Wireless Networking II - Computer Graphics Home
advertisement

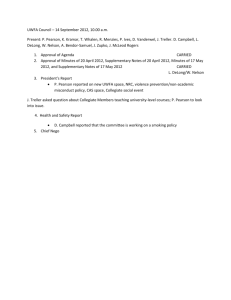
Chapter 7 802.11 Security 802.11 LAN management Other local wireless technologies © 2013 Pearson 2 Drive-By Hackers ◦ Sit outside the corporate premises and read network traffic ◦ Can send malicious traffic into the network ◦ Easily done with readily downloadable software War Drivers ◦ Merely discover unprotected access points— become drive-by hackers only if they break in ◦ War driving per se is not illegal © 2013 Pearson 3 Unprotected Access Points ◦ Drive by hackers can associate with any unprotected access point. ◦ They gain access to the local area network without going through the site firewall. © 2013 Pearson 4 Rogue Access Points ◦ Unauthorized access points that are set up by a department or an individual ◦ Often have very poor security, making drive-by hacking easier ◦ Often operate at high power, attracting many hosts to their low-security service © 2013 Pearson 5 Core security protocols protect communication between a wireless client and a legitimate access point. They provide encryption for confidentiality and other cryptographic protections. © 2013 Pearson 6 802.11 core security protocols protect only wireless client– access point communication. © 2013 Pearson 7 Provide Security Between the Wireless Station and the Wireless Access Point ◦ Client (and perhaps access point) authentication ◦ Encryption of messages for confidentiality © 2013 Pearson 8 Wired Equivalent Privacy (WEP) ◦ Initial rudimentary security provided with 802.11 in 1997. ◦ Everyone shared the same secret encryption key, and this key could not be changed automatically. ◦ Because secret key was shared, it did not seem to be secret. Users often gave out freely ◦ Key initially could be cracked in 1 to 2 hours; now can be cracked in 3 to 10 minutes using readily available software. © 2013 Pearson 9 Wireless Protected Access (WPA) ◦ The Wi-Fi Alliance Normally certifies interoperability of 802.11 equipment Certified equipment may display the Wi-Fi name on their boxes Created WPA as a stop-gap security standard in 2002 until 802.11i was finished © 2013 Pearson 10 Wireless Protected Access (WPA) ◦ Designed for upgrading old equipment WPA uses a subset of 802.11i that can run on older wireless NICs and access points. WPA added simpler security algorithms for functions that could not run on older machines. ◦ Equipment that cannot be upgraded to WPA should be discarded. © 2013 Pearson 11 802.11i (WPA2) ◦ Uses AES-CCMP with 128-bit keys for confidentiality and key management. ◦ 802.11i is the gold standard in 802.11 security. ◦ But companies have large installed bases of WPAconfigured equipment, so they are hesitant to upgrade. ◦ WPA has now been partially cracked, and this is leading many firms to upgrade. © 2013 Pearson 12 WEP Initial core security standard. Easily cracked today. WPA Has been partially cracked. Large installed base makes upgrading the entire network to 802.11i expensive. 802.11i (WPA2) Today’s preferred standard. Extremely strong. © 2013 Pearson 13 Both WPA and 802.11i have two modes of operation. ◦ 802.1X mode For large organizations Uses a central authentication server for consistency Authentication server also provides key management Wi-Fi Alliance calls it Enterprise Mode © 2013 Pearson 14 Both WPA and 802.11i have two modes of operation. ◦ 802.1X mode 802.1X standard protects communication with an extensible authentication protocol. Several EAP versions exist with different security protections. Firm implementing 802.1X must choose one. Protected EAP (PEAP) is popular because Microsoft favors it. © 2013 Pearson 15 Both WPA and 802.11i have two modes of operation. ◦ Pre-Shared Key mode for homes or small firms For homes or small businesses with a single access point. Access point does all authentication and key management. All users must know an initial pre-shared key (PSK). Each, however, is later given a unique key. © 2013 Pearson 16 Both WPA and 802.11i have two modes of operation. ◦ Pre-Shared Key mode If the pre-shared key is weak, it is easily cracked. Pass phrases that generate keys must be at least 20 characters long. Wi-Fi Alliance calls this personal mode. © 2013 Pearson 17 Can use Can use PSK 802.1X mode? mode? WPA Yes Yes 802.11i Yes Yes Both WPA and 802.11i use both modes. This