Cryptography-Symmetric
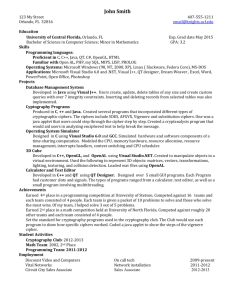
advertisement

Next: Cryptogrpahy. Corresponds with Chapter 2 of textbook. When not stated explicitly, the slide is based on material or has been provided by the textbook (Security in Computing by Pfleeger and Pfleeger. ISBN-10: 0132390779 ISBN-13: 978-0132390774 ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Summary • So far we looked at various threats, exploits and vulnerabilities to: – Application programs (buffer overflows, race conditions) – Applications on web (SQL injection, XSS and Hidden Parameter manipulation) – Physical security – Personnel security • NEXT: Securing computing infrastructures. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Remember: Security is holistic. • “Holistic” because it requires: – Technological security – security achieved using technological means. – Physical security, and, – Administrative security. • The next 7-8 weeks we will study various aspects of technological security. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Security is holistic. (2) • The next 7-8 weeks we will study various aspects of technological security. • Given that there are several technological security mechanisms our goals is to cover a wide-variety of those without going too much into depth. – Later courses: 445 and 455 will go into depth in some of those topics. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Overview of our coverage of technological security. • • • • Cryptography Application program security. OS security Network security. • Next: cryptography. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Encoding vs Encrypting - Encoding: represent information as data (in some specific format). - zip code, area code, ISBN, … - ASCII code, unicode, … - error codes … - class java.util.Date; program design Not about secrecy/security. - Encryption: secure data from attackers. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Why study cryptography? • Forms the foundation of many security mechanism. • Clearly the basis for network security and OS security. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Cryptography “ Many savages at the present day regard their names as vital parts of themselves, and therefore take great pains to conceal their real names, lest these should give to evil-disposed persons a handle by which to injure their owners.” —The Golden Bough, Sir James George Frazer (Quote obtained from: Cryptography and Network Security Slides by Dr. Lawrie Brown. Slides at:http://www.box.net/shared/h164at4gsc). ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Cryptography • Cryptography is not just encryption/decryption!. • Aspects of cryptography (we will study): – Two types of cryptography: • Symmetric key (also called private key or secret key) • Asymmetric key (also called public key cryptography) – In addition cryptography also includes another interesting mechanism: • Secure hash functions (also called message digests) – used for creating digital signatures and for assuring integrity of data. • These three types are used for achieving various things: • Encryption and decryption of messages. • Exchanging passwords or other secret information. • Creating digital signatures. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Cryptography and mathematics. • Cryptography is a course (or multiple courses) by itself! – Involves a lot of mathematics. – Cannot be covered as a one single topic easily. • Our focus and plan: – First: Encryption/Decryption using symmetric key cryptography – Next: Flavor of asymmetric key cryptography and its difference from symmetric key and – Then: secure hash functions and – Finally: using all of them for various tasks: confidentiality, integrity, authentication and non-repudiation. • Mathematics will be covered in ITEC 455 (network security). • Alternatively, read Chapter 12. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Encryption/Decryption. • What is encryption? • Decryption? In 5th grade, teacher placed me and my best friend on opposite side of room. We pass notes… but teacher could intercept! Solution: Captain Justice's Decoder Pencil. