Lecture Legal and Ethical Aspects of Computer Hacking (Power Point)
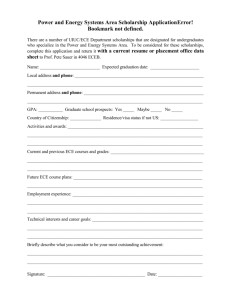
advertisement

Legal and Ethical Aspects of Computer Hacking ECE4112 – Internetwork Security Georgia Institute of Technology 1 Some History of Hacking • December 1993 USENET posting by Farmer and Venema • Idea of using techniques of an intruder to evaluate system security • Approach can help companies secure systems • Distributed Security Analysis Tool for Auditing Networks (SATAN) ECE 4110 - Internetwork Security 2 Ethical Hacking • Approval from the organization inside which the hacking will occur • Tiger team uses tools and techniques to evaluate security • Inform owner of files and systems before the fact ECE 4110 - Internetwork Security 3 Hackers • Term coined by the media back when computer time was stolen by unauthorized users • Prior to this media coined term, a Hacker was: “a person who enjoys exploring the details of programmable systems and how to stretch their capabilities; … one who programs enthusiastically.” ECE 4110 - Internetwork Security 4 Learning to Hack • Hacking Schools Zi Hackademy, Paris Civil Hackers school, Moscow • Hacking Classes This class Government Training Company training ECE 4110 - Internetwork Security 5 Ethical or Not? • So who is responsible for the outcome from these teachings? It’s the teachers! They are the ones teaching such techniques and tools and inflicting painful examinations. It’s the students! They are responsible for the actions they decide to take after learning tools that others use to attack. How can you figure out how to defend yourself if you do not understand the attacks? Only through knowledge can you defend yourself ECE 4110 - Internetwork Security 6 The Law • • • • • What types of policies are in place? How do they differ from each other? What kind of defined lines are there? Should these laws exist? Are these laws clear enough? ECE 4110 - Internetwork Security 7 United States Code Title 18 Crimes and Criminal Procedure • Part 1 > Chapter 119 > Section 2511 Interception and disclosure of wire, oral, or electronic communications prohibited. • Part 1 > Chapter 121 > Section 2701 Unlawful access to stored communications http://www4.law.cornell.edu/uscode/18/ ECE 4110 - Internetwork Security 8 Georgia Computer Systems Protection Act HB 822 • Computer Invasion of Privacy Any person who uses a computer or computer network with the intention of examining any employment, medical, salary, credit, or any other financial or personal data relating to any other person with knowledge that such examination is without authority shall be guilty of the crime of computer invasion of privacy. ECE 4110 - Internetwork Security 9 Patriot Act: • USA Patriot Act: Uniting and Strengthening America by Providing Appropriate Tools Required to Intercept and Obstruct Terrorism Act • U.S. government’s anti-terrorism policy ECE 4110 - Internetwork Security 10 Homeland Security • • • • • Department of Homeland Security Some call this a National Police Force Connects 22 different Agencies Exchange of information becomes a norm Centralized institution with the power to keep track of computer and email usage ECE 4110 - Internetwork Security 11 Georgia Institute of Technology • Computer and Network Usage Policy Available for all students and faculty http://www.oit.gatech.edu/information_securi ty/policy/usage/ • Authorize users and uses • Privileges for individuals • User Responsibilities Access to Facilities and Information ECE 4110 - Internetwork Security 12 GIT Computer and Network Usage Policy 4.6. Attempts to circumvent security Users are prohibited from attempting to circumvent or subvert any system.s security measures. This section does not prohibit use of security tools by personnel authorized by OIT or their unit. 4.6.1. Decoding access control information Users are prohibited from using any computer program or device to intercept or decode passwords or similar access control information. 4.6.2. Denial of service Deliberate attempts to degrade the performance of a computer system or network or to deprive authorized personnel of resources or access to any Institute computer system or network are prohibited. 