the 47 PowerPoint ® slides
advertisement

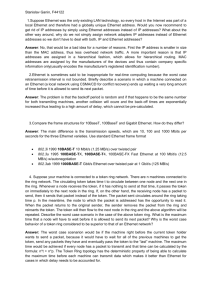
The Workings of the Internet CECS 5030 with Cathie Norris, Jennifer Smolka & Gerald Knezek Overview Layered Organization Topologies Network Transports Access Methods Routing ISO/OSI Model Developed by International Organization for Standardization in 1974 Consists of seven layers Each with unique function Each hands off functions to adjacent layer Modules (layers) may be replaced with another of equal functionality (Xerox vs. Novell, for example) OSI Model Layers OSI Layer Function Provided Application Network applications such as file transfer and terminal emulation Presentation Data formatting and encryption Session Transport Network Establishment and maintenance of sessions Provision for end-to-end reliable and unreliable delivery Delivery of packets of information, which includes routing Data Link Transfer of units of information, framing, and error checking Physical Transmission of binary signal Network Topologies Architectural “drawings” that show the overall physical configuration for a given communications system Determine access methods and rules used to design and implement a communication system Represent the drawing of your network cable plant Three main types: star, ring, and bus Network Topologies Linear Bus - Ethernet/IEEE 802.3 10Base2 and 10Base5 Star Wired Bus - Ethernet/IEEE 802.3i 10BaseT Star Wired Ring - Token Ring/IEEE 802.5 Dual Counter Rotating Ring FDDI/ANSI X3T9.5 Wireless - Product Specific Star Topology First used with the telephone switches Centralized hub with all stations connected No single point of failure effects the whole network, except the hub Oldest and most popular topology Better network management Node Node Central Hub Node Node Ring Topology All stations (repeaters) are enclosed in a loop Each receives the signal and repeats it on the other side to its “downstream” neighbor Data is transmitted in one direction only Single point of failure when one station quits repeating Management processes invoked that dynamically remove a station allowing the ring to return to an operational state Ring Topology Node Transmitter Node Data Direction Receiver Node Repeater Node Bus Topology Also known as linear bus Uses a single length of cable with all stations attached to it The network is terminated at its endpoints (not a closed loop) A break on the single cable will bring down all attachments on the network The bus topology is most commonly used for Ethernet networks Bus Topology Node Node Node Star-Wired Bus Topology Each node is attached to Node Node hub When one node fails, it Node Node doesn’t affect the other nodes Node Node The hub is a single point of failure for all nodes Concentrator Hub failure causes all Hub nodes to lose connectivity Physical Media Physical media provide the connections between network devices that make networking possible There are four main types of physical media in widespread use today: Coaxial Cable Twisted Pair Fiber Optic Cable Wireless Media Thick Coaxial Cable Used in the first Ethernet networks Type RG-11 / 10Base5 Usually orange/black Thickness of a small garden hose Very expensive and heavy cable Two strands along the axis Conductor down the center Insulator surrounds conductor Shielded mesh serves as outside Thin Coaxial Cable Alternative to Thick Ethernet Cable Type RG-58 / 10Base2 / “Cheapnet” Usually black Thickness of a pencil More flexible than thick Ethernet Reduced the cost of the cabling Flexible Twisted Pair Cable Phone Systems Twisted Pair Cable consists of two copper wires, usually twisted around each other to cancel out any noise in the circuit Two main type of Twisted Pair Cabling Shielded Twisted Pair (STP) Unshielded Twisted Pair (UTP) Shielded Twisted Pair (STP) Shielded twisted pair is the original media used for token ring networks STP can be used for high-speed networks, such as FDDI or ATM, where shielding is important Unshielded Twisted Pair (UTP) Most commonly used twisted pair cable Uses common telephone wire UTP was standardized by the IEEE 802.3 committee in October of 1990 UTP for LANs is now classified as: Category 3 - used for LANs up to 10 Mbps Category 4 - used for LANs up to 16 Mbps Category 5 - used for LANs up to 100 Mbps Fiber Optic Cable Uses light signals transmitted over a very thin filament, usually made of glass Advantage over other types of media security against eavesdropping immunity to interference maximum length of a single segment Most expensive of all media Wireless Media Connect your computer to your cell phone? Problems with stability of connection Have wireless for a long time Commercial Satellite Geostationary Orbit Microwave Wavelength Expensive Wireless Media A number of wireless media are used in internetworking, e.g.: Microwave Commercial Radio wave Infrared signaling (Palm Synching) Concentrators/Hubs Hubs allow multiple users to be connected to a single network as a shared device The more users on a hub the slower the response time Network Transports Ethernet / Fast Ethernet / IEEE 802.3 Token Ring / IEEE 802.5 FDDI / FDDI/ANSI X3T9.5 Wireless/IEEE 802.11 Ethernet Cable Names Unshielded Twisted Name Thick Coaxial Thin Coaxial Pair Fiber Wire Type RG-8 RG-58 22 - 26 AWG 62.5/125 micron IEEE Name 10BASE5 10BASE2 10BASET 10BASEF Standard Number IEEE 802.3 IEEE 802.3a IEEE 802.3i NA Other Names Thick net Thin net UTP How Ethernet Works