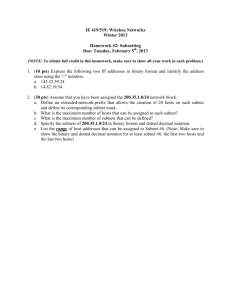
2 IP Addressing and Related Topics A Guide to TCP/IP Chapter 2
advertisement

2 IP Addressing and Related Topics A Guide to TCP/IP Chapter 2 1 2 Objectives After reading this chapter and completing the exercises you will be able to: • Understand IP addressing, anatomy and structures, and addresses from a computer’s point of view • Recognize and describe the various IP address classes from A to E, and explain how they’re composed and used • Understand the nature of IP address limitations, and how techniques like Classless Inter-Domain Routing and Network Address Translation ease those limitations Chapter 2 2 2 Objectives After reading this chapter and completing the exercises you will be able to: • Define the terms subnet and supernet, and apply your knowledge of how subnets and supernets work to solve specific network design problems • Understand how public and private Internet addresses are assigned, how to obtain them, and how to use them properly • Recognize the importance and value of an IP addressing scheme Chapter 2 3 2 IP Addressing Basics • Symbolic names are easier to remember a string, such as www.course.com, than a numeric address, such as 199.95.728—computers are the opposite • They deal with network addresses in the form of bit patterns that translate into decimal numbers • IP uses a three-part addressing scheme, as follows: – Symbolic – Logical numeric – Physical numeric Chapter 2 4 2 IP Addressing Basics • In keeping with the layered nature of network models, it makes sense to associate the MAC layer address with the Data Link layer (or TCP/IP Network Access layer, if you prefer to think in terms of that model), and to associate IP addresses with the Network layer (or the TCP/IP Internet layer) • As data moves through intermediate hosts between the original sender and the ultimate receiver, it does so between pairs of machines, where each pair resides on the same physical network Chapter 2 5 2 IP Addressing Basics • At the Network layer, the original sender’s address is represented in the IP source address field in the IP packet header, and the ultimate recipient’s address is represented in the IP destination address field in the same IP packet header • The IP destination address value, in fact, is what drives the sometimes-long series of intermediate transfers, or hops, which occur as data makes its way across a network from sender to receiver Chapter 2 6 2 Anatomy of an IP Address • Numeric IP addresses use dotted decimal notation when expressed in decimal numbers, and take the form n.n.n.n., in which n is guaranteed to be between zero and 255 for each and every value • The numeric values in dotted decimal representations of numeric IP addresses are usually decimal values, but may occasionally appear in hexadecimal (base 16) or binary (base 2) notation Chapter 2 7 2 Anatomy of an IP Address • Duplication of numeric IP addresses is not allowed because that would lead to confusion • Also, there is a notion of “neighborhood” when it comes to interpreting numeric IP addresses • Proximity between two numeric IP addresses (especially if the difference is only in the rightmost one or two octets) can sometimes indicate that the machines to which those addresses correspond reside close enough together to be on the same general network, if not on the same physical cable segment Chapter 2 8 2 IP Address Classes • Initially, these addresses were further subdivided into five classes, from Class A to Class E • For the first three classes of addresses, divide the octets as follows to understand how they behave: Class A n h.h.h Class B n.n Class C n.n.n h.h h • If more than one octet is part of the network or host portion of the address, then the bits are simply concentrated to determine the numeric address Chapter 2 9 2 IP Address Classes • The network portion of that address is 10, whereas the host portion is 12.120.2, treated as a three-octet number • Address Classes D and E are for special uses • Class D addresses are used for multicast communications, in which a single address may be associated with more than one network host machine • This is useful only when information is broadcast to more than one recipient at a time so it should come as no surprise that video and teleconferencing applications, for example, use multicast addresses Chapter 2 10 2 More About Class A Addresses • Expressed in binary form (ones and zeroes only), Class A addresses always take the form: 0bbbbbbb.bbbbbbbb.bbbbbbbb.bbbbbbbb • The leading digit is always zero, and all other digits can be either ones or zeroes • On any IP network, addresses consisting of all zeroes and all ones are reserved for special uses, so of those 128 possible network addresses, only those from 00000001 to 01111110 (or 1 to 126, in decimal terms) are considered usable Chapter 2 11 2 More About Class A Addresses • The address for network 10 is reserved for private network use • Also, by convention, the address 127.n.n.n is reserved for loopback testing (or checking the integrity and usability of a TCP/IP protocol stack installed on any computer Chapter 2 12 2 More About Class B Addresses • Class B addresses always take the form: 10bbbbbb.bbbbbbbb.bbbbbbbb.bbbbbbbb • The leading two digits are 10, and the remaining digits can be either ones or zeroes • RFC 1918 stipulates that 16 Class B addresses, from 172.16.0.0 to 172.32.255.255, are reserved for private use • This means that the maximum number of public IP addresses for Class B is 16,382-16, or 16,366 Chapter 2 13 2 Class B Address