FZDH approaches to the data hiding problem from a different
advertisement
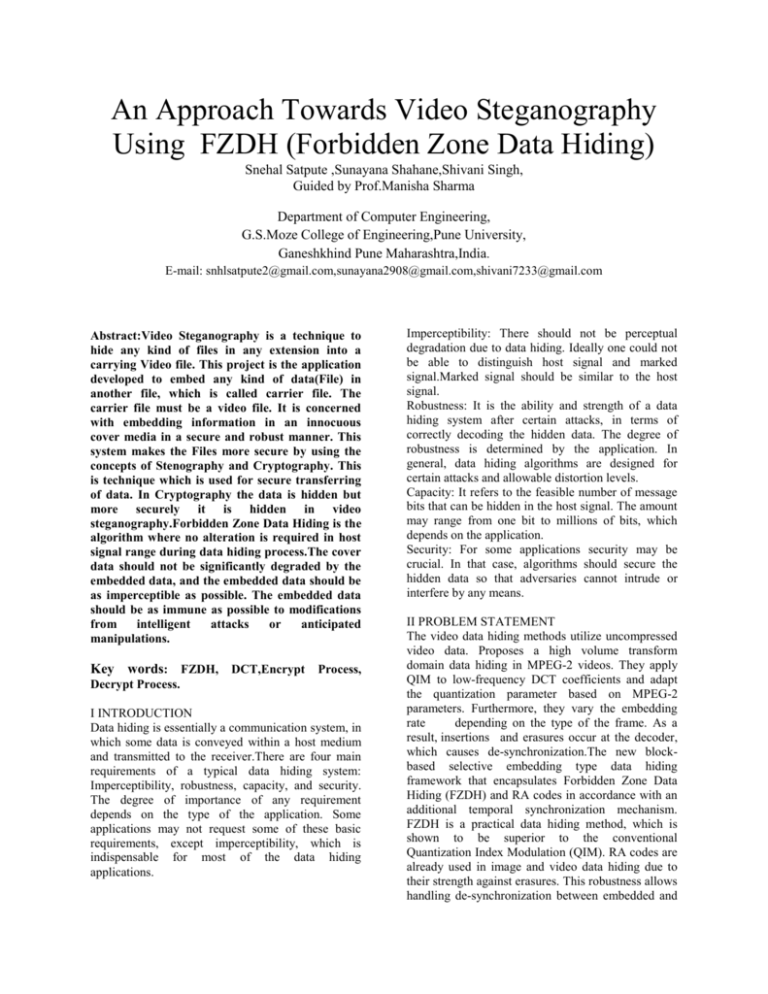
An Approach Towards Video Steganography Using FZDH (Forbidden Zone Data Hiding) Snehal Satpute ,Sunayana Shahane,Shivani Singh, Guided by Prof.Manisha Sharma Department of Computer Engineering, G.S.Moze College of Engineering,Pune University, Ganeshkhind Pune Maharashtra,India. E-mail: snhlsatpute2@gmail.com,sunayana2908@gmail.com,shivani7233@gmail.com Abstract:Video Steganography is a technique to hide any kind of files in any extension into a carrying Video file. This project is the application developed to embed any kind of data(File) in another file, which is called carrier file. The carrier file must be a video file. It is concerned with embedding information in an innocuous cover media in a secure and robust manner. This system makes the Files more secure by using the concepts of Stenography and Cryptography. This is technique which is used for secure transferring of data. In Cryptography the data is hidden but more securely it is hidden in video steganography.Forbidden Zone Data Hiding is the algorithm where no alteration is required in host signal range during data hiding process.The cover data should not be significantly degraded by the embedded data, and the embedded data should be as imperceptible as possible. The embedded data should be as immune as possible to modifications from intelligent attacks or anticipated manipulations. Key words: FZDH, DCT,Encrypt Process, Decrypt Process. I INTRODUCTION Data hiding is essentially a communication system, in which some data is conveyed within a host medium and transmitted to the receiver.There are four main requirements of a typical data hiding system: Imperceptibility, robustness, capacity, and security. The degree of importance of any requirement depends on the type of the application. Some applications may not request some of these basic requirements, except imperceptibility, which is indispensable for most of the data hiding applications. Imperceptibility: There should not be perceptual degradation due to data hiding. Ideally one could not be able to distinguish host signal and marked signal.Marked signal should be similar to the host signal. Robustness: It is the ability and strength of a data hiding system after certain attacks, in terms of correctly decoding the hidden data. The degree of robustness is determined by the application. In general, data hiding algorithms are designed for certain attacks and allowable distortion levels. Capacity: It refers to the feasible number of message bits that can be hidden in the host signal. The amount may range from one bit to millions of bits, which depends on the application. Security: For some applications security may be crucial. In that case, algorithms should secure the hidden data so that adversaries cannot intrude or interfere by any means. II PROBLEM STATEMENT The video data hiding methods utilize uncompressed video data. Proposes a high volume transform domain data hiding in MPEG-2 videos. They apply QIM to low-frequency DCT coefficients and adapt the quantization parameter based on MPEG-2 parameters. Furthermore, they vary the embedding rate depending on the type of the frame. As a result, insertions and erasures occur at the decoder, which causes de-synchronization.The new blockbased selective embedding type data hiding framework that encapsulates Forbidden Zone Data Hiding (FZDH) and RA codes in accordance with an additional temporal synchronization mechanism. FZDH is a practical data hiding method, which is shown to be superior to the conventional Quantization Index Modulation (QIM). RA codes are already used in image and video data hiding due to their strength against erasures. This robustness allows handling de-synchronization between embedded and decoder that occurs as a result of the differences in the selected coefficients. III DATA HIDING: With respect to host signal domain, data hiding in video sequences is performed in two major ways: bitstream level and data level. In bitstream level, the redundancies within the current compression standards are exploited. Typically, encoders have various options during encoding and this freedom of selection is suitable for manipulation