Legal Research, Issues
and Practice in
Cyberspace
-
First Amendment, Digital
Discovery, Data Retention,
and Digital Security
Cyrus Daftary & Todd Krieger
March 25, 2013
1
Agenda
2
Project / presentation discussion
Online security
First Amendment
Data retention and digital discovery
Questions and Answers
Have I Learned Anything
Practical Yet?
3
http://media.away.com/images/contests/
photo-contest/away-com-monthly-photocontest-terms-conditions.pdf
Breaking Supreme Court News – Week 5 Revisited
Is Software Sold or Licensed?
4
Ensure the software is properly licensed.
Unusual opinion in Vernor vs. Autodesk.
Court looked at characteristics of transaction,
not how the transaction was described by the
parties.
Appeals court reiterated the licensor’s rights.
First Sale Doctrine Revisited
“Copyright © 2008 John Wiley & Sons (Asia) Pte Ltd[.]
All rights reserved. This book is authorized for sale in
Europe, Asia, Africa, and the Middle East only and may
be not exported out of these territories. Exportation
from or importation of this book to another region
without the Publisher’s authorization is illegal and is a
violation of the Publisher’s rights. The Publisher may
take legal action to enforce its rights. . . . Printed in
Asia.” J. Walker, Fundamentals of Physics, p. vi (8th
ed. 2008 Wiley Int’l Student ed.).
Kirtsaeng vs. John Wiley & Sons, No. 11-697, 2013 BL
72102 (U.S. Mar. 19, 2013).
5
Data Security is a Relatively
New Area of Liability
Company computers may house sensitive
consumer data and trade secrets.
Failure to adequately protect consumer data
has led to high profile settlements with the FTC:
6
Choicepoint: $15 million
TJX
BJs Wholesale Club
Hannafords – 3/08 - 4 million credit card numbers
compromised.
Failure to adequately protect trade secrets can
also create a corporate disaster.
Sensitive Digital Data May
Reside in Surprising Places
7
http://www.cbsnews.com/830118563_162-6412439.html
http://business.ftc.gov/documents/bus43copier-data-security
Nevada SB 267 Was Passed
in Response
Section 4 of this bill requires a business entity or a
data collector to ensure that any personal information
which is stored on the data storage device of a
copier, facsimile machine or multifunction device in
the possession of the business entity or data collector
is securely encrypted or destroyed by certain
approved methods before the business entity or data
collector relinquishes ownership, physical control or
custody of the copier, facsimile machine or
multifunction device to another person.
http://openstates.org/nv/bills/76/SB267/documents/NVD00008333/
8
Companies are Obligated to
Protect Sensitive Data and
Report Breaches
Most states require notification of residents if
personal data is compromised and many other
states are not far behind.
9
Massachusetts 93H
http://www.mass.gov/ocabr/business/identity-theft/requirements-for-securitybreach-notifications.html
Hundreds of data breaches have been reported
Reporting has led to bad publicity and fines.
Marriott reported the loss of 200,000 names in
missing backup tapes.
Some reporting requirements are exempted if the
data was encrypted.
ID Theft Has Impacted
Millions of Americans
U.S. consumers lost billions to identity theft
in 2012
ID Theft consumes time and money.
Consumers are more careful with their
personal information.
Vulnerable to phishing attacks
As safe as the company where they used their credit
card.
IRS Criminal Investigation Targets Identity Theft Refund Fraud
FS-2013-4, February 2013
The IRS has seen a significant increase in refund fraud that
involves identity thieves who file false claims for refunds by stealing
and using someone's Social Security number.
http://www.irs.gov/uac/Newsroom/IRS-Criminal-Investigation-Targets-Identity-Theft-Refund-Fraud-2013
10
Phishing Attacks Can Be
Cleverly Disguised
11
Data Thieves Actively Target
Websites and Corporate
Networks
May use e-mail viruses to crack
networks
Target specific applications to get
sensitive data
12
Once the perimeter security is cracked, the entire
network may be available.
Hijack remote computers to
anonymously attack sites.
