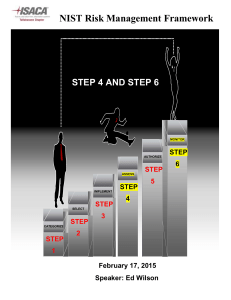
NIST - ISACA Denver Chapter
advertisement

Defending the United States in the Digital Age A Risk Management Framework to Improve Information Security ISACA Denver Chapter Annual General Meeting April 19, 2012 Dr. Ron Ross Computer Security Division Information Technology Laboratory NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 1 Part 1 The Fundamentals NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 2 Information technology is our greatest strength and at the same time, our greatest weakness… NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 3 The Perfect Storm Explosive growth and aggressive use of information technology. Proliferation of information systems and networks with virtually unlimited connectivity. Increasing sophistication of threat including exponential growth rate in malware (malicious code). Resulting in an increasing number of penetrations of information systems in the public and private sectors… NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 4 The Threat Situation Continuing serious cyber attacks on public and private sector information systems targeting key operations, assets, and individuals… Attacks are organized, disciplined, aggressive, and well resourced; many are extremely sophisticated. Adversaries are nation states, terrorist groups, criminals, hackers, and individuals or groups with hostile intentions. Effective deployment of malware causing significant exfiltration of sensitive information (e.g., intellectual property). Potential for disruption of critical systems and services. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 5 Advanced Persistent Threat An adversary that — Possesses significant levels of expertise / resources. Creates opportunities to achieve its objectives by using multiple attack vectors (e.g., cyber, physical, deception). Establishes footholds within IT infrastructure of targeted organizations— To exfiltrate information. Undermine / impede critical aspects of a mission, program, or organization. Position itself to carry out these objectives in the future. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 6 Unconventional Threats to Security Connectivity Complexity NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY Culture 7 “Red Zone” Security NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 8 The Present We have our heads under the hood looking at every last detail in the engine compartment—that is, pursuing an endless number of information system vulnerabilities… NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 9 Instead of trying to figure out what type of car we need— that is, what level of information system resiliency is necessary to effectively support our core missions and business functions… NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 10 Active Cyber Defenses – The Future Develop risk-aware mission and business processes. Develop and implement enterprise architectures with embedded information security architectures that support organizational mission/business processes. Use information technology wisely considering current threat landscape (capabilities, intent, and targeting). Develop and implement robust continuous monitoring programs. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 11 Cyber Defense Vision Core Principles Strong, resilient, penetration-resistant information systems supporting core missions / mission processes. Ongoing monitoring of the security state of information systems and environments of operation. Continuous improvement in security controls. Flexibility and agility in cyber security and risk management activities. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 12 Core Concepts IT Products and Systems Modularity. Layering. Monitoring. To achieve defense-in-depth and defense-in-breadth. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 13 Dual Protection Strategies Boundary Protection Primary Consideration: Penetration Resistance Adversary Location: Outside the Defensive Perimeter Objective: Repelling the Attack Agile Defense Primary Consideration: Information System Resilience Adversary Location: Inside the Defensive Perimeter Objective: Operating while under Attack NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 14 Agile Defense Boundary protection is a necessary but not sufficient condition for Agile Defense Examples of Agile Defense measures: Compartmentalization and segregation of critical assets Targeted allocation of security controls Virtualization and obfuscation techniques Encryption of data at rest Limiting of privileges Routine reconstitution to known secure state Bottom Line: Limit damage of hostile attack while operating in a (potentially) degraded mode… NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 15 Enterprise-Wide Risk Management Multi-tiered Risk Management Approach Implemented by the Risk Executive Function Enterprise Architecture and SDLC Focus Flexible and Agile Implementation STRATEGIC RISK FOCUS TIER 1 Organization (Governance) TIER 2 Mission / Business Process (Information and Information Flows) TIER 3 TACTICAL RISK FOCUS Information System (Environment of Operation) NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 16 Characteristics of Risk-Based Approaches (1 of 2) Integrates information security more closely into the enterprise architecture and system life cycle. Promotes near real-time risk management and ongoing system authorization through the implementation of robust continuous monitoring processes. Provides senior leaders with necessary information to make risk-based decisions regarding information systems supporting their core missions and business functions. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 17 Characteristics of Risk-Based Approaches (2 of 2) Links risk management activities at the organization, mission, and information system levels through a risk executive (function). Establishes responsibility and accountability for security controls deployed within information systems. Encourages the use of automation to increase consistency, effectiveness, and timeliness of security control implementation. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 18 Risk Management Process Risk Framing Risk Framing Assess Respond Risk Risk Framing Monitor NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY Risk Framing 19 Architectural and Engineering Approach Organization risk management strategy Mission / Business Process Mission / Business Process Mission / Business Process informs informs enterprise architecture (Reference Models, Segment Architecture, Solution Architecture) information security architecture (Security Requirement and Control Allocation) informs informs INFORMATION SYSTEM INFORMATION SYSTEM INFORMATION SYSTEM Environments of Operation NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 20 Enterprise Architecture Consolidation. Optimization. Standardization. Wise use of information technology… Build a leaner, more streamlined IT infrastructure that facilitates more effective deployment of security controls to organizational information systems and environments of operation. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 21 Risk Management Framework Starting Point CATEGORIZE Information System MONITOR Security Controls Continuously track changes to the information system that may affect security controls and reassess control effectiveness. Define criticality/sensitivity of information system according to potential worst-case, adverse impact to mission/business. Security Life Cycle SELECT Security Controls Select baseline security controls; apply tailoring guidance and supplement controls as needed based on risk assessment. AUTHORIZE IMPLEMENT Information System Security Controls Determine risk to organizational operations and assets, individuals, other organizations, and the Nation; if acceptable, authorize operation. Implement security controls within enterprise architecture using sound systems engineering practices; apply security configuration settings. ASSESS Security Controls Determine security control effectiveness (i.e., controls implemented correctly, operating as intended, meeting security requirements for information system). NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 22 Defense-in-Depth Links in the Security Chain: Management, Operational, and Technical Controls Risk assessment Security planning, policies, procedures Configuration management and control Contingency planning Incident response planning Security awareness and training Security in acquisitions Physical security Personnel security Security assessments and authorization Continuous monitoring Access control mechanisms Identification & authentication mechanisms (Biometrics, tokens, passwords) Audit mechanisms Encryption mechanisms Boundary and network protection devices (Firewalls, guards, routers, gateways) Intrusion protection/detection systems Security configuration settings Anti-viral, anti-spyware, anti-spam software Smart cards Adversaries attack the weakest link…where is yours? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 23 Why Continuous Monitoring? Determine effectiveness of risk mitigation measures. Identify changes to information systems and environments of operation. Verify compliance. Bottom Line: Increase situational awareness to help determine risk to organizational operations and assets, individuals, other organizations, and the Nation. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 24 Assurance and Trustworthiness TRUSTWORTHINESS Information Systems Security Capability Prevent Attacks, Deter Attacks, Limit Harm from Attacks, Respond to Attacks, Recover from Attacks FUNCTIONALITY ASSURANCE Security Features, Functions, Services, Mechanisms, Procedures Measures of Confidence Security Strength Correctness, Completeness, Resistance to Tamper and Bypass Development Actions Operational Actions Security Evidence Development Artifacts, Test/Evaluation Results, Flaw Reports Enables Understanding of Security Capability NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 25 Unified Information Security Framework The Generalized Model Unique Information Security Requirements Intelligence Community Department of Defense The “Delta” Common Information Security Requirements Federal Civil Agencies C N S S Private Sector State/Local Govt Foundational Set of Information Security Standards and Guidance • • • • • Risk management (organization, mission, information system) Security categorization (information criticality/sensitivity) Security controls (safeguards and countermeasures) Security assessment procedures Security authorization process National security and non national security information systems NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 26 Joint Task Force Transformation Initiative A Broad-Based Partnership — National Institute of Standards and Technology Department of Defense Intelligence Community Office of the Director of National Intelligence 17 U.S. Intelligence Agencies Committee on National Security Systems NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 27 Joint Task Force Transformation Initiative Core Risk Management Publications NIST Special Publication 800-39 Managing Information Security Risk: Organization, Mission, and Information System View Completed NIST Special Publication 800-37, Revision 1 Applying the Risk Management Framework to Federal Information Systems: A Security Lifecycle Approach Completed NIST Special Publication 800-30, Revision 1 Guide for Conducting Risk Assessments Projected September 2011 (Public Draft) NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 28 Joint Task Force Transformation Initiative Core Risk Management Publications NIST Special Publication 800-53, Revision 3 Recommended Security Controls for Federal Information Systems and Organizations Completed NIST Special Publication 800-53A, Revision 1 Guide for Assessing the Security Controls in Federal Information Systems and Organizations: Building Effective Assessment Plans NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY