Slides
advertisement

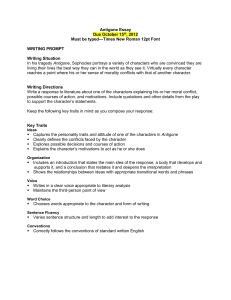
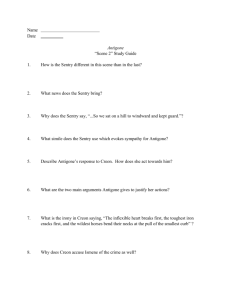
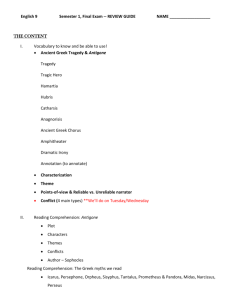
Antigone: Security Policy Management in Group Communication Patrick McDaniel EECS, University of Michigan April 30, 2001 Outline Problem Statement Ismene Group Policy Management Antigone Communication Infrastructure Implementation and Applications Telecommuters Scenario 1 Printer Consultants Scanner Fax Start Application 1 Application 2 Confidentiality Integrity Authenticity Authorization Headquarters Customers Scenario 2 Confidentiality Integrity Authenticity Authorization Commitment Satellite Offices Contract Negotiation Arbitrator Legal Representatives Problem How do we develop and enforce a group session security policy appropriate for the run-time environment and membership within a single framework? Session requirements may be unique Each entity may have unique abilities and constraints The structure and needs of the group may change dramatically over time (Our) definition of session policy Member Member “... a statement of the entirety of security relevant parameters and facilities used to implement the group.” Member Member Network Member Member Member Member who are the entities allowed to participate and in what capacity (authorization and access control) which mechanisms will be used to achieve mission critical goals (provisioning) Note: historically not restricted to electronically distributed Related Work Policy Management Group/Coalition Policy Management MSME, GSAKMP, DCCM, SMuG/MSEC Authorization and Access Control IPsec SPS, Policy Working Group GAA-API, Extended ACLs, and many more Trust management REFEREE, PolicyMaker, KeyNote, SPKI/SDSI, Strongman Contributions Investigation of Policy Group Policy Design Space Policy Determination (Ismene) Policy Enforcement (Antigone) Goals Policy Determination Flexibly express conditional session requirements Support reconciliation of member policies Allow assessment of session policy with local requirements Efficiently derive/evaluate policy Policy Enforcement Provide efficient, secure (unreliable) group communication Support a wide range of security services/policies Easily integrate new services/policies The Antigone/Ismene Approach Ismene Policy Instantiation Policy Compiler Local Policies Group Policy Application Confidentl/DES Integrity/HMAC KeyMgmt/LKH Policy Engine Antigone Group API Security Services Transport Services Outline Problem Statement Ismene Group Policy Management Ismene Policy Instantiation Policy Compiler Local Policies Group Policy Application Confidentl/DES Integrity/HMAC KeyMgmt/LKH Policy Engine Antigone Group API Security Services Transport Services Antigone Communication Infrastructure Implementation and Applications Secure Group Policy Dimensions Session rekeying policy Data Security policy Distribution/accuracy of membership Process failure policy Content guarantees Membership policy How and when to rekey? Failures detected/recovered from? Authorization and Access Control Example Policy : Confidentiality Confidentiality Policy : All code reviews using the distributed editor must be confidential. session: GroupType(codeReview), Application(DistEdit) :: config(datahandler(guar=conf)); Policy states the requirements appropriate for application, data sensitivity, membership, and other aspects of the environment Example Policy: Group Participation Group Participation Policy: Only members of the legal department can participate in contract negotiations. join : GroupType(contractNegotiation), credential( &cert, $cert.issuer=$CA, $cert.type="X.509", $cert.ORG=“LegalDept" ) :: accept; Any number of possible services may be used for stating authorization and access control An Antigone Group Policy Issuer Member (M 1) Initiator (M 0) Member (M 2) Member (M 3) Policy Specification ... Key Member (M n) Instantiated Policy Policy Repository + Local Policy Ismene