Reasonable Measures To
Protect Sensitive Information
Policies
13
http://www.mass.gov/ocabr/docs/idtheft/compliance-checklist.pdf
Encryption
Intrusion detection
Firewalls
Password protection
Anti-virus programs
Physical security of laptops and portable media.
First Amendment
The First Amendment mandates that “Congress
shall make no law respecting an establishment of religion,
or prohibiting the free exercise thereof; or abridging the
freedom of speech, or of the press, or the right of the
people to peaceably assemble, and to petition the
Government for redress of grievances.”
14
First Amendment protects citizens from the
federal government, whereas the Fourteenth
Amendment applies to state and local
governments
General Guidelines
15
Every citizen has First Amendment Rights. It makes no
difference who you are, what you do, or what you
believe.
Rarely can words alone get someone into trouble.
There are situations where there is a need to punish
speakers for the harm their words might cause to
others, or to compensate those harmed by their speech.
Technology has created new venues for
communications.
Most messages in Cyberspace qualify for protection
under the First Amendment.
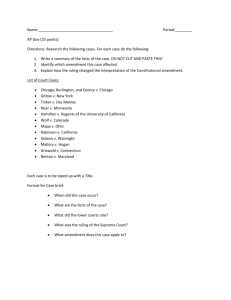
Fire!
Speech that does not warrant
protection
Clear and Present Danger
Recall the Brandenburg test…
1. Speech in question must be directed to inciting or
producing imminent lawless action; and
2. Speech must be likely to incite or product such action
Fighting Words - Hate crimes/speech
Obscenity and Child Pornography
False or Deceptive Advertising
Defamation
Cyberspace defamation = libel since it is written
16
Other Harmful Communication
May Not Be Actionable
17
In 2006, 13 year old Megan Meier
committed suicide after receiving cruel
messages from an online friend, Josh,
who she met on MySpace.
‘Josh’ turned out to be the mother of a
girl who lived nearby.
Law enforcement officials could find no
grounds to charge the mother.
Eventually convicted by a jury for
misdemeanor unauthorized access of a
computer.
Courts have Recognized the
Value of Online Communication
“[the Internet is the] most participatory
form of mass speech yet developed…a
far more speech-enhancing medium
than print.”
18
U.S. District Judge Stewart Dalzell (ACLU vs. Reno)
Questions to Consider
Does an internet service provider violate 1st
Amendment privileges when (s)he deletes
content from a website?
(A user could claim that an ISP who deletes a message has acted in
an unconstitutional way)
Is Cyberspace a public forum?
(consider who owns the Internet - Most of Cyberspace is considered
nonpublic and is privately owned; hence the owners are free to
exercise editorial control over any speech in any manner.)
19
Can you come up with a restriction that is content
neutral and is aimed at the time, place, or
manner of the activity.
Challenges to First Amendment
Rights - Defamation
20
An unfortunate byproduct of the Internet is the rapid
rise of “cybersmearing” – which is the anonymous or
pseudonymous defamation on the ‘Net of individuals,
companies, and corporate executives.
Cause of action – actionable defamation or other torts.
Need to obtain a broad ex parte order from the court
authorizing the issuance and service of an
identification-seeking subpoena directed at the ISP to
reveal the DOE defendant.
Anonymous Patent Troll Tracker blog author was
‘outed’ when a patent attorney criticized on the blog
offered a $15,000 award.
Blogger subsequently sued for critical postings on the site.
Challenges to First Amendment
Rights Online – Reno vs. ACLU:
Reno vs. ACLU: Community Decency Act 1996 - attempted to ban transmission of
obscene or indecent material across the
Internet. Unconstitutional, overbroad.
Reno vs. ACLU - COPA Designed to limit
online information that could be ‘harmful to
minors’
21
What is the presumption for a content based restriction?
Overbroad definition relying on varying community
standards.
The First Amendment Stops
at the Border
Free speech rights vary by country.
Yahoo! battled in French courts to allow
auction users to sell Nazi memorabilia.
