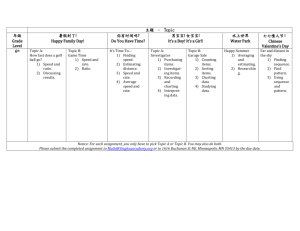
Test 8 - Bill Buchanan
advertisement

E-Security CO73046 Network Security Contact: Room: Telephone: MSN Messenger: WWW: w.buchanan@napier.ac.uk C.63 X2759 w_j_buchanan@hotmail.com http://www.dcs.napier.ac.uk/~bill http://buchananweb.co.uk Author: Bill Buchanan Prof. Bill Buchanan Work Schedule Week Date Academic Assessment Lab/Tutorial 1 4 Feb 1: Introduction 2: Security Fundamentals 2 11 Feb 3: IDS Lab 1: Packet Capture Lab 2: Packet Capture (Filter) 3 18 Feb 4: Encryption Lab 3: Packet Capture (IDS) Lab 4: Packet Capture (ARP) 4 25 Feb 5: Authentication (Part 1) Lab 5: IDS Snort 1 5 3 Mar 5: Authentication (Part 2) Lab 6: IDS Snort 2 6 10 Mar 6: Software Security Lab 7: Private-key encryption 7 17 Mar 7: Network Security 8: Secure Protocols Lab 8: Public-key encryption 8 7 Apr 9 14 Apr Security Specialisation (.NET Security or Network Security) 10 21 Apr Security Specialisation (.NET Security or Network Security) Specialisation Lab 11 28 Apr Security Specialisation (.NET Security or Network Security) Specialisation Lab 12 5 May Security Specialisation (.NET Security or Network Security) C/W hand-in (IDS) [50%] MCQ Test [10%] Author: Bill Buchanan MCQ Test [40%] Friday, 11 Apr 2008 Week 1-8 Academic Element On-line test: 40% Coursework: Agent-based IDS Web-CT submission: 50% Web-CT submission .NET Security On-line test: 10% Cisco Academy NS 1 On-line test: 10% On-line test Author: Bill Buchanan Week 8-13 MCQ Test Author: Bill Buchanan PIX Certification Questions The Cisco Secure PIX Firewall Advanced exam (CSPFA 642-521) is one of the exams associated with the Cisco Certified Security Professional and the Cisco Firewall Specialist certifications. Candidates can prepare for this exam by taking the CSPFA v3.2 course. This exam includes simulations and tests a candidate's knowledge and ability to describe, configure, verify and manage the PIX Firewall product family. CCNA or CCDA recertification candidates who pass the 642-521 CSPFA exam will be considered recertified at the CCNA or CCDA level. Author: Bill Buchanan • 1. What is CA? Author: Bill Buchanan A. Configured applications B. Cisco authentication C. Certificate authority D. Command approval 2. How many interfaces does the PIX 506 support? Author: Bill Buchanan A. 4 B. 2 C. 6 D. 3 3. How do you change the activation key on the PIX? Author: Bill Buchanan A. Reset the PIX B. With the checksum command C. Copy a PIX image to the flash D. The activation key cannot be changed 4. When configuring ACL to identify traffic that requires encryption, two entries are needed. One for inbound traffic and one for outbound traffic. Author: Bill Buchanan A. True B. False 5. What is the different about the PIX privileged access mode as opposed to the privileged access mode of a Cisco IOS router? Author: Bill Buchanan A. The "?" command does not work on the PIX B. No difference C. Each configuration command is automatically saved to flash D. The ability to view the running configuration from the configuration mode 7. What are some application layer protocols that CBAC can inspect? (choose all that apply) Author: Bill Buchanan A. TFTP B. TCP C. SMTP D. UDP E. HTTP F. FTP 8. What two commands are needed for inbound access? (choose two) Author: Bill Buchanan A. Static B. Access-list C. PAT D. NAT 9. In CBAC, what is a state table? Author: Bill Buchanan A. A table containing access-list information B. A table containing information about the state of CBAC C. A table containing information about the state of the packet's connection D. A table containing routing information 10. What is required for stateful failover on the PIX 515? (choose all that apply) Author: Bill Buchanan A. Unrestricted software license B. Cisco failover cable C. Cisco IOS failover feature set D. 2 Ethernet interfaces interconnected 11. What is the purpose of a syslog server? Author: Bill Buchanan A. To host websites B. To collect system messages C. To maintain current backup configurations D. To maintain URL filtering information 12. Default "fixup protocol" commands cannot be disabled. Author: Bill Buchanan A. True B. False 13. What command deletes all authentication proxy entries? Author: Bill Buchanan A. Clear ip authentication-proxy cache B. Clear ip authentication-proxy cache all C. Clear ip authentication-proxy cache D. Clear authentication-proxy all entries 14. At what frequency does the PIX send hello packets to the failover unit? Author: Bill Buchanan A. 15 seconds B. 60 seconds C. 6 seconds D. 20 seconds 15. In AAA, what does the method keyword "local" mean? Author: Bill Buchanan A. That the AAA server is local B. Deny if login request is local C. Use the local database for authentication D. Authenticate if login request is local 16. What three types of entries does the PAM table provide? (choose 3) Author: Bill Buchanan A. User defined B. Internet specific C. Host specific D. System defined. 