IKE details
advertisement

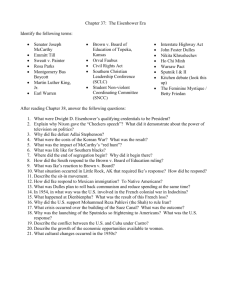
Header and Payload Formats The IKE Header • Each IKE message begins with the IKE header IKE-SA Initiator’s SPI IKE-SA Responder’s SPI Next MjVer MnVer Payload Exchange Type Message ID Length Flags The IKE Header • The message begins with the IKE header followed by one or more IKE payloads • Payloads are processed in the order they appear in the IKE message The IKE Header Fields • Initiator’s SPI¹ (8 octets) – chosen by the Initiator to identify a unique IKE SA. must not be zero • Responder’s SPI (8 octets) – chosen by the responder to identify a unique IKE SA. must be zero in the first message of the Initial Exchange and must not be zero in any other message 1. SPI – Security Parameter Index The IKE Header Fields • Next Payload (1 octet) – indicates the type of payload that immediately follows the header • Major Version (4 bits) – indicates the major version of the IKE protocol in use. Implementations based on version 2 must reject (or ignore) messages containing a version number greater than 2. The IKE Header Fields • Minor Version (4 octets) – indicates the minor version of the IKE protocol in use. • Exchange Type (1 octets) – indicates the type of exchange being used. This dictates the payloads sent in each message and message orderings in the exchanges The IKE Header Fields • Flags (1 octet) – R(eserved) (bits 0-2) – I(nitiator) (bit 3) – set when the message is from the Original Initiator of the IKE-SA, and cleared otherwise. Used by the recipient to determine whether the message is a request or a response. – V(ersion) (bit 4) – indicates that the transmitter is capable of speaking a higher major version number than the one indicated in the major version number field – R(eserved) (bits 5-7) The IKE Header Fields • Message Id (4 octets) – used to control retransmission of lost packets and matching requests and responses • Length (4 octets) – length of the total message (header + payloads) in octets. Generic Payload header Next Payload C RESERVED Payload Length • Each IKE payload (that will be discussed later) begins with a generic header • The construction and processing of the generic payload header is identical for each payload Generic Payload header Fields • Next payload (1 octet) – indicates the type of the next payload in the message In the last payload in the message the field is zero • Critical (1 bit) – indicates if the sender wants the receiver to skip (set to 0) or to reject (set to 1) this payload if he doesn’t understand the payload type code. If the recipient understands the code he should ignore this field Generic Payload header Fields • RESERVED (7 bits) • Payload Length (2 octets) – length in octets of the current payload, including the generic payload header SA (Security Association) Payload • Used to negotiate attributes of a security association • May contain multiple proposals • Each proposal includes a Suite-ID which implies one or more protocols and the associated cryptographic algorithms Proposal Structure • Contains a Proposal # , a Suite-ID and the sending entity SPI(s) • When the SA is accepted, the SA payload send back must contain a single proposal and its number must match the number in the accepted proposal KE (Key Exchange) Payload • Used to exchange Diffie-Hellman public numbers as part of a DH key exchange • The length of the DH public value must be equal to the length of the prime modulus over which the exponentiation was performed (prepending zero bits if necessary) KE (Key Exchange) Payload • Alice sends her DH value in the IKE_SA_INIT, so she must guess the DH group that Bob will select from her list • If she guesses wrong, Bob will reply with a Notify payload indicating the selected suite ID (Identification) payload • Allows peers to assert an identity to one another • Names the identity to be authenticated with the AUTH payload • Assigned values for the ID Type field contain: ID_IPV4_ADDR, ID_IPV6_ADDR, ID_FQDN (a fully-qualified domain name string), ID_KEY_ID (may be used to pass vendor-specific information) and more CERT (Certificate) Payload • Provides a means to transport certificates or other certificate-related information via IKE • CERT payloads should be included in an exchange if certificates are available to the sender • Certificate Encoding field indicates the type of certificate contained in the Certificate Data field. CERTREQ (Certificate Request) Payload • Provides a means to request preferred certificates via IKE • Can appear in the first, second, or third message of Phase 1 • CERTREQ payloads