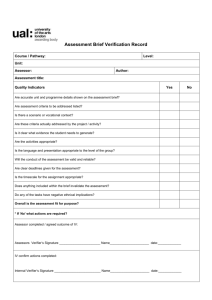
Figure 9-2
advertisement

Security Chapter 9 Panko’s Business Data Networks and Telecommunications, 6th edition Copyright 2006 Prentice-Hall Security Requirements • Authenticity • Confidentiality • Integrity • Non-repudiation • Availability 2 Figure 9-2: Malware • Malware (惡意軟體) – A general name for evil software • Viruses – Pieces of code that attach to other programs – When infected programs execute, the virus executes – Infects other programs on the computer – Spreads to other computers by e-mail attachments, IM, peer-to-peer file transfers, etc. – Antivirus programs are needed to scan arriving files • Also scans for other malware 3 Figure 9-2: Malware • Worms – Stand-alone programs that do not need to attach to other programs – Can propagate like viruses through e-mail, etc. • But this require human gullibility, which is slow – Vulnerability-enabled worms jump to victim hosts directly 漏洞 – Can do this because hosts have vulnerabilities – Vulnerability-enabled worms can spread with amazing speed – Vendors develop patches for vulnerabilities but companies often fail or are slow to apply them 4 Figure 9-2: Malware • Payloads – After propagation, viruses and worms execute their payloads (damage code) – Payloads erase hard disks, send users to pornography sites if they mistype URLs – Trojan horses: exploitation programs disguise (假裝) themselves as system files 5 Figure 9-2: Malware • Attacks on Individuals – Social engineering—tricking the victim into doing something against his or her interests Phishing – Spam—unsolicited(未被懇求的) commercial e-mail – Credit card number theft is performed by carders – Identity theft: collect enough data to impersonate the victim in large financial transactions – Fraud: get-rich-quick schemes(一夜致富法), medical scams(欺詐) 6 Figure 9-2: Malware • Attacks on Individuals – Adware pops up advertisements – Spyware collects sensitive data and sends it to an attacker – Phishing: sophisticated social engineering attack in which an authentic-looking e-mail or website entices the user to enter his or her username, password, or other sensitive information 7 Figure 9-3: Human Break-Ins (Hacking) • Human Break-Ins – Viruses and worms rely on one main attack method – Humans can keep trying different approaches until they succeed • Hacking – Breaking into a computer – Hacking is intentionally using a computer resource without authorization or in excess of authorization 8 Figure 9-3: Human Break-Ins (Hacking) • Scanning Phase – Send attack probes to map the network and identify possible victim hosts – Nmap programming is popular (Figure 9-4) 9 Figure 9-4: Nmap IP Range to Scan Type of Scan Identified Host and Open Ports 10 Figure 9-3: Human Break-Ins (Hacking) (開拓) • The Exploit – The actual break-in – Noun: Exploit is the program used to make the break-in – Verb: Attackers exploit the computer 11 Figure 9-3: Human Break-Ins (Hacking) • After the Break-In – Become invisible by deleting log files – Create a backdoor (way to get back into the computer) • Backdoor account—account with a known password and super user privileges • Backdoor program—program to allow reentry; usually Trojanized • Rootkit—stealthy backdoor that cannot be detected New by the operating system – Do damage at leisure 12 Figure 9-5: Distributed Denial-of-Service Flooding Attack TCP Syn Flooding Attack Command Attacker 1.34.150.37 Attack Command Handler Zombie Attack Command Attack Packet Attack Packet Victim 60.168.47.47 Attack Command Attack Command Zombie Attack Packet Handler Zombie The attacker installs handler and zombie programs on victims The attacker sends an attack command to handlers. Handlers send attack commands to zombies. The zombies overwhelm the victim with attack packets. 13 Figure 9-6: Bots Human Master Command Bot Software Update Bot Bots are like zombies, but they can be updated by the human master to give new functionality. 