From: AAAI Technical Report WS-02-06. Compilation copyright © 2002, AAAI (www.aaai.org). All rights reserved.
Price-oriented, Rationing-free Protocol: Guideline for Designing
Strategy/False-name Proof Auction Protocols
Makoto Yokoo and Yuko Sakurai
Kenji Terada
NTTCorporation
NTTCorporation
NTr CommunicationScience Laboratories
NTTInformation Sharing Platform Laboratories
2-4 Hikaridai, Seika-cho
3-9-11 Midori-cho
Soraku-gun, Kyoto 619-0237 Japan
Musashino, Tokyo 180-8585, Japan
email: {yokoo,yuko}@cslab.kecl.ntt.co.jp
email: terada.kenji @lab.ntt.co.jp
http’J/www.kecl.ntt.co.jp/csl/ccrg/members/{yokoo, yuko}
Abstract
to profit from submitting false bids madeunder fictitious
names, e.g., multiple e-mail addresses (Sakurai, Yokoo,
& Matsubara 1999; Yokoo, Sakurai, & Matsubara 2001b).
Sucha dishonestaction is very difficult to detect since identifying each participant on the Internet is virtually impossible. Comparedwith collusion (Klemperer1999), a falsenamebid is easier to execute since it can be done by someone acting alone. Wecan consider false-name bids a very
restricted subset of general collusion.
Yokooet al. have been conducted a series of works on
false-name bids. Their results can be summarizedas follows.
Weidentify a distinctive class of combinatorial
auctionprotocols called a Price-oriented, Rationing-free(PORF)
protocol, whichcan be used as a guideline for developing
strategy/false-name proof protocols. APORF
protocol is
automaticallyguaranteedto be strategy-proof,i.e., for each
agent,declaringits true evaluationvaluesis an optimalstrategyregardlessof the declarationsof other agents. Furthermore,if a PORF
protocolsatisfies additionalconditions,the
protocolis also guaranteed
to be false-name-proof,
that is, it
eliminatesthe benefits fromusingfalse-name
bids, i.e., bids
submittedundermultiplefictitious namessuch as multiple
e-mailaddresses.ForIntemetauctionprotocols,beingfalsename-proof
is importantsince identifyingeachparticipanton
the Intemetis virtuallyimpossible.
Thecharacteristics of a PORF
protocol are as follows. For
each agent, the price of eachbundleof goodsis presented.
Thisprice is determined
basedon the declaredevaluationvalues of otheragents,whileit is independent
of its owndeclaration. Then,eachagent can choosethe bundlethat maximizes
its utility independently
of the allocationsof otheragents(i.e.,
mOoning-free).Weshowthat an existing false-name-proof
protocol can be representedas a PORF
protocol. Furthermore,wedevelopa newfalse-name-proofPORF
protocol.
¯ The generalized Vickrey auction protocol (GVA)(Varian
1995), whichis strategy-proof, individually rational, and
Pareto efficient, if there exists no false-namebid, is no
longer strategy-proof whenfalse-namebids are possible,
i.e., the GVA
is not false-name-proof(Sakurai, Yokoo,
Matsubara 1999; Yokoo,Sakurai, & Matsubara 2000).
¯ There exists no false-name-proof combinatorial auction
protocol that simultaneously satisfies Pareto efficiency
and individual rationality (Sakurai, Yokoo,&Matsubara
1999; Yokoo,Sakurai, & Matsubara2000).
Introduction
Internet auctions have becomean especially popular part of
Electronic Commerce(EC). Amongvarious studies related
to Interact auctions, those on combinatorial auctions have
lately attracted considerable attention (Fujishima, LeytonBrown, & Shoham1999; Klemperer 1999; Sandholm 1999;
Lehmann, O’Callaghan, & Shoham1999). Although conventional auctions sell a single item at a time, combinatorial auctions sell multiple items with interdependentvalues simultaneously and allow the bidders to bid on any
combination of items. In a combinatorial auction, a bidder can express complementary/substitutable preferences
over multiple bids. By taking into account complementary/substitutable preferences, we can increase the participants’ utilities and the revenueof the seller.
However,the possibility of a newtype of cheating called
false-namebids has been pointed out, i.e., an agent maytry
Copyright© 2002, American
Associationfor Artificial Intelligence(www.aaai.org).
All rights reserved.
119
¯ A false-name-proofcombinatorial auction protocol called
the LDSprotocol (Yokoo, Sakurai, & Matsubara 2001b)
and a false-name-proofmulti-unit auction protocol called
the IR protocol (Yokoo, Sakurai, & Matsubara 2001c)
were developed.
