Lecture 13: Authentication and Cash
advertisement

Lecture 13:
Authentication and Cash
Cash is a problem. It’s annoying to carry, it spreads
germs, and people can steal it from you. Checks and
credit cards have reduced the amount of physical cash
flowing through society, but the complete elimination of
cash is virtually impossible. It’ll never happen; drug
dealers and politicians would never stand for it. Checks
and credit cards have an audit trail; you can’t hide to
whom you gave money.
Bruce Schneier, Applied Cryptography
CS588: Security and Privacy
University of Virginia
Computer Science
David Evans
http://www.cs.virginia.edu/~evans
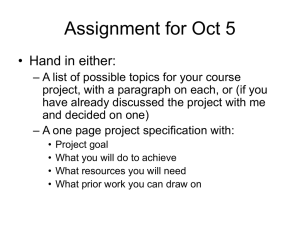
Menu
• Authentication
• Digital Cash
10 Oct 2001
University of Virginia CS 588
2
Last Time
Terminal
Login: evans
Password: ******
login sends
<“evans”, “memodn”>
shankly.cs.virginia.edu
Eve
Trusted subsystem computes
DES+25memodn (0, salt) and
compares to stored value.
10 Oct 2001
University of Virginia CS 588
3
Simplified SSH Protocol
Terminal
Login: evans
Password: ******
login sends
EKUshankly<“evans”, “memodn”>
shankly.cs.virginia.edu
Eve
Can’t decrypt without KRshankly
10 Oct 2001
University of Virginia CS 588
4
Actual SSH Protocol
Server
Client
1
requests connection
KUS, KUt
Compares
to stored KUS
time
3
10 Oct 2001
EKUS [EKUt [r]]
|| { IDEA | 3DES }
All traffic encrypted using r and
selected algorithm. Can do
regular login (or something more
complicated).
University of Virginia CS 588
KUS - server’s
2 public host key
KUt – server’s
public key,
changes every
hour
r – 256-bit
random number
generated by
client
5
Comparing to stored KUS
• It better be stored securely
– PuTTY stores it in windows registry
(HKEY_CURRENT_USER\Software\Simon
Tatham\PuTTY\SshHostKeys)
10 Oct 2001
University of Virginia CS 588
6
Why Johnny Can’t Even Login
SecureCRT
Default choice!
10 Oct 2001
University of Virginia CS 588
7
ssh.com’s SSH
10 Oct 2001
University of Virginia CS 588
8
ssh Error
10 Oct 2001
University of Virginia CS 588
9
Jennifer Kahng’s TCC Thesis Project
• People are stupid
31% clicked Continue
• Getting people to pay
attention is difficult
unless you really want
to make them angry.
(Security vs.
convenience.)
• Only two people (of >
700) emailed
webmaster about
potential security
vulnerability.
University of Virginia CS 588
2% typed in “yes”
10 Oct 2001
10
Why Johnny (von Neumann)
Can’t Even Login
• A smart attacker just replaces the stored
key in registry
– An ActiveX control can do this trivially
– No warning from SSH when you now connect
to the host controlled by the attacker (have to
spoof DNS or intercept connection, but this is
easy)
• No easy solution…see Question 4 from
last year’s midterm
10 Oct 2001
University of Virginia CS 588
11
Recap – Authentication Problems
• Need to store the passwords somewhere –
dangerous to rely on this being secure
• Need to transmit password from user to
host
• Remaining problems:
• User’s pick bad passwords
• Even if everything is secure, can still watch
victim type!
• Only have to mess up once
10 Oct 2001
University of Virginia CS 588
12
Solution – Don’t Reuse Passwords
• One-time passwords
• New users have to memorize a list of
secure passwords and use one in turn
for each login
• Host generates the list using
cryptographic random numbers and
stores it securely
• Users spend hours memorizing
passwords...and better not forget one!
10 Oct 2001
University of Virginia CS 588
13
Terminal
Challenge-Response
Login: evans
EKUshankly[“evans”]
Challenge
Challenge: What’s the 15th word of
the Jefferson Wheel Cipher
Challenge?