17. During IPSec security associations negotiation, if there are multiple transform sets, which one is used? Author: Bill Buchanan A. Is does not matter B. The first common one C. The first one D. The last one 18. CBAC inspection can only be configured in one direction. Author: Bill Buchanan A. False B. True 19. How do you identify a syslog server on the PIX? Author: Bill Buchanan A. logging host 10.1.1.1 B. TFTP server 10.1.1.1 C. syslog-server 10.1.1.1 D. syslog server 10.1.1.1 20. In CBAC, where are dynamic access entries added? Author: Bill Buchanan A. A new access-list is configured for each access entry B. At the beginning of the access-list C. A separate access-list is created for access entries D. At the end of the access-list 21. You establish an IPSec tunnel with a remote peer. You verify by viewing the security associations. You view the security associations two days later and find they are not there. What is the problem? Author: Bill Buchanan A. This would not happen B. You have used an incorrect command to view the security associations C. Your PIX is not powered up. D. No traffic was identified to be encrypted. 22. What is the purpose of the "route 0 0" command? Author: Bill Buchanan A. To configure a static route B. To enable routing on the PIX C. To configure a default route D. To route between 2 interfaces 23. What does DDOS stand for? Author: Bill Buchanan A. Distributed denial of service B. Dedicated Department of Security C. Dead, Denied, Out of Service D. Demand denial of service 24. In CBAC, how are half-open sessions measured? Author: Bill Buchanan A. Both TCP & UPD half-open sessions are calculated B. Only UDP half-open sessions are calculated C. CBAC does not calculate half-open sessions D. Only TCP half-open sessions are calculated 25. AAA stands for authentication, authorization, &______________. Author: Bill Buchanan A. application B. accounting C. access control D. authenticity 26. A transform set is a combination of ________ _______ & ____________. (choose all that apply) Author: Bill Buchanan A. access-list B. crypto maps C. security protocols D. algorithms 27. At what layer of the OSI model does IPSec provide security? Author: Bill Buchanan A. 4 B. 7 C. 8 D. 3 28. What is the purpose of the "clear access-list" command? Author: Bill Buchanan A. Remove an access-list from an interface B. To clear all access-list from the PIX C. To clear all access-list counters D. Invalid command 29. What are the two licenses supported on the PIX515? Author: Bill Buchanan A. Unrestricted B. Limited C. Restricted D. Unlimited 30. How are transform sets selected in manually established security associations? Author: Bill Buchanan A. Transform sets are not used in manually established security associations B. Manually established security associations only have one transform set C. The first transform set is always used D. The first common transform set is used 31. Access-list are supported with Radius authorization. Author: Bill Buchanan A. True. B. False 32. How do you view active NAT translations? Author: Bill Buchanan A. show nat-translations B. show ip-nat translations C. show xlate D. show translations 33. What does IKE Extended authentication provide? Author: Bill Buchanan A. Authentication of multiple IPSec peers B. Auto-negotiation of IPSec security associations C. User authentication using Radius/TACACS+ 34. What are two purposes of NAT? (choose 2) Author: Bill Buchanan A. To build routing tables B. To expedite packet inspection C. To connect two separate interfaces D. To conserve non-RFC1918 addresses E. To hide internal servers and workstations real IP addresses from the Internet 35. Only one IPSec tunnel can exist between two peers. Author: Bill Buchanan A. False B. True 36. How many hello packets must be missed