Policy Description Language (IPDL) Clause : (policy) tag: (if) conditionals :: (then) consequences Tags identify sub-policies that must be satisfied, Conditionals test the environment (predicate) Consequences apply policy E.g., “All Contract negotiations must use a leave-sensitive LKH key management service. Other sessions should use KEK key management.” groupprot: GroupType(contractNegotiation) :: config(lkhkeymgmt(sens=leave)); groupprot: :: config(kekkeymgmt()); Consequences Describes results of positive evaluation of conditionals Tags Configuration config(lkhkeymgmt()); config(lkhkeymgmt(keytime=10secs)); Pick Statements pick(config(lkhkeymgmt(keytime=10secs)), config(kekkeymgmt(keytime=5secs)) ); Provisioning Policy Evaluation provision : :: keymgt, dhandler, fprot; keymgt : GroupType(contractNegotiation) :: config(lkhkeymgt()); keymgt : :: config(kekkeymgt()); dhandler : GroupType(contractNegotiation) :: config(dhnd(crypt=aes)); dhandler : :: pick(config(dhnd(crypt=des), config(dhnd(crypt=rc4))); fprot: :: config(chainfp()), fpparms; fpparms: groupsize(>100) :: config(chainfp(hbperiod=5)); fpparms: config(chainfp(hbperiod=3)); Authorization and Access Control Credentials are modeled sets of attributes E.g., X.509 Certificates consist of attributes for subject/common name, … Credential conditions test the existence of credentials with specific attributes Authorization and Access Control Clauses join : day(Monday), config(kekkeymgt()), credential(&tick,$tick.service=contractconference, $tick.server=bigco.com) :: accept; IPDL represents a closed world Integrating External Authorization and Access Control Current approach designed to express simple authorization and access control Some applications may require more sophistication Using external policy infrastructure (e.g. KeyNote) join : KeyNote($requestor, $attrset, $grppol, $creds) :: accept; Policy Reconciliation The group and each local policy is Ismene Policy evaluated (result: config, pick, Compiler Auth+A-Cntl statements) Group Local Example: Policy Policies Confidentl/DES Integrity/HMAC KeyMgmt/LKH kekkeymgt(), chainfp(hbperiod=5), pick(config(dhnd(crypt=des), config(dhnd(crypt=rc4))) Reconciliation: Given evaluated group and local policies, how do we arrive at single configuration? Provisioning Reconciliation Strategies Option 1: Prioritized local policies, implemented Group policy a, b, pick(c,d), pick(e,f) Local policy A d, pick(e,f) Policy Instantiation a,b,d,e Local policy B d, pick(e,g) Option 2: Finding largest satisfiable subgroup (NP-complete) Reduction:MAX2SAT Authorization and Access Control Reconciliation Strategies How do we reconcile the authorization and access control statements to arrive at a definition satisfying all local policies OR (if any policy would accept) AND (if all policies accept) Group policy join : C1 :: accept; join : C2 :: accept; Local policy A join : C3 :: accept; Local policy B join : C4 :: accept; Policy Instantiation join : ((C1 or C2) and c3 and c4) :: accept; Compliance Is the session policy instantiation in consistent with my local policy? Provisioning compliance (containment), Simple search – P-time Authorization and Access Control For all actions/conditions, is the group policy more specific (less permissive) than local policy c | (c) (c) Closely related problem of secure interoperatibility is NP [Gong and Qian, 1994] Note: reconciled policies are trivially compliant Ismene Summary IPDL is a language for expressing group policy Provisioning and access control flexibly specified Policies sensitive to changing conditions Algorithm Efficiency Participant Initiator/ Reconciled Member Unreconciled Member Reconciliation A+ACtrl Compliance P Known a priori Known a priori None P P Other features Provisioning Compliance Analysis, reconfig, … Outline Problem Statement Ismene Group Policy Management Antigone Communication Infrastructure Ismene Policy Instantiation Policy Compiler