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Three parts to cryptography • Most cryptographic algorithms are used for: – Encryption: encoding a message so that its meaning is not obvious. – Decryption: reverse process • Crypt analysis: this is the key vulnerability and deals with breaking the encryption. Figure 2-1 Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. ITEC345 ©Australian MaterialDefence from slides from Pfleeger or Neil Daswani. Lawrie Brown, Institute derived (http://www.box.net/shared/h164at4gsc) Next: • Symmetric key cryptography: – This is what most layperson’s call as cryptographic algorithms. – Primarily used for encryption/decryption. – Also called: secret-key cryptography or private-key cryptography. Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown,© Australian Defence ITEC345 Material fromInstitute(http://www.box.net/shared/h164at4gsc) slides derived from Pfleeger or Neil Daswani. Notations we will use in discussing symmetric cryptography • Notations used to discuss symmetric cryptography: • • • • • M = message (plaintext) C = cipher text (the encrypted text) E = encryption function D = decryption function K = key (secret key, usually a number) E.g., C = E(M, K) (read this in English as: cipher text is generated by applying the encryption function on the message “M” and key “K”. Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute(http://www.box.net/shared/h164at4gsc) ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. What is symmetric cryptography? • In symmetric key cryptography: – The same secret key is used for both encryption and decryption. – The word “symmetric” comes from the above fact – same key for both functions. • E.g.,: If secret key is “K”, then: – C = E (M, K) and – M = D (C, K) (message is decryption of cipher text with the same key “K”. • E.g., (simple example) Caeser substitution cipher (next slide). Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Example of a symmetric encryption: Caeser Substitution Cipher • • • • Consider the following: M = MEET ME AT CENTRAL PARK C = PHHW PH DW FHQWUDO SDUN Secret key: (plaintext) (ciphertext) – Plain: ABCDEFGHIJKLMNOPQRSTUVWXYZ – Cipher:DEFGHIJKLMNOPQRSTUVWXYZABC • i.e., we replace each alphabet with another alphabet. E.g., character ‘A’ replaced by ‘D’, ‘B’ by ‘E’ etc.. • So what is the key? – The key is simply something like: “shift 3”, i.e., shift the alphabets to the right by 3 positions. Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute(http://www.box.net/shared/h164at4gsc) ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Caeser cipher. • Is the Caeser cipher secure? • If not, why not? – How easy is it to break Caeser cipher? – What process did you use? • E.g., what does this message mean? LWHF LV FRRO In particular, the security of a cryptographic algorithm is tested using: cryptanalysis. Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Institute.derived (http://www.box.net/shared/h164at4gsc) ITEC345 ©Australian MaterialDefence from slides from Pfleeger or Neil Daswani. Cryptanalysis • Used to test cryptographic techniques (e.g, how do we know how secure an encryption is?). – Two techniques are used: cryptanalysis and brute-force. • Cryptanalysis: Based on understanding the “nature” of the cryptographic algorithm. – Exploits characteristics of the algorithm to: • Attempt to deduce plaintext (OR) • Deduce the key being used. – Deducing key is more dangerous! • Brute-force: Try out all possible keys. Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. ITEC345 Material fromInstitute. slides(http://www.box.net/shared/h164at4gsc) derived from Pfleeger or Neil Daswani. Lawrie Brown, © Australian Defence Cryptanalysis of Caesar Cipher • In Caeser ciphper: • There are only 26 possible secret keys: – E.g., Shift right by 1, shift right by 2 etc.., – Attacker can easily try each key in turn • a brute force search • given ciphertext, just try all shifts of letters. • Hence, it is easy to break. © Dr. Lawrie Brown, Australian Defence Institute Notes based© onMaterial © William Stallings, Cryptography and Network Security.or Slides © Dr. ITEC345 from slides derived from Pfleeger NeilbyDaswani. Lawrie Brown, Australian Defence Institute. (http://www.box.net/shared/h164at4gsc) Classical Substitution Ciphers • Caeser cipher is a classic example of “substitution ciphers” • where letters of plaintext are replaced by other letters or by numbers or symbols • or if plaintext is viewed as a sequence of bits, then substitution involves replacing plaintext bit patterns with ciphertext bit patterns © Dr. Lawrie Brown, Australian Defence Institute Notes based © on Material © William Stallings, Cryptography andfrom Network Security. or Slides by Daswani. © Dr. ITEC345 from slides derived Pfleeger Neil Lawrie Brown, Australian Defence Institute. (http://www.box.net/shared/h164at4gsc) Classical