Facts and Figures Chapter 2 14 2 More About Class C Addresses • Class C addresses always take the form: 110bbbbb.bbbbbbbb.bbbbbbbb.bbbbbbbb • The leading three digits are 110, and the remaining digits can be either ones or zeroes • Note that this scheme reduces the total number of networks possible by the most significant three bits Chapter 2 15 2 More About Address Classes D and E • Class D addresses always take the form: 1110bbbb.bbbbbbbb.bbbbbbbb.bbbbbbbb • Class E addresses always take the form: 11110bbb.bbbbbbbb.bbbbbbbb.bbbbbbbbb • Class D is used for multicast addresses so that multiple users can “share” a single IP address and receive the same broadcast across a network from a single transmission Chapter 2 16 2 Network, Broadcast, Multicast, and Other Special IP Addresses • When an IP packet moves from its sender to its receiver, the network portion of the address directs that traffic from the sender’s network to the receiver’s network • The only time the host portion of the address comes into play is when the sender and receiver both reside on the same physical network or subnet Chapter 2 17 2 Network, Broadcast, Multicast, and Other Special IP Addresses • The broadcast address represents a network address that all hosts on a network must read • Although broadcasts still have some valid uses on modern networks, they originated in an era when networks were small and of limited scope, in which a sort of “all hands on deck” message represented a convenient way to ask for services when a specific server could not be explicitly identified Chapter 2 18 2 Broadcast Packet Structures • IP broadcast packets have two destination address fields—one Data Link layer destination address field, and one destination network address field Chapter 2 19 2 Multicast Packet and Address Structures • When a host uses a service that employs a multicast address (such as the 224. 0.0.9 address used for RIPv2 router updates), it registers itself to “listen” on that address, as well as on its own unique host address • That host must also inform its IP gateway (the router or other device that will forward traffic to the host’s physical network) that it is registering for this service so that device will forward such multicast traffic to that network (otherwise, it will never appear there) Chapter 2 20 2 Multicast Packet and Address Structures • The Internet Corporation for Assigned Names and Numbers (ICANN) allocates multicast addresses on a controlled basis • Formerly, addresses were under the auspices of IANA, the Internet Assigned Numbers Authority Chapter 2 21 2 Multicast Packet and Address Structures • The Data Link layer address 0x01-00-5E-00-05 is obtained with the following calculation: 1. Replace the first byte with the corresponding 3-byte OUI. In this case, 224 is replaced with 0x00-00-5E (assigned to IANA) 2. Change the first byte to an odd value (from 0x00 to 0x01) 3. Replace the second through fourth bytes with their decimal equivalents Chapter 2 22 2 Data Link Layer Address Conversion Chapter 2 23 2 The Vanishing IP Address Space • IP addresses were assigned for public use, they were assigned on a per-network basis • With the ever-increasing demand for public IP addresses for Internet access, it should come as no surprise that, as early as the mid-1990s, experts began to predict that the Internet would “run out” of available IP addresses Chapter 2 24 2 The Vanishing IP Address Space • The causes for concern have abated somewhat, Here’s why: – The technocrats at the IETF introduced a new way to carve up the IP address space—Classless Inter-Domain Routing (CIDR) – A brisk trade in existing IP network addresses sprung up during the same time – RFC 1918 reserves three ranges of IP addresses for private use—a single Class A (10.0.0.0-10.255.255.255), 16 Class Bs (172.16.0.0-172.31.255.255), AND 256 Class Cs (192.168.0.0-192.168.255.255). When used in tandem with a technology called Network Address Translation (a.k.a NAT), private IP addresses can help lift the “cap” on public IP addresses Chapter 2 25 2 Understanding Basic Binary Arithmetic • For the purposes of this text, you must master four different kinds of binary calculations: 1. Converting binary to decimal 2. Converting decimal to binary 3. Understanding how setting increasing numbers of high-order bits to 1 in 8-bit binary numbers corresponds to specific decimal numbers 4. Understanding how setting increasing low-order bits to 1 in 8-bit binary numbers corresponds to specific decimal numbers Chapter 2 26 2 Converting Decimal to Binary • Simply divide the number by two, write the remainder (which must be 0 or 1), then write the dividend, and repeat until the dividend is zero • To produce the binary number that corresponds to 125, you write the digits starting with the last remainder value, and work your way up: 1111101 • The alternate approach to convert the number depends on what mathematicians like to call a “step function” Chapter 2 27 2 Converting Binary to Decimal • This is extremely easy, if you know your powers of two • Follow these steps, using 11011011 as the example number: 1. Count the total number of digits in the number (11011011 has eight digits) 2. Subtract one from the total (8-1 = 7). That is the power of two to associate with the highest exponent for two in the exponential notation for that number 3. Convert to exponential notation, using all the digits as multipliers Chapter 2 28 2 High-Order Bit Patterns • In an 8-bit number, there’s little or no value in blocking less than two bits, or more than six bits, so