is not surprising because WPA was derived from 802.11i. © 2013 Pearson 18 © 2013 Pearson 19 802.1X Mode (See Figure 7-5) ◦ 802.1X in WPA and 802.11i protects client-access point communication with an extensible authentication protocol. EAP must be protected. No problem with UTP. Big problem for wireless. For wireless, EAP had to be extended. © 2013 Pearson 20 802.1X Mode (See Figure 7-5) ◦ 802.1X standard protects communication with an extensible authentication protocol. Several EAP versions exist with different security protections. Firm implementing 802.1X must choose one. Protected EAP (PEAP) is popular because Microsoft favors it. © 2013 Pearson 21 © 2013 Pearson 22 © 2013 Pearson 23 WEP ◦ Used the same shared key for everyone. ◦ It was used for a great deal of traffic. ◦ This made the key easy to break. PSK Mode in 802.11i ◦ Only uses the shared initial key for initial communication, so can’t be cracked. ◦ Only a few people share this key so won’t give it out. ◦ Each host then gets a different shared session key. ◦ Too little traffic is sent with this key to be cracked. © 2013 Pearson 24 Sits outside the premises or in a wireless hot spot ◦ A PC with software to emulate an access point ◦ Entices the wireless client to associate with it © 2013 Pearson 25 Establishes a second connection with a legitimate access point ◦ All traffic between the wireless client and network servers passes through the evil twin. © 2013 Pearson 26 This is a classic man-in-the-middle attack. Attacks on confidentiality because evil twin reads all traffic. ◦ Client encrypts traffic. ◦ Evil twin decrypts it and reads it. ◦ Evil twin reencrypts it and sends it on. Evil twin can also send attack packets, which do not pass through the border firewall. © 2013 Pearson 27 Virtual Private Networks (VPNs) ◦ End-to-end encryption with a pre-shared client-server secret ◦ The secret is never transmitted so cannot be intercepted. © 2013 Pearson 28 Usually just called WPS Protocol to make it easier to connect clients to access points Very popular Created by the Wi-Fi Alliance, not the 802 Committee © 2013 Pearson 29 Designed poorly Pre-shared keys can be cracked in about 5,500 attempts ◦ Easy to do with automated attacks Only solution is to turn off WPS at the router ◦ Many routers cannot even turn it off A problem for PSK but not 802.1X © 2013 Pearson 30 Either overloads the access point with traffic Or sends a command to get a client to disassociate from an access point Uncommon but dangerous © 2013 Pearson 31 802.11 Security 802.11 LAN management Other local wireless technologies © 2013 Pearson 32 Access Points Placement in a Building ◦ Must be done carefully for good coverage and to minimize interference between access points. ◦ Lay out 30-meter to 50-meter radius circles on blueprints. ◦ Adjust for obvious potential problems such as brick walls. ◦ In multistory buildings, must consider interference in three dimensions. © 2013 Pearson 33 Access Points Placement in a Building ◦ Install access points and do site surveys to determine signal quality. ◦ Adjust placement and signal strength as needed. ◦ In commercial access points, signal strength and other configuration information can be actively controlled. © 2013 Pearson 34 Remote Access Point Management ◦ The manual labor to manage many access points can be very high. ◦ They must be managed efficiently through automation. © 2013 Pearson 35 © 2013 Pearson 36 Remote Access Point Management ◦ Desired networking functionality: Notify the WLAN administrators of failures immediately. Support remote access point adjustment. Should provide continuous transmission quality monitoring. Allow software updates to be pushed out to all access points or WLAN switches. Work automatically whenever possible. © 2013 Pearson 37 Remote Access Point Management ◦ Desired security functionality: Notify administrator of rogue access points. Notify administrator of evil twin access points. Notify the administrator of flooding denial-ofservice attacks. Notify the administrator of disassociate message denial-of-service attacks. Instantly deny access to selected stations under selected conditions. © 2013 Pearson 38 Box © 2013 Pearson Expressing ratios of transmission power ◦ Attenuation of signal during propagation (-) ◦ Amplification of signal so it will travel farther (+) Multiples of 3 dB (decibels) ◦ ◦ ◦ ◦ ◦ +3 dB +6 dB +9 dB -3 dB -6 dB © 2013 Pearson X2 (times two) power X4 power ? ½ power ? 