the subnet mask? 17. You need to set up a group of IPv6 network interfaces in such a way that each packet is delivered to each interface. You should implement a _____ address. 18. Which is the local loopback address in IPv6? 19. Which file resolves NetBIOS names to IP addresses? 20. Which data transmission method uses a private tunnel over a public network? 21. Which two statements are true about Microsoft security zones? (Choose two) 22. Mach each port speed to its definition. 1 Kbps is ________________ bits per second 10 Mbps is ______________ bits per second 1 Gbps is 1 thousand Megabits per second, or ______________ bits 1000 Kbps is ___________________, or 1 Megabit per second 23. This question requires that you evaluate the underlined text to determine if it is correct. E1 connections use 32 channels to obtain a top speed of 2.048 Mbps. Select the correct answer if the underlined text does not make the statement correct. Select “No change is needed” if the underlined text makes the statement correct. 24. How many T1 lines are used for a full T3 connection? 25. The LAN at your workplace uses a layout similar to the image. Use the drop-down menus to complete each statement. The physical topology of this network is a…________ An example that typically uses this topology is…________ 26. This question requires that you evaluate the underlined text to determine if it is correct. An example of a physical Ring topology would be eight hubs connected to a single switch. Select the correct answer if the underlined text does not make the statement correct. Select “No change is needed” if the underlined text makes the statement correct. 27. For each of the following statements, select Yes if the statement is true. Otherwise, select No. In a star topology, a bad cable affects only two interfaces: In a star topology, failure of a central connectivity device does not bring down the entire network: In a star topology, a central connection point allows for flexibility and scalability: 28. For each statement regard switch redundancy, indicate Yes if the statement is true and No if the statement is false. A switch stack makes multiple physical switches appear as one logical switch: Load balancing is limited to routers and is not available on switches: Switches can use active-passive load balancing: 29. Which two statements are true about layer 2 switches? (Choose two) 30. The question requires that you evaluate the underlined text to determine if it is correct. A router is a device that functions primarily on the Data Link layer of the OSI Model. Select the correct answer if the underlined text does not make the statement correct. Select “No change is need” if the underlined text makes the statement correct. 31. Which IP address in a routing table signifies a default route? 32. Your IT manager has asked you to identify and label a box of miscellaneous networking components. In the box is a cable wired as in the image. The cable is a ________ cable In which type of connection would this cable be used? 33. For each of the following statements regarding causes of signal interference in networks, select Yes if the statement if true. Otherwise, select No. Microwave ovens tend to cause interference in wired networks: Fluorescent lighting can cause EMI: Cordless phones can cause interference for wireless networks: 34. Match each port speed to its definition. Cat2 – Cat3 – Cat5 – Cat5e – 35. Match each Tunneling Protocol to its corresponding TCP/IP port. PPTP to L2TP to SSTP to PPP to 36. Match each Tunneling Protocol to its corresponding method of encryption. PPTP to L2TP to SSTP to PPP to 37. Mach each device with its function. ________ – A technology used on Layer 1 of the OSI model to transmit data. ________ – Uses MAC addressing to determine which port to forward a frame. ________ – Connects two networks using different protocols. Network Interface Card – ________ 38. For each of the following statements, select Yes if the statement is true. Otherwise, select No. Unsecured websites are accessed through port 80 by default: Public websites are accessed through port 25: Secured websites are accessed through port 443 by default: 39. Match each IP address to its class. Not all addresses will be used. 100.100.1.1 – 170.100.1.5 – 198.126.1.55 – 224.0.0.2 – 40. You are troubleshooting a friend’s computer that will not connect to a specific website on the Internet, yet it can connect to other websites. You can connect to the website with no problems using your smartphone. Using a TCP/IP tool on your friend’s computer, you can receive the information shown in the image. Which command was used to generate these results? To solve the connectivity problem, you should clear the computer’s memory by executing which command? 41. This question requires that you evaluate the underlined text to determine if it is correct. AAAA records resolve hostnames to 128-bit IP addresses. 42. For each of the following statements, select Yes if the statement is true. Otherwise, select No. ipconfig /release is the command that deletes an IP address bound to an interface: dhcp -renew is the command that acquires an IP address from a DHCP server: dhcp -release is the command that deletes an IP address bound to an interface: ipconfig /renew is the command that acquires an IP address from a DHCP server: 43. For each of the following statements regarding firewalls, select Yes if the statement is true. Otherwise, select No. Firewalls mainly use user accounts to filter data packets: Firewalls can be hardware or software-based: Firewalls are only set up on individual host machines: 44. Use the screenshot to answer the drop-down menu-based questions. Which command was run to generate these results? Which command should be run to just show these results for tcp connections? 45. You receive a call from a friend whose computer is unable to connect to the Louvre Museum website located in France. Using a TCP/IP tool, you attempt to contact the website’s host from your friend’s computer and receive the information in the image. Which command-line tool was used to generate these results? Which command-line tool should be used if both hops and statistics showing a percentage of dropped packets need to be known?