Developinga strategy/false-name proof protocol has been
a difficult task. In this paper, we identify a distinctive
class of combinatorial auction protocols called a Priceoriented, Rationing-free (PORF)protocol. The notion
a PORFprotocol can be used as a guideline for developing strategy/false-name protocols. Morespecifically, if a
protocol can be represented as a PORFprotocol, it is automatically guaranteed to be strategy-proof. Furthermore,
if a PORF
protocol satisfies additional conditions, it is also
guaranteed to be false-name-proof.
In a PORF
protocol, for each agent, the price of each bundle of goods is presented. This price is determined based
on the declared evaluation values of other agents, while it
must be independent of its own declarations. Then, each
agent can choosethe bundle that maximizesits utility based
on the presented prices, independentlyof the allocations of
other agents.
A PORFprotocol is different from a normal fixed-price
mechanism,where fixed prices of goods/bundles are determined, and agents choose one or a set of bundles they are
willing to buy, then the auctioneertries to ration the allocation, e.g., to choosewinners by using a lottery. In a PORF
protocol, the auctioneer doesnot try to ration the allocation,
i.e., if an agent is willing to buya bundle,the agent is guaranteed to obtain the bundle regardless of the allocations of
other agents. In a PORF
protocol, the auctioneer must carefully determinethe prices so that a feasible allocation, i.e.,
the allocation wherethe samegoodis not allocated to different agents, can be obtained without using a lottery.
Weshow that various protocols, including the existing false-name-proof protocol called LDSprotocol (Yokoo,
Sakurai, & Matsubara2001b) can be represented as a PORF
protocol. Furthermore, we develop a new false-name-proof
PORFprotocol and compareit with the LDSprotocol.
Preliminaries
Here, we introduce several basic terms and concepts.
Weconcentrate on private value auctions (Mas-Colell,
Whinston, & Green 1995). In private value auctions, each
agent knowswith certainty its ownevaluation values of
goods, which are independent of the other agents’ evaluation values. Wedefine an agent’s utility as the difference
betweenthis private value of the allocated bundle, i.e., a
set of goods, and its payment.Such a utility is called a
quasi-linear utility (Mas-Colell, Whinston,&Green 1995).
These assumptions are commonlyused for makingtheoretical analyses tractable. Formally, we assumethat for each
agent i, its type Oi is drawnfrom a set O. The utility of
agent i, whoobtains bundle B and an amountof moneyt~,
is represented
as v ( B, Oi) +ti, wherev ( B, Oi) representsthe
private value of agent i for bundle B.
In a traditional definition (Mas-Colell, Whinston,
Green1995), an auction protocol is (dominant-strategy) incentive compatible(or strategy-proof)if biddingthe true private values of goods is a dominantstrategy for each agent,
i.e., an optimal strategy regardless of the actions of other
agents. Therevelation principle states that in the design of
an auction protocol we can restrict our attention to incentive compatible protocols without loss of generality (MasColell, Whinston, & Green 1995; Yokoo, Sakurai, & Matsubara 2000). In other words, if a certain property (e.g.,
Pareto efficiency) can be achieved using someauction protocol in a dominant-strategyequilibrium, i.e., a combination
of dominantstrategies of agents, the property can also be
achieved using an incentive compatibleauction protocol.
In this paper, we extend the traditional definition of incentive compatibility so that it can address false-namebid
manipulations, i.e., we define that an auction protocol is
(dominant-strategy)incentive compatibleif bidding the true
private values of goodsby using the true identifier is a dominant strategy for each agent. To distinguish the traditional
and extendeddefinition of incentive compatibility, we refer
to the traditional definition as strategy-proof and to the extended definition as false-name-proof.
Wesay an auction protocol is Pareto efficient whenthe
sumof all participants’ utilities (including that of the auctioneer), i.e., the social surplus, is maximized
in a dominantstrategy equilibrium. An auction protocol is individually
rational if no participant suffers any loss in a dominantstrategy equilibrium, i.e., the paymentnever exceeds the
evaluation value of the obtained goods. In a private value
auction, individual rationality is indispensable; no agent
wants to participate in an auction whereit might be charged
moremoneythan it is willing to pay. Therefore, in this paper, werestrict our attention to individually rational protocols.
Price-oriented,
Rationing-free Protocol
Weshow the overview of a PORFprotocol.
¯ Weassume there is a set of goods M= {1, 2,..., m}.
For each bundle B C M, each agent declares its (not
necessarily true) evaluation value.