Substitution Ciphers • Caeser cipher is an example of “substitution ciphers” • where letters of plaintext are replaced by other letters or by numbers or symbols • or if plaintext is viewed as a sequence of bits, then substitution involves replacing plaintext bit patterns with ciphertext bit patterns • In general, such substitution ciphers are not very secure. We will see why. © Dr. Lawrie Brown, Australian Defence Institute Notes based©onMaterial © William Stallings, Cryptography Network Security.or Slides © Dr. ITEC345 from slides derivedandfrom Pfleeger NeilbyDaswani. Lawrie Brown, Australian Defence Institute. (http://www.box.net/shared/h164at4gsc) Why substitution cipher is not secure (1) • We know Caeser cipher is not very secure because there are only 26 possible keys. • Alternative: a substitution cipher with several possible keys. – E.g., instead of using a single key “3”, use multiple keys “3”, “4”, “5”, where first character substituted by the third character, 2nd by the 4th and so on… © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. • 1William Stallings, Cryptography and Network Security Why substitution cipher is not secure (2). How secure is this? • instead of using a single key (e.g. 3), • use multiple keys. (For example: “3”, “4”, “5”, where first character is substituted by the third character, 2nd by the 4th and so on…) – E.g., • ‘A’ is substituted by ‘B’ (i.e., a character 1 place away), • ‘B’ is substituted by ‘D’ (i.e., a character 2 places away) • ‘C’ is substituted by ‘G’ (i.e., a character 5 places away). • How secure are such ciphers/mathematically? In other words, how many keys must you try before you break this cipher? Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Why substitution cipher is not secure (3). • For the problem on previous slide, there are 26! possible keys. Why? – First character ‘A’ can be substituted with any of the 26 characters. – Second character ‘B’ will now only have 25 other characters to substitute it (the one used for A cannot be used again – that was our intention). – Third character ‘C’ will now have only 24 other characters to substituted it. • Hence, we have: 26 * 25 * 24 *…. * 1 = 26! Possible secret keys. Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute. (http://www.box.net/shared/h164at4gsc) ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. How big is big? • Is 262 big? Is 26! big? • Current computers run at _____, which means _____ ops per sec. • 10 9 ops requires ~ ____ sec. • 1012 ops requires ~ ____ ____s. • 1015 ops requires ~ ____ ____s. • 1018 ops requires ~ ____ ____s. Age of universe? #particles in univ.? ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. How easy is it to break a substitution cipher? • So, brute-force means checking 26! ≈ 4 x 1026 keys • with so many keys, we might think it is secure • but would be WRONG! • Why? problem is language characteristics © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute(http://www.box.net/shared/h164at 4gsc) Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute. (http://www.box.net/shared/h164at4gsc) ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Why substitution cipher is not secure (3). Language Redundancy and Cryptanalysis • human languages are redundant • E.g., can you decipher this quote? “Fr lds to ngr. ngr lds to ht. Ht lds to sffrng.” • In English, – – – – - letters are not equally commonly used in English e is by far the most common letter then T,A,O,I,N,S,R (mnemonic: "creations") other letters are remarkably rare e.g. Z,J,K,Q,X Some letters disproportionally common at word-start; some words disproportionally common at document-start - After 'q', ____ • This makes text easier to guess! © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr.Defence Institute Australian ITEC345 © Material from slides derived fromBrown, Pfleeger or Neil Daswani. Lawrie Brown, Australian Defence Institute. (http://www.box.net/shared/h164at4gsc) English Letter Frequencies – shows that ‘e’ is most commonly used. Every use of ‘e’ in the text can easily be identified by the cryptanalyst. © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute. ITEC345 © Material from slides(http://www.box.net/shared/h164at4gsc) derived from Pfleeger or Neil Daswani. Using language characteristics to break substitution cipher • Example of using English characteristics: Consider the cipher text: wklv phvvdjh lv qrw wrr kdug wr euhdn ____ _______ __ ___ ___ ____ __ _____ Look for words such as “too” , “am” try to guess what each word may map in cipher text. This message has been enciphered with a 27-symbol alphabet: A – Z + blank character. © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence Institute Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Institute.derived (http://www.box.net/shared/h164at4gsc) ITEC345 ©Australian MaterialDefence from slides from Pfleeger or Neil Daswani. So how useful is substitution ciphers? • We have seen that substitution ciphers are not “by themselves” very secure. • So do they have any use at all? Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Institute.derived (http://www.box.net/shared/h164at4gsc) ITEC345 ©Australian MaterialDefence from slides from Pfleeger or Neil Daswani. So how useful are substitution ciphers? • Not in practice. But conceptually: • Principle of timeliness in security: a security measure must be strong enough to keep out the attacker only for the life of the data. • E.g., if Corp.HQ e-mails quarterly earnings to a branch office 5min before the public shareholder announcment, a cipher that takes longer than 5 minutes to break is sufficient! Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Institute.derived (http://www.box.net/shared/h164at4gsc) ITEC345 ©Australian MaterialDefence from slides from Pfleeger or Neil Daswani. What can make a substitution cipher better? • So, our next goal is to make substitution ciphers more secure? • How? Any ideas? ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Making substitution cipher more effective • Some ideas: - shift each letter… but change the shift-amount at each step! – One – time pad. – Using transposition (permutations). ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. One time pad • What if each letter in the message were encrypted with a different key? • E.g. shift by 4, then by 5, then by 6, …: E("aaa",4) = "efg" • Instead of adding one to the shift, add 7? • Or, multiply-by-5-then-add-7? • Or, have the next shift depend on the current shift and the letter just enciphered! (Enigma) Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Institute.derived (http://www.box.net/shared/h164at4gsc) ITEC345 ©Australian MaterialDefence from slides from Pfleeger or Neil Daswani. One time pad • The "5k+7 (mod 26)" sequence is a simple pseudo-random-number generator: 1, 12, 15, 4, … • What if we had a truly random sequence, as our key? • Advantage: cannot possibly break it any part of it, so long as key is truly random. • This is the idea behind a One-Time Pad • Unbreakable … if you never re-use the pad! Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Institute.derived (http://www.box.net/shared/h164at4gsc) ITEC345 ©Australian MaterialDefence from slides from Pfleeger or Neil Daswani. Other substitution ciphers… • Several others including: – Book ciphers. • Next: an alternative to substitution: transposition ciphers. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Transposition cipher … • Based on what you learnt so far, What is the biggest weakness of a substitution cipher – in other words what makes it easy to break? ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Transposition (or permutation) cipher … • Based on what you learnt so far, What is the biggest weakness of a substitution cipher – in other words what makes it easy to break? Substitution ciphers might preserve (language) patterns in the input. Transposition ciphers aim to break the patterns. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Two terms: confusion and diffusion. • Substitution ciphers create confusion: characters in the cipher text are not what they are. • Transposition ciphers: create diffusion – they spread the characters around breaking patterns. In other words they create “jumbles”. Notes based on © William Stallings, Cryptography and Network Security. Slides by © Dr. Lawrie Brown, Australian Defence ITEC345 © Material fromInstitute. slides(http://www.box.net/shared/h164at4gsc) derived from Pfleeger or Neil Daswani. Transposition cipher example: columnar cipher • In columnar transposition, words are basically being jumbled. Figure 2-4 Columnar Transposition. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Transposition cipher: columnar cipher • Example: To encrypt: This is ITEC, we can use the following transposition: T h i s I s I T E C Read down the columns to get cipher text: TssTh EiIIC ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Summary so far … • We have seen substitution and transposition ciphers. • These are trivial – though they illustrate the concepts. • Next: we will see how a mixture of these ciphers are used in commercial encryption/decryption algorithms: DES and AES. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. DES encryption. • Data Encryption Standard. • Selected by the National Bureau of Standards in 1976. • Symmetric encryption – used 56 bit keys. • Uses a mix of substitution and transposition (permutation) ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Slides image © Neil Daswani et al, , Foundations of Security: What every programmer needs to know. ISBN-13: 978-1590597842 High level view of DES • This is one round in DES. (16 such rounds are used for encrypting.) This is also called Feistal network Called S-boxes Called Permute Boxes. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Parts of DES: S-box (Substitution Box) • n bits input; m bits output (n x m S-box) • output is functionally determined by input • Ex: If input = 011001, and n bits (say) output = 1001 S-box • 2n possible inputs m bits • 2m possible outputs • Exercise: how many possible distinct substitution boxes could you build? Slide © Neil Daswani et al, , • In DES: S-boxes fixed. Foundations of Security: What © Neil Daswani every programmer needs to know. ISBN-13: 978-1590597842 ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Parts of a DES: Permute Functions • Permutation Functions: changes order of bits Slides image © Neil Daswani et al, , Foundations of Security: What every programmer needs to know. ISBN-13: 978-1590597842 – Example: P(b0b1b2)=b1b2b0 – P(101)=011 0 1 • Expansion Permutation: changes order, and re-uses bits more than once – Example: P’(b0b1b2)=b1b2b1b0b2 – P’(101)=01011 0 © Neil Daswani ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. 1 2 2 DES • The "sub"keys used in each of the 16 rounds are derived from the original key. • To de-crypt: Just apply the subkeys in opposite order • This is important practically: same hardware can be used. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Key Strength • Just search every possibility to break the key? • 256 is possible to brute-force, though 57bits is twice as hard; 58bits is 4x harder; 264 is 256x bigger than 256. • What about with 128-bit keys? 2128 possible keys – too many to brute-force! • But I still have my hardware for 56-bit key DES. Idea: encrypt twice, with k1 then k2: this is equivalent to using a 2x56 = 128 bit key. © Neil Daswani Slide © Neil Daswani et al, , Foundations of Security: What every programmer needs to know. ISBN-13: 978-1590597842 ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. 3DES: Triple DES • Do DES 3 times with 3 different keys • E = f( f-1( f( M ,k1) ,k2) ,k3) where f = DES • Keying options (best to worst): choose – k1 ≠ k2 ≠ k3: – k1 = k3: – k1 = k2 = k3: © Neil Daswani 168-bit (192-bit) 112-bit (128-bit) 56-bit (64-bit) Slide © Neil Daswani et al, , Foundations of Security: What every programmer needs to know. ISBN-13: 978-1590597842 ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. © Neil Daswani Some things to note • Security depends on keys… algorithms are public! • Every additional bit adds twice as many possibilities to have to search. – Why? All previous keys: prepend 0; prepend 1. • For 128-bit key, need to “attack” mathematical properties of encryption Slide © Neil Daswani et al, , Foundations of Security: What algorithm every programmer needs to know. ISBN-13: 978-1590597842 • Hint: when encrypting: don’t invent your own encryption algorithm! Use existing, vetted ones. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. © Neil Daswani et al, Foundations of Security: What every programmer needs to know. ISBN-13: 978-1590597842 AES (Rijndael) • AES: Advanced Encryption Standard: Rijndael ("Rein doll") • Invented by 2 cryptographers from Belgium • Selected by NIST from 15 competitors • Selection Criteria: Security, Cost (speed, memory), Implementation Considerations (hw,sw) • Key size / Block size: 128, 192, or 256 bits • 10, 12, or 14 rounds depending upon key/block size • Has S-Boxes and XORs, but no Feistel network © William Stallings, Cryptography and Network Security ITEC345 © Material from slides derived from Pfleeger or Neil Daswani. Next: • Asymmetric ciphers. ITEC345 © Material from slides derived from Pfleeger or Neil Daswani.





![[#OPENDS-1029] Update daily build mail subject to indicate](http://s3.studylib.net/store/data/007734190_2-d66144ca725a9119b45ca78b6568f0a8-300x300.png)