14 Figure 9-19: Cryptographic Systems • Cryptographic Systems – Provide security to multi-message dialogues • At the Beginning of Each Communication Session – The two parties authenticate each other Party A Party B Credentials Credentials Initial Authentication 15 Figure 9-19: Cryptographic Systems • Message-by-Message Protection – After this initial authentication, cryptographic systems provide protection to every message – Encrypt each message for confidentiality so that eavesdroppers cannot read it Messages Encrypted for Confidentiality Party A Party B 16 Figure 9-19: Cryptographic Systems • Message-by-Message Protection – Adds an electronic signature to each message – The electronic signature authenticates the sender – It also provides message integrity: receiver can tell if a message has been changed in transit Party A Electronic Signature Party B 17 Symmetric and Public Key Encryption Symmetric Key Encryption for Confidentiality Symmetric Key Message Encryption Method & “Hello” Key Encrypted Message Network Party A Party B Encryption uses a non-secret encryption method and a secret key 18 Figure 9-20: Symmetric and Public Key Encryption Symmetric Key Encryption for Confidentiality Symmetric Key Encrypted Message Interceptor Network Party A Encrypted Message Interceptor cannot read encrypted messages Party B 19 Figure 9-20: Symmetric and Public Key Encryption Symmetric Key Encryption for Confidentiality Symmetric Key Message Encryption Method & “Hello” Key Encrypted Message Interceptor Network Party A Encrypted Message Receiver decrypts the message Using the same encryption message And the same symmetric key Same Symmetric Key Decryption Message Method & “Hello” Key Party B 20 Types of Symmetric Key Encryption DES 3DES AES Key Length (bits) 56 112 or 168 128, 192, or 256 Strength Weak Strong Strong to Very Strong Processing Requirements Moderate High Modest RAM Requirements Moderate High Modest 21 Figure 9-20: Symmetric and Public Key Encryption Public Key Encryption for Confidentiality Encrypt with Party B’s Public Key Party A Encrypted Message Decrypt with Party B’s Private Key Note: Four keys are used to encrypt and decrypt in both directions Decrypt with Party A’s Private Key Encrypted Message Party B Encrypt with Party A’s Public Key 22 Figure D-7: Digital Signature Encrypted for Confidentiality DS Plaintext Sender Receiver Add Digital Signature to Each Message Provides Message-by-Message Authentication 23 Figure D-7: Digital Signature: Sender To Create the Digital Signature: 1. Hash the plaintext to create a brief message digest; This is NOT the digital signature 2. Sign (encrypt) the message digest with the sender’s private key to create the digital Signature Hash algorithms: MD5, SHA-1 http://en.wikipedia.org/wiki/MD5 http://en.wikipedia.org/wiki/SHA-1 Plaintext Hash MD Sign (Encrypt) MD with Sender’s Private Key DS 24 Figure D-7: Digital Signature Send Plaintext Plus Digital Signature Encrypted with Symmetric Session Key DS Plaintext Transmission Sender Encrypts Receiver Decrypts the Message, Getting the Plaintext Plus Digital Signature Receiver Decrypts 25 Figure D-7: Digital Signature: Receiver Received Plaintext 1. Hash DS 2. Decrypt with True Party’s Public Key MD 3. Are they Equal? MD 1. Hash the received plaintext with the same hashing algorithm the sender used. This gives the message digest. 2. Decrypt the digital signature with the sender’s public key. This also should give the message digest. 3. If the two match, the message is authenticated; The sender has the true Party’s private key 26 Figure D-8: Public Key Deception Impostor Verifier “I am the True Party.” Must authenticate True Party. “Here is TP’s public key.” (Sends Impostor’s public key) Critical Deception Believes now has TP’s public key “Here is authentication based on TP’s private key.” (Really Impostor’s private key) Believes True Party is authenticated based on Impostor’s public key Decryption of message from Verifier encrypted with Impostor’s public key, so Impostor can decrypt it “True Party, here is a message encrypted with your public key.” 27 Digital Certificates • Digital certificates are electronic documents that give the true party’s name and public key • Applicants claiming to be the true party have their authentication methods tested by this public key • If they are not the true party, they cannot use the true party’s private key and so will not be authenticated • Digital certificates follow the X.509 Standard 28 Figure D-10: Roles of Digital Certificates and Digital Signatures in Authentication • Public key authentication