Response: of
“of”
10 Oct 2001
University of Virginia CS 588
14
Terminal
Challenge-Response
Login: evans
EKUmamba[“evans”]
Challenge x
Challenge: 2357938523
Response: f(x)
f(x)
10 Oct 2001
University of Virginia CS 588
15
Challenge-Response Systems
• Ask a question, see if the answer is
right
• Hard to make up questions only host
and user can answer
• Question: x? Answer: f(x).
• What’s a good choice for f?
– E (x, key known to both)
– Still have to problem of storing the key
• SecureID systems work like this
– Don’t need to send challenge, its the time
10 Oct 2001
University of Virginia CS 588
16
One-Time Use Passwords
• Can we create a sequence of
passwords the host can check without
storing anything useful to an attacker on
the host?
Recall: Unix repeated use passwords
Host stores: H(p)
User provides: x
Password is valid if H(x) = H(p)
10 Oct 2001
University of Virginia CS 588
17
S-Key
• Alice picks random number R
• S-Key program generates H(R),
H(H(R)), ... , H99(R).
• Alice prints out these numbers and
stores somewhere secure
• Host stores H100(R).
10 Oct 2001
University of Virginia CS 588
18
S/Key Login
•
•
•
•
•
•
Alice enters H99(R).
Host calculates H (H99(R)).
Compares to stored H100(R).
If they match, allows login
And replaces old value with H99(R).
Alice crosses off H99(R), enters H98(R)
next time.
• S/Key uses MD4 for H
10 Oct 2001
University of Virginia CS 588
19
S/Key
> keyinit
Adding evans:
Reminder - Only use this method if you
are directly connected.
If you are using telnet or rlogin exit
with no password and use keyinit -s.
Enter secret password: test
Again secret password: test
ID evans s/key is 99 sh69506
H100(test) = sh69506
What do I need to enter to log in?
10 Oct 2001
University of Virginia CS 588
20
S/Key
> key -n 100 99 sh69506
Reminder - Do not use this program
while logged in via telnet or
rlogin.
Enter secret password: test
0: KEEL FLED SUDS BOHR DUD SUP
1: TOW JOBS HOFF GIVE CHUB LAUD
…
98: JEAN THEN WEAK ELAN SLOB GAS
99: MUG KNOB ACT ALOE REST TOO
10 Oct 2001
University of Virginia CS 588
21
Digital Cash
10 Oct 2001
University of Virginia CS 588
22
Properties of Physical Cash
•
•
•
•
Universally recognized as valuable
Easy to transfer
Anonymous
Big and Heavy
– Average bank robbery takes $4552
– 500 US bills / pound
– Bill Gates net worth would be 400 tons in $100 bills
• Moderately difficult to counterfeit in small
quantities
• Extremely difficult to get away with
counterfeiting large quantities (unless you are
Iran or Syria)
10 Oct 2001
University of Virginia CS 588
23
Real Cash
• Why does it have value?
– Nice pictures of dead presidents (< 1¢)
– Because it is hard to print (< 5¢)
• Because other people think it does
– We trust our government not to print too
much
– People who forge it get sent to jail
10 Oct 2001
University of Virginia CS 588
24
Counterfeiting
• Secret Service siezed $209M in 1994 (of
$380B circulated)
• Nearly 2/3 of US cash is in foreign countries
• Why did US bills change?
– Iran and Syria probably print counterfeit US bills
– They have a De la rue Giori (Switzerland) printing
press, same as used for old US bills
– 1992 report, led to currency redesign
• Most foreign countries are smarter
– Use of color
– Obvious, well-known security features
– Bigger bills for bigger denominations
10 Oct 2001
University of Virginia CS 588
25
IOU Protocol (Lecture 11)
M = “I, Alice, owe Bob $1000.”
M
EKRA[H(M)]
Bob
knows KUA
Alice
{KUA, KRA}
10 Oct 2001
M
Judge
knows KUA
EKRA[H(M)]
Bob can verify H(M) by
decrypting, but cannot forge
M, EKRA[H(M)] pair without
knowing KRA.
University of Virginia CS 588
26
IOU Protocol
x Universally recognized as valuable
x Easy to transfer
x Anonymous
x Heavy
? Moderately difficult to counterfeit in
small quantities
? Extremely difficult to get away with
counterfeiting large quantities
10 Oct 2001
University of Virginia CS 588
27
What is cash really?