should be included in an exchange whenever the peer may have multiple certificates, some of which might be trusted while others not CERTREQ Payload Processing Certificate Encoding has Certificate Authority has send it doesn’t have doesn’t have no processing Not an error condition of the protocol AUTH (Authentication) Payload • Contains data used for authentication purposes • Auth Method field specifies the method of authentication used: Digital Signature (1) or Shared Key Message Integrity Code (2) • Authentication Data field contains the results from applying the method to the IKE state • If the specified authentication method is not supported or validation fails an error must be sent and the connection closed Nonce Payload • Ni – Initiator’s nonce • Nr – Responder’s nonce • Contains random data used: – In IKE_SA_INIT as inputs to cryptographic functions – In CREATE_CHILD_SA to add freshness to the key derivation technique used to obtain keys for CHILDSAs • Nonce values must not be reused N (Notify) Payload • Used to transmit informational data: error conditions and state transitions • May appear in a response message (usually specifying why a request was rejected), or in an Informational Exchange N (Notify) Payload Fields • Protocol-Id (1 octet) – specifies the protocol about which this notification is being sent. For phase 2 will contain an IPsec protocol (AH or ESP), in other cases must be zero • SPI Size (1 octet) • Notify message type (2 octets) – the type of the notification message (next slide) • SPI (variable length) • Notification Data (variable length) – informational or error data transmitted in addition to the Notify Message Type Notify Messages – Error Types • UNSUPPORTED-CRITICAL-PAYLOAD sent if the payload has the “critical” bit set and the payload type is not recognized • INVALID-SPI indicates an IKE message was received with an unrecognized destination SPI (usually indicates that the recipient has rebooted and forgotten the existence of an IKE-SA) Notify Messages – Error Types • INVALID-SYNTAX Indicates that the message was invalid (type, length, or value out of range or the request was rejected for policy reasons) To avoid DOS attack using forged messages, this status may only be returned for and in a (valid) encrypted packet • INVALID-MESSAGE-ID sent when received a MESSAGE-ID outside the supported window Notify Messages – Error Types • NO-PROPOSAL-CHOSEN none of the proposed crypto suites was acceptable • AUTHENTICATION-FAILED sent in response to an IKE_AUTH message when the authentication failed • NO-ADDITIONAL-SAS indicates that Phase 2 SA request is unacceptable because the Responder is unwilling to accept any more CHILD-SAs on this IKE-SA. Notify Messages – Status Types • INITIAL-CONTACT asserts that this IKE-SA is the only IKE-SA currently active between the authenticated identities • SET-WINDOW-SIZE sends the size of the window D (Delete) Payload • ESP and AH SAs always exist in pairs • To delete an SA, an Informational Exchange with one or more Delete Payloads is sent, listing the SPIs of the SAs to be deleted • May be deletion of IKE-SA or of a CHILD-SA Vendor ID Payload • Contains a vendor defined constant • the constant is used by vendors to identify and recognize remote instances of their implementations • allows a vendor to experiment with new features, while maintaining backwards compatibility TS (Traffic Selector) Payload • Allows endpoints to communicate some of the information from their SPD to their peers • 2 TS payloads appear in each of the messages in the exchange that creates the CHILD-SA pair • Each traffic selector consists of an address range, a port range and a protocol ID Encrypted Payload • Contains other payloads in encrypted form • Must be the last payload in message often it is the only payload in a message CP (Configuration Payload) • Used to exchange configuration information between IKE peers Some more … Rekeying • SAs should be used for a limited time and protect limited amount of data • Rekeying means reestablishment of SAs to take place of ones which expire • Done to IKE-SA and CHILD-SA • An IKE-SA created inherits all of the original IKESA’s CHILD-SAs • The new SA should be established before the old one expires and becomes unusable Error Handling • Errors that occur before a cryptographically protected IKE-SA is established must be handled very carefully because it can be a part of a DOS attack based on forged messages • The frequency of liveliness tests for IKE-SA should be limited to avoid being tricked into participating in a Denial Of Service attack