¯ For each agent i, the price of each bundleB is calculated.
This price can be a differentialprice, i.e., the price of the
samebundlecan vary for different agents. Also, the price
for bundleB does not necessarily haveto be additive, i.e.,
the sumof the prices of the goodsin the bundle. The price
can be super-additive (morethan the sum) or sub-additive
(less than the sum).
¯ Theprice for agent i is totally independentof its owndeclared evaluation values, while it is basedon the declared
evaluation values of the agents other than i.
¯ For agent i, a bundlethat maximizes
its utility is allocated
underthe given prices. If there exist multiple bundlesthat
maximizei’s utility, the auctioneer can coordinate the allocation and choosesa feasible allocation, i.e., the allocation wherethe samegoodis not allocated to different
agents.
¯ Unless agent i is totally indifferent amongmultiple bundies, the auctioneer does not coordinate the allocation,
i.e., the bundle allocated to agent i is determinedindependently of the allocations of the other agents. Wecall
this propertyrationing-free.
Formally, a PORFprotocol can be described as follows.
¯ Eachagent i declares its (not necessarily true) type/~i.
assumean agent can declare multiple types using multiple
identifiers.
¯ Weassume a PORFprotocol is an anonymousprotocol,
where permuting agents’ identifiers does not change the
outcome. Let us represent a set of agents other than
agent i as X and the set of declared types of X as
Ox. The price of agent i for bundle B is represented
as Pn(ex), i.e., the function of ex.
For agent i whodeclares its type as 0i, the auctioneer
chooses a bundle B*, where B* = axgmaxn v(B, 0i)
PB(OX). Such a bundle might not be determined
uniquely. Let us represent the set of such bundles as SB~..
The auctioneer determines an allocation,
g = (B1, B2,...),
where Bi SB* and fo r al l i
120
j, Bi O Bj = 13. If the prices are determined appropriately, we can guarantee that the auctioneer is able to
choosesuch a feasible allocation.
If there exists no false-namebid, i.e., an agent can use
only one identifier, it is obvious that a PORF
protocol is
strategy-proof. For agent i, its price for a bundle is determinedindependentlyof its declared type. Also, the protocol
is rationing-free, i.e., the bundleallocated to agent i is determined so that its utility is maximized,independently of
the allocations of other agents. Therefore,over-declaringits
evaluation value for bundle B, so that other agents’ prices
for bundle B would increase and they would give up the
idea of buyingB, is totally useless.
Onthe other hand, the auctioneer must set the prices appropriately so that he/she can choosea feasible allocation
without rationing. Wecan see an interesting relationship between a PORFprotocol and a traditional protocol, where a
feasible allocation is determinedfirst, and then the payment
of each agent is determinedbasedon the allocation. In a traditional protocol, it is obviousthat the obtainedallocation is
feasible, but the auctioneer must determinethe paymentappropriately so that the protocol is strategy-proof. In a PORF
protocol,it is obviousthat the protocolis sta’ategy-proof,but
the auctioneer must determine prices appropriately so that
he/she can choosea feasible allocation without rationing.
agent i whenagent i does participate and obtains bundle/3.
In the GVA,we can assumeeach agent is required to pay the
decreased amountof social surplus for other agents caused
by its participation.
The GVAcan be represented as a PORFprotocol, where
PB(OX),i.e., the price of agent i for bundle B, is represented as follows.
PB(OX) = V*(X, M) - V*(X, M
It is straightforwardto showthat the auctioneer can choosea
feasible allocation, whichalso maximizesthe social surplus,
in this PORF
protocol.
Bundle-size Ordered Protocol
Wedescribe a new PORFprotocol that is false-name-proof.
Wecall this protocol Bundle-size Ordered(BSO)protocol.
OverviewThe overview of the BSOprotocol is as follows.
¯ The auctioneer determines the reservation price rj for
each goodj, i.e., the auctioneer will not sell goodj for
less than rj. For simplicity, we assume that all goods
have the same reservation price r. Relaxing this condition is rather straightforward.
¯ Theprice of agent i for bundle/3is determinedas follows.
Let us assumek is the size of bundle B, i.e., the number
of goods in/3. Weassumethe reservation price of bundle
/3 isr x k.
Let us assume/3~represents the bundle that satisfies the
followingconditions.
1. There exists at least one commongood between/3 and
BI, i.e.,/3 O/3’ ~ O.
2. For agent j ¢ i, whosedeclared type is 6, v(B’, ~)
r x k~, wherek’ is the size of Bt, i.e., there exists an
agent whoseevaluation value for/3’ is larger than (or
equal to) the reservation price of/3~.