• IOU from a bank
• Instead of generating, “I, Alice, owe Bob
$1000”, let’s generate, “I, the
Trustworthy Trust Bank, owe the bearer
of this note $1000.”
• Alice asks the bank for an IOU, and the
bank deducts $1000 from her account.
10 Oct 2001
University of Virginia CS 588
28
Bank IOU Protocol
Universally recognized as valuable
Easy to transfer
Anonymous
x Heavy
? Moderately difficult to counterfeit in
small quantities
? Extremely difficult to get away with
counterfeiting large quantities
10 Oct 2001
University of Virginia CS 588
29
Counterfeiting Bank IOUs
• Assuming the hash and signature are
secure
• Alice gives Bob bank IOU for $1000
• Bob sends bank 100 copies of bank
IOU
• The bank has lost $99 000.
• Bits are easy to copy! Hard to make
something rare...
10 Oct 2001
University of Virginia CS 588
30
Bank Identifiers
• Bank adds a unique tag to each IOU it
generates
• When someone cashes an IOU, bank
checks that that IOU has not already
been cashed
• Can’t tell if it was Alice or Bob who
cheated
• Alice loses her anonymity – the bank
can tell where she spends her money
10 Oct 2001
University of Virginia CS 588
31
Digital Cash, Protocol #1
1. Alice prepares 100 money orders for
$1000 each.
2. Puts each one in a different sealed
envelope, with a piece of carbon paper.
3. Gives envelopes to bank.
4. Bank opens 99 envelopes and checks
they contain money order for $1000.
5. Bank signs the remaining envelope
without opening it (signature goes
through carbon paper).
10 Oct 2001
University of Virginia CS 588
32
Digital Cash, Protocol #1 cont.
6. Bank returns envelope to Alice and
deducts $1000 from her account.
7. Alice opens envelope, and spends the
money order.
8. Merchant checks the Bank’s signature.
9. Merchant deposits money order.
10. Bank verifies its signature and credits
Merchant’s account.
10 Oct 2001
University of Virginia CS 588
33
Digital Cash, Protocol #1
• Is it anonymous?
• Can Alice cheat?
– Make one of the money orders for $100000, 1%
chance of picking right bill, 99% chance bank
detects attempted fraud.
• Better make the penalty for this high (e.g., jail)
– Copy the signed money order and re-spend it.
• Can Merchant cheat?
– Copy the signed money order and re-deposit it.
10 Oct 2001
University of Virginia CS 588
34
Digital Cash, Protocol #2
• Idea: prevent double-spending by giving
each money order a unique ID.
• Problem: how do we provide unique IDs
without losing anonymity?
• Solution: let Alice generate the unique
IDs, and keep them secret from bank.
10 Oct 2001
University of Virginia CS 588
35
Digital Cash, Protocol #2
1. Alice prepares 100 money orders for
$1000 each, adds a long, unique random
ID to each note.
2. Puts each one in a different sealed
envelope, with a piece of carbon paper.
3. Gives envelopes to bank.
4. Bank opens 99 envelopes and checks they
contain money order for $1000.
5. Bank signs the remaining envelope without
opening it.
10 Oct 2001
University of Virginia CS 588
36
Digital Cash, Protocol #2 cont.
6. Bank returns envelope to Alice and
deducts $1000 from her account.
7. Alice opens envelope, and spends the
money order.
8. Merchant checks the Bank’s signature.
9. Merchant deposits money order.
10. Bank verifies its signature, checks that the
unique random ID has not already been
spent, credits Merchant’s account, and
records the unique random ID.
10 Oct 2001
University of Virginia CS 588
37
Digital Cash, Protocol #2
•
•
•
•
Is it anonymous?
Can Alice cheat?
Can Merchant cheat?
Can bank catch cheaters?
10 Oct 2001
University of Virginia CS 588
38
Mimicking Carbon Paper
• How does bank sign the envelope
without knowing what it contains?
• Normal signatures
Alice sends bank M
Bank sends Alice, SM = EKRBank (M)
Alice shows SM to Bob who decrypts with
banks public key.
10 Oct 2001
University of Virginia CS 588
39
Blind Signatures
• Alice picks random k between 1 and n.
