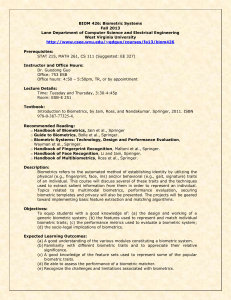
Biometrics, Security, & You

Presenter: Dr. Karl Ricanek, Jr.
Director Face Aging Group
Dept. of Computer Science, UNCW
Overview
Biometrics Definition
History of Biometrics
Biometrics Overview
Variety of Biometric Technology
Anatomy of a Biometric
Face recognition biometric deep dive
Acquiring face, features of face used, similarity measures, etc.
Remaining challenges of FR
Biometrics, Security and You
Security needs for biometrics
Why implement biometrics for security?
Where can we find biometrics in use today?
What are the future trends for biometrics? Is the movie “Minority Report” on target?
What are you opinions of a pervasive use of biometrics for security purposes?
Wrap Up / Q&A
1/28/09 Biometric Weekly Meetings (Spring 09) 2
Biometrics Definition
Biometrics (wikipedia) -- Biometrics are used to identify the identity of an input sample when compared to a template, used in cases to identify specific people by certain characteristics.
possession-based: using one specific "token" such as a security tag or a card knowledge-based: the use of a code or password.
Biometrics (questbiometric.com) -- The word "biometrics" is derived from the Greek words 'bios' and 'metric' ; which means life and measurement respectively. This directly translates into "life measurement”. General science has included biometrics as a field of statistical development since the early twentieth century. A very good example is the statistical analysis of data from agricultural field experiments comparing the yields of different varieties of wheat. In this way, science is taking a life measurement of the agriculture to ultimately determine more efficient methods of growth.
Biometrics technologies measure a particular set of a person's vital statistics in order to determine identity.
Biometrics in the high technology sector refers to a particular class of identification technologies. These technologies use an individual's unique
biological traits to determine one's identity. The traits that are considered include fingerprints, retina and iris patterns, facial characteristics and many more.
1/28/09 Biometric Weekly Meetings (Spring 09) 3
History of Biometrics
The earliest written record of biometric use was by the Egyptians during the building of the great pyramids. The workforce for building the pyramids has been estimated in the tens of thousands.
Payments were recorded based on identifying characteristics of the person, parentage, and place of birth.
China 14 th Century – merchants stamped children’s palm prints and footprints on paper with ink to differentiate the young children. Practice is in use today throughout the world.
Alphonse Bertillon (Paris 1890) – developed a system track criminals by taking multiple body measurements. The system known as Bertillonage was used for years until it was discovered that some people had the same body measures.
(not a unique measure.)
Richard Edward Henry (Scotland Yard) – is credited for developing the fingerprinting method. (Note: that the Chinese had been doing this for
centuries prior.)
The last three decades has seen an explosion in the development of, and use of, biometrics. An impetus was the tragedy of September 11.
1/28/09 Biometric Weekly Meetings (Spring 09) 4
Biometrics Overview
The security field uses three different types of identification:
Something You Know —a password, PIN, or piece of personal information (such as your mother's maiden name);
Something You Have—a card key, smart card, or token (like a Secure ID card); and/or
Something You Are—a biometric.
Of these, a biometric is the most secure and convenient authentication tool. It can't be borrowed, stolen, or forgotten, and forging one is practically impossible.
1/28/09 Biometric Weekly Meetings (Spring 09) 5
Biometrics Overview (cont.)
Types of Authentication
Identification (1 to many) - A task where the biometric system searches a database for a reference matching a submitted biometric sample, and if found, returns a corresponding identity. A biometric is collected and compared to all the references in a database. Identification is “closed-set” if the person is known to exist in the database.
Verification (1 to 1) - A task where the biometric system attempts to confirm an individual’s claimed identity by comparing a submitted sample to one or more previously enrolled templates.
Watch List (1 to few) - The biometric system determines if the individual’s biometric template matches a biometric template of someone on the watch list. The individual does not make an identity claim.
1/28/09 Biometric Weekly Meetings (Spring 09) 6
Biometrics Overview (cont.)
Characteristics of a biometric for authentication:
Uniqueness -The same trait will not appear in two people.
Universality -The trait has to occur in many people as possible.
