OneClick-CITP
advertisement

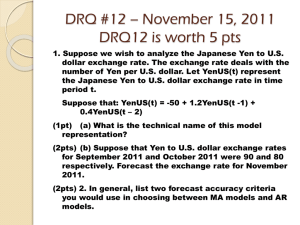
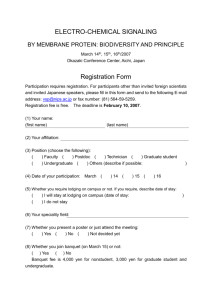
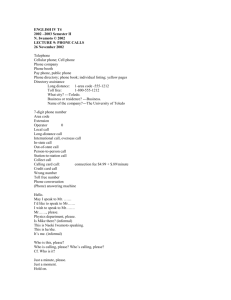
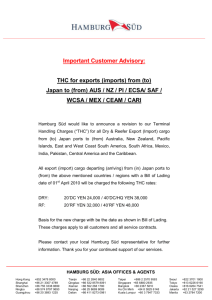
Nicolas Christin, CMU INI/CyLab Sally S. Yanagihara, CMU INI/CyLab Japan Keisuke Kamataki, CMU CS/LTI Pervasive online fraud found in Japan since 2004 “as seen on TV!” Victim clicks on a (innocuous) HTML link email, website, or SMS variants … only to be told they entered a binding contract… … and are required to pay a nominal fee or “legal actions” would be taken Japanese cousin of scareware scams One Click Contracts/Frauds, Wikipedia http://ja.wikipedia.org/wiki/ワンクリック詐欺 Fear of embarrassment, divorce, public shame, loss of job… Show IP address and a notice that “contact information has been recorded” Show victim sample of the billing statement that will be sent to the home (postcard with pornographic picture) One Click Frauds, http://support.zaq.ne.jp/security/oneclick5.html Quite large monetary impact Roughly 2.6 billion yen (~30 million US dollars) annually since 2004* Victim’s private information and payment are shared within the underground community and exposes victims to more frauds** Actual market size, damages, and number of victims are unknown due to embarrassment factor Only 2,859 cases (657 arrests) are solved on average each year Persistent plague over the 4 years we looked at (20062009) *Japan Police Force Annual Report 2004-2009 **http://journal.mycom.co.jp/articles/2009/04/24/adultsite1/index.html What makes One Click Fraud easy to perpetrate? What vulnerabilities do we have in our infrastructure? How are criminals exploiting those vulnerabilities? Who is committing these crimes? “Random crooks”, or… … is there evidence of any organized criminal activity? ▪ Do they operate in groups? ▪ Can they be linked to other forms of online crime? How should we address this problem? ▪ Technological vs. economical vs. legal remedies Source of data: “vigilante” websites posting information about frauds 2 Channel (2ちゃんねる 掲示板) http://society6.2ch.net/test/read.cgi/police/1215642976 Japan’s largest BBS We focus on the ‘One Click Fraud’ posts Potential difficulty: posts made using natural language, lots of noise, potentially hard to parse automatically Koguma-neko Teikoku (こぐまねこ帝国) http://kogumaneko.tk/ Consumer-oriented website (helpdesks, information, …) Structured reports, parsing easy Wan-Cli Zukan (ワンクリ図鑑) http://1zukan.269g.net/ Vigilante blog dedicated to exposing One Click Frauds Structured reports, parsing easy Collected 2,140 incident reports, dated March 6,2006-October 26, 2009 No evidence of slander Strip reports of following attributes and store into mysql database URL Bank account ID Bank account name* Bank branch name Bank name Phone number DNS information Genuine attributes* ▪ Registrar info ▪ DNS-reverse DNS lookup “Required” fee Many incomplete/ambiguous records, frequent overlap between different incidents *Bank Account owner’s name can be falsified but account is genuine (not false) [2ch Example] 1. Look for patterns across frauds in: Bank accounts used Phone numbers used DNS information (registrars, name servers) 2. Draw correlations to link several frauds to same perpetrators Common bank Bank accounts used account! Website 1 Phone numbers used Website 2 DNS information (registrars, name servers) Fraudsters’ phone