• Sends bank t = mke mod n. (e from
Bank’s public key).
• Bank signs t using private key d. Sends
Alice:
td = (mke mod n)d mod n
= (mke)d mod n mdked mod n
= (mke)d mod n mdked mod n
What do we know about ked mod n?
10 Oct 2001
University of Virginia CS 588
40
Blind Signatures
• Alice gets
td mdk mod n
• Alice divides by k to get
sm mdk / k md mod n.
• Hence: bank can sign money orders
without opening them!
10 Oct 2001
University of Virginia CS 588
41
Digital Cash Protocol #2
• Instead of envelopes, Alice blinds each
money order using a different randomly
selected ki.
• The bank asks for any 99 of the ki’s.
The bank unblinds the messages (by
dividing) and checks they are valid.
• The bank signs the other money order.
• Still haven’t solved the catching
cheaters problem!
10 Oct 2001
University of Virginia CS 588
42
Anonymity for Non-Cheaters
• Spend a bill once – maintain anonymity
• Spend a bill twice – lose anonymity
• Have we seen anything like this?
10 Oct 2001
University of Virginia CS 588
43
Digital Cash
1. Alice prepares n money orders each
containing:
Amount
Uniqueness String: X
Identity Strings: I1 = (h(I1L), h(I1R))
...
In = (h(InL), h(InR))
Each In pair reveals Alice’s identity (name,
address, etc.). I = IiL IiR.
h is a secure, one-way hash function.
10 Oct 2001
University of Virginia CS 588
44
Digital Cash, cont.
2. Alice blinds (multiplies by random k) all n
money orders and sends them to bank.
3. Bank asks for any n-1 of the random kis
and all its corresponding identity strings.
4. Bank checks money orders. If okay,
signs the remaining blinded money
order, and deducts amount from Alice’s
account.
10 Oct 2001
University of Virginia CS 588
45
Digital Cash, cont.
5. Alice unblinds the signed note, and
spends it with a Merchant.
6. Merchant asks Alice to randomly reveal
either IiL or IiR for each i. (Merchant
chooses n-bit selector string.)
7. Alice sends Merchant corresponding IiL’s
or IiR’s.
8. Merchant uses h to confirm Alice didn’t
cheat.
10 Oct 2001
University of Virginia CS 588
46
Digital Cash, cont.
9. Merchant takes money order and
identity string halves to bank.
10. Bank verifies its signature, and checks
uniqueness string. If it has not been
previously deposited, bank credits
Merchant and records uniqueness string
and identity string halves.
10 Oct 2001
University of Virginia CS 588
47
Digital Cash, cont.
11. If it has been previously deposited,
bank looks up previous identity string
halves. Finds one where both L and R
halves are known, and calculates I.
Arrests Alice.
12. If there are no i’s, where different
halves are known, arrest Merchant.
10 Oct 2001
University of Virginia CS 588
48
Digital Cash Protocol
Universally recognized as valuable
Easy to transfer
Anonymous
x Heavy
Moderately difficult to counterfeit in
small quantities
? Extremely difficult to get away with
counterfeiting large quantities (unless
you are Iran or Syria)
10 Oct 2001
University of Virginia CS 588
49
Digital Cash Summary
• Preserves anonymity of non-cheating
spenders (assuming large bank and
standard denominations)
• Doesn’t preserve anonymity of Merchants
• Requires a trusted off-line bank
• Expensive – lots of computation for one
transaction
• Other schemes (Millicent, CyberCoin,
NetBill, etc.) proposed for smaller
transactions
10 Oct 2001
University of Virginia CS 588
50
Reading “Holiday”
“… professors should make sure to
keep at least one holiday stress-free.”
- Tuesday’s Cav Daily Editorial
You have no assignments next week!
But…project presentations start week after
Thanksgiving.
So…either make lots of progress on your project
next week, or plan on working on them a lot over
Thanksgiving break.
10 Oct 2001
University of Virginia CS 588
51
Charge
• User Interfaces Matter – Especially for
Security
• 86% of users pick dumb passwords, but
everyone will click “Ok” to any securityrelated question
• Cryptographers can make infinite
amounts of money!
10 Oct 2001
University of Virginia CS 588
52