11-1 scanning
advertisement

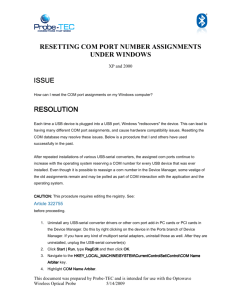
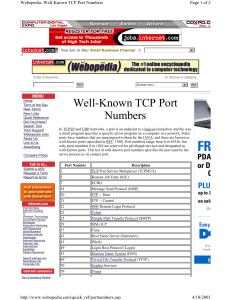
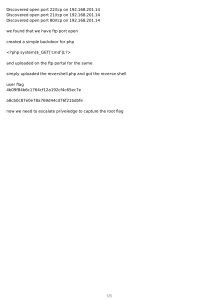
Network Security Port Scanning and Enumeration (NMAP) Port Scanning Definition: Probing the ports on a remote machine to gain information Port – a virtual identifier on a system for a particular application/protocol Examples: ftp: port 21 ssh: port 22 telnet: port 23 http: port 80 Oracle: port 1521 Usefulness Attacker: which ports are open? Defender: which ports are potential vulnerabilities? Specific Uses Find out if system is up Ping scanning Find open/vulnerable ports – what services are available? Port scanning Operating System identification TCP/IP fingerprinting Based on packet TTL, packet size, flags set on SYN/SYN|ACK packets in TCP handshaking How to use this information Identify exposed ports/services Shut down any unneeded services Famous last words - “I didn’t know X was running on my system” Ensure that services that are running do not have security vulnerabilities Issues Possible problems with usage Options can flood target machine with packets, potentially affecting it Ethics Is it ethical to probe an arbitrary system? Most say “no” Identification of probing system http://www.insecure.org/nmap/idlescan.html Port Scanning Tools Unix/Linux nmap HPING2 udp_scan netcat (nc) Windows SuperScan4 WinScan ipEye nmap One of many software implementations of a port scanner Open source Available on Windows and Unix Supports many hardware options, including some PDAs Now with GUI front ends Linux: nmapfe Windows: nmapwin http://www.insecure.org nmap features Identifies open ports Options for regular or stealth scanning Regular scanning – attempt full connection with port; scanned system knows scan is occurring and can identify scanner Stealth scanning – attempt partial connection with port; scanned system may not know scan is occurring and may not be able to identify scanner Attempts to identify operating system Usually correct, but can be fooled nmap Output Example Starting nmap V. 2.54 (www.insecure.org) Interesting ports on (www.xxx.yyy.zzz) (The xxxx ports scanned but not shown here are in state: closed) Port State Service 22/tcp open ssh 47017/tcp open unknown TCP Sequence Prediction: Class-random positive increments Difficulty=3980866 (Good luck!) Remote operating system guess: Linux 2.1.122 – 2.2.16 Nmap run completed - - 1 IP address (1 host up) scanned in 5 seconds SuperScan4 Nice Windows GUI Many extra options Information on ports/services in HTML report format