The Non-Advanced Persistent Threat
advertisement

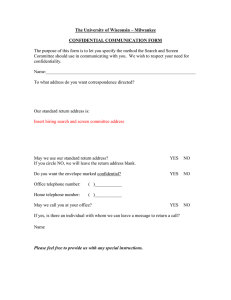
The Non-Advanced Persistent Threat Sagie Dulce, Security Research Engineer, Imperva 1 © 2014 Imperva, Inc. All rights reserved. Confidential Agenda APT • Scenario • Infamous APTs Non-APTs • The non-APT • NTLM weaknesses • Demo - Poisoning the Well (File Share) • More attack scenarios Waiting for good things to come Privilege escalation • Demo – SharePoint Poisoning Leftovers Conclusion 2 © 2014 Imperva, Inc. All rights reserved. Confidential Sagie Dulce, Security Research Engineer, Imperva 10+ years of cyber security experience Researcher at IDF Intelligence Core Data Researcher at the ADC group Frequent contributor to Imperva’s Blog Authored several Hacker Intelligence Initiative (HII) Reports 3 © 2014 Imperva, Inc. All rights reserved. Advanced Persistent Threats What Comes to Mind 4 © 2014 Imperva, Inc. All rights reserved. Confidential What Is APT? Data Center File Share / Database Initial Compromise 5 Establish Foothold © 2014 Imperva, Inc. All rights reserved. Lateral Movement Confidential Gather Data Exfiltrate Few Infamous APTs From Governments to the People CHS • Stolen Records ~4,500,000 • Period ~3 months • Initial Compromise – Heartbleed eBay • Stolen Records ~145,000,000 • Period ~ 2 months • Initial Compromise – stolen credentials (phishing / reuse) Target • Stolen Records ~70,000,000 • Period ~ 3 weeks • Initial Compromise – Credentials from partner (HVAC) 6 © 2014 Imperva, Inc. All rights reserved. Confidential Non-Advanced Persistent Threats 7 © 2014 Imperva, Inc. All rights reserved. Confidential The Non-Advanced Persistent Threat What is APT ? • Advanced • Persistent • Threat Show equivalent scenario • Not advanced • Not persistent (not extremely) • Still a threat 8 © 2014 Imperva, Inc. All rights reserved. Confidential Windows NT LAN Manager (NTLM) Authentication protocol designed by Microsoft Messages (challenge response): Negotiate Challenge Response Gives the user the Single Sign On experience • Client stores LM / NT Hash (used for authentication) Used in a variety of protocols: HTTP, SMTP, IMAP, CIFS/SMB, RDP, Telnet, MSSQL, Oracle and more… Microsoft says: • “Although Microsoft Kerberos is the protocol of choice, NTLM is still supported” • “Applications are generally advised not to use NTLM” 9 © 2014 Imperva, Inc. All rights reserved. Confidential NTLM Vulnerabilities Pass the Hash APT1 • Because response is calculated using LM / NT hash, it is equivalent to plaintext password Weak Response Calculations • In early versions, attacker that has challenge & response can calculate LM / NT hash (CloudCracker) • Extract easily with public tools: Windows Credential Editor (WCE) / QuarksPwDump Relay Attack 10 © 2014 Imperva, Inc. All rights reserved. Confidential Demo Poisoning the Well 11 © 2014 Imperva, Inc. All rights reserved. Confidential Demo - Poisoning the Well CatCorp inc. Alice Bob Initial Compromise 12 Poison File Share / SharePoint © 2014 Imperva, Inc. All rights reserved. Gather Privileges (NTLM Relay) Confidential Exfiltrate Poisoning the Well File Share 1 2 3 13 © 2014 Imperva, Inc. All rights reserved. Compromised Confidential Waiting for Good Things to Come Data Center File Share / Database Firewall Agent 2 14 © 2014 Imperva, Inc. All rights reserved. Compromised Confidential 1 Privilege Escalation Metasploit SMB capture SMB relay & authenticate SMB relay & crack Compromised SMB Reflect 15 © 2014 Imperva, Inc. All rights reserved. Confidential Demo SharePoint Poisoning 16 © 2014 Imperva, Inc. All rights reserved. Confidential Demo – SharePoint Poisoning CatCorp, Inc. Alice Bob Easily skip between protocols: HTTP to SMB / RDP / MSSQL, etc. 17 © 2014 Imperva, Inc. All rights reserved. Confidential Leftovers What We Left Out and Why 18 © 2014 Imperva, Inc. All rights reserved. Confidential Things We Left Out We didn’t talk about the “edges” • Initial Compromise done with simple methods (phishing, stealing, pay per infection) Security is not equal, attackers go for the weakest link. recently was hacked via a “test server” “That means it would have been possible, if difficult, for the intruder to move through the network and try to view more protected information” • Exfiltration copy stolen data from asset Use any legitimate cloud service (Google Drive etc.) Initial Compromise 19 Establish Foothold © 2014 Imperva, Inc. All rights reserved. Lateral Movement Confidential Gather Data Exfiltrate Conclusion What Does It All Mean & How to Mitigate? 20 © 2014 Imperva, Inc. All rights reserved. Confidential Conclusion APT is not the sole domain of government or sophisticated criminal groups • No need for zero days • Low technical skills NTLM is only a symptom • Patching / upgrading does not always happen, especially when it’s costly • SSO experience is convenient for attackers : go from file to DB, Web Server, Exchange, etc. The least confidential locations could prove dangerous • Not strictly monitored 21 © 2014 Imperva, Inc. All rights reserved. Confidential Mitigations Upgrade • While a good idea, but not always feasible • Kerberos also has its vulnerabilities (e.g. Pass the Ticket) Monitor authentications to resources • Same machine authenticates with several users • Same user authenticates from several machines Avoid services that logon to large number of assets • Services authentication can leave behind hashes, tickets or used in a relay / MIM attacks 22 © 2014 Imperva, Inc. All rights reserved. Confidential Webinar Materials Join Imperva LinkedIn Group, Imperva Data Security Direct, for… 23 Post-Webinar Discussions Answers to Attendee Questions Webinar Recording Link Join Group © 2014 Imperva, Inc. All rights reserved. Questions? www.imperva.com 24 © 2014 Imperva, Inc. All rights reserved. Thank You 25 © 2014 Imperva, Inc. All rights reserved.