with the aim of data hiding. However, these methods highly rely on the structure of the bitstream; hence they are quite fragile; in the sense that in many cases, they cannot survive any format conversion or transcoding even without any significant loss of perceptual quality. As a result, this type of data hiding methods is generally proposed for fragile applications, such as authentication. On the other hand, data level methods are more robust to attacks. Therefore, they are suitable for a broader range of applications. On the other hand, data level methods are more robust to attacks. Therefore, they are suitable for a broader range of applications.Despite their fragility, the bitstream based methods are still attractive for data hiding applications. However, most of the video data hiding methods utilize uncompressed video data. A system proposes a high volume transform domain data hiding in MPEG-2 videos. They apply QIM to low-frequency DCT coefficients and adapt the quantization parameter based on MPEG-2 parameters. Furthermore, they vary the embedding rate depending on the type of the frame. As a result, insertions and erasures occur at the decoder, which causes de-synchronization.They utilize Repeat Accumulate (RA) codes in order to withstand erasures. Since they adapt the parameters according to type of frame, each frame is processed separately. RA codes are already applied in image data hiding. In adaptive block selection results in de-synchronization and they utilize RA codes to handle erasures. Insertions and erasures can be also handled by convolutional codes.Multiple parallel decoders are used to correct de-synchronization errors. However, it is observed that such a scheme is successful when the number of the selected host signal samples is much less than the total number of host signal samples.A 3-D DWT domain is used to hide data. They use lowest subband coefficients and do not perform any adaptive selection. Therefore, they do not use error correction codes robust to erasures. Instead, they use BCH code to increase error correction capability. One perform 3-D interleaving in order to get rid of local burst of errors. Additionally, they propose a temporal synchronization technique to cope with temporal attacks, such as frame drop, insert and repeat. Image and video data hiding share many common points; however, video data hiding necessitates more complex designs. IV STEGANOGRAPHY [A] Historical View: Steganography is basically stega + nography. ‘Stega’ means ‘covered’ coming from the Greek word“stegos” and ‘nography’ means ‘writing’ coming from the Greek word “graphia”. Thus, Steganographymeans covered writing. Steganography is an ancient art of conveying messages in a secret way such thatonly the receiver knows the presence of the message. The most common use of steganography is to hide a file inside another file.The message is hidden in another media such that thetransmitted media appears meaningful to the attacker. If the hidden message is extracted the steganography technique fails. Steganographic technique allows one party to communicate with another party withoutthird party being aware that communication is occurring. Steganography is the method of encodingsecret data such that the existence of the information is concealed. Usually, the data is concealed inside an innocuous cover such that even if hostile agents discover the cover, there is no suspicions about thepresence of data in that cover. Steganography and Cryptography are cousins in the spy craft family .However, Cryptographic & Steganographic technique differs from each other. In cryptography, the originalmessage is scrambled i.e. its original structure is changed in order to make it meaningless. Thus, whenan attacker discovers the message it is still difficult for him to get the original message back. Cryptographydoes not try to hide the message. In steganography, the message is secretly hidden inside an image oraudio/video file. Thus there arises no suspicion to the attacker. Steganography does not attempt to scramblethe original message. The intention of both steganography & cryptography is to protect the originalmessage from the attacker. Both are excellent means, but when used alone can be broken. As a result,several