40 Expressing ratios of transmission power ◦ Attenuation of signal during propagation (-) ◦ Amplification of signal so it will travel farther (+) Units of 10 dB ◦ +10 dB X10 power ◦ +20 dB ? ? ◦ -10 dB ? ◦ -20 dB ? © 2013 Pearson 41 Power is measured in Watts (W) ◦ Milliwatt (mW) = 1/1000 of a Watt Transmitted power is 12 mW ◦ Attenuation during travel is -6 dB ◦ Final transmission power: ? Radio power is 2 mW ◦ Antenna amplifies signal by 9 dB ◦ Final transmission power: ? © 2013 Pearson 42 In radio engineering, you often have to express the ratio of two signal powers, P1 and P2. ◦ Amplification may make P2 larger than P1, the original signal strength. ◦ Attenuation may make P2 smaller than P1, the original signal strength. ◦ Connector loss may make transmitted power P2 smaller than P1, the original signal strength. © 2013 Pearson 43 In general, simple ratios are easy to understand. However, P1 and P2 can vary by orders of magnitude, giving numbers that are difficult to interpret by reading. Radio engineers express signal ratios in a logarithmic scale, decibels (dB). © 2013 Pearson 44 Suppose you have amplification, so that while P1 is 20 milliwatts (mW), P2 is 80 mW. Use the Excel LOG10() function. If P2 > P1, then the ratio is greater than 1, and the dB value is positive 45 © 2013 Pearson Suppose you have attenuation, so that while P1 is 30 milliwatts (mW), P2 is 1.3 mW. Use the Excel LOG10() function. If P2 < P1, then the ratio is less than 1, and the dB value is negative © 2013 Pearson 46 Suppose you have amplification, so that while P1 is 20 milliwatts (mW), P2 is 30 mW. ◦ What is LdB? © 2013 Pearson 47 Suppose you have a loss of power of 30% at a coupler between the radio and the antenna. ◦ How would you compute LdB? © 2013 Pearson 48 A doubling of power is 3.0103 dB ◦ This is almost exactly 3. ◦ Use 3 in estimates. ◦ Fill in the two missing dB values. © 2013 Pearson Ratio N (as in 2N ) dB 16 8 4 4 3 2 9 dB 6 dB 2 1 1/2 1/4 1 0 -1 -2 3 dB 0 dB -3 dB -6 dB 1/8 -3 49 A factor of 10 increase is 10 dB ◦ This is exactly 10. ◦ Fill in the two missing dB values. © 2013 Pearson Ratio N (as in 2N ) dB 10,000 1,000 100 4 3 2 30 dB 20 dB 10 1 1/10 1/100 1 0 -1 -2 10 dB 0 dB -10 dB -20 dB 1/1,000 -3 50 dB gives power ratios. dBm gives absolute power, relative to 1 milliwatt (mW). ◦ P1 = 1 mW What is the dBm for 2 mW? What is the dBm for 0.01 mW? What is the dBm for 1 Watt? © 2013 Pearson 51 Power ratios multiply ◦ Initial power = 1 Watt ◦ Loss of power at antenna coupler = .5 ◦ Loss of power due to attenuation = 90% ◦ Loss of power due to wall = 75% ◦ What is the final power? © 2013 Pearson 52 Decibels add ◦ Initial power = 1 Watt (30 dBm) ◦ Loss of power at antenna coupler = .5 (-3 dB) ◦ Loss of power due to attenuation = 90% (-10 dB) ◦ Loss of power due to wall = 75% (-6 dB) ◦ What is the final power? © 2013 Pearson 53 Converting decibels back to power ratios © 2013 Pearson 54 Converting decibels back to power ratios ◦ What is the power ratio for 30 dB? ◦ What is the power ratio for -8 dB? (Do it in a spreadsheet.) © 2013 Pearson 55 802.11 Security 802.11 LAN management Other local wireless technologies © 2013 Pearson 56 Use 802.11i Bluetooth Near Field Communication (NFC) Ultrawideband (UWB) Wi-Fi Direct gives direct communication between two wireless devices Personal area networks (PANs) around a desk or a person’s body Very near communication between two wireless hosts Extremely high speed, short distance communication © 2013 Pearson 57 Wi-Fi Direct Bluetooth Near Field Ultrawideband Communi(UWB) cation (NFC) Typical Speed Service Range 20-300 Mbps 30-50 m 2 Mbps 10 m 106, 212, 100 Mbps or 424 kbps 10 cm 10 m Requires Wall Power Yes No No Yes Service Band 2.4 and 5 GHz 2.4 GHz 13.56 kHz UWB channels typically span multiple entire service bands © 2013 Pearson 58 For Personal Area Networks (PANs) ◦ Devices on a person’s body and nearby (earphone, mobile phone, netbook computer, etc.) ◦ Devices around a desk (computer, mouse, keyboard, printer) © 2013 Pearson 59 Cable Replacement Technology ◦ For example, with a Bluetooth phone, you can print wirelessly to a nearby Bluetooth-enabled printer. ◦ Does not use access points. © 2013 Pearson 60 Classic Bluetooth High-Speed Bluetooth Low-Energy