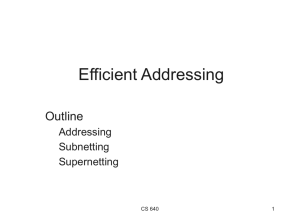
Module 1.0: Introduction

Module 5.1: Internet Protocol
•
TCP/IP Suite
•
IP Addressing
•
ARP
•
RARP
•
DHCP
K. Salah 1
Some Protocols in TCP/IP Suite
K. Salah 2
Address Types
K. Salah 3
Address Relations and Encapsulation
K. Salah 4
IP Addressing
•
IP address is 32 bits
•
Originally had 2 level of hierarchy: network ID and host ID
•
The network ID is assigned by the Internet Network Information Center (InterNIC).
•
Routers use only network ID
•
Five classes of IP This is called “Classful Addressing”
– Identify class by looking at the first byte
0-127 gives A, 128-191 gives B, and 192 to 223 gives C
– A gives 126 networks with 16 million hosts
– B gives 16,382 networks with 64k hosts
– C gives 2 million networks with 254 hosts
K. Salah 5
IP Addressing (Cont.)
•
IP addresses are written in dotted-decimal notations
•
Subnetting
– Calss B address can support 64000 hosts! Hard to manage on a single network.
– Adds another hierarchical level called the “subnet”.
– Every host has its own IP address and its subnet mask. Hence, this host can determine, if a destination IP address is:
On its own subnet
On different subnet, but same own network
On different network
K. Salah 6
IP Addressing (Cont.)
K. Salah 7
Classful vs. Classless Addressing
* Only applicable on directly connected links
K. Salah 8
Classless Inter-Domain Routing (CIDR)
•
Classless Inter-Domain Routing is based on variable-length subnet masking (VLSM) to allow allocation on arbitrary-length prefixes. Variable-length subnet masks are mentioned in RFC
950.
•
CIDR is principally a bitwise, prefix-based standard for the interpretation of IP addresses.
•
These groups, commonly called CIDR blocks , share an initial sequence of bits in the binary representation of their IP addresses.
•
IPv4 CIDR blocks are identified using a syntax similar to that of
IPv4 addresses: a four-part dotted-decimal address, followed by a slash, then a number from 0 to 32: A.B.C.D/N .
K. Salah 9
CIDR Blocks
• All of these CIDR prefixes would be used, at different locations in the network.
• Outside of MCI's network, the 208.128.0.0/11 prefix would be used to direct to MCI traffic bound not only for 208.130.29.33, but also for any of the roughly two million IP addresses with the same initial 11 bits.
• Within MCI's network, 208.130.28.0/22 would become visible, directing traffic to the leased line serving ARS.
• Only within the ARS corporate network would the 208.130.29.0/24 prefix have been used.
K. Salah 10
Special Addresses
•
There are several IP addresses that are reserved for special purposes and are not available for assignment for hosts.
•
Any address with a first octet value of 127 is a
loopback address.
•
A loopback address is used by a host to communicate with itself through TCP/IP. It is also used for testing and diagnostics.
K. Salah 11
•
255 in either the host id or the network id designates a broadcast .
– A message sent to 255.255.255.255 is broadcast to every host on the local network. A message sent to 196.1.64.255 is broadcast for every host on network 196.1.64.
•
0 in both host id and network id can only appear as a source address in
BOOTP protocol in bootstrapping when host is determining its own address.
•
Address Allocation for Private Intranets:
– 10 A single Class A network.
– 172.16 through 172.31 16 contiguous class B network
– 192.168.0 through 192.168.255 256 contiguous Class C networks .
– Any organization can use any address in these ranges without reference to any other organization.
– Routers in networks do not use private addresses, e.g. ISP. Routers quietly discard all routing information regarding these addresses.
– Hosts having only a private IP address do not have IP layer connectivity to the Internet. They have to go through NAT gateway.
K. Salah
Special Addresses (cont.)
12
ARP
•
How does a machine map an IP address to its Data Link layer
(hardware or MAC) address?
•
This is needed by the source host (A) who needs to send an IP packet to another host (B)
– if B is on same IP network as A, address frame to B
– if B on a separate network, address frame to a router
•
TCP/IP solution: Address Resolution Protocol (ARP). See next figure.
•
ARP cache or table is used by hosts to avoid sending ARP request every time. ARP table entries age after a certain time (30 seconds).
K. Salah 13
K. Salah 14
RARP
•
How does a diskless machine (X terminal) determine its IP address?
•
When bootstrap code starts execution on a diskless machine, it must use the network to contact a server to obtain the machine’s IP address
•
Usually, a machine’s IP address is kept on disk where OS finds it at startup
•
RARP is the protocol used to solve the reverse problem solved by ARP
– Given a physical address, get the corresponding IP address
•
The RARP server must be located on the same physical network as the host.
K. Salah 15
K. Salah 16
Encapsulation of ARP and RARP messages in Ethernet frames
Note : The types above are unique. The length field is constant which is 2 bytes.
The value of both types are more than 1500 bytes.
K. Salah 17
BOOTP and DHCP
•
A host requires three elements to connect to the Internet:
– IP address
– subnet mask
– nearby router
•
BOOTP (Bootstrap Protocol) provided such information to hosts.
•
DHCP (Dynamic Host Configuration Protocol) builds on the capability of
BOOTP.
•
DHCP is widely used because it provides a mechanism for assigning temporary IP addresses to hosts.
•
ISP uses DHCP to maximize the usage of their limited IP address space.
•
Typical messages used by DHCP:
– DHCP Discover – broadcast initiated by host
– DHCP Offer – reply by DHCP server(s) offering service to host
– DHCP request – used by host to request info from a particular server.
– DHCP ACK – reply by the selected server to host.
K. Salah 18
Passing of IP packet.
K. Salah 19