Watermarking and Steganography
advertisement

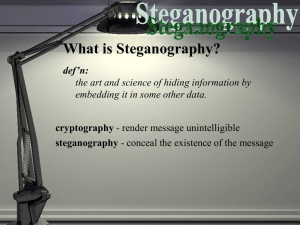
Watermarking and Steganography Watermarks • First introduced in Bologna, Italy in 1282 • Dandy Roll presses pattern into drying paper – Changes thickness of paper fibers • Uses: – – – – By paper makers to identify their product Security for stamps, official documents. Stock certificates, money, etc. Chic • Other “watermarks” – Printing on plastic with a window. (Australian $10 note) Dandy Roll • Pressed into paper during paper-making process J. Plank Features •In-house watermark design •Computerized design process •Quick-change sleeves and sections •Dandy roll •7.25" diameter •Watermarking possible http://www.uwsp.edu/papersci/PM/Machine/Dandy.htm Dandy Roll • Wet pulp sprayed onto moving belt • Dandy Roll pressed into pulp • Dandy Roll looks like oversized printer’s roll covered with pattern •High grade stainless steel construction •Incorporates internal oscillating shower, internal pan, internal steam shower and external saveall pan •Extended Header Brush for easy cleaning of shower pipe Laser Printed “Watermarks” • Used on bond paper, but who uses bond paper? – Doesn’t work well in inkjets or laserjets • “Watermarks” with most print drivers… Printed Watermarks • Looks great • You can even put it in your PDF file…which is the problem! • No security Printed Document Authentication Techniques • Microprinting – Print that is too small to produce or copy with conventional equipment • Intaglio –engraved pattern used to press ink with great force; raised letters • Letterpress – Ink rolled raised type, leaving depression. Used for printing numbers. • Simultan press – precise registration of front and back. (see-through register). Changing ink colors (rainbowing). • Optically variable inks (change color depending on angle) • Metal foils & threads embedded in paper • Security holograms Lessons for paper authentication • Security features should convey a message relevant to the product. – Use iridescent ink to print the banknote denomination • Should obviously belong where they are – They become “embedded in the user’s cognitive model.” • Should be obvious • Should not have competitors • Should be standardized Source: Security Engineering, Anderson Information Hiding • Copyright Marks: – Watermarks - Hidden copyright messages – Fingerprints – Hidden serial numbers • Steganography – Hidden messages. • Other applications: – Closed captioning (hidden in first 21 scan lines) • http://www.robson.org/gary/writing/nv-line21.html – Audio RDS (Radio Data Service)-like service • “What’s that song?” Watermarks for Copyright Policy • “never copy” • “copy only once” • “copy only at low quality” JPMG Linnartz, “The ‘Ticket’ Concept for Copy Control Based on Embedded Signaling” (Anderson [504] ) Suggests a hash-based implementation of “copy only once:” – X is the ticket – Record h(h(X)) on DVD – Provided with X, DVD recorded stores h(X) on secondgeneration copy. The Broadcast Flag • “Advanced Television Systems Committee Flag” • Enable/Disable: – high-quality digital output – Re-transmitting on an “unprotected” channel • In the future: – Time-shifting? – Disallow fast-forward through commercials • Required on all digital TV cards sold after July 2005 • Only broadcast, not satellite or cable-transmitted. “Losing Control of Your TV,” Technology Review, March 3, 2004 http://www.technologyreview.com/articles/04/03/wo_garfinkel030304.asp?p=1 Steganography • A hidden message that can't be found by humans • A hidden message that can't be found by an algorithm. A hidden message that can be found by an algorithm but not by a human. • A hidden message that can be found by some algorithms but not others. [Wayner 2004] What is Hidden? Defining "Hidden" is not easy – We run into the usual Goedel limits that prevents us from being logical about detection. – Humans are very different. Some musicians have very, very good ears. – Some algorithms leave statistical anomalies. The message is often more random than the carrier signal. These statistics can give away the message. Who wants it? • Evil doers. If evil messages can't be seen by good people, evil will triumph. Osama bin Laden? • Good doers. If the good guys can communicate in secret, then good will triumph. U.S. forces • Content owners and copyright czars. Hidden messages can carry information about rights to view, copy, share, listen, understand, etc. • Software Developers. "Hidden" channels can be added to data structures without crashing previous versions. Steganography can fight bit rot. Models for Steganography • Replace random number generators with the message. – This works if the random numbers are used in a detectable way. – TCP/IP, for instance, uses a random number for connections. Some grab this for their own purposes. • Replace noise with the message. – Just replace the least-significant bit. – Avoid the noise and tweak the salient features. • Anything not affected by compression. – If you have the freedom to change data without hurting the data, then you have the freedom to include another message. Models for Steganography • Structured Models – Run some compression algorithm in reverse • If the compression models the data accurately, then running it in reverse should spit out something that models the data well. • Huffman algorithms give common letters short bit strings and rare ones long ones. – Change the structure or the order. • GifEncoder, for instance, changes the order of the colors in the palette. – Synthesize something new and use the data to guide the synthesis. • Is the ghoul shooting at you in the game using a revolver or a machine gun? That's one bit. Noise • The least significant bit of pixels or sound files is very popular. • Tweaking the LSB is only a small change. Less than 1%. – 140=10001100 – 141=10001101 • You can encrypt, too! LSB modified to hide info LSB Modification • Side Effects: – The data may not have the same statistical pattern as the least significant bits being replaced. • Add a lot of noise, and it’s obvious 4 LSB modified produces banding More LSB Modification 6 bits 7 bits 8 out of 8 bits All 8 bits Bit 8 vs. Bit 1 Wayner Demos • Information hiding at the bit level: – http://www.wayner.org/books/discrypt2/bitlevel .php • Encoding information through list order: – http://www.wayner.org/books/discrypt2/sorted. php#note2 JPEG Watermarking “Hide and Seek: An Introduction to Steganography” IEEE Security & Privacy Figure 2. Embedded information in a JPEG. (a) The unmodified original picture; (b) the picture with the first chapter of The Hunting of the Snark embedded in it. Mesh Watermarking • Robust mesh watermarking, Emil Praun, Hugues Hoppe, Adam Finkelstein, July 1999 Proceedings of the 26th annual conference on Computer graphics and interactive techniques Issues to evaluate • “Capability” – Payload carrying ability – Detectability – Robustness • Securing information: Capacity is the wrong paradigm, Ira S. Moskowitz, LiWu Chang, Richard E. Newman , September 2002 Proceedings of the 2002 workshop on New security paradigms SDMI – Secure Digital Media Initiative • SDMI (200+ companies) published an “Open Letter to the Digital Community” with an SDMI Challenge. – Earn up to $10,000 for breaking their “watermarks” – Challenge from September 15, 2000 – October 7, 2000 • SDMI Systems: – Designed to prevent “remixing” of privated CDs – Designed to survive MP3 compression SDMI & The Academics • The Academics: – Scott Craver, Patrick McGregor, Min Wu, Bede Liu, (Dept. of Electrical Engineering, Princeton University) – Adam Stubblefield, Ben Swartzlander, Dan S. Wallach (Dept. of Computer Science, Rice University) – Edward W. Felten (Dept. of Computer Science, Princeton University) • What they did: – Successfully removed the digital watermark from the challenge audio samples. • How did they know they did it? – SDMI provided an “Oracle” that told them they did! SDMI & Academics: Part 2 • Academics couldn’t claim cash prize – Doing so would have required signing a “confidentiality agreement” and prohibit the academics from sharing results with the public • DMCA didn’t apply… – … because SDMI specifically invited the work • Felton &c decided to present their findings at the 4th International Information Hiding Workshop April 25-29, 2001 • April 9, 2001 RIAA Senior VP for Business and Legal Affairs sent Felton letter with veiled DMCA threats • April 26, 2001 Felton declines to present paper • May 3, 2001 – RIAA and SDMI say they never intended to sue • June 6, 2001 – Felton files suit against RIAA asking for a declaratory judgment that they would not be infringing • November 28, 2001 – Case dismissed for mootness DigiMarc • Leading provider of watermarking technologies • Plug-ins for Windows, PhotoShop, etc. • Communicates: – Copyright ownership – Image ID – Image content – adult, etc. Tools and References • Fabien a. p. penticolas – http://www.petitcolas.net/fabien/steganography/ • Digimarc • http://theargon.com/archivess/steganograp hy/ • Hiding Secrets with Steganography, by Dru Lavigne, – http://www.onlamp.com/pub/a/bsd/2003/12/04 /FreeBSD_Basics.html • http://www.outguess.org “Mosaïc attack” • Defeat an embedded watermark by chopping up image and serving it in pieces <nobr> <img SRC="kings_chapel_wmk1.jpg’ BORDER="0’ ALT="1/6’ width="116’ height="140"> <img SRC="kings_chapel_wmk2.jpg’ BORDER="0’ ALT="2/6’ width="116’ height="140"> <img SRC="kings_chapel_wmk3.jpg’ BORDER="0’ ALT="3/6’ width="118’ height="140"> </nobr> <br> <nobr> <img SRC="kings_chapel_wmk4.jpg’ BORDER="0’ ALT="4/6’ width="116’ height="140"> <img SRC="kings_chapel_wmk5.jpg’ BORDER="0’ ALT="5/6’ width="116’ height="140"> <img SRC="kings_chapel_wmk6.jpg’ BORDER="0’ ALT="6/6’ width="118’ height="140"> </nobr> Mosaïc assembled • Some websites use mosaics to deter casual copying! MP3Stego • Hides information in MP3 files during the compression process • Takes advantage of the fact that MP3 provides high-quality compression of 11:1 – Plenty of room for information hiding! – Randomly chooses which parts of the Layer III inner loop to modify; makes sure modifications don’t exceed threshold defined by the psycho acoustic model. • “Weak but better than the MPEG copyright flag defined in the standard” • Defeat by decompressing & recompressing MP3Stego in action http://www.petitcolas.net/fabien/steganography/mp3stego/index.html Translucent Databases (More Wayner Work, if we have time…) Translucent Database • Instead of: – INSERT INO purchases values (“bob jones”, 55424, “36”, NOW()) • Use: – INSERT INTO purchases values (MD5(“bob jones”, 55424, “36”, NOW()) TD’s with Redundency • INSERT INTO salaries2 VALUES ( MD5(“Fred Smith/1313 Mockingbird Lane/06-011960/012-34-5678”), MD5(“Fred Smith/1313 Mockingbird Lane/012-34-5678”), MD5(“Fred Smith/1313 Mockingbird Lane/06-01-1960”), MD5(“Fred Smith//06-01-1960/012-34-5678”), 60000, 5 20 ) Coordinating Users nameHash1 nameHash2 Message d3b07384d113edec49ea a6238ad5ff00 2b00042f7481c7b056c4 b410d28f33cf You’ve got some explaining to do 2b00042f7481c7b056c4 b410d28f33cf D3b07384d113edec49ea a6238ad5ff00 It’s not my fault! Inserting into multi-user table • INSERT INTO bboard1 Values(MD5(“Lucy”),MD5(“Ricky”),”You’ve got some explaining to do.”) • INSERT INTO bboard1 Values(MD5(“Lucy”),MD5(“Ricky”),ENCRY PT(”You’ve got some explaining to do.”))