Permanence -The trait does not change over time.
Measurability -The trait can be measured with simple technical instruments.
User friendliness -The trait is easily measured with minimal discomfort.
1/28/09 Biometric Weekly Meetings (Spring 09) 7
Variety of Biometrics
Two categories of biometrics:
1/28/09 Biometric Weekly Meetings (Spring 09) 8
Variety of Biometrics (cont.)
Passive Biometrics – does not require active participation by subject.
Face Recognition: The identification of a person by their facial image characteristics.
Voice Recognition: Identification using the acoustic features of speech that have been found to differ between individuals.
(partial passive)
Iris Recognition: This identification method uses the unique characterizes of the iris. (partial passive)
Gait Recognition: This identification method uses the unique characteristics of a person’s walking pattern differentiate people.
1/28/09 Biometric Weekly Meetings (Spring 09) 9
Variety of Biometrics (cont.)
Active Biometrics – does require active participation of subject.
Fingerprint Recognition: Identification by using patterns of friction ridges and valleys on an individual's fingertips are unique to that individual. By far the most widely accepted biometric.
Hand and Finger Geometry: Identification by measuring either physical characteristics of the fingers or the hands.
Signature Verification: Identification using the dynamic analysis of a signature to authenticate a person (keystroke biometric is a derivative of this
form of biometric).
Venial Recognition: A system for Identification using a persons unique vein patterns (retina recognition is a form).
Palm Print Recognition: Uses the lines on one's palm to identify an individual
(similar to fingerprint recognition).
Bio-signal Recognition: Identification by analyzing signals generated by the body through its normal chemical/electrical (neural/nervous) system. (Still in
its infancy as a biometric.)
DNA: Identification based on the unique sequence of DNA that all persons have.
1/28/09 Biometric Weekly Meetings (Spring 09) 10
Variety of Biometrics (cont.)
Multimodal biometric systems are those that utilize more than one physiological or behavioral characteristic for enrollment, verification, or authentication.
Multi-modal biometric systems are looked to as a means of:
reducing false non-match and false match rates,
providing a secondary means of enrollment, verification, and identification if sufficient data cannot be acquired from a given biometric sample, and
combating attempts to spoof biometric systems through nonlive data sources such as fake fingers.
1/28/09 Biometric Weekly Meetings (Spring 09) 11
Anatomy of a Biometric
Face Recognition (identification) – identifies people from images of their face when presented to the system.
Process
Enrollment -- faces associated with a group must be “enrolled” into the system. The process of enrollment involves extracting specific features from the face image and projecting them in to a hyper dimensional space (face space).
Query/probe – the face to be identified is presented to the system.
The system extracts the features that it uses and projects the face into the face space.
Similarity Measure – the system generates a similarity score of the probe against all enrolled faces. The system uses a criteria to determine which of the enrolled faces it should match to, if any at all. (The probe may not be a known person, i.e. a person not enrolled.)
Identification – the system selects the best enrolled candidate and returns it to the end-user, if a match is determined likely.
1/28/09 Biometric Weekly Meetings (Spring 09) 12
Anatomy of a Biometric (cont.)
Enrollment : Capture and processing of user biometric data for use by system in subsequent authentication operations.
Acquire and Digitize
Biometric Data
Extract
High Quality Biometric
Features/Representation
Formulate
Biometric
Feature/Rep Template
Database
Template
Repository
Authentication/Verification : Capture and processing of user biometric data in order to render an authentication decision based on the outcome of a matching process of the stored to current template.
Acquire and Digitize
Biometric Data
1/28/09
Extract
High Quality Biometric
Features/Representation
Formulate
Biometric
Feature/Rep Template
Biometric Weekly Meetings (Spring 09)
Template
Matcher
13
Anatomy of a Biometric (cont.)
FR’s remaining challenges:
FR has been an active research topic for the last two decades and many system challenges have been overcome:
lateral pose – from left profile to full frontal to right profile (use 3D model
correction) angular pose – up/down head position profile (use 3D model correction) azimuth pose – tilt of the head profile (use 3D model correction) lighting/shadowing – lighting differences between enrolled and probe images has almost been eliminated as a source of error. Strong angular lighting/shadowing is still a research topic. (Use lighting models to correct.) facial expression/gesture – has made significant in roads over the last decade. A facial gesture can change the location of features and the shape of the face. (Still
being resolved.) aging of face – an aging face undergoes significant changes that affect the shape and appearance of the face in unpredictable manner. The problem is further exacerbated by the nonlinear effects of age and the multitude of parameters that contribute to aging, e.g. sun exposure, smoking, drugs, genetics, gender, ethnicity, etc. (My research team is working to resolve these issues.)