3. k~ is largest within the bundles that satisfy the above
two conditions.
4. v(/3’, ~.) is largest within the bundlesthat satisfy the
abovethree conditions.
Examples of PORF Protocols
GVA
In the Vickreyauction protocol for a single-item single-unit
auction, the agent whodeclares the highest evaluation value
obtains the goodby payingthe price that is equal to the second highest evaluation value. This protocol can be described
as a PORF
protocol as follows. For agent i, the price of the
goodis the highest evaluationvalue of agents other than i. It
is clear that only one agent is willing to buythe goodexcept
for the case of randomtie-breaking, wherethe utility of the
winneris 0.
In the generalized Vickrey auction protocol (GVA)(Varian 1995), whichcan be used for a combinatorialauction, the
goodsare allocated in a waythat maximizesthe obtained social surplus, i.e., the sumof all participants’utilities including the auctioneer.
To simplify the protocol description, we introducethe following notation. For a set of agents X and a set of goods
S, we define V*(X, S) as the sum of the evaluation values of X when S is allocated optimally amongX. To be
precise, for a possible allocation g ----- (/31,/3%...), where
Uj~x Bj = S and for all x # y, B~ n/3v = O, V*(X, S) is
defined as max9 ~-~d~xv(/3j, Oj), where~ is the declared
type of agent j.
The paymentof agent i whoobtains bundle/3 is represented as follows, whereX is the set of agents other than
i:
V*(X, M) - V*(X, M \
The first term of this formula represents the optimal social surplus whenagent i does not participate in the auction.
Thesecondterm represents the optimal social surplus except
Now,the price of agent i for bundle/3 is defined as follows:
when k~ > k: oo,
when k’ = k: v(B’, ~),
whenk~ < k: r x k.
In short, whenanother agent is willing to pay morethan the
reservation price for bundle B~, whichis larger than/3 and
conflicting with B, i.e., B and B’ have a common
good, then
agent i cannot buy/3. If the sizes are the same, the agent
declaring the highest evaluation value can buy the bundle
with the secondhighest evaluation value. If nobodyis willing to pay morethan the reservation price for a conflicting
bundle with the sameor larger size, then the agent can buy
the bundleat the reservation price.
Example1 Let us assume there are three goods a, b, and
c, and the reservation price for each is 100. There are two
121
agents, agent 1 and agent 2, whosetypes are 01,02, respectively. Theevaluationvalue for a bundlev( B, Oi ) is determinedas follows.
O1
02
(a)
0
0
(b)
0
110
(c) (a,b)
0 210
110 110
(b,c) (a,c)
0
0
110 110
210
110
meve1111
abcd,
j
level 2
level 3
level 4
[ {(a,b,c)}, {(b,c,d)}, {(a,c,d)}
[ {(a,b),(c,d)}, {(a,c),(b,d)}, {(a,d),(b,c)}
[ {(a),(b),(c),(d)}
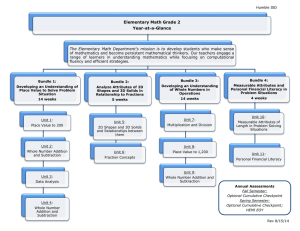
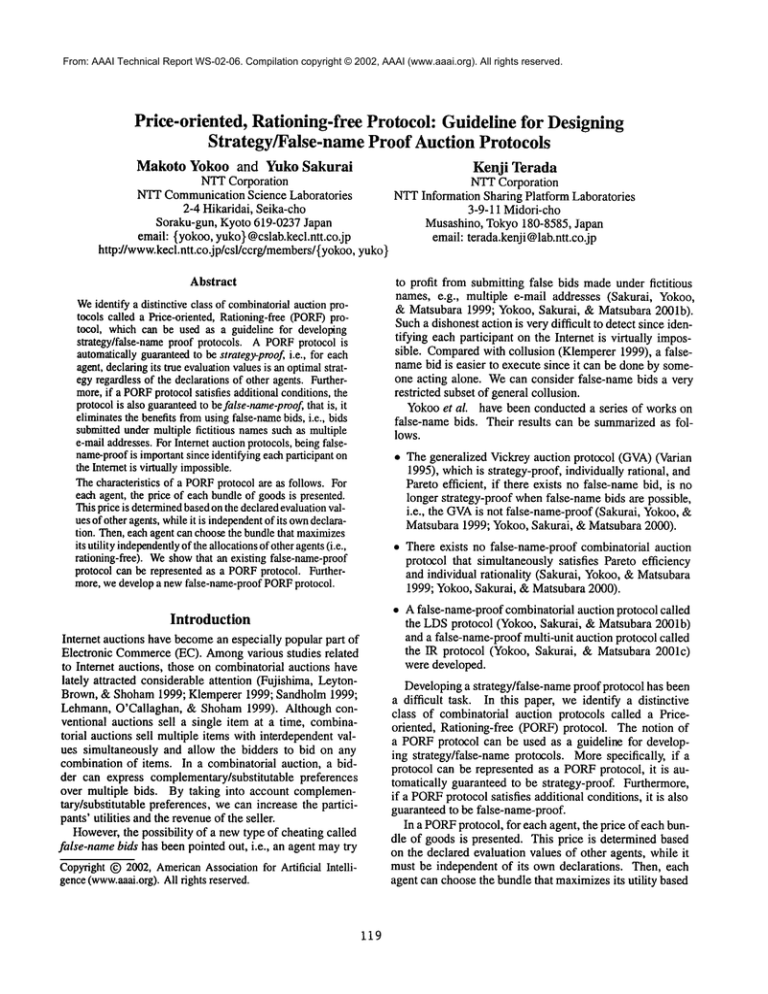
Figure 1: Exampleof Leveled Division Sets
These evaluation values meanthat agem1 needs both a and