Bluetooth Principal Benefit Good performance at low power High-speed transfers available when needed Ultra-long battery life and ultra-fast setup times Speed Up to 3 Mbps Up to about 24 Mbps Up to 200 kbps Expected Duty Cycle Low to High Low to High Very Low High ~30 m Not Given Very Low ~15 m < 3 ms Power Required Low Distance ~10 m Setup Time <6s © 2013 Pearson 61 © 2013 Pearson 62 A device, in this case the Desktop, can be simultaneously a master and a slave. © 2013 Pearson 63 Headset © 2013 Pearson 64 Bluetooth Profiles ◦ 802.11 did not have to develop application standards. Many standards already existed. ◦ But standards did not exist for new short-distance applications such as printing to a printer. ◦ The Bluetooth Special Interest Group had to develop various standards in addition to radio transmission standards. ◦ It called these Bluetooth profiles. © 2013 Pearson 65 Bluetooth Profiles © 2013 Pearson 66 Peering ◦ When two devices first encounter each other, they must go through a negotiation process. ◦ This negotiation process is called peering. ◦ It involves the exchange of device information. ◦ It may involve authentication. ◦ It may also involve one or both of the device owners explicitly deciding if the two devices should be allowed to communicate. © 2013 Pearson 67 Service Discovery Profile (SDP) ◦ Peering uses the Service Discovery Profile (SDP). ◦ Normally, a device is in discoverable mode. ◦ If it receives a Service Discovery Protocol request, it will send information about itself: Name Device class Bluetooth profiles supported Technical information such as manufacturer’s name © 2013 Pearson 68 Binding ◦ After peering is complete, the two devices are bound. ◦ They can begin communicating. ◦ If they are brought together later, they are still bound. ◦ They will begin communication without the peering process. ◦ This allows fast setup. ◦ The owner of either device can end the binding. © 2013 Pearson 69 802.11 Wi-Fi uses 20 MHz or 40 MHz channels in the 2.4 GHz and 5 GHz bands. Bluetooth operates in the 2.4 GHz band. Bluetooth divides the band into 79 channels, each 1 MHz wide. © 2013 Pearson 70 Bluetooth radios hop among the frequencies up to 1,600 times per second. These radios avoid channels where other devices (including 802.11 devices) are active. © 2013 Pearson 71 © 2013 Pearson 72 Payment of bus fares (already popular in some countries) Opening car doors Turning on the ignition Building door entry control Sharing business cards Continued… © 2013 Pearson 73 Sharing webpages between mobile devices Retail payments, including loyalty points and coupons (beginning to be popular) NFC posters with tap points for more communication Passive Radio Frequency ID (RFID) Tags © 2013 Pearson 74 Radio frequency ID tags contain information about an item. A passive RFID tag has no internal power source. When read by an NFC device, the power of the reader request gives power for the response. 13.56 kHz was specified by ISO/IEC for passive RFID tags long before NFC standards were created. With sensitive antennas, NFC transmission can be eavesdropped upon from a distance. © 2013 Pearson 75 Enormously wide channels Very low power per hertz to avoid interfering with other transmissions Very high speeds over short distances (~10 m) © 2013 Pearson 76 Threats ◦ Eavesdropping ◦ Data modification ◦ Impersonation ◦ Denial-of-service attacks © 2013 Pearson 77 Cryptological Security ◦ Some local wireless technologies have no cryptological security. ◦ Example: Near field communication for reading passive ID tags. ◦ They rely on short transmission distances to foil eavesdroppers. ◦ Directional antennas and amplifiers can defeat this. © 2013 Pearson 78 Strength of Security ◦ Some have reasonably good security. ◦ Example: Bluetooth ◦ However, still not as strong as 802.11i and WPA security. © 2013 Pearson 79 Device Loss or Theft ◦ In this age of bring your own device (BYOD) to work, this is a serious problem. ◦ Most devices are protected only by short PINs. © 2013 Pearson 80 Maturity ◦ In general, new security technologies take some time to mature. ◦ During this period, they often have vulnerabilities that must be fixed quickly. ◦ User companies must master security for each new technology. © 2013 Pearson 81 802.11 Security 802.11 LAN management Other local wireless technologies © 2013 Pearson 82