Local Policies Group Policy Application Confidentl/DES Integrity/HMAC KeyMgmt/LKH Policy Engine Antigone Group API Security Services Transport Services Implementation and Applications Antigone Application Group communication framework implementing Group Interface policy though the the Mechanisms Layer flexible composition of ... M M M M security mechanisms Broadcast Transport Layer Composition directed by the security policy Multicast/Point to Point - UDP/IP specification Study of the requirements and enforcement of group policy 1 2 3 n ; Policy Engine Antigone Policy Enforcement Architecture Mechanism Given a group policy, coordinates the provisioning and enforcement of available services … is a basic service used to implement the group E.g., Data-handler (MSEC, GSAKMP, …) Event-based architecture Security relevant events are detected and distributed to interested mechanisms Policy directs reaction to observed events Antigone Architecture Application ; Group Interface M1 Mechanisms Layer ... M M 2 3 Mn Broadcast Transport Layer Multicast/Point to Point - UDP/IP Policy Engine Policy Enforcement Group Interface Policy Engine SE Send? ... ... SE Membership Management Event Bus Key Management ... SE sent SE buf Yes Data Handler sentSESEbufbuf Fault Detection sent SE buf buf hdr encr hmac Broadcast Transport buf ... Features/Optimizations Message construction/marshalling Internal buffer handling Implementing the many mechanism protocol variants difficult (e.g., AH, ESP, MESP, …) Generalized message handling Messages are frequently created/destroyed Internal heap of often used/resized buffer objects Minimization of byte copying, key context switching Throughput and Latency Latency 10 5 9 4.5 8 4 7 3.5 RTT (msec) Megabytes/second Throughput 6 5 4 3 2.5 2 3 1.5 2 1 1 0.5 0 512 1024 4096 Packet size (bytes) Direct Antigone 8192 0 30 512 1024 Packet Size Direct Antigone 4096 8192 Antigone Overhead Constant overhead (50usec /message) 4% 10% Marshalling Event Processing Buffer Management Queueing 46% 40% Antigone Summary Framework for enforcing group policy Supports a wide range of security services Event based architecture Easy integration of new services and policies Efficient implementation Low per packet overhead (50usec) High throughput Outline Problem Statement Ismene Group Policy Management Antigone Communication Infrastructure Implementation and Applications Ismene Policy Instantiation Policy Compiler Local Policies Group Policy Application Confidentl/DES Integrity/HMAC KeyMgmt/LKH Policy Engine Antigone Group API Security Services Transport Services Implementation Status Antigone API – six libraries, implementing various security, group management, and transport level services Language grammar, apcc compiler 30,000 lines of C++ code Supports a wide range of secure group communication mechanisms (e.g., OpenSSL) Currently alpha Experimenting/optimizing/developing Freely available http://antigone.eecs.umich.edu Applications AMirD – secure filesystem replication Secure Group Messaging Service Filesystem state updated over secure “control group” Simultaneous groups distribute files implementing policies appropriate for their content Group based secure instant messaging (I.e., ICQ, MS-M) Native Antigone - “Bump-in-the stack” Secure existing applications Conclusions Ismene : language and infrastructure for flexible and efficient policy determination Antigone : framework for the flexible and efficient enforcement of group security policy Flexible conditional statements of provisioning and authorization and access control Efficient reconciliation and analysis (and compliance) Unreliable group communication service Easy integration of new services and policies Low latency, high throughput group communication Applications illustrate the Antigone policy approach Contact Information Comments, questions are welcomed pdmcdan@eecs.umich.edu Antigone/Ismene Website http://antigone.eecs.umich.edu/