the bit patterns you care about most appear in the second through the sixth positions in the list of possibilities shown on page 68 of the textbook Chapter 2 29 2 Low-Order Bit Patterns • Here, we stand the previous example on its head, and start counting up through the bit positions in 8-bit numbers from right to left, adding ones as we increment • Note that each of these numbers is the same as two raised to the power of the number of bits showing, minus one Chapter 2 30 2 Of IP Networks, Subnets, and Masks • If two network interfaces are on the same physical network, they can communicate directly with one another at the MAC layer • In fact, each of the three primary IP address classes—namely A, B, and C— also has an associated default subnet mask Chapter 2 31 2 IP Subnets and Supernets • A subnet mask is a special bit pattern that “blocks off” the network portion of an IP address with an all-ones pattern • The reason why concepts like subnets and supernets are important for TCP/IP networks is because each of these ideas refers to a single “local neighborhood” on such a network, seen from a routing perspective Chapter 2 32 2 IP Subnets and Supernets • Thus, a subnet mask that is larger than the default mask for the address in use divides a single network IP address into multiple subnetworks • The network prefix identifies the number of bits in the IP address, counting from the left that represents the actual network address itself, and the additional two bits of subnetting represent the bits that were borrowed from the host portion of that IP address to extend the network portion Chapter 2 33 2 IP Subnets and Supernets • The entire network address, including the network prefix and the subnetting bits, is called the extended network prefix • This activity of stealing bits from the host portion of further subdivide the network portion of an address is called subnetting a network address, or subnetting Chapter 2 34 2 IP Subnets and Supernets • When a computer on one subnet wishes to communicate with a computer on another subnet, traffic must be forwarded from the sender to a nearby IP gateway to send the message on its way from one subnet to another • Supernetting takes the opposite approach: by combining contiguous network addresses, it steals bits from the network portion and uses them to create a single, larger contiguous address space for host addresses Chapter 2 35 2 Calculating Subnet Masks • The simplest form of subnet masking uses a technique called constant-length subnet masking (CLSM), in which each subnet includes the same number of stations and represents a simple division of the address space made available by subnetting into multiple equal segments • Another form of subnet masking uses a technique called variable-length subnet masking (VLSM) and permits a single address to be subdivided into multiple subnets, in which subnets need not all be the same size Chapter 2 36 2 Designing a Constant-Length Subnet Mask • To design a CLSM subnet mask, in which each portion of the network has the same number of addresses, follow the steps outlined on pages 71 and 72 of the textbook Chapter 2 37 2 Another ConstantLength Subnet Mask Example • Let’s pick a more ambitious design this time, which shows how subnet masks or host addresses can extend across multiple octets • Remember, the whole purpose of this exercise is to compare the number of hosts needed for each subnet to the number you just calculated Chapter 2 38 2 Designing a Variable-Length Subnet Mask • Designing and configuring variable-length subnet masks is more time-consuming and difficult, but makes much better use of available address space • But let’s suppose that over half the subnets at PU require support for 30 devices or less • VSLM was devised to cover this contingency • VSLM makes it possible to create routing hierarchies and limit traffic on the backbone by making sure that smaller subnet address spaces can access the resources they need as efficiently as possible Chapter 2 39 2 Designing a Variable-Length Subnet Mask • You must: – Analyze the requirements for individual subnets – Aggregate those requirements by their relationships to the nearest power of two that is at least two greater than the number of such subnets required – Use the subnets that require the largest number of devices to decide the minimum size of the subnet mask – Aggregate subnets that require smaller numbers of hosts within address spaces defined by the largest subdivisions – Define a VLSM scheme that provides the necessary number of subnets of each size to fit its intended use best by aggregating subnets large and small to create the most efficient network traffic patterns Chapter 2 40 2 Calculating Supernets • Supernets “steal” bits from the network portion of an IP address to “lend” those bits to the host part • As part of how they work, supernets permit multiple IP network addresses to be combined and make them function together as if they represent a single logical network Chapter 2 41 2 Classless Inter-Domain Routing (CIDR) • CIDR gets its name from the notion that it ignores the traditional A, B, and C class designations for IP addresses, and can therefore set the network-host ID boundary wherever it wants to, in a way that simplifies routing across the resulting IP address spaces Chapter 2 42 2 Classless Inter-Domain Routing (CIDR) • Creating a CIDR address is subject to the following limitations: – All the addresses in the CIDR address must be contiguous – When address aggregation occurs, CIDR address blocks work best when they come