b at the sametime, while agent 2 needseither b or c but not
both at the sametime. In this case, the price of agent I for
bundle(a, b), i.e., P(a,b)({ 02} ), 200, i.e ., the reservation
price, the price of agent2 for b, i.e., P(b)( { 01}), is oodue
agent I’s evaluationvalue for (a, b), andthe price of agent2
for¢ i.e., P(e)({01}), is 100, i.e,, the reservationprice. As
a result, agent 1 obtains bundle (a, b) for 200 and agent 2
obtains c for 100.
Example2 The numberof goods and reservation prices are
identical to Example1. Thereexist three agents whosetypes
are as follows.
(a)
(b)
(c) (a,b) (b,c) (a,c)
0
0
0
210
0
0
210
01
0
0
0
0
205
0
02
205
0
0 150
150
03
0
150
150
Agent 1 needs both a and b at the same time and agent 2
needs both b and c at the same time, while agent 3 needs
only a In this case, the price of ageml for bundle(a, b)
205due to agent 2’s evaluation value for (b, c), the price
agent 2for bundle (b, e) is 210 due to agent l’s evaluation
value for (a, b), andthe price of agent 3for c is co due
agent 2"s evaluation value for (b, c). As a result, agent
obtains bundle(a, b) for 205, while c cannotbe allocated.
Allocation Feasibility Here, we showthat the auctioneer
can alwayschoosea feasible allocation in the BSOprotocol.
Morespecifically, we showthat for any bundle that contains
gooda, there exists at mostone agent whois willing to buy
such a bundle, except whenmultiple agents are willing to
buy the bundlebut the utilities of these agents are 0. If the
utility of an agent is 0, the agent is indifferent betweenobtaining and not obtainingthe bundle. Therefore, the auctioneer can coordinate and choosea feasible allocation.
First, let us choosethe bundleBm~xthat satisfies the followingconditions.
1. B,,,,,x contains gooda.
2. For agent i, whosetype is 0i, v(Braax, Oi) > r x kmax,
where kma x is the size of Bmax . We assumeeach agent is
declaringits true type since the protocolis strategy-proof.
3. k,n~, is largest within the bundlesthat satisfy the above
twoconditions.
4. v(Bmaz,Oi) is largest within the bundles that satisfy the
abovethree conditions.
For agent j where j # i, the price of agent j for bundle B
that contains a is determinedas follows. Let us represent the
size of B as k. If v(B, 0j) _> r x k, by this wayof choosing
Bmaz, kmaz >_ k holds.
122
whenkr,,a~ > k: co,
when kmax= k: v(Brnax, Oi),
whenk,,,~ < k: r x k.
Whenkmax > k, it is clear that nobody wants B at this
price. Whenk,~x = k, since B,~ is chosen so that
v(Bm~,0i) is maximized,the utility of agent j cannot be
positive by obtaining B at this price, whenk,,,,~ < k, the
utility of agent j cannot be positive since v(B, Oj) < r x
LDS Protocol
In the LDSprotocol, the auctioneer needs to define not only
the reservation price, but also the methodfor dividing goods
into bundles. Thisdescription is called a leveled division set.
Figure 1 showsan exampleof a leveled division set where
there are four goods(a, b, c, and d).