requires both a digital signature and a digital certificate to give the public key needed to test the digital signature Certificate Authority Digital Certificate: True Party’s Public Key Applicant DS Plaintext Verifier 29 Figure D-10: Roles of Digital Certificates and Digital Signatures in Authentication Applicant Certificate Authority Digital Signature Digital Certificate: True Party’s Name and Public Key Must be Tested with True Party’s Digital Certificate Authentication Verifier 30 Figure D-9: Public Key Infrastructure (PKI) 1. Create Public Key/ Private Key Pair Certificate Authority PKI Server Verifier (Cheng) 2. Distribute Private Key Verifier (Brown) Applicant (Lee) 31 Figure D-9: Public Key Infrastructure (PKI) Certificate Authority PKI Server 3. Request Certificate for Lee Verifier (Cheng) 4. Certificate for Lee Verifier (Brown) Applicant (Lee) 32 Figure D-9: Public Key Infrastructure (PKI) Certificate Authority PKI Server 6. Request Certificate Revocation List (CRL) 7. CRL Verifier (Cheng) Verifier (Brown) 5. Certificate for Lee Applicant (Lee) 33 Figure 9-9: Access Control • Companies must then develop an access control plan for each asset – The plan includes the AAA protections – Authentication—proving the identity of the person wishing access – Authorization—determining what the person may do if they are authenticated – Auditing*—logging data on user actions for later appraisal *3rd A: Accounting http://en.wikipedia.org/wiki/AAA_protocol 34 Figure 9-10: Authentication 1. 憑據 Credentials (Password, etc.) Authentication Verifier Server 2. OK? 3. OK and Authorizations 4. Welcome Applicant Verifier Applicant The applicant is the person who wishes to prove his or her identity. The verifier is the person who wants to authenticate the applicant. The applicant sends credentials (passwords, etc.). Usually a central authentication server judges the credentials. This provides consistency in authentication. 35 Figure 9-11: Password Authentication • Passwords should be complex – Mix case (A and a), digits (6), and other keyboard characters ($, #, etc.) – Can only be cracked with brute force attacks (trying all possibilities) • Passwords should be long – Eight characters minimum – Each added character increases the brute force search time by a factor of about 70 36 Figure 9-12: Digital Certificate Authentication • Public and Private Keys – Each party will have both a public key and a private key – Each party makes its public key available to everybody – Each party keeps the private key secret • Digital Certificate – Tamper-proof file giving a party’s public key 37 Figure 9-12: Digital Certificate Authentication • Operation – Applicant performs a computation with his or her private key, which only he or she should know – Verifier tests the calculation with the public key in the digital certificate of the party the applicant claims to be – If the test is successful, the applicant is authenticated as knowing the claimed party’s secret public key – If the test fails, the applicant is rejected 38 Figure 9-12: Digital Certificate Authentication Calculation Digital Certificate Calculation created with the private key of applicant Public key of the person the applicant claims to be Authentication Verifier tests the calculation with the public key of the claimed party. If the test succeeds, the applicant must know the secret private key of the claimed party, which only the claimed party should know. 39 Figure 9-12: Digital Certificate Authentication • Appraisal (評價) – Digital signature authentication gives extremely strong authentication – Very expensive: must set up infrastructure for distributing public-private key pairs – Must do the labor of creating, distributing, and installing private keys. 40 Figure 9-13: Biometric Authentication • Biometric Authentication – Authentication based on bodily measurements – Promises to eliminate passwords • Fingerprint Scanning – Dominates biometrics use today – Simple and inexpensive – Substantial error rate (misidentification) – Often can be fooled fairly easily by determined impostors – Not a problem for low-risk situations like home computers 41 Figure 9-13: Biometric Authentication • Iris Scanners – Scan the iris (colored part of the eye) – Irises are