1/28/09 Biometric Weekly Meetings (Spring 09) 14
Anatomy of a Biometric (cont.)
Example of typical aging:
1/28/09
Caucasian male 18 - 42
Biometric Weekly Meetings (Spring 09)
Caucasian female 32 - 44
15
Anatomy of a Biometric (cont.)
Facial model demonstration.
1/28/09 Biometric Weekly Meetings (Spring 09) 16
Biometrics, Security, & You
Security needs for biometrics:
Physical Security: Access to a physical location such as a building or room.
Cyber Security: Access to an organization’s network through a biometrically authenticated login schema.
Transactional Security: Any monetary transaction which biometrically authenticates, accesses, and atomically debits or credits the user’s account.
1/28/09 Biometric Weekly Meetings (Spring 09) 17
Biometrics, Security, & You (cont.)
Why implement biometrics for security?
Convenience for users
Control for businesses
Inexpensive implementation
Price/Performance curves dropping
Saves money (i.e., no need for producing keys, etc.)
Accountability/Non-Repudiation Improved identification
(i.e., authentication, verification, impersonation)
Improved audit trail
Less administration (i.e., paperwork, cards, etc.)
More security (depends on implementation)
1/28/09 Biometric Weekly Meetings (Spring 09) 18
Biometrics, Security, & You (cont.)
Where can we find biometrics in use today?
Voter Registration
Driver Licensing
Border Control
Passport / VISA
Welfare / Government Insurance (WIC)
Criminal ID / Wanted Persons Lookup
Jail Management
Airports / Frequent Traveler / Passenger Tracking
Check Cashing eCommerce & Financial Services
Identity Theft ranked as the number one complaint for the fourth year in a row, with 635,000 reported instances in 2004, up 300 percent from last year's figure of 161,819
1/28/09 Biometric Weekly Meetings (Spring 09) 19
Biometrics, Security, & You (cont.)
Where can we find biometrics in use today?
At Walt Disney World biometric measurements are taken from the fingers of guests to ensure that the person's ticket is used by the same person from day to day
1/28/09
At your local Harris Teeter grocery chain. They use a finger geometry system for electronic checking.
Your local bank uses fingerprinting techniques for authentication.
Biometric Weekly Meetings (Spring 09) 20
Biometrics, Security, & You (cont.)
Examples from www.youtube.com
http://www.youtube.com/watch?v=R-EjqmxH_wQ http://www.youtube.com/watch?v=H2a0KYtG97E
1/28/09 Biometric Weekly Meetings (Spring 09) 21
Biometrics, Security, & You (cont.)
FBI has an initiative to collect biometric data on all citizens. This is a new initiative that flies in the face of citizens rights over security. More details can be found at: http://www.youtube.com/swf/l.swf?video_id=jADItD
HOHOA
What are your opinions of a pervasive use of biometrics for security purposes?
1/28/09 Biometric Weekly Meetings (Spring 09) 22
Biometrics, Security, & You (cont.)
What are the future trends for biometrics? Is the
1/28/09 Biometric Weekly Meetings (Spring 09) 23
Closing
Wrap-up
Biometrics are here to stay. We have grown accustomed to their use and utility within our communities.
Biometrics will continue to invade our daily lives.
Minority Report like capabilities are on the horizon and will be in place in the next decade or two.
Questions & Answers.
1/28/09 Biometric Weekly Meetings (Spring 09) 24
4.
5.
6.
References
1.
2.
3.
www.computer.org/itpro/homepage/Jan_Feb/securit y3.htm
www.veid.net/Applications/biometrics.htm
http://www.biometricscatalog.org/biometrics/Glossa ryDec2005.pdf
http://www.biometrics.gov/NSTC/Presentations.aspx
http://en.wikipedia.org/wiki/Biometric http://www.questbiometrics.com/
1/28/09 Biometric Weekly Meetings (Spring 09) 25