UNIT 5 Which of the following is NOT an example of a network node
advertisement

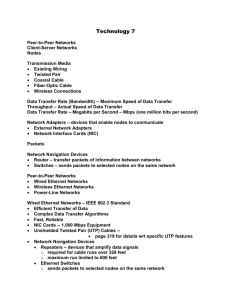
UNIT 5 1. Which of the following is NOT an example of a network node? A. printer B. computer C. NOS D. modem Answer: C 2. The network architecture used in most home networks is: A. client-server LAN. B. peer-to-peer LAN. C. client-server WAN. D. peer-to-peer WAN. Answer: B 3. You must install a(n) ____________ on a network if you want to share a broadband Internet connection. A. router B. modem C. node D. cable Answer: A 4. Which of the following statements concerning peer-to-peer networks is FALSE? A. A peer-to-peer network is the most common example of a locally controlled network. B. Peer-to-peer networks cost more than client/server networks and are more difficult to maintain. C. Each node on a peer-to-peer network can communicate directly with every other node on the network. D. Peer-to-peer networks are the most common type of home network. Answer: B 5. The design of the network is called the network: A. architecture. B. server. C. transmission. D. type. Answer: A 6. Data transfer rate (also called bandwidth) is the ____________ speed at which data can be transmitted between two nodes on a network. A. average B. minimum C. actual D. maximum Answer: D 7. ____________ are the navigation devices that act as the “traffic cops” of the network and forward packets to nodes on the same network (not between two networks). A. NICs B. Routers C. Switches D. Modems Answer: C 8. Which of the following statements is FALSE concerning Ethernet networks? A. Cat 5e UTP cable is recommended for Ethernet networks. B. Cat 5 UTP supports a data transmission rate of 1 Gbps. C. Ethernet typically uses an RJ-45 connector. D. When using UTP, a cable run cannot exceed 328 feet. Answer: B 9. Devices installed on long cable runs to amplify the signal are called: A. repeaters. B. adapters. C. switches. D. routers. Answer: A 10. A network navigation device that merely retransmits a signal to all other nodes attached to it is a(n): A. router. B. NIC. C. hub. D. adapter. Answer: C 11. The network navigation device known as a “smart hub” that transmits a signal only to the node to which it should be sent is a(n): A. router. B. switch. C. NIC. D. adapter. Answer: B 12. A ____________ is a device, contained in a wireless network adapter, that translates the electronic data on a network into radio waves and broadcasts the radio waves to other nodes on the network. A. router B. switch C. hub D. transceiver Answer: D 13. A switch is also known as a(n): A. smart hub. B. DSL modem. C. smart router. D. cable modem. Answer: A 14. When creating a phoneline network, it is necessary to install a(n) ____________ adapter. A. wireless B. phone cord C. home phoneline network D. Digital Subscriber Line (DSL) Answer: C 15. ____________ adapters, used on a power-line network, are available in either USB or Ethernet versions. A. Power-line network B. Peer-to-peer network C. Phoneline network D. Wireless network Answer: A 16. All of the following statements concerning client/server networks are true EXCEPT: A. one computer on a client/server network must act as a server. B. there is no centralized security or administration on a client/server network. C. most networks that have 10 or more nodes are client/server networks. D. the Internet is an example of a client/server network. Answer: B 17. Which of the following types of network adapter card is most likely to be preinstalled in a typical home computer? A. Ethernet B. power-line adapter C. wireless adapter D. HPNA adapter Answer: A 18. If a home network is connected to the Internet a ____________ is required to send data between the two networks. A. router B. repeater C. switch D. network operating system Answer: A 19. CAT 5, CAT 5E, and CAT 6 are all types of: A. network adapters. B. Ethernet ports. C. UTP cables. D. connector jacks. Answer: C 20. A wireless network uses ____________ as its transmission media. A. cables B. radio waves C. twisted pair D. fiber optics Answer: B 21. The main difference between the various 802.11 standards is the: A. data transfer rate. B. maximum allowable cable length. C. simplicity of installation. D. collision detection rate. Answer: A 22. The transceiver is the device that converts electronic data into ____________ for broadcast to other network nodes. A. packets B. radio waves C. WAPs D. 802.11 standards Answer: B 23. If you wish to extend the length of the network without having the signal degrade, you would use a: A. repeater. B. router. C. gateway. D. switch. Answer: A 24. If computers in a wireless network are unable to connect to the wireless router, adding a(n) ____________ extends the range of the wireless network by providing a second point to which the nodes can connect to the network. A. router B. Internet portal C. cable modem D. wireless access point Answer: D 25. In network terminology, a(n) ____________ is a wireless router that combines the capabilities of a wired router with the ability to receive wireless signals. A. hub B. gateway C. adapter D. Ethernet port Answer: B 26. If you frequently need to transfer streaming video or very large files between computers, which of the following networks would be the best choice? A. Ethernet B. wireless C. power-line D. phoneline Answer: A 27. The ____________ operating system assists with configuring home networks with a Network Setup Wizard. A. Windows 98 B. Windows ME C. Windows XP D. DOS Answer: C 28. In a(n) ____________ network, any electrical outlet provides a network connection. A. wireless B. power-line C. phoneline D. Ethernet Answer: B 29. In a(n) ____________ network, any phone jack provides a network connection. A. phoneline B. power-line C. 802.11g D. Ethernet Answer: A 30. A computer virus attaches itself to and attempts to hide within the code of a(n) ____________ program. A. zombie B. Trojan horse C. host D. worm Answer: C 31. ____________ viruses replicate themselves to the Master Boot Record whenever the computer boots up, ensuring that the virus will be loaded into memory before some virus protection programs are loaded. A. Zombie B. Trojan horse C. Worm D. Boot-sector Answer: D 32. ____________ viruses are often transmitted by a floppy disk left in the floppy disk drive. A. Boot-sector B. Trojan horse C. Script D. Logic bomb Answer: A 33. ____________ are viruses that are triggered when certain logical conditions are met. A. Boot-sector viruses B. Logic bombs C. Macro viruses D. Worms Answer: B 34. ____________viruses attach themselves to documents such as Word and Excel. A. Boot-sector B. Trojan horse C. DOS D. Macro Answer: D 35. A numbered communication gateway or path, used to organize requests for information, that is assigned for a commonly used network service such as SMTP or HTTP is called a: A. protocol. B. physical port. C. logical port. D. packet filter. Answer: C 36. Which of the following would most likely NOT be a symptom of a virus? A. Existing program files and icons disappear. B. The CD-ROM stops functioning. C. The Web browser opens to an unusual home page. D. Odd messages or images are displayed on the screen. Answer: B 37. Blocking access to logical ports is a common method used by ____________ for maximizing computer security. A. switches B. Web browsers C. firewalls D. access points Answer: C 38. ____________ are a series of commands, actually mini programs that are executed without your knowledge. A. Scripts B. Trojan horses C. Worms D. Boot-sector viruses Answer: A 39. A firewall’s ability to examine incoming and outgoing information and prevent the use of unauthorized logical ports is known as: A. packet filtering. B. logical port blocking. C. Network Address Translation. D. network key distribution. Answer: A 40. Classifications of viruses by the methods they take to avoid detection by antivirus software include all of the following EXCEPT: A. polymorphic. B. multipartite. C. encryption. D. stealth. Answer: C 41. The purpose of Network Address Translation is to: A. translate an IP address to a text-based URL. B. hide user IP addresses from the Internet. C. convert logical ports to physical port configurations. D. dynamically assign IP addresses via an ISP. Answer: B 42. When you set up a router for a wireless network, the router uses a default network name known as the: A. service set identifier (SSID). B. router address. C. MAC address. D. IP identifier. Answer: A 43. Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA) are examples of: A. packet filtering services. B. network address translation protocols. C. security protocols. D. service set identifiers. Answer: C 44. A ____________ is the name given to a computer that is controlled by hackers through the installation of a backdoor program and used to flood a target computer with bogus requests. A. zombie B. worm C. DoS D. Trojan horse Answer: A 45. Wired Equivalent Privacy (WEP) and Wi-Fi Protected Access (WPA) use ____________ to protect data. A. packet filtering B. network address translation C. encryption D. service set identifiers Answer: C 46. ____________ are viruses that are triggered by the passage of time or on a certain date. A. Boot-sector viruses B. Macro viruses C. Time bombs D. Worms Answer: C 47. Unlike other viruses, ____________ are viruses that can run independently of host file execution and are much more active in spreading themselves. A. boot-sector viruses B. time bombs C. Trojan horses D. worms Answer: D 48. ____________ viruses temporarily erase their code from the files where they reside and hide in active memory. A. Multipartite B. Stealth C. Polymorphic D. Script Answer: B 49. All of the following are recommended to secure a wireless network EXCEPT: A. changing the default password on your router. B. turning on security protocols. C. using static IP addressing. D. restricting access to the network to certain MAC addresses. Answer: C 50. If a virus signature or other suspicious activity is detected by the antivirus software, it places the virus in a secure area of the hard drive so that it won’t spread infection to other files. This procedure is known as: A. inoculation. B. automatic updating. C. encryption. D. quarantining. Answer: D