CS475 – Networks Reminders Lecture 18 Chapter 5: End-to-End Protocols
advertisement

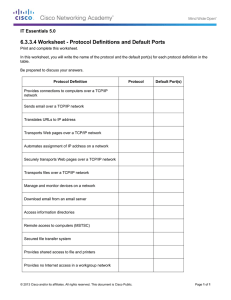
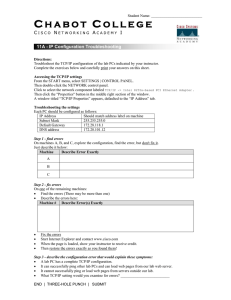
CS475 – Networks Lecture 18 Chapter 5: End-to-End Protocols Reminders • Homework 5, Wireshark Project 3, and Programming Project 3 due today. Chapter 5: End-to-End Protocols We've covered connecting computers. The ________________ messages, synchronization, flow control, support for multiple layer deals with connecting processes running on computers. processes. A transport protocol may be expected to provide: guaranteed Lower layers may: drop messages, reorder messages, deliver delivery, in-order delivery, no duplicates, support for large duplicates, limit message size, deliver after a long delay. 5.1 Simple Demultiplexer (UDP) UDP extends the host-to-host service of the network to a process-to-process service but adds no other functionality. UDP uses 16-bit port numbers to _______________________ between processes. (A process is identified with a port number/IP number pair.) Implementation of the port abstraction may vary from OS to OS. UDP header format Typically, each port is associated with a message queue. When a process receives a message one is removed from the queue. How does a client know which port to send a message to on the process on a well-known port. The client communicated with server? The server may use a well-known port (see /etc/services the port mapper to find the port number of the desired process. on a UNIX machine). UDP does employ a checksum to verify a message. Packets with Alternatively, the server could run a _______________________ errors are dropped. 5.2 Reliable Byte Stream (TCP) In addition to demultiplexing, TCP provides guaranteed, reliable, Flow control prevents the sender from overwhelming the in-order delivery with flow and congestion control. TCP receiver. ___________________________ control prevents the connections are full-duplex. sender from overwhelming the network (switches, links). 10/27/2011 Page 1 of 6 5.2.1 End-to-End Issues The sliding window algorithm used by TCP is like that used on a 3. point-to-point link (Section 2.5.2), but there are important lifetime or MSL is typically 120 s) differences: 1. 4. Setup (exchange of state so the sliding window Resources are not tied to a single link and can not be determined in advance (flow control needed), algorithm can start) and teardown are needed 2. Packets can be reordered (the maximum segment 5. Congestion is possible (congestion control needed) RTTs are variable, so timeouts must be ____________, 5.2.2 Segment Format TCP is a ____________________ protocol. Bytes are normally collected into segments before before being sent to the The TCP header is shown above. A TCP connection is identified destination. by the 4-tuple (SrcPort, SrcIPAddr, DstPort, DstIPAddr). The HdrLen is the size of the header in 32-bit words. The Acknowledgment, SequenceNum and AdvertisedWindow The Flags field contains 6 bits: SYN, FIN, RESET, PUSH, fields are used by the _________________________ algorithm. URG, and ACK. Each transmitted byte has a corresponding SequenceNum. Acknowledgment and AdvertisedWindow are associated with • SYN and FIN are used to set up a connection. • RESET indicates that the receiver is confused and received data. wants to abort the connection. • PUSH indicates that data should be send immediately. • URG signifies that the segment contains urgent data. The UrgPtr field contains the number of urgent data bytes. • 10/27/2011 Page 2 of 6 ACK is set when the Acknowledgment field is valid. 5.2.3 Connection Establishment A three-way ______________________ is used to set up the connection. Packets contain the initial sequence numbers to be used by the client and the server (x and y) in subsequent packets. The TCP specification requires that the initial sequence numbers be random numbers. A trans.diagram for TCP setup and tear down is shown above. Rectangles show states. Arcs have tags of the form event/action. Retransmissions due to __________________ are not shown. 5.2.4 Sliding Window Revisited The sliding window algorithm discussed previously provided while on the receiver: reliable, in-order delivery. TCP's sliding window algorithm LastByteRead < NextByteExpected ≤ LastByteRcvd + 1 extends the prior one by adding _______________________. Flow control is achieved by having the receiver advertise a window size to the sender instead of using a fixed-size window. Assume the send and receive buffers are of size MaxSendBuffer and MaxRcvBuffer. On the receive side TCP must keep: LastByteRcvd – LastByteRead ≤ MaxRcvBuffer The sender is limited to sending no more than AdvertisedWindow bytes of unacknowledged data at any time. The advertised window size is AdvertisedWindow = MaxRcvBuffer – ((NextByteExpected – 1) – LastByteRead) On the sending side TCP ensures: LastByteSent–LastByteAcked ≤ AdvertisedWindow while maintaining LastByteWritten – LastByteAcked ≤ MaxSendBuffer If the sending process tries to write n bytes in such a way that The sender maintains three pointers where: LastByteAcked ≤ LastByteSent ≤ LastByteWritten this inequality would not be maintained then the process is ______________________. 10/27/2011 Page 3 of 6 A 32-bit sequence number will wrap around in 57 minutes at a should be large enough to allow for a full delay x BW product. 