Eachlevel contains a set of divisions, wherea division is
a set of mutually exclusive bundles. The LDSprotocol basically apply the GVA
using divisions from level 1, level 2,
and so on, until someagent can afford to buy a bundle by
paying more than the reservation price. A leveled division
set must be defined so that a union of multiple bundles in
one division is alwaysincluded in a division of an earlier
level. For example,in level 4 of Figure 1, there is a division
{(a),(b),(c),(d)}. Wecan see that all unions of multiple
dies, e.g., {(a,b)}, {(a,b,c)}, appear in earlier levels.
condition is required to makethe protocol false-name-proof.
Please consult (Yokoo,Sakurai, &Matsubara2001b) for details of the LDSprotocol.
The LDSprotocol can be described as a PORFprotocol.
The price of bundle B for agent i is defined as follows. AssumeB is included in a division of level l. If B is not included in any division, the price is co. Also, let us assume
l,mn represents the earliest level, whereanother agent wants
to buya bundle in level lm~nby paying morethan the reservation price.
when lmin < l: co,
whenlmin = l: the price for B is determinedby the same
method as the GVA,where possible allocations are restricted by the divisions of level l,
whenlmin > l: the reservation price.
Dueto space limitations, we omit a detailed explanation,
but wecan showthat by using this protocol description, the
obtained results are identical to that by the LDSprotocol
presented in (Yokoo, Sakurai, &Matsubara2001b).
False-name-proof PORFProtocol
Weshow that a PORFprotocol is false-name-proof if the
protocol satisfies followingtwo additional conditions.
monotonleprice increase: Whenthe number of other
agents increases, the price of an agent does not decrease.
Formally,for any set of agent X, agent i whois not in X,
and any bundle B, PB(Ox) <_ PB(OXU {01}) holds.
-= f I-°-LDS
no sulmr-additiveprice increase: For any mutually exclusive bundles B, B~, /any set of agents X, and agents i, i
whoare not in X, PB(OXO {0¢ }) + P/3, (Ox 13 {0i})
PBtm,(Ox)holds. The first term in the left side represents the price of agent i for bundle13, the secondterm in
the left side represents the price of agent i I ~,
for bundleB
and the right side represents the price for bundlet3 u B’
for agent i (or i’) whenagents other than i (or i’) are
X.
I f
-~
I
-k
/
Here, we showthat a PORF
protocol that satisfies the above
two conditions is false-name-proof. Assumeagent i uses
twoidentifiers i, i’. If the agent obtains bundle/7only with
one identifier, say, i, then by the condition of monotonic
price increase, the price of i for bundle/3 decreases or remains the same when agent i refrains from using another
~.
identifieri
On the other hand, if the agent obtains bundle t3 under
identifier i and bundleB’ underidentifier i’, by the condition
of no super-additiveprice increase, if the agent uses a single
identifier, the price of B 13 B~ becomessmaller than (or the
sameas) the sumof the prices for B and/3’.
Whenan agent uses three or more identifiers, by using
a similar argumentwe can showthat the agent’s utility increases or at least remains the same when the agent uses
onlyone identifier.
Now,let us showthat the BSOprotocol satisfies these two
conditions. It is obviousthat the protocol satisfies the condition of monotonicprice increase. For the condition of no
super-additiveprice increase, it is clear that the conditionis
satisfied whenPBt.tB’ ({~X) is the reservationprice, since the
price of a bundleis never less than the reservation price. On
the other hand, if Pooo, (Ox) is not the reservation price,
i.e., it is larger than the reservation price, then, there exists a bundle B’~ that has at least one commongood with
B 13 BI, wherethe size of B" is larger than or the sameas
B U/3’ and the evaluation value for B’~ of one agent in X is
larger than or equal to the reservation price. Therefore, either PB(OxO {Ov}) or PB,(Ox 13 {Oi}) becomesoo, thus
the conditionof no super-additive price increase holds.
On the other hand, the GVA
fails to satisfy both conditions. Therefore, as shownin (Sakurai, Yokoo,&Matsubara
1999; Yokoo,Sakurai, & Matsubara 2001b), an agent can
decrease its paymentby using false-names and splitting its
bid.
Evaluations
Wecomparethe obtained social surplus of the BSOprotocol
and that of the LDSprotocol using a simulation.
