Slides for lecture 7
advertisement

CMSC 414
Computer and Network Security
Lecture 7
Jonathan Katz
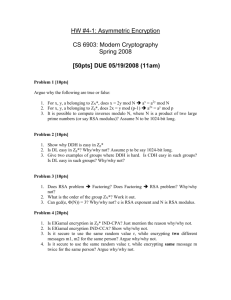
Review: El Gamal encryption
(Some aspects of the actual scheme are simplified)
Key generation
– Choose a large prime p, and an element g Zp*
– Choose random x {0, …, p-2}, set h=gx
– The public key is (p, g, h), and the private key is x
Encryption
– View the message m as an element of Zp*
– Choose random r {0, …, p-2}
– The ciphertext is (gr, hr m)
To decrypt ciphertext (c1, c2) output c2/c1x
– Correctness?
Security?
Security of El Gamal encryption is based on the
decisional Diffie-Hellman assumption
Best current algorithm for the decisional Diffie-
Hellman problem in Zp* runs in time ≈ exp(|p|1/3)
– So if p is a 1024-bit prime, best current attack on El
Gamal encryption requires time ≈ 260
In other groups, the Diffie-Hellman problem is
currently ‘harder’
– E.g., for elliptic curve groups, best current algorithms
require time exp(|p|/2)
– Can use 120-bit primes to get 260 security
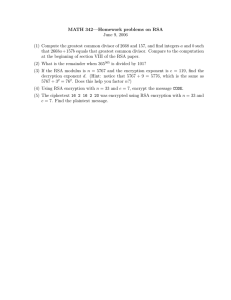
RSA background
N=pq, p and q distinct, odd primes
(N) = (p-1)(q-1) = |ZN*|
– Easy to compute (N) given the factorization of N
– Hard to compute (N) without the factorization of N
For all x ZN*, it holds that x(N) = 1 mod N
If ed=1 mod (N), then for all m:
(me)d = m mod N
I.e., given d, we can compute eth roots
We have an asymmetry!
Let e be relatively prime to (N)
– Needed so that ed=1 mod (N) has a solution
Given e and the factors of N, can compute d and
hence compute eth roots
Without the factorization of N, no apparent way to
compute eth roots
Hardness of computing eth roots?
The RSA problem:
– Given N, e, and c, compute c1/e mod N
If factoring is easy, then the RSA problem is easy
We know of no other way to solve the RSA
problem besides factoring N
– But we do not know how to prove that the RSA
problem is as hard as factoring
The upshot: we believe factoring is hard, and we
believe the RSA problem is hard
How hard is factoring?
Best current algorithms for factoring N=pq a
product of two equal-length primes, run in time
≈ exp(|N|1/3)
So need |N| ≈ 1024 for reasonable security
Currently |N| ≈ 2048 recommended for good
security margins
We have an asymmetry!
Given d (which can be computed from e and the
factorization of N), possible to compute eth roots
Without the factorization of N, no apparent way to
compute eth roots
Let’s use this to encrypt…
RSA key generation
Generate random p, q of sufficient length
Compute N=pq and (N) = (p-1)(q-1)
Compute e and d such that ed = 1 mod (N)
– e must be relatively prime to (N)
– Typical choice: e = 3; other choices possible
Public key = (N, e); private key = (N, d)
“Textbook RSA” encryption
Public key (N, e); private key (N, d)
To encrypt a message m ZN*, compute
c = me mod N
To decrypt a ciphertext c, compute m = cd mod N
Correctness…
…what about security?
Textbook RSA is insecure!
It is deterministic!
Furthermore, it can be shown that the ciphertext
leaks specific information about the plaintext
Padded RSA
Introduce randomization…
Public key (N, e); private key (N, d)
– Say |N| = 1024 bits
To encrypt m {0,1}895,
– Choose random r {0,1}128
– Compute c = (r | m)e mod N
Decryption done in the natural way…
Essentially this is standardized as PKCS #1 v1.5
Hybrid encryption
Public-key encryption is “slow”
Encrypting “block-by-block” would be inefficient
for long messages
Hybrid encryption gives the functionality of
public-key encryption at the (asymptotic)
efficiency of private-key encryption!
Hybrid encryption
message
pk
Enc’
Enc
k
random!
“encapsulated
key”
Enc = public-key encryption scheme
Enc’ = private-key encryption scheme
ciphertext
“encrypted
message”
Security
If public-key component and private-key
component are secure against chosen-plaintext
attacks, then hybrid encryption is secure against
chosen-plaintext attacks
Extension
How should hybrid encryption be done when
sending the same message to multiple recipients
(e.g., email encryption)?
Malleability
All the public-key encryption schemes we have
seen so far are malleable
– Given ciphertext c that encrypts (unknown) message m,
possible to generate a ciphertext c’ that encrypts a
related message m’
In the public-key setting, security against chosen-
ciphertext attacks implies non-malleability
In many scenarios, malleability/chosen-ciphertext
attacks are problematic
– E.g., auction example; password example;
Bleichenbacher attack…
Bleichenbacher’s attack
RSA PKCS #1 v1.5 is actually defined as:
c = (00 || 02 || r || 0 || m)e mod N
When decrypting, return an error if formatting is
not obeyed
This enables a chosen-ciphertext attack that relies
only on the ability to detect errors upon decryption
Bleichenbacher’s attack
c = Encpk(m)
c1
…
If the {ci} are
carefully constructed,
error/no error
this information is
enough to determine m!
c999
error/no error
Malleability
All the public-key encryption schemes we have
seen so far are malleable
– Given a ciphertext c that encrypts an (unknown)
message m, possible to generate a ciphertext c’ that
encrypts a related message m’
Note: the problem is not integrity (there is no
integrity in public-key encryption, anyway), but
malleability and/or the ability to conduct a chosenciphertext attack
Malleability in private-key setting
Malleability is an issue in the private-key setting
as well
– Recall that CBC, OFB, CTR mode are all vulnerable to
chosen-ciphertext attacks, and are all malleable
Authenticated encryption schemes (e.g., “encrypt-
then-authenticate”) are secure against chosenciphertext attacks (and non-malleable)