10 Mbps transmit rate, but in only _________ seconds at 1 A cross country delay of 100 ms at 10 Mbps corresponds to 122 Gbps. An extension to TCP extends the sequence number space. KB. The TCP extension increases the advertised window size A 16-bit AdvertisedWindow field allows for a 64 KB window. It also. 5.2.5 Triggering Transmission TCP will transmit a segment when (1) it has collected a Nagle's Algorithm: when there is data to send if both the data and the window ≥ MSS send a full segment else if there is unACKed data in flight buffer data until ACK arrives else send all data now maximum segment size (MSS) number of bytes, (2) the sending process tells it too (a ______________), or (3) a “timer” expires. 5.2.6 Adaptive Retransmission Originally, a TimeOut value for retransmission was computed using: EstimatedRTT = α EstimatedRTT + (1 – α)SampleRTT TimeOut = 2 x EstimatedRTT where SampleRTT is the time between when a segment is sent and its _____________________ arrives. The original TCP spec recommended a value of α between 0.8 Unfortunately an ACK for a retransmission is identical to an ACK for the original. This can lead to incorrect values for and 0.9. _______________________. The Karn/Partridge algorithm fixed the problem quite simply. The original algorithm did not handle situations in which the SampleRTT was measured only for segments that have been SampleRTT might _________________ a lot. The sent once. Jackobson/Karels algorithm was an improvement: The new algorithm included a second change. After each Difference = SampleRTT – EstimatedRTT retransmit the next timeout value would be set to twice the EstimatedRTT = EstimatedRTT+(δ x Difference) previous timeout value (exponential backoff). This helped to Deviation = Deviation+δ(|Difference|-Deviation) alleviate problems due to network ______________________. TimeOut = μ x EstimatedRTT + φ x Deviation where μ was typically 1 and φ was 4. 10/27/2011 Page 4 of 6 5.2.7 Record Boundaries TCP has two features that allow record boundaries to be put into A TCP push operation can be used to indicate a complete record. the byte stream. (The sockets API does not provide access to the PUSH flag.) TCP allows data to be flagged as urgent or _________________. It is usually simpler for record boundary markers to be inserted Urgent data can be used to indicate the end of a record. by the application. 5.2.8 TCP Extensions There have been four optional extensions to TCP that are to determine if the sequence number has wrapped implemented using Options in the TCP header: around. 1. The sender places a 32-bit _______________________ 3. in the header. The receiver echoes the time stamp in the ACK. This allows for accurate measurement of the 2. larger than 64 KB. 4. The receiver can respond with a selective RTT. acknowledgment (______________). This allows the The sequence number and the time stamp are examined sender to transmit just missing segments. 5.2.9 Performace Now that we have a complete protocol graph, we can discuss how to measure its performance as seen by applications. In particular, as network speeds increase, can a protocol like TCP provide enough data to keep the network full? Simple host-to-host in a room. 2 2.4GHz dual cores; 2 Gbps bandwidth. TTCP benchmark using various sizes of messages. Note: "perfect" network, measures TCP implementation and workstation hardware/software only. Will see other issues like ____________________. 10/27/2011 A scaling factor can be included to advertise a window Page 5 of 6 5.2.10 Alternative Design Choices TCP is a stream-oriented protocol as opposed to a request/reply TCP uses connection setup and teardown. It is possible to send protocol. We will examine a request/reply protocol (_________) all connection parameters with the first data message. TCP setup next time. (TCP can be used for request/reply applications, but allows a receiver to reject a connection before any data is sent. there are complications.) TCP teardown means that “____________________” messages TCP is a byte-stream rather than a message-stream service. don't need to be sent. (Record boundaries can however be inserted into the byte TCP uses window-based versus rate-based flow control. There stream.) are similarities but also some interesting differences. In Class Exercise Log on locally under Linux or log on remotely to csserver to answer the following questions: • How do we send out-of-band data via TCP? (man send) • How do we receive out-of-band data? (man recv) • Which of the four TCP extensions described in class are supported under Linux? (man tcp) • What acronym is used for the TCP extension that helps to determine if the sequence number has wrapped around? What does this acronym stand for? • Is there a way to disable Nagle's algorithm so that segments are sent immediately? If so, how? The Linux /proc pseudo-filesystem interface can be used to tune many of the TCP algorithms. Changing the parameters requires system administration privileges. Use cat to examine appropriate /proc file contents (man tcp) and determine the answers to the following: • Is the optional SACK extension enabled? • What is the default receive buffer size? • Is the optional window scaling extension enabled? • What is the default congestion control algorithm? Which algorithms are available for use? 10/27/2011 Page 6 of 6