numbers Syndicate's Telephone Share Hyogo Pref. 0.4% Docomo 10.3% Osaka Pref. 0.4% Free Dial 10.5% Japan Cellphone Market Share 2009 eMobile 1.5% Gunma Pref. 0.2% au 38.6% Willcom 4.0% Softbank 18.5% NTT Docomo 48.5% Tokyo Pref. 16.5% Softbank 23.3% au 27.4% Can identify phone numbers in 516 distinct incidents “au (by KDDI)” may have lax restrictions for new contracts Tokyo ’03-***’ numbers may be numbers using transfer services Syndicate's Bank Count 10) Bank accounts used (Top in frauds Tokyo Tomin Bank 8% Tokyo Star Bank 6% Mizuho Bank 16% Chuou Mitsui Sumitomo Trust & Trust & Banking Co. 2% JapanNet eBank 4% Bank 4% Banking Co. 3% Seven Bank 17% Risona Bank 6% Mitsubishi Tokyo UFJ Bank 12% Japan Bank Market 2009 (Top 8) Shinsei Bank 13% Mitsui Sumitomo Bank 14% Shinsei Bank 2% Aozora Bank Mitsui 1% (Tokyo) UFJ Financial Group 25% Risona Holdings Inc. 5% Japan Post Bank Co. Sumitomo 26% Mitsui Financial Group 16% Mizuho Financial Group 20% Can identify banks in 803 distinct incidents No “smoking gun” here Internet banks make it easier to create bank accounts since there is no physical interaction More prone to abuse Global Top 10 Registrar Registrar Top 10 registrars Syndicate's Fraudulent websites’ NEW DREAM ALLEARTHDOMAI NETWORK, LLC NS ABDOMAINATION 2% 1% S 1% KEY-SYSTEMS GMBH TUCOWS INC. 3% 4% KEY-SYSTEMS 2% PUBLIC DOMAIN REGISTRY 3% REGISTER.COM 3% DOTSTER 1% MONIKER 1% XINNET.COM 2% DOTSTER 1% ONLINENIC 1% FABULOUS.COM 1% MONIKER 3% GODADDY.COM, INC. 5% WILD WEST DOMAINS 4% ABOVE, INC. 6% GO DADDY 40% MELBOURNE IT 6% ENOM, INC. 56% GMO INTERNET, INC. 20% SCHLUND+PARTN ER 6% NETWORK SOLUTIONS 8% TUCOWS 9% Can identify registrar in 389 distinct incidents Evidence of a bias Is this due to lack of enforcement? Questionable subcontracting? (Resellers) ENOM INC. 11% Fraudsters’ choice of DNS Reseller can be defined by grouping Name Servers Identified in 97 incidents Very often also offer web hosting services Maido3.com is reseller of TuCows Inc Value-Domain.com is reseller of Enom Inc DreamHost.com is reseller/branch of New Dream Network LLC Number of websites hosted 1. Look for patterns across frauds in: Bank Accounts Cellphones, Telephones “au (KDDI)” brand cellphones may have lax contracting restrictions Tokyo “03-**” number probably due to phone number transfer services Phone Numbers DNS Registrars and Resellers Bank accounts No “smoking gun” Internet banks are seemingly easier to abuse DNS Registrars and Resellers Biased to specific DNS vendors DNS vendor resellers can be found by registered Name Server URL AccountID Phone number A family of scams actually contain some malware (in the form of downloadable “video”) Trojan in .exe format Collects email addresses in Outlook Express and Becky! Sends information back to “hachimitsu-lemon.com” server ▪ Has been taken down for a while Information used to blackmail to victims notifying them they “owe” registration fees Recently seen on Oct 26th, 2009 “Relatively” harmless Hypothesis: same criminal organization? Correlated by identical “Technical Contact Phone Number” in WHOIS information(+816-6241-6585) Basic clustering + WHOIS Seems to follow Zipf’s law (high concentration, long tail) 8 groups Identified (at most) 105 organized criminal groups On average, each group maintains 3.7 websites 5.2 bank accounts 1.3 phone numbers A few “syndicates” seem responsible for most