Sent the message and listens for a response An access method based on the Carrier Sense Multiple Access with Collision Detection (CSMA/CD) algorithm Cooperative effort between Digital, Intel, and Xerox produced Ethernet version 1.0 in 1980 How Ethernet Works Ethernet was adopted with modifications by the standards committees IEEE 802.3 and ANSI 8802/3 Most widely used network system today Normal Ethernet Operation B C Address mismatch packet discarded Address mismatch packet discarded Send data to node D Transmitted packet seen A by all stations on the LAN (broadcast medium) Data Address match packet processed D Final Ethernet Issues Ethernet is an access method that strictly adheres to the CSMA/CD algorithm Ethernet is a multiprotocol solution Ethernet is usually hardware (firmware), not software How Token Ring Works Token Ring controls which PC can send messages by passing a token from station to station around the ring When a PC wants to transmit it will replace the token with a “frame” (message) The frame is passed from PC to PC until it reaches its destination How Token Ring Works The destination PC makes a copy of the “frame” (message) and marks the frame to indicate that it got the message The frame circulates around the network until it gets back to the sender The sender, seeing that the message has been received, replaces it with a new token Wide Area Network (WAN) Topologies Dedicated Circuits 56Kb T-1 DS-3 Frame-Relay 56Kb to T-1 speeds Integrated Services Digital Network (ISDN) Inter-networking Networks have their restrictions Thick coaxial cable maximum length is 500 meters LANs are broadcast-oriented Proper network design is impossible using repeaters Inter-networking Properly extending the LAN requires special devices known as bridges and routers A LAN that uses bridges is called an extended LAN A LAN that uses routers is called an internet or inter-network A gateway between dissimilar networks Inter-networking Bridges and routers are data-forwarding devices that forward packets to one or more LANs They allow for more efficient networks to be designed Inter-networking Categories Application Presentation Gateways Session Transport Network Routers Data Link Bridges Physical Repeaters Repeaters Extend the network by interconnecting multiple segments Have transformed into wiring concentrators (hubs) Low cost Can be used to interconnect different wiring types but not different access methods e.g. Coax to twisted pair Bridge Designs Cascaded Locates on bridge next to another in a pillar fashion Backbone For networks with many LANs Backbone cable is run vertically in building’s riser LAN “ribs” run on each floor Star Used in wide area networks or remote bridged networks Cascaded Terminal Server Workstation Terminal Host Cable segment 1 Cable segment 2 Cable segment 3 File Server Backbone Workstation Floor 20 Host Fiber backbone Workstation Terminal Floor 1 Star California Serial line Serial line Texas Virginia Serial line North Carolina Introduction to Routers Routers are data forwarding devices but operate differently than a bridge Routers separate networks into regions. Each region is assigned a unique network number These network numbers are unique for each network they are assigned to Packet forwarding is based on these network Ids Routers route packets based on a protocol as well as a network ID Most routers today are multiprotocol in that one box can forward different protocol packets Routers, like bridges, can be used locally or remotely Routing Most network protocols were designed with network-layer routing Routers base forwarding decisions on an embedded network number in the network layer header of the packet Network numbers can be thought of as area codes in the phone system Must use the area code to call different areas Any number of end stations may be assigned to one network number Most routers do not keep track of individual end stations’ addresses Network numbers group network stations into one or more network numbers Taken as a whole, routers combine networks and form internets Routers - Operation Node D Router sends packet directly to the end station MAC address for the router Destination network number is different Network 2 C Router Z Find router B and give packet to the router Node A Node P Destination network address is local transmit packet directly to the end station Network 1 Routing Diagram G Network 4 Router X H F E Network 3 Router Y D Network 2 C MAC Addresses Router Z B A Network 1 Multiprotocol Routers LANs currently operate with many different types of protocols Apple Computers can use AppleTalk UNIX workstations use TCP/IP Client/Server applications could use Novell NetWare To require one router for each protocol on the LAN is not efficient Multiprotocol routers were invented to handle this Arrived around 1986 Routes not only based on the network IDs but are able to pass the packet to the correct protocol processor by examining the Type of packet Gateways Complex devices that provide for a protocol translation during data forwarding Examples are: TCP/IP to SNA asynchronous to synchronous serial stream Gateways differ from bridges and routers Perform protocol translation of the incoming packet to match the outgoing stream References From Networking 101 Jim Cabral, Puget Technology Group, Inc. & Tammy Ruth, Children’s Hospital and Medical Center www.pugettech.com cabralje@pugettech.com truth@chmc.org