Security Services
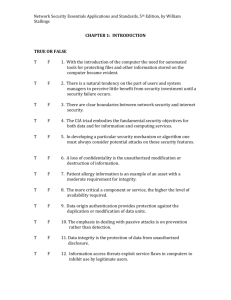
advertisement
Introduction X.800 – OSI Security Services • Security Service – a service provided by a protocol layer of communicating open systems, which ensures adequate security of the systems or of data transfers • RFC 2828 – a processing or communication service that is provided by a system to give a specific kind of protection to system resources; security services implement security policies and are implemented by security mechanisms. Security Services • Authentication – assurance that the communicating entity is who they say they are • Access Control – prevent the unauthorized access to some system resource – Who can access – Under what conditions – What they are allowed to do • Data Confidentiality – protection of data from unauthorized disclosure • Data Integrity – insure that data received is exactely what was sent • Nonrepudiation – protection from denial by one of the entities involved in a communication of having participated in all or part of the communication Authentication • Peer Entity Authentication – in a connection based environment; provide confidence in the identity of a connecting entity – Logging in with a password – Gaining access via biological identity verification • DNA identification, retinal scan, finger/hand print identification – Access via audio voice identification • Data Origin Authentication – in a connectionless environment; provide assurance that the source of received data is as claimed – Corroborates the source of the data – Does not proved assurance against duplicate or modified data Access Control • This service provides protection against unauthorized use of resources accessible via OSI. These may be OSI or nonOSI resources accessed via OSI protocols. This protection service may be applied to various types of access to a resource or to all accesses to a resource – e.g., the use of a communications resource; the reading, the writing, or the deletion of an information resource; the execution of a processing resource Data Confidentiality • Connection Confidentiality – Protection of all user data on a connection • Connectionless Confidentiality – Protection of all data within a single data block • Selective-Field Confidentiality – Insure confidentiality of selected fields with within the user data on a connection or in a single data block connection • Traffic-Flow Confidentiality – Protection of information that might be derived by observing the traffic flow patterns Data Integrity • Connection Integrity with Recovery – Detect any modification of stream data or replay of data and retry; • Connection Integrity without Recovery – Detect any modification and report it, no retry…continue on • Selective-Field Connection Integrity – Same except for selected fields • Connectionless Integrity – Detect modifications in fixed block connectionless data, may provide replay detection and protection • Selective-Field Connectionless Integrity – Same, except for selected fields • Total stream protection would encompass all of the above and is probably the best strategy Nonrepudiation • Nonrepudiation, Origin – Proof that the message was sent by the specified party • Nonrepudiation, Destination – Proof that the message was received by the specified party Security Mechanisms (X.800) • • • • • • • Encipherment – algorithmic/mathematical conversion Digital Signature – appending a secret signature Access Control Access Control Data Integrity Authentication Exchange Traffic Padding – appending extra chars to foil traffic analysis techniques • Routing Control – selection of secure routeds through the network • Notarization – use a trused 3rd party (like a notary public) Other Security Mechanisms (non X.800) • Trusted Functionality – That which is perceived to be true by some criteria (policy) • Security Label – The marking of (bound to) a resource that names or desiginates the security attributes of the resource • Event Detection – Intrusion detection – Detection of specific hacks (detector hardware) – Too many log in attempts • Security Audit Trail – Logging of all system events • Security Recovery – Recovery based on requests from security mechanisms and/or event handling. Network Security Model Trusted 3rd Party M F(s) M’ Info Channel M’ s F(s) s Opponent F(s)-some function that mutates M into M’ based on s F(s) – some function that reverses the mutation of M’ back into M M Internet Organizations • Internet Architecture Board (IAB) – responsible for the overall design of the Internet, provides guidance to IETF • Internet Engineering Task Force (IETF) – protocol engineering and development of the Internet – Working groups chartered by IETF do actual development work • Internet Draft, RFC, Standard • 8 areas – General, Applications, Internet, Operations and management, Routing, Security, Transport, User Services – IETF responsible for actual publishing • Internet Engineering Steering Group (IESG) – responsible for technical management if IETF activities and the Internet Standards process RFC Publication Process Internet Draft Proposed Standard Best Current Practice Experimental Draft Standard Internet Standard Historic Informational