Completed 29 Focus Areas — 2012 and Beyond Risk Assessment Guideline Systems and Security Engineering Guideline Update to NIST Special Publication 800-53, Revision 4 Insider Threats Application Security Supply Chain Security Advanced Persistent Threats Industrial / Process Control Systems Mobile Devices, Cloud Computing Privacy Controls NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 30 Part 2 The Risk Management Framework NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 31 Risk Management Framework Starting Point CATEGORIZE Information System MONITOR Security Controls Continuously track changes to the information system that may affect security controls and reassess control effectiveness. Define criticality/sensitivity of information system according to potential worst-case, adverse impact to mission/business. Security Life Cycle SELECT Security Controls Select baseline security controls; apply tailoring guidance and supplement controls as needed based on risk assessment. AUTHORIZE IMPLEMENT Information System Security Controls Determine risk to organizational operations and assets, individuals, other organizations, and the Nation; if acceptable, authorize operation. Implement security controls within enterprise architecture using sound systems engineering practices; apply security configuration settings. ASSESS Security Controls Determine security control effectiveness (i.e., controls implemented correctly, operating as intended, meeting security requirements for information system). NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 32 Security Categorization Example: An Organizational Information System Guidance for Mapping Types of Information and Information Systems to FIPS 199 Security Categories SP 800-60 FIPS 199 LOW MODERATE HIGH Confidentiality The loss of confidentiality could be expected to have a limited adverse effect on organizational operations, organizational assets, or individuals. The loss of confidentiality could be expected to have a serious adverse effect on organizational operations, organizational assets, or individuals. The loss of confidentiality could be expected to have a severe or catastrophic adverse effect on organizational operations, organizational assets, or individuals. Integrity The loss of integrity could be expected to have a limited adverse effect on organizational operations, organizational assets, or individuals. The loss of integrity could be expected to have a serious adverse effect on organizational operations, organizational assets, or individuals. The loss of integrity could be expected to have a severe or catastrophic adverse effect on organizational operations, organizational assets, or individuals. Availability The loss of availability could be expected to have a limited adverse effect on organizational operations, organizational assets, or individuals. The loss of availability could be expected to have a serious adverse effect on organizational operations, organizational assets, or individuals. The loss of availability could be expected to have a severe or catastrophic adverse effect on organizational operations, organizational assets, or individuals. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY Baseline Security Controls for High Impact Systems 33 Security Controls The management, operational, and technical safeguards or countermeasures prescribed for an information system to protect the confidentiality, integrity, and availability of the system and its information. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 3434 Security Control Baselines (Appendix D) Master Security Control Catalog Complete Set of Security Controls and Control Enhancements Minimum Security Controls Minimum Security Controls Minimum Security Controls Low Impact Information Systems Moderate Impact Information Systems High Impact Information Systems Baseline #1 Baseline #2 Baseline #3 Selection of a subset of security controls from the master catalog— consisting of basic level controls Builds on low baseline. Selection of a subset of controls from the master catalog—basic level controls, additional controls, and control enhancements Builds on moderate baseline. Selection of a subset of controls from the master catalog—basic level controls, additional controls, and control enhancements NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 35 35 Tailoring Security Controls Scoping, Parameterization, and Compensating Controls Baseline Security Controls Baseline Security Controls Baseline Security Controls Low Impact Information Systems Moderate Impact Information Systems High Impact Information Systems Low Baseline Moderate Baseline High Baseline Tailored Security Controls Tailored Security Controls Tailored Security Controls Organization #1 Organization #2 Organization #3 Operational Environment #1 Operational Environment #2 Operational Environment #3 Cost effective, risk-based approach to achieving adequate information security… NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 36 36 Expanded Tailoring Guidance (1 of 2) Identifying and designating common controls in initial security control baselines. Applying scoping considerations to the remaining baseline security controls. Selecting compensating security controls, if needed. Assigning specific values to organization-defined security control parameters via explicit assignment and selection statements. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 37 Expanded Tailoring Guidance (2 of 2) Supplementing baselines with additional security controls and control enhancements, if needed. • Providing additional specification information for control implementation. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 38 Tailoring the Baseline Tailoring Guidance INITIAL SECURITY CONTROL BASELINE (Low, Mod, High) Identifying and Designating Common Controls Applying Scoping Considerations Selecting Compensating Controls Assigning Security Control Parameter Values Supplementing Baseline Security Controls Providing Additional Specification Information for Implementation Before Tailoring TAILORED SECURITY CONTROL BASELINE (Low, Mod, High) After Tailoring Assessment of Organizational Risk DOCUMENT SECURITY CONTROL DECISIONS Rationale that the agreed-upon set of security controls for the information system provide adequate protection of organizational operations and assets, individuals, other organizations, and the Nation. Document risk management decisions made during the tailoring process to provide information necessary for authorizing officials to make risk-based authorization decisions. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 39 Common Risk Management Process NIST Special Publication 800-37, Revision 1 Guide for Applying the Risk Management Framework to Federal Information Systems: A Security Life Cycle Approach Developed by Joint Task Force Transformation Initiative Working Group Office of the Director of National Intelligence Department of Defense Committee on National Security Systems National Institute of Standards and Technology Final Public Draft (November 2009) Final Publication (February 2010) NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 40 Purpose Provide guidelines for applying the Risk Management Framework to federal information systems— To ensure that managing risk from information systems is consistent with mission/business objectives and the overall risk strategy established by the senior leadership through the risk executive (function). To ensure that information security requirements, including necessary security controls, are integrated into the organization’s enterprise architecture and system development life cycle processes. To support consistent, well-informed, and ongoing security authorization decisions (through continuous monitoring), transparency of security and risk-related information, and reciprocity of authorization results. To achieve more secure information and information systems through the implementation of appropriate risk mitigation strategies. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 41 Applicability Federal information systems other than those systems designated as national security systems as defined in 44 U.S.C., Section 3542. National security systems with the approval of federal officials exercising policy authority over such systems. State, local, and tribal governments, as well as private sector organizations are encouraged to consider using these guidelines, as appropriate. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 42 Target Audience Individuals with mission/business ownership responsibilities or fiduciary responsibilities. Individuals with information system development and integration responsibilities. Individuals with information system and/or security management/oversight responsibilities. Individuals with information system and security control assessment and monitoring responsibilities. Individuals with information security implementation and operational responsibilities. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 43 Mainstreaming Information Security Information security requirements must be considered first order requirements and are critical to mission and business success. An effective organization-wide information security program helps to ensure that security considerations are specifically addressed in the enterprise architecture for the organization and are integrated early into the system development life cycle. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 44 System Development Life Cycle (1 of 2) RMF steps are carried out within the five phases of the SDLC. System Initiation Phase System Development / Acquisition Phase System Implementation Phase System Operation / Maintenance Phase System Disposal Phase Flexibility on types of SDLC models employed by the organization (e.g., spiral, waterfall, agile development). NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 45 System Development Life Cycle (2 of 2) Integrating information security requirements into the SDLC provides the most efficient and cost-effective method for an organization to ensure that: Cost, schedule, and performance requirements are satisfied. Missions and business operations supported by the information system are adequately protected. Security-related activities are carried out as early as possible and not repeated unnecessarily. Risk management activities are not isolated or decoupled from the management processes employed to develop, implement, operate, and maintain the information system. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 46 Applying the Risk Management Framework to Information Systems Output from Automated Support Tools Risk Executive (Function) Inputs SECURITY PLAN including updated Risk Assessment Near Real Time Security Status Information SECURITY ASSESSMENT REPORT PLAN OF ACTION AND MILESTONES Authorization Package INFORMATION SYSTEM CATEGORIZE Information System MONITOR Security Controls Risk Management Framework SELECT Security Controls AUTHORIZE IMPLEMENT Information System Security Controls ASSESS Security Controls NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 47 Information System Boundaries Define the scope of protection for information systems (i.e., what the organization agrees to protect under its direct control or within the scope of its responsibilities). Include the people, processes, and technologies that are part of the systems supporting the organization’s missions and business processes. Need to be established before information system security categorization and the development of security plans. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 48 Large and Complex Systems From a centralized development, implementation, and operations perspective— The organization examines the purpose of the information system and considers the feasibility of decomposing the complex system into more manageable components, or subsystems. From a distributed development, implementation, and operations perspective— The organization recognizes that multiple entities, possibly operating under different policies, may be contributing to the development, implementation, and/or operations of the subsystems that comprise the overall information system. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 49 Large and Complex Systems (Including System of Systems) ORGANIZATIONAL INFORMATION SYSTEM SUBSYSTEM SUBSYSTEM SUBSYSTEM LAN ONE GUARD LAN TWO DYNAMIC SUBSYSTEM (Sub) System Boundary SUBSYSTEM GUARD / GATEWAY DYNAMIC EXTERNAL SUBSYSTEM DYNAMIC SUBSYSTEM STATIC EXTERNAL SUBSYSTEM - Security plan reflects information system decomposition with security controls assigned to each subsystem component. - Security assessment procedures tailored for the security controls in each subsystem component and for the combined system level. - Security control assessment performed on each subsystem component and on system-level controls not covered by subsystem security control assessments. - Security authorization conducted on the information system as a whole. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 50 Security Control Allocation Security controls are defined to be system-specific, hybrid, or common. Security controls are allocated to specific components of organizational information systems as systemspecific, hybrid, or common controls. Security control allocations are consistent with the organization’s enterprise architecture and information security architecture. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 51 Security Control Accountability RISK EXECUTIVE FUNCTION Security Assessment Report INFORMATION SYSTEM INFORMATION SYSTEM System-specific Controls System-specific Controls Plan of Action and Milestones Security Plan Security Assessment Report Plan of Action and Milestones RISK MANAGEMENT FRAMEWORK (RMF) COMMON CONTROLS Security Controls Inherited by Organizational Information Systems Security Plan Security Assessment Report Ongoing Authorization Decisions Security Plan Hybrid Controls Tactical Risk Management Focus Core Missions / Business Processes Security Requirements Policy Guidance Hybrid Controls Strategic Risk Management Focus Ongoing Authorization Decisions Organization-wide Risk Governance and Oversight Top Level Risk Management Strategy Informs Operational Elements Enterprise-Wide Plan of Action and Milestones Ongoing Authorization Decisions NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 52 The Process NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 53 RMF Task Structure (1 of 2) Task Section Describes the specific RMF task within the appropriate step in the Risk Management Framework. Primary Responsibility Section Lists the individual or group within the organization having primary responsibility for executing the RMF task. Supporting Roles Section Lists the supporting roles within the organization that may be necessary to help the individual or group with primary responsibility for executing the RMF task. SDLC Phase Section Lists the particular phase of the SDLC when the RMF task is typically executed. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 54 RMF Task Structure (2 of 2) Supplemental Guidance Section Provides supplemental guidance for executing the RMF task including additional information from relevant supporting security policies, instructions, standards, and guidelines. References Section Provides general references to NIST security standards and guidelines that should be consulted for additional information with regard to executing the RMF task. Provides specific national security system references to CNSS policies and instructions that should be consulted for additional information with regard to executing the RMF task when the general references are either insufficient or inappropriate for national security application. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 55 RMF Step 1 Tasks Categorize Information System Security Categorization Task 1-1: Categorize the information system and document the results of the security categorization in the security plan. Information System Description Task 1-2: Describe the information system (including system boundary) and document the description in the security plan. Information System Registration Task 1-3: Register the information system with appropriate organizational program/management offices. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 56 Milestone Checkpoint #1 Has the organization completed a security categorization of the information system including the information to be processed, stored, and transmitted by the system? Are the results of the security categorization process for the information system consistent with the organization’s enterprise architecture and commitment to protecting organizational mission/business processes? Do the results of the security categorization process reflect the organization’s risk management strategy? Has the organization adequately described the characteristics of the information system? Has the organization registered the information system for purposes of management, accountability, and oversight? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 57 RMF Step 2 Tasks Select Security Controls Common Control Identification Task 2-1: Identify the security controls that are provided by the organization as common controls for organizational information systems and document the controls in a security plan (or equivalent document). Security Control Selection Task 2-2: Select the security controls for the information system and document the controls in the security plan. Monitoring Strategy Task 2-3: Develop a strategy for the continuous monitoring of security control effectiveness and any proposed/actual changes to the information system and its environment of operation. Security Plan Approval Task 2-4: Review and approve the security plan. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 58 Milestone Checkpoint #2 (1 of 3) Has the organization allocated all security controls to the information system as system-specific, hybrid, or common controls? Has the organization used its risk assessment (either formal or informal) to inform and guide the security control selection process? Has the organization identified authorizing officials for the information system and all common controls inherited by the system? Has the organization tailored and supplemented the baseline security controls to ensure that the controls, if implemented, adequately mitigate risks to organizational operations and assets, individuals, other organizations, and the Nation? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 59 Milestone Checkpoint #2 (2 of 3) Has the organization addressed minimum assurance requirements for the security controls employed within and inherited by the information system? Has the organization consulted information system owners when identifying common controls to ensure that the security capability provided by the inherited controls is sufficient to deliver adequate protection? Has the organization supplemented the common controls with systemspecific or hybrid controls when the security control baselines of the common controls are less than those of the information system inheriting the controls? Has the organization documented the common controls inherited from external providers? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 60 Milestone Checkpoint #2 (3 of 3) Has the organization developed a continuous monitoring strategy for the information system that reflects the organizational risk management strategy and commitment to protecting critical missions and business functions? Have appropriate organizational officials approved security plans containing system-specific, hybrid, and common controls? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 61 RMF Step 3 Tasks Implement Security Controls Security Control Implementation Task 3-1: Implement the security controls specified in the security plan. Security Control Documentation Task 3-2: Document the security control implementation, as appropriate, in the security plan, providing a functional description of the control implementation (including planned inputs, expected behavior, and expected outputs). NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 62 Milestone Checkpoint #3 (1 of 2) Has the organization allocated security controls as system-specific, hybrid, or common controls consistent with the enterprise architecture and information security architecture? Has the organization demonstrated the use of sound information system and security engineering methodologies in integrating information technology products into the information system and in implementing the security controls contained in the security plan? Has the organization documented how common controls inherited by organizational information systems have been implemented? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 63 Milestone Checkpoint #3 (2 of 2) Has the organization documented how system-specific and hybrid security controls have been implemented within the information system taking into account specific technologies and platform dependencies? Has the organization taken into account the minimum assurance requirements when implementing security controls? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 64 RMF Step 4 Tasks Assess Security Controls Assessment Preparation Task 4-1: Develop, review, and approve a plan to assess the security controls. Security Control Assessment Task 4-2: Assess the security controls in accordance with the assessment procedures defined in the security assessment plan. Security Assessment Report Task 4-3: Prepare the security assessment report documenting the issues, findings, and recommendations from the security control assessment. Remediation Actions Task 4-4: Conduct initial remediation actions on security controls based on the findings and recommendations of the security assessment report and reassess remediated control(s), as appropriate.. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 65 Milestone Checkpoint #4 (1 of 2) Has the organization developed a comprehensive plan to assess the security controls employed within or inherited by the information system? Was the assessment plan reviewed and approved by appropriate organizational officials? Has the organization considered the appropriate level of assessor independence for the security control assessment? Has the organization provided all of the essential supporting assessmentrelated materials needed by the assessor(s) to conduct an effective security control assessment? Has the organization examined opportunities for reusing assessment results from previous assessments or from other sources? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 66 Milestone Checkpoint #4 (2 of 2) Did the assessor(s) complete the security control assessment in accordance with the stated assessment plan? Did the organization receive the completed security assessment report with appropriate findings and recommendations from the assessors)? Did the organization take the necessary remediation actions to address the most important weaknesses and deficiencies in the information system and its environment of operation based on the findings and recommendations in the security assessment report? Did the organization update appropriate security plans based on the findings and recommendations in the security assessment report and any subsequent changes to the information system and its environment of operation? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 67 RMF Step 5 Tasks Authorize Information System Plan of Action and Milestones Task 5-1: Prepare the plan of action and milestones based on the findings and recommendations of the security assessment report excluding any remediation actions taken. Security Authorization Package Task 5-2: Assemble the security authorization package and submit the package to the authorizing official for adjudication. Risk Determination Task 5-3: Determine the risk to organizational operations (including mission, functions, image, or reputation), organizational assets, individuals, other organizations, or the Nation. Risk Acceptance Task 5-4: Determine if the risk to organizational operations, organizational assets, individuals, other organizations, or the Nation is acceptable. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 68 Milestone Checkpoint #5 (1 of 2) Did the organization take the necessary remediation actions to address the most important weaknesses and deficiencies in the information system and its environment of operation based on the findings and recommendations in the security assessment report? Did the organization develop an appropriate authorization package with all key documents including the security plan, security assessment report, and plan of action and milestones (if applicable)? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 69 Milestone Checkpoint #5 (2 of 2) Did the final risk determination and risk acceptance by the authorizing official reflect the risk management strategy developed by the organization and conveyed by the risk executive (function)? • Was the authorization decision conveyed to appropriate organizational personnel including information system owners and common control providers? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 70 RMF Step 6 Tasks Monitor Security Controls Information System and Environment Changes Task 6-1: Determine the security impact of proposed or actual changes to the information system and its environment of operation. Ongoing Security Control Assessments Task 6-2: Assess a selected subset of the technical, management, and operational security controls employed within and inherited by the information system in accordance with the organization-defined monitoring strategy. Ongoing Remediation Actions Task 6-3: Conduct selected remediation actions based on the results of ongoing monitoring activities, assessment of risk, and the outstanding items in the plan of action and milestones. Key Updates Task 6-4: Update the security plan, security assessment report, and plan of action and milestones based on the results of the continuous monitoring process. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 71 RMF Step 6 Tasks Monitor Security Controls Security Status Reporting Task 6-5: Report the security status of the information system (including the effectiveness of security controls employed within and inherited by the system) to appropriate organizational officials on an ongoing basis in accordance with the organization-defined monitoring strategy. Ongoing Risk Determination and Acceptance Task 6-6: Review the reported security status of the information system (including the effectiveness of security controls employed within and inherited by the system) on an ongoing basis in accordance with the monitoring strategy to determine whether the risk to organizational operations, organizational assets, individuals, other organizations, or the Nation remains acceptable. Information System Removal and Decommissioning Task 6-7: Implement an information system decommissioning strategy, when needed, which executes required actions when a system is removed from service. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 72 Milestone Checkpoint #6 (1 of 2) Is the organization effectively monitoring changes to the information system and its environment of operation including the effectiveness of deployed security controls in accordance with the continuous monitoring strategy? Is the organization effectively analyzing the security impacts of identified changes to the information system and its environment of operation? Is the organization conducting ongoing assessments of security controls in accordance with the monitoring strategy? Is the organization taking the necessary remediation actions on an ongoing basis to address identified weaknesses and deficiencies in the information system and its environment of operation? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 73 Milestone Checkpoint #6 (2 of 2) Does the organization have an effective process in place to report the security status of the information system and its environment of operation to the authorizing officials and other designated senior leaders within the organization on an ongoing basis? Is the organization updating critical risk management documents based on ongoing monitoring activities? Are authorizing officials conducting ongoing security authorizations by employing effective continuous monitoring activities and communicating updated risk determination and acceptance decisions to information system owners and common control providers? NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 74 Recognition of Authorization Results Organization One Business / Mission Information Flow INFORMATION SYSTEM INFORMATION SYSTEM Security Plan Security Plan Security Assessment Report Organization Two Security Authorization Information Plan of Action and Milestones Determining risk to the organization’s operations and assets, individuals, other organizations, and the Nation; and the acceptability of such risk. Security Assessment Report Plan of Action and Milestones Determining risk to the organization’s operations and assets, individuals, other organizations, and the Nation; and the acceptability of such risk. The objective is to achieve transparency of prospective partner’s information security authorization processes…establishing trust relationships based on common, shared risk management principles. NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 75 Contact Information 100 Bureau Drive Mailstop 8930 Gaithersburg, MD USA 20899-8930 Project Leader Administrative Support Dr. Ron Ross (301) 975-5390 ron.ross@nist.gov Peggy Himes (301) 975-2489 peggy.himes@nist.gov Senior Information Security Researchers and Technical Support Marianne Swanson (301) 975-3293 marianne.swanson@nist.gov Kelley Dempsey (301) 975-2827 kelley.dempsey@nist.gov Pat Toth (301) 975-5140 patricia.toth@nist.gov Arnold Johnson (301) 975-3247 arnold.johnson@nist.gov Web: csrc.nist.gov/sec-cert Comments: sec-cert@nist.gov NATIONAL INSTITUTE OF STANDARDS AND TECHNOLOGY 76