in sets that are greater than one, and equal to some lower-order bit pattern that corresponds to all ones – CIDR addresses are commonly applied to Class C addresses – To use a CIDR address on any network, all routers in the routing domain must “understand” CIDR notation Chapter 2 43 2 Public Versus Private IP Addresses • The private IP address ranges may be expressed in the form of IP network addresses, as shown in Table 2-4 • Private IP addresses have one other noteworthy limitation Chapter 2 44 2 Public Versus Private IP Addresses • Some IP services require what’s called a secure end-to-end connection—IP traffic must be able to move in encrypted form between the sender and receiver without intermediate translation • Most organizations need public IP addresses only for two classes of equipment: – Devices that permit organizations to attach networks to the Internet – Servers that are designed to be accessible to the Internet Chapter 2 45 2 Managing Access to IP Address Information • Although use of private IP addresses mandates NAT or a similar address substitutions or masquerade capability, some organizations elect to use address substitutions or masquerade even when they use perfectly valid public IP addresses on their internal networks • Proxy servers can provide what is sometimes called reverse proxying • This permits the proxy server to front for servers inside the boundary by advertising only the proxy server’s address to the outside world, and then forwarding only legitimate requests for service to internal servers for further processing Chapter 2 46 2 Obtaining Public IP Addresses • Unless you work for an organization that has possessed its own public IP addresses since the 1980s (or acquired such addresses through merger or acquisition), it’s highly likely that whatever public IP addresses your organization uses were issued by the very same ISP who provides your organization with Internet access • Because all devices accessible to the Internet must have public IP addresses, changing providers often means going through a tedious exercise called IP renumbering Chapter 2 47 2 IP Addressing Schemes • To the uninitiated, it may appear that all these IP addresses are randomly assigned, or perhaps generated automatically by some computer somewhere • A great deal of thought has gone into the strategy for allocating IP addresses around the world Chapter 2 48 2 The Network Space • There are a number of critical factors that typically constrain IP addressing schemes, and we look at these in two groups • The first group of constraints determines the number and size of networks • These are: – Number of physical locations – Number of network devices at each location – Amount of broadcast traffic at each location – Availability of IP addresses – Delay caused by routing from one network to another Chapter 2 49 2 The Network Space • In most routers, the Layer 3 routing decisions are typically made by software, so it’s relatively slow when compared to similar decisions made at Layer 2 by switches • This is because switches make their decisions with specialized hardware known as Application Specific Integrated Circuits (ASICs) • A relatively new device known as a layer-3 switch simply implements the layer-3 logic from the software into its own ASICs Chapter 2 50 2 The Network Space • The second group that helps users determine how to choose which IP addresses go where are design objectives: – Minimize the size of the routing tables – Minimize the time required for the network to “converge” – Maximize flexibility and facilitate management and troubleshooting • We already defined a number of networks necessary, so how do we reduce the number of routes in the routing table? The answer is called route aggregation, or summary addresses Chapter 2 51 2 The Host Space • Now that you understand some of the factors involved in numbering the networks, let’s take a brief look at assigning IP addresses to hosts • The advantage of a well-thought-out host naming strategy are a more flexible environment, and one that is easier to support • You can easily identify devices by their IP addresses, regardless of which office they’re in Chapter 2 52 2 Summary • IP addresses provide the foundation for identifying individual network interfaces (and therefore computers or other devices as well) on TCP/IP networks • IP addresses come in five classes named A through E • Classes A through C use the IPv4 32-bit address to establish different break points between the network and host portions of such network addresses Chapter 2 53 2 Summary • Understanding binary arithmetic is essential to knowing how to deal with IP addresses, particularly when working with subnet masks • To help ease address scarcity, the IETF created a form of classless addressing called Classless Inter-Domain Routing (CIDR) that permits the network-host boundary to fall away from octet boundaries • Likewise, to make best use of IP network addresses, a technique called subnetting permits additional bits to be taken from the host portion of a network Chapter 2 54 2 Summary • Several techniques exist to hide internal network IP addresses from outside view, including address masquerading and address substitution • Within the Class A, B, and C IP address ranges, the IETF has reserved private IP addresses or address ranges • When it comes to obtaining public IP addresses, the Internet Corporation for Assigned Names and Numbers (ICANN), previously the Internet Assigned Numbers Authority, or IANA, handled this task) is the ultimate authority Chapter 2 55