For each agent i, we determine bundle/3 required by
agent i and v(B, Oi) by the following method.
t First, we determinek, whichrepresents the size of bundle
B, by using an exponential distribution de(k) = -pk
(Fujishima, Leyton-Brown, & Shoham1999). By using
123
<o.1:
i
0
.,
i
,
I.
i
i
,
,
I
,
0.5
1
Reservation Price
1.5
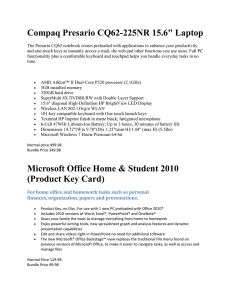
Figure 2: Comparisonof Social Surplus
this distribution, manysmall bundles are created. The
provability that a size k bundleis created is ep times larger
than that of a size k + 1 bundle.
¯ Next, we randomly choose k goods included in/3 and
choose randomlyv(B, 0~) from within the range of
[(1 - q)k, (1 + q)k]. Weassumethat the evaluation values
of an agent are all-or-nothing, i.e., the evaluationvalue for
a bundlethat does not include all of the goodsin/3 is 0.
In the LDSprotocol, the auctioneer must determinea leveled division set. In this evaluation, we construct a leveled
divisionset similar to that in Figure1, i.e., at level 1, weput
a division that contains a single bundle of mgoods. Then,
at level 2, we put m- I divisions, each of whichcontains a
bundle of m- 1 goods, and so on. Morespecifically, we put
divisions that contain size m- 1 + 1 bundles at level l. If
possible, we combinemultiple bundles in a single division,
as shownin level 3 and level 4 in Figure 1. By using this
method,we can put all small bundles in the leveled division
set.
Figure 2 showsthe average ratio of the obtained social
surplus to the Pareto efficient social surplus by varying the
reservation price. In Figure 2, we set the numberof goods
m = 100, the numberof agents n = 100, p = 1, and q --0.5. Eachdata point represents the average of 100 problem
instances.
As shownin Figure 2, by setting the reservation price
within the range of [0.75, 0.98], the obtained social surplus
of the BSOprotocol can reach 70%of the Pareto efficient
social surplus. Onthe other hand, in the LDSprotocol, the
obtained social surplus becomesat most 11%.
In this problemsetting, most bundles consist of one or
two goods, while there are a few bundles with size 7 or 8.
Whenthe reservation price is very small, both protocols sell
a size mbundle to a single agent. By increasing the reservation price, the BSOprotocol can allocate multiple bun-
o I LDSl/
/
1.2 -o-
~0.9
¯ ~0.7
0.2~
0"10
0
I
/
However,as in the case of the GVA,LDS,and BSOprotocols, wecan describe a protocol either as a PORF
protocol or
as the traditional mannerin whichan allocation of goodsis
determined, then the paymentsare calculated based on the
allocation. Wecan assume that the description of a PORF
protocol is not for an actual implementationbut for a normativeguideline for provingcharacteristics of a protocol.
As far as the authors are aware, all knownfalse-nameproof protocols, including the IR protocol (Yokoo, Sakurai, &Matsubara2001c)for multi-trait auctions, can be described as a PORF
protocol. Aninteresting open question is
whether any false-name-proofprotocol can be described as a
PORF
protocol that satisfies the aboveadditional conditions.
In comparing the LDSand BSOprotocols, we can see
that each protocol has its merits and demerits. In the previous section, we assumethat the auctioneer does not have
goodknowledgeof the possible evaluation values of agents.
Therefore, the auctioneer mustuse a leveled division set that
contains all possible small-sized bundles. Onthe other hand,
when the auctioneer has good knowledgeof the possible
evaluation values of agents, the auctioneer can construct a
more specialized leveled division set using the methoddescribed in (Yokoo, Sakurai, &Matsubara 2001a). In this
case, the social surplus obtained by the LDSprotocol becomesclose to a Pareto efficient social surplus, whichwould
be muchbetter than that of the BSOprotocol.
While the LDSprotocol is based on the GVA,the BSO
protocol is similar to a greedy protocol for single-minded
bidders described in (Lehmann, O’Callaghan, & Shoham
1999). A single-mindedbidder is an agent whois interested
in only one particular bundle. In the BSOprotocol, when
determiningthe price of an agent, the protocol treats other
agents as if they are a collection of single-mindedbidders
without considering the substitutable preferences of these
agents.
\_
\
0.5
1
Reservation Price
1.5
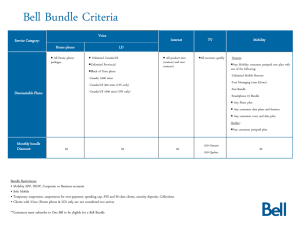
Figure 3: Comparisonof Revenue
dies with different sizes to different agents. Onthe other
hand, in the LDSprotocol, even whenthe reservation price
increases, the goodsare sold at the level wherebundles contain 7 or 8 goods, thus the LDSprotocol can allocate only a
few bundles and the obtained social surplus cannot increase
very much.
