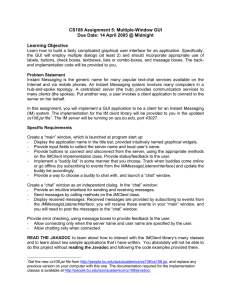
Instant Messenger Security with a focus on implementing security
advertisement

Instant Messenger Security with a focus on implementing security policies in corporate IM services Kaushal S Chandrashekar CS 691 Dr. Edward Chow UCCS Outline • Instant Messaging •Problems with IM in corporate environments • General threats to IM • Implementing security policies in IM • Design details and problems • Summary • References Instant Messaging •Instant Messaging (IM) is the online chat medium that allows people to connect and collaborate in real-time. • Based on IP protocols • 10 million enterprise users in 2002 • Expected to explode up to 180 million users by 2007 Problems with Free IM in corporate environments •Privacy concerns •Security Concerns •No central administration •No integration with corporate IT •Security and firewall problems •Dependence on external infrastructure providers General threats to IM •Worms • Bypasses most anti-virus scanners • Can resend itself to all on the buddy list •Backdoor Trojan Horses • Utilize IM app to send information about user • Can modify configuration settings to make whole HDD available for file sharing General threats to IM Contd •Hijacking and Impersonation • Account information can be stolen and misused • Man-in-the-middle attacks •Denial of Service • Flood attacks Implementing security policies in IM • Why? • Most enterprise IMs provide only primitive control • A more fine-grained approach required • Common breaches of security • Transfer of confidential files to unauthorized users • Unauthorized attendees in confidential conferences • Messages containing confidential information Required features in corporate IMs • Secure log-in • Chatting • Internal, application based • External, web based • Conferencing • File sharing Basic IM Service architecture Web based IM Web Server Central Messaging Server No external IP Protected against internal DOS attacks Authentication Access Control Certificate handling DMZ Client(s) Authentication Encryption Internal Network Security Clearance hierarchy Mgmt Level 1 Mgmt Level 2 . . Regular Employee . Customer Support . External Log-in • Essential because it determines security clearance • Password-locked certificates • Problems • Weak passwords • Vulnerable to software cracking and social engineering • Biometric keys • Integration of IM login with terminal login Chatting • Rules • External chat only with employees with Ls >= lk, a predetermined level • If Ls(S1) >= Ls(S2), S1 can chat unchecked with S2, but messages from S2 to S1 are monitored • All chat messages are encrypted using mutually negotiated session keys, except for ones with externals. Chatting contd. • Chat monitoring and logging • All chat activity is monitored and logged to log files that are accessible only to any non-sysadmin users • Suspect word list to raise alerts • Problems • Words split up, capitalized • Sentences in unrecognized languages spelt in a recognized language •IM activity at unusual times could raise alerts Conferences • Collaborative chatting with ability to record conversation by attendees as minutes • Rules •Each conference has security level assigned to level l • If Ls(Employee) <= l, employee can read/write • Custom invitations to conferences also possible • Downgrading of conference level after starting possible, but is logged and all messages generated by users with higher security clearances will be hidden to less secure users File Sharing • All files that are shared are assumed to be at the sender’s security level • Levels can be changed by the system administrator • If Lo >= Ls, the file can be transferred • All manuals and public documents are tagged in a central repository by the sys-admin with Lo >= Ls(External) so that customer service can transfer documents or parts of it to clients Summary • Conflict between restrictions imposed by security policies and ease of use built into IM services • No security policy is a match for human ingenuity. • Further research is required and perhaps a new model for enterprise IM services • Unified messaging, currently getting popular, requires a extremely vast and diverse security policy. References http://www.symantec.com/avcenter/reference/secure.instant.messaging.pdf http://www.symantec.com/avcenter/reference/threats.to.instant.messaging.pdf http://www.go4teams.com/papers/enterprise_im.pdf http://www.jabber.com/download.php?dl=Extensible_IM_Essentials.pdf http://www.informationweek.com/story/IWK20030226S0009 Computer Security – Art and Science by Matt Bishop