4.6.3. Harmful activities Harmful activities are prohibited. Examples include IP spoofing; creating and propagating viruses; port scanning; disrupting services; damaging files; or intentional destruction of or damage to equipment, software, or data. ECE 4110 - Internetwork Security 13 Policy Maker Questions: • How easy is it to catch hackers and how many hackers have been caught? • Are these policies good enough? • Do the current policies actually define the limits of “hacking”? • Can companies hack into their own systems and find vulnerabilities? • Can other find vulnerabilities for them without being asked to? ECE 4110 - Internetwork Security 14 What if? • A Georgia Tech student uses their personal PC and the school’s network to do a port scan on a commercial web site. • A Georgia Tech student uses their personal PC and a commercial ISP to do a port scan on a commercial web site. • A Georgia Tech student sends a “spoofed mail” from the school account that appears to come from another user. • A Georgia Tech student uses a school computer and password guessing software to access and crack the administrator password. • A Georgia Tech student discovers that another user failed to log off when departing. The student uses the account to send an inflammatory email to the department chair. ECE 4110 - Internetwork Security 15 Lab Enhancements What corrections and or improvements do you suggest for this lab? Please be very specific and if you add new material give the exact wording and instructions you would give to future students in the new lab handout. You may cross out and edit the text of the lab on previous pages to make minor corrections/suggestions. General suggestions like add tool xyz to do more capable scanning will not be awarded extras points even if the statement is totally true. Specific text that could be cut and pasted into this lab, completed exercises, and completed solutions may be awarded additional credit. Thus if tool xyx adds a capability or additional or better learning experience for future students here is what you need to do. You should add that tool to the lab by writing new detailed lab instructions on where to get the tool, how to install it, how to run it, what exactly to do with it in our lab, example outputs, etc. You must prove with what you turn in that you actually did the lab improvement yourself. Screen shots and output hardcopy are a good way to demonstrate that you actually completed your suggested enhancements. ECE 4110 - Internetwork Security 16 17 References 1. Pfleeger, Charles. (2000). Security In Computing (2 nd ed.). Upper Saddle River, NJ: Printice Hall PTR. 2. From RedDragon on IRC, handed to newbies. January 16, 2001. http://newdata.box.sk/2001/jan/are.you.a.hacker.html 3. Protect Yourselves From Hackers CDs. 2002. http://www.onedollarcds.com/hack 4. Vasilyev, Ilya V. Civil Hackers' School. April 12, 1999. 5. Coomarasamy, James. Learning to Hack. December 1, 2001. http://news.bbc.co.uk/1/hi/world/europe/1686450.stm 6. Georgia Computer Systems Protection Act. Last Modified: June 29, 2002. http://www.security.gatech.edu/policy/law_library/gcspa.html http://klein.zen.ru/hscool/ 7. Title 18, Part 1, Chapter 119, Section 2511 – Interception and disclosure of wire, oral, or electronic communications prohibited. US Code Collection. http://www4.law.cornell.edu/uscode/18/2511.html 8. Title 18, Part 1, Chapter 121, Section 2701 – Unlawful access to stored communications. US Code Collection. http://www4.law.cornell.edu/uscode/18/2511.html 9. Minow, Mary. The USA PATRIOT Act and Patron Privacy on Library Internet Terminals. February 15, 2002. http://www.llrx.com/features/usapatriotact.htm 10. Bush Homeland Security bill nears passage by US Congress. The Editorial Board. November 18, 2002. http://www.wsws.org/articles/2002/nov2002/homen18.shtml 11. Georgia Institute of Technology Computer and Network Usage Policy. Office of Information Technology. Last Modified October 20, 2003. http://www.oit.gatech.edu/information_security/policy/usage/ 12. Baase, Sara. A Gift of Fire: Social, Legal, and Ethical Issues for Computers and the Internet. 2nd edition. Prentice Hall. 2003. Page 289. 13. Palmer, C.C. Ethical Hacking. International Business Machines Corporation. Copyright 2001. www.research.ibm.com/journal/sj/403/palmer.html 14. Harvey, Brian. Computer Hacking and Ethics. April 1985. www.cs.berkeley.edu/~bh/hackers.html 15. Shell, Barry. Ethical Hacking. Georgia Straight Weekly, Vancouver, BC. September 14, 2000. http://css.sfu.ca/update/ethical-hacking.html ECE 4110 - Internetwork Security 18