experts have suggested the idea of using both the techniques in order to provide additional layer ofsecurity. Cryptographic technique encrypts the original message. This encrypted message is then hiddenusing steganographic technique. Now, even if attacker defeats the steganographic technique, he stillrequires cryptographic decoding key to decipher the encrypted message. [B] Modules Required 1. Encryption Module In Encryption module, it consists of Key file part, where key file can be specified with the password as aspecial security in it. Then the user can type the data or else can upload the data also though the browsebutton, when it is clicked the open file dialog box is opened and where the user can select the secret message. Then the user can select the image or video file through another open file dialog box which isopened when the cover file button is clicked. Where the user can select the cover file and then the Hidebutton is clicked so that the secret data or message is hidden in cover file using Forbidden Zone Datahiding technique. Start 2. Decryption Module This module is the opposite as such as Encryption module where the Key file should be also specified same as that of encryption part. Then the user should select the encrypted cover file and then shouldselect the extract button so that the hidden message is displayed in the text area specified in theapplication or else it is extracted to the place where the user specifies it. 3. Data Extraction: This module describes about the data extraction, it extracts the data from the secret image and results in original data. It takes the secret image as input and results in original message by giving the secret key. This module process is backward process of above modules. The data extraction process is discussed as follows. Select file as input Secret image Select cover file Secret key Fig 2: Data extraction process V ENCRYPTION FRAMEWORK Select destination path Enter password Encrypt data embedded video Select embedded video file Decrypt data embedded video Stop Fig1: Encryption and decryption process Original data AND DECRYPTION In the embedding step, host signal is mapped to a marked signal depending on the data to be hidden. System parameters denote the required parameters specific to the utilized data hiding method. The same parameters should also be available to the decoder. The optional cryptographic key is required for security applications. The channel refers to the modifications made on the marked signal before the receiver.The decoder operates on the received signal and extracts the hidden data. The existence of the host signal at the decoder is optional. Host Signal: The medium into which the data will be hidden. It can be any suitable type such as image, audio, video, or even text. The main requirement on the host signal is that it should have some sort of redundancy that can be used to hide data imperceptibly. Message: The data to be hidden Marked Signal: The medium which conveys the hidden data. Its type is identical to the host signal. Embedding Function: The function that maps the host signal to marked signal according to the message. Embedding Distortion: The distortion introduced to the host signal as a result of the embedding operation. System Parameters: Method specific parameters required for embedding and decoding. Received Signal: The signal received by the decoder, in other words attacked marked signal. Decoding Function: The function that decodes the hidden data from the received signal. to compare the framework with watermarking and the video data hiding method in. The figures 3 and 4show the host frame and marked frame respectively VI FORBIDDEN ZONE DATA HINDING Forbidden Zone (FZ) is defined as the host signal range, where alteration is not allowed during data hiding process. Forbidden Zone Data Hiding (FZDH) simply makes use of FZ to adjust the robustnessinvisibility trade-off. The definition of FZ concept may lead to an impression of similarity between FZ and masking, whereas they correspond to totally different concepts. Masking is applied to data hiding and watermarking in a number of efforts, as in order to incorporate perceptual analysis, so that perceptually usable host signal samples and permissible