Egypt blocked Internet and cell phone access
when unrest began
22
Facebook, Twitter and Google have facilitated
communication.
Pakistan’s ISP blocked YouTube and took
down the site worldwide for over a day.
Other Domestic Challenges to
First Amendment Rights Online:
Unpopular criticism: Curzon-Brown vs. San Francisco Community
College District: Criticized teacher trying to shut down online “teacher review.”
(www.aclunc.org).
State laws (often declared unconstitutional).
American Booksellers vs. Dean, PSINet vs.
Chapman - VA Code (200 U.S. Dist. Lexis 11621 08/08/2000)
Mandatory filters (schools, libraries). (Mainstream
Loudoun vs. Board of Trustees of the Loudoun County Library 24 F Supp 2 d
552 (E.D. Va. 1998)
Unprotected speech: is a program that decrypts
protected DVDs protected speech? (DVD Copy Control
Association vs. Bunner No. H021153)
23
Untested laws: USA Patriot Act – school removed local link to a
violent Marxist insurgency in Columbia (U.C.S.D.)
An Expensive Lawsuit Can Also
Quell First Amendment Rights
24
Bally Fitness Centers sued the registrant of
“Ballysucks.com” and failed. Walmart was able
to prevail against Walmartsucks.com in
arbitration.
The Church of Scientology sued Google.com
and compelled the search engine to remove
links to a supposedly infringing site.
Other examples available at
www.chillingeffects.org
Is Access to Wikileaks a First
Amendment right?
The NY Times published some of the same
information
How about Amazon hosting, Paypal, and other
sites refusing access?
25
Other First Amendment
domain name issues
Anti-hate groups have registered many ethnic
slurs as domain names, preventing others from
exploiting the words.
Network Solutions had blocked registration of
the 7 dirty words. Should (naughty word).com
be permitted? What about other languages and
terms that are offensive to other cultures.
26
Not a free speech issue since other registrars do not filter
obscene words.
Name.Space Inc. vs. Network Solutions:
Domain names are not protected speech.
Internet Network and Service
Providers also Regulate Content
Terms and conditions of many ISPs prohibit
certain content and activities.
Genuity’s acceptable use policy for the Genuity
Network:
It is strictly prohibited to create, transmit, or distribute…material
which:
(Illegal Activity)
•
•
•
•
•
27
Infringes I.P.
Is obscene or child pornography
Is libelous, defamatory, hateful, or constitutes an illegal threat or abuse.
Violates export control laws or regulations
Encourages conduct that would constitute a criminal offense or give rise to civil liability.
(Abuse)
• ..Violates the accepted norms and expectations of the Internet community at large.
• Harassment, whether through language, frequency, or size of messages.
6 Strikes From the ISP: CAS
Copyright Alert System
Strike 1 & 2: E-mail from ISP
Strike 3 & 4: Landing page requiring
agreement not to engage in illegal
activity
Strike 5 & 6: Mitigation Measures
AT&T, Cablevision, Comcast, Time
Warner, and Verizon are participating
28
Is Net Neutrality an Oxymoron?
29
Comcast case discussion
Netflix may be slower on Comcast
networks.
Should Comcast be able to charge
content providers to deliver content to
Comcast customers?
Antitrust concerns?
Filtering content: how far
should it extend?
30
Should students be able to access:
Obscene words?
Obscene images?
Hate speech?
Bomb making instructions?
Unregulated chat rooms?
How about school hosted site with student postings?
Should public libraries have the same restrictions?
What about employers?
Should Hate Speech be
Permitted Online?
31
The Internet provides hate groups with a global
reach.
While membership in hate groups has declined,
online sales of supremacist CDs are exploding.
Hate content in the U.S. may violate laws of
other countries.
Should hate groups be permitted to recruit
online?
Blogging: Anyone Can Be a
Writer Online
Blogging: an online journal or newsletter that
is frequently updated and publicly available,
usually reflecting the personality of the writer.
Topics span every conceivable interest and
subject.