of the frauds 50% of all scams Checked multiple DNS blacklists for a subset of our results 842 domain tested 275 unique IP addresses cbl.abusat.org Open proxies, spamware 2.55% dnsbl.sorbs.net Spam 8% zen.spamhaus.org L2.apews.org bl.spamcop.net Combined DB 8.36% No significant evidence of spamming, except for Spam or spam-friendly 32.73% “parked” domains seems to substantiate the Spam “lenient reseller” hypothesis 1.45% aspews.ext.sorbs.net Spam 4% ix.dnsbl.manitu.net Spam 1.45% Google Safe Browsing (URLs) Phish, Malware 0% Google Safe Browsing (IPs) Phish, Malware 16% Hardware/connection EeePC (900X): 28,000yen Yahoo!BB (ADSL 8M): 3,904 yen/month Rental Servers Maido3.com (Starter Pack) ▪ Domain Registration fee : FREE ▪ Server Setup fee: 3,675 yen ▪ Payment/month 7,350 yen/month Running website for a year ≤ 166,873 yen Illegally purchased (includes legal stamp): 30,000-50,000 yen Mail order banks, internet banks are easier to create due to lack of physical interaction Forged bank account names can be easily made since phonetic reading only is required when wiring money Fraudulent bank account for a year ≤ 50,000 yen 白井市蜜粉 “Shirai City Mitsuko” Submitted at application as name for ‘PTA Baking Club of Shirai City’ Forged signed paper is sufficient シライシミツコ カタカナ(Katakana) of the account name is shown as only “Shi-Ra-I-Shi-Mi-Tsu-Ko” (白石光子) “Shi-Ra-I-Shi-Mi-TsuKo” can be easily misconceived as a woman’s name, “Shiraishi Mitsuko” Cellphones can be illegally purchased: approx 35,000 yen Non traceable if payment (7,685yen/month) is done at convenience stores or prepaid instead of bank drafts Telephones such as popular ”Tokyo 03” can be easily transferred to other numbers to evade traceability: 840 yen/month e.g. Symphonet Services Co. Untraceable phone for a year ≤ 137,300 yen Registration fees are primarily between 45,000 and 50,000 yen (USD $500) Matches average Japanese businessmen monthly allowance* (45,600 yen)! amount Syndicate's Fraud Registration Fee (Top 10) (top 10 most common) 283 300 Website Count 250 200 142 150 109 119 98 92 100 50 54 46 66 47 *In Japan, usually the wife does the household accounting and provides the husband with an allowance to cover food, etc 5, 00 0 35 ,0 00 40 ,0 00 45 ,0 00 50 ,0 00 55 ,0 00 60 ,0 00 80 ,0 00 90 ,0 0 10 0 0, 00 0 0 Amount of Money (Yen) Assuming, on average, 3.7 websites, 5.2 bank accounts, and 1.3 phone lines (based on our analysis), an average fraudster breaks even as soon as approx. 4 users/site operated (about 16 people total) fall for the fraud within a year … obviously some people make a lot more money Analysis from police reports People who got caught, the really reckless guys Income: 9,094,089 yen / case / year **2.6bil yen / 2,859cases = 9,094,089 yen/case 4.4 frauds/organization on average **2,859 cases / 657 persons = 4.351 cases/ person Very close to our findings (3.6 websites operated by each organization/person on average) Organization’s income: 39,397,475 yen (9,094,089 * 4.4) – 616,517 = 39,397,475 yen (about $400K!) Important caveat: includes One Click Fraud and related confidence scams (e.g., Ore Ore). Very strong assumption (hinted by police): all scams are roughly in the same ballpark DATE PREFECTURE CRIMINAL ORGANIZATION MONETARY DAMAGES (total, Yen) VICTIMS (total) References 2004/22005/04/13 Osaka Nakanishi 5 other 600 Million 10,000+ http://blog.hitachinet.jp/archives/18867382. html 2004/82005/11/08 Iwate Mori 4 other 28 Million 450+ http://www.yomiuri.co.jp/n et/news/20051108nt03.ht m 2005/82007/03/04 Saitama Matsushita 50 Million 700+ http://blog.kogumaneko.tk/ log/eid591.html 2006/72007/11/28 Chiba Ochiai 6 other 300 Million 3,400+ http://www.yomiuri.co.jp/n et/security/snews/20071128nt0c.htm 2007/72008/8/16 Yamaguchi Nagaoka 5 other (2 Groups) 240 Million 3500+ http://blog.kogumaneko.tk/ log/eid1005.html Police arrest reports disclosed to media show criminals can earn extremely large amounts of money in roughly 1-2 years Hard to prosecute Victim must make complaint but rarely do so (embarrassment factor) Hard to show a crime: “Glorified panhandling” Low penalty Fraudsters can be sentenced up to 10 years but generally less than 5 years Relatively hard to identify Cases Arrest Sentence Fine (yen) Osaka 4/2005 2.5 yrs 2,000,000 Kyoto 7/2005 2.5 yrs 300,000 Nara 7/2005 2 yrs 1,000,000 Lawyer Sakurai 1/2006 0 yrs 300,000 DNS servers are overseas, difficult to obtain actual registrant information Telephone numbers use transferring service Barring possession of an arrest warrant, police cannot obtain contact and network information What makes One Click Fraud appealing? Miscreants can readily exploit infrastructure vulnerabilities ▪ Lax cellphone registration practices ▪ Forwarding services ▪ Registrars turning a blind eye Economically beneficial since low investment and high income Legal penalties are extremely low and not effective to curb crimes Who is committing these crimes? A few miscreants seem to control a majority of the fraudulent sites Relatively low technological sophistication, although usage of(relatively simple) malware observed Not much evidence of connections to other types of frauds, but deserves to be more fully investigated One Click Fraud must be primarily addressed by non-technological means Economic balance tipping far too much in favor of fraudsters Policy DNS Blacklist or pressure DNS resellers (ICANN) Strengthen control over exploitable banks, cellphone contracts, etc Law Increase legal actions for traceability of phone numbers Impose higher legal penalties? ▪ Prison, but more importantly fines will increase expected attacker costs Technology Increase IT literacy to avoid people panicking when faced with such threats Decrease the pool of potential victims Similarities with scareware? Nicolas Christin, Sally S. Yanagihara, and Keisuke Kamataki “Dissecting One Click Frauds” CyLab Technical Report CMU-CyLab-10-011. http://www.andrew.cmu.edu/user/nicolasc/papers.html Email: nicolasc@cmu.edu Amount of Money vs Time •Registration fees concentrate at 50,000 yen •Time and Japanese economic conditions do not seem to affect price Amount of Money 200,000 150,000 100,000 50,000 0 2006/1/1 2006/7/20 2007/2/5 2007/8/24 2008/3/11 Time 2008/9/27 2009/4/15 2009/11/1 .hta format tool that persistently show “Please Pay Registration Fee” window Persistently show window even if ‘x’ is clicked and when PC is rebooted Does not collect data Cause of sudden increase of calls to police and IPA Help Desk in May, 2009 First seen on April 7th, 2009 Recently seen on Oct 12th, 2009 Many anti-virus applications prevent .hta module downloads from July, 2009 Groups could not be distinguished by collected attributes Other analysis such as .hta module code comparison are required