distortion margins are determined. However, FZ does not involve any perceptual analysis and adaptive coefficient selection process. The main motivation of FZ is decreasing the embedding distortion at a certain decoding error level. Similar to QIM, FZ should be applied, when the embedding distortion is within perceptually feasible margins. This requirement is generally satisfied as a result of the host signal power constraint, which states that the host signal power is significantly greater than embedding distortion. The general and simple parametric forms of FZDH are given in the following subsections. FZDH involves a set partitioning to determine the range of host signal where alteration is allowed. FZDH employs a mapping in the AZ, for which quantizers are not the only choice.In FZDH, initially all regions are forbidden and one decreases these zones according to the desired level of decoding error with respect to a channel noise level.FZDH keeps some of the host signal unaltered. FZDH approaches to the data hiding problem from a different perspective than coding techniques: there exists uncoded portions of the host signal range. The main motivation is to keep the host signal unaltered for some ranges, which should be determined according to the desired level of robustness, embedding distortion amount and channel noise level. VII EXPERIMENT Experiments are performed in three stages. In the first stage QIM and FZDH are compared. In the second stage observes video processing attacks and the system’s stability in handling them. The third stage is Fig 3:Host frame before steganography Fig 4:Marked frame after steganography Comparing above images it doesn’t see that change in image after video stenography. The superiority of image occurs hence third party will not able to understand message is hidden behind image. VIII CONCLUSION Encryption software protects internet connected computers from crackers and other online intruders.The technology is widely used to encrypt credit card information, bank account numbers and other type of financial records so they can send safely and securely across the internet.Protect much of the intellectual content that’s marketed on the web, such as music, Videos, articles, and software, restricting its availability to paying customers.This system helps to hide the information while sending the important and confidential documents in video files; it will be invisible for the third person.This system is helpful for the defense and security departments sending and receiving theconfidential matters in emergency situations. A new technique is proposed here for data hiding which is based on the adaptive video data hiding method that makes use of FZDH. It is superior to both QIMand also DC-QIM and RA codes. Selective embedding as described in is used in this work. The new technique of Video data hiding is propose.It is having superiority in video. Video data hiding framework that makes use of erasure correction capability of RA codes and superiority of FZDH. We observed that FZDH is superior to QIM, especially for low embedding distortion levels.Typical system parameters are reported for error-free decoding. The results indicate that the framework can be successfully utilized in video data hiding applications. IX REFERENCES [1]F.A.P.Petitcolas,R.J.Anderson,M.G.Kuhn, “Information Hiding-A Survey”, Proceeding of the IEEE, vol. 87, no. 7, June 1999, pp.1062-1078. [2] J. J. Chae, B. S. Manjunath, “Data Hiding in Video”,Proceedings of the 6th IEEE International Conference on Image Processing, 1999, pp.311-315 [3] M. Wu, H. Yu, and B. Liu, “Data hiding in image and video: II. Designs and applications,” IEEE Trans. Image Process, vol. 12, no. 6, pp. 696–705, Jun. 2003. [4]B. Chen and G. W. Wornell, “Quantization index modulation: a class of provably good methods for digital watermarking and information embedding,” IEEE Transactions on Information Theory, vol. 47, May 2001, pp. 1423-1443, May 2001. [5] B. Chen and G. W. Wornell, “Quantization index modulation: A class of provably good methods for digital watermarking and information embedding,” IEEETrans. Inform. Theory, vol. 47, no. 4, pp. 1423– 1443, May 2001. Trans. Circuits Syst. VideoTechnol., vol. 19, no. 10, pp. 1499–1512, Oct. 2009.