Evaluations
Figure 3 showsthe average ratio of seller’s revenue to the
revenue obtained by using the GVAassumingthere exists no
false-namebids. Parametersettings are identical to Figure 2.
Wecan see that trends are almost identical to that of the
social surplus, with a notable exception that the ratio can
be morethan 1, i.e., the BSOprotocol can obtain a better
revenuethat that of the GVA,whenthe reservation prices
are set appropriately.
Conclusions
In this paper, we introducedthe conceptof a Price-oriented,
Rationing-free (PORF)protocol. Weshowedthat if a protocol can be represented as a PORFprotocol, the protocol
is automatically guaranteed to be strategy-proof. Also, we
showedthat if the protocol satisfies additional conditions,
the protocol is also guaranteed to be false-name-proof. We
showedthat existing protocols, such as the GVAand LDS,
can be formalized as PORFprotocols.
Furthermore, we developed a new false-name-proof
PORFprotocol called the BSOprotocol and compared it
with the LDSprotocol. Weshowed that the BSOprotocol
can obtain a better social surplus and better revenue than
that of the LDSprotocol whenthe auctioneer does not have
a goodmodelof possible evaluation values of agents.
Discussions
Designinga protocol that is guaranteedto be strategy/falsenameproof has beena difficult task. If the protocol can be
represented as a PORFprotocol, the protocol is automatically strategy-proof. Furthermore,if the protocol satisfies
additional conditions, the protocol is guaranteedto be falsename-proof.
Of course, we need to prove that a PORFprotocol can
obtain a feasible allocation. However,this tends to be much
easier than provinga protocol is false-name-proof,since we
can assumeeach agent declares its true type using a single
identifier.
As for the computationalcost of executing a protocol, a
naive implementationof a PORFprotocol requires calculating prices for all bundles of all agents. Whenthe number
of goods/agents becomeslarge, this computational cost becomesprohibitively high.
References
Fujishima, Y.; Leyton-Brown,K.; and Shoham,Y. 1999.
Tamingthe computation complexity of combinatorial auctions: Optimal and approximate approaches. In Proceedings of the Sixteenth International Joint Conferenceon Artificial Intelligence (IJCAI-99),548-553.
124
Klempcrer,E 1999. Auction theory: A guide to the literature. Journal of EconomicsSurveys 13(3):227-286.
Lehmann,D.; O’Callaghan, L. I.; and Shoham,Y. 1999.
Truth revelation in approximatelyefficient combinatorial
auction. In Proceedings of the First ACMConference on
Electronic Commerce(EC-99), 96-102.
Mas-Colell, A.; Whinston, M. D.; and Green, J. R. 1995.
MicroeconomicTheory. Oxford University Press.
Sakurai, Y.; Yokoo,M.; and Matsubara, S. 1999. A limitation of the Generalized Vickrey Auction in Electronic
Commerce:Robustness against false-name bids. In Proceedings of the Sixteenth NationalConferenceon Artificial
Intelligence (AAAI-99), 86-92.
Sandholm,T. 1999. An algorithm for optimal winner determination in combinatorial auction. In Proceedings of
the Sixteenth International Joint Conferenceon Artificial
Intelligence (IJCAI-99), 542-547.
Varian, H. R. 1995. Economicmechanismdesign for computerized agents. In Proceedingsof the First UsenixWorkshop on Electronic Commerce.
Yokoo,M.; Sakurai, Y.; and Matsubara,S. 2000. The effect
of false-name declarations in mechanismdesign: Towards
collective decision makingon the Internet. In Proceedings
of the Twentieth International Conferenceon Distributed
ComputingSystems ( ICDCS-2000),146-153.
Yokoo, M.; Sakurai, Y.; and Matsubara, S. 2001a. Bundle design in robust combinatorialauction protocol against
false-namebids. In Proceedingsof l 7th International Joint
Conferenceon Artificial Intelligence (1JCAI-2001),10951101.
Yokoo,M.; Sakurai, Y.; and Matsubara, S. 2001b. Robust
combinatorial auction protocol against false-name bids.
Artificial Intelligence 130(2): 167-181.
Yokoo, M.; Sakurai, Y.; and Matsubara, S. 2001c. Robust multi-unit auction protocol against false-name bids.
In Proceedingsof 17th International Joint Conferenceon
Artificial lntelligence ( IJCAI-2001),1089-1094.
125