Blog searching: http://blogsearch.google.com/
Blog about Suffolk:
http://anonymouslawyer.blogspot.com/2006/02/i-seem-to-haveunderestimated-students.html
32
Blogs May Cross The Line
into Journalism
Some popular news issues came to the
mainstream media due to blogs
Blog writers may be anonymous and lack
the accountability of journalists.
Legal Risks:
Online defamation
Privacy of the poster
Trade secrets revealed
Mainstream journalists can enjoy some degree of
protection of their sources
• Apple Case
33
Blogging has opened new
avenues of expression and risk
Citizens world wide have a new means of
addressing political issues.
Bloggers have been jailed in the Middle
East, North Africa and Asia.
Overview of blogging liability concerns:
http://www.eff.org/bloggers/lg/
34
What is Discovery?
“Discovery” refers to the process of compelling
another party to provide information, which may
include documents, during the course of
litigation.
Gives litigants access to information relevant to
the dispute.
Discovery requests may be very broad and
burdensome, especially in business litigation.
Facebook postings and other seemingly private
information can be within the scope of a
discovery request.
35
Case discussion: McCann vs. Harleysville Ins. Co. of
N.Y.
Digital Discovery and Data
Retention
36
Most new information is electronic.
Companies need codified policies for retention
of digital and printed information or they could
be overwhelmed by a discovery request.
Define retention periods based on legal,
business and personal obligations.
Must follow policies carefully.
Third party solutions available.
Federal Rules of Civil Procedure
For Electronic Discovery
Implemented 12/06
37
Rules put in place process for party to
demand access to information that is claimed
to be ‘burdensome to access and produce.’
Companies may have hundreds of
unorganized legacy back-up tapes with year
of e-mails and other information
New rules provide exceptions for good faith
inadvertent destruction.
New Rules Harmonize
Electronic Discovery Practices
38
Attorneys involved in litigation must
address electronic discovery at the
earliest stage of discovery planning.
New rules provide a framework for
courts and easier guidance to assist
clients.
Some Specific Requirements:
Rule 26(a)(1)(B) changes ‘data compilations’ to
‘electronically stored information’.
39
(similar amendments to other rules)
Rule 16(b) amended to require that scheduling order may
include electronically stored information.
Rule 26(f) requires parties to confer and discuss issues
related to electronic information.
Rule 26(b)(2)(B) addresses the burden for data that is not
readily accessible. Party receiving request must establish
unreasonableness of request.
Rule 37(f) accommodates the accidental loss or
destruction during a routine operation of electronic
information if the party took reasonable steps for
preservation.
Keep in mind other changes as well.
http://www.ims-expertservices.com/newsletters/nov/eddrules-111406.htm
Courts Have Defined
Expectations of Digital Discovery
“Now that the key issues have been addressed
and national standards are developing, parties
and their counsel are fully on notice of their
responsibility to preserve and produce
electronically stored information.”
Complying with digital discovery requests may
be very expensive, time consuming and
implicating.
40
Judge Shura Scheindlin, Zubulake vs. Warburg
Final jury verdict: $29 million.
Pension Committee of U of Montreal vs. Banc of America case
discussion
High Profile Cases Have Led
to Big Verdicts
41
Coleman vs. Morgan Stanley: $1.45 Billion
jury verdict for overwriting e-mails, failing to
timely process backup tapes, failure to
produce relevant e-mails and attachments.
U.S. vs. Philip Morris , 327 F. Supp. 2d 21:
$2.75 Million in sanctions for failure to follow
order to preserve e-mails and other ediscovery violations.
Meta-data May Be Critical
Metadata = ‘data about data’
Metadata must remain intact:
History (date of creation and modification)
Tracking (who created the document and where does it
reside)
Comments and annotation.
Metadata may leave an implicating trail.
42
Previously deleted text
Comments
Identity of those who worked on document
Dates and times of work.
Changes in date in Windows may not be the same in the
underlying DOS.
Electronic Discovery Can be
Very Expensive
Average may be $1-3 million
Litigants need efficient data search and
management strategies
43
Law firms bill for searches on an hourly basis
Data may not be in a common or
searchable format
Questions and Answers
44