complex, so very strong authentication – Expensive • Face Recognition – Camera allows analysis of facial structure – Can be done surreptitiously—without the knowledge or consent of person being scanned – Very high error rate and easy to fool 42 Figure 9-13: Biometric Authentication • Error Rates and Deception(欺騙) – Error rates are higher than vendors claim – Deception is easier than vendors claim – The usefulness of biometrics is uncertain 43 Figure 9-14: Firewall Operation Allowed Legitimate Packet Hardened Server Attack Packet Internet Firewall Internet Attacker Hardened Client PC Denied Attack Packet Log File Ingress Filtering Legitimate Egress Filtering Packet Internal Corporate Network Legitimate Host Firewalls inspect each packet. Legitimate packets are allowed through. Provable attack packets are dropped and logged. 44 Figure 9-15: Stateful Firewall Filtering • Stateful Firewall Filtering – There are several types of firewall filtering – Stateful inspection is the dominant methodology today – Stateful firewalls often use other filtering mechanisms as secondary mechanisms 45 Figure 9-15: Stateful Firewall Filtering • Connection Initiation – Some Packets Attempt to Open a Connection • Example: packets with TCP segments whose SYN bits are set • Stateful firewalls have default rules for connection-opening attempts Internally Initiated Connections Are Allowed by default Site Stateful Border Firewall Externally Initiated Connections are Rejected By Default 46 Stateful Firewalls All Packets Connection-Opening Attempts Default Behavior for Connections Other Packets Not Part of Previously Permitted Connection Part of Previously Permitted Connection Drop Packet Accept Packet ACL Exceptions 47 Figure 9-15: Stateful Firewall Filtering • Perspective – Simple operation leads to inexpensive stateful firewall operation – However, stateful inspection firewall operation is highly secure 48 Figure 9-17: Ingress Access Control List (ACL) for a Stateful Inspection Firewall • 1. If packet’s source and destination sockets are in the connection table, PASS. – If the packet is part of an previously-established connection, pass it without further filtering. • 2. If the packet’s source and destination sockets are not in the connection table and the packet is not a connection-opening attempt, DROP and LOG. – Drop any packet that is not a connection-opening attempt and that is not part of an established connection. 49 Figure 9-17: Ingress Access Control List (ACL) for a Stateful Inspection Firewall • 3. If protocol = TCP AND destination port number = 25, PASS and add connection to connection table – This rule permits external access to all internal mail servers. • 4. If IP address = 10.47.122.79 AND protocol = TCP AND destination port number = 80, PASS and add connection to connection table. – This rule permits access to a particular webserver, 10.47.122.79 50 Figure 9-17: Ingress Access Control List (ACL) for a Stateful Inspection Firewall • 5. Deny All AND LOG – If earlier rules do not result in a pass or deny decision, this last rule enforces the default rule of banning all externally-initiated connection-opening attempts. 51 Figure 9-18: Firewalls, Intrusion Detection Systems, and Intrusion Prevention Systems • Firewalls – Drop provable attack packets • Intrusion Detection Systems (IDSs) – Very sophisticated filtering—better than firewalls – Identify suspicious packets – Cannot drop--suspicious packets may be legitimate • Intrusion Prevention Systems (IPSs) – Use IDS filtering mechanisms – Drop suspicious packets highly likely to be attacks – Ignore other suspicious packets 52 Figure 9-18: Firewalls, Intrusion Detection Systems, and Intrusion Prevention Systems • IDS and IPS filtering – Stream Analysis • Analyze streams of packets to identify suspicious patterns – Deep packet inspection • Inspect headers and messages at the internet, transport, and application layers 53 Figure 9-18: Firewalls, Intrusion Detection Systems, and Intrusion Prevention Systems Firewalls IDSs IPSs Processing Power Needed Modest Heavy Heavy Maturity Fairly Mature Still immature. Too many false positives New. Tuning reduces false positives but is laborintensive Only used to stop attacks that can be identified fairly accurately. 54