before the failover unit will become active? Author: Bill Buchanan A. 2 B. 3 C. 1 D. 5 37. What are the two transport layer protocols? (choose 2) Author: Bill Buchanan A. TCP B. IP C. ICMP D. UDP 38. How do you configure a PAT address? Author: Bill Buchanan A. Nat (Outside) 1 1.1.1.1 1.1.1.1 255.255.255.255 B. IP PAT (Outside) 1 1.1.1.1 255.255.255.255 C. PAT (Outside) 1 1.1.1.1 255.255.255.255 D. Global (Outside) 1 1.1.1.1 1.1.1.1 255.255.255.255 39. How many interfaces does the PIX 515R support? Author: Bill Buchanan A. 3 B. 4 C. 2 D. 6 40. What are some advantages of using the PIX firewall over other firewalls such as Microsoft Proxy? (choose all that apply) Author: Bill Buchanan A. No security problems from running on top of other operating systems B. PIX firewall is plug and play, no configuration required C. PIX inspects on lower layer protocols D. PIX does stateful packet inspections E. One box solution A. Enable the new interface in the configuration B. Add the "conduit permit any any" statement to your configuration C. Nothing. The problem is probably with the clients workstations, not the PIX. D. Add the Cisco client proxy software to each workstation on the new network. Author: Bill Buchanan 41. You decide you need more interfaces for your PIX 515 and you already have the unrestricted license installed. The PIX firewall only shipped with 2 Ethernet interfaces. You install a new Ethernet interface that you ordered from Cisco. After you power the PIX on, you assign an IP address to the interface and configure a NAT & global statement for the new network. But users on the new network are unable to browse the Internet. What else do you need to do? 42. What two concepts are included in data authentication? (choose all that apply) Author: Bill Buchanan A. Anti replay B. Data origin authentication C. Data integrity. D. Data confidentiality 43. What is the layer-4 difference between Radius and TACACS+? Author: Bill Buchanan A. Radius uses TCP & TACACS+ uses UDP B. Radius uses UDP & TACACS+ uses TCP C. TACACS+ uses FTP & Radius uses TFTP D. There is no layer-4 difference between Radius & TACACS+ 44. "Logging timestamp" specifies that syslog messages sent to the syslog server should have a time stamp value on each message. Author: Bill Buchanan A. True B. False 45. What does the " crypto access-list" command accomplish? Author: Bill Buchanan A. There are no such access list B. They block non-encrypted traffic C. They identify crypto map statements D. Identifies which traffic is to be encrypted 46. What is the purpose of the outbound accesslist for a CBAC solution? Author: Bill Buchanan A. To block all traffic, CBAC will then inspect the traffic and allow legitimate traffic out B. Packets you want inspected by CBAC C. The is no need for an outbound access-list in a CBAC solution D. To identify legitimate inbound traffic from the Internet 47. How do you delete the following PAM entry? IP port-map http port 81 Author: Bill Buchanan A. clear IP port-map http port 81 B. This is a system-defined entry and cannot be deleted C. no IP port-map http port 81 D. delete IP port-map http port 81 48. What is the first step in configuring IPSec without CA? Author: Bill Buchanan A. Crypto B. ISAKMP C. IKE D. IPSEC 49. What version of IOS was the "ip port-map" command introduced? Author: Bill Buchanan A. 13.(1) B. 12.1 C. 11.0(1) D. 12.05(t) 50. What is the purpose of the "fixup protocol" commands? Author: Bill Buchanan A. To identify what protocols are permitted through the PIX B. Change PIX firewall application protocol feature C. To identify what protocols are to be blocked by the PIX D. To map a protocol to a TCP or UDP port 51. Without stateful failover, how are active connections handled? Author: Bill Buchanan A. Connections are maintained between the PIX and the failover unit B. Dropped C. UDP connections are maintained D. TCP connections are maintained 52. How many default routes can be assigned to the PIX firewall? Author: Bill Buchanan A. 1 per network B. 1. C. As many as required D. 1 per interface E. 1 for the primary PIX and 1 for the standby PIX 53. You have a PIX firewall and you are only given one public IP address from your ISP to use on the PIX. You do not have any type of servers that need be accessed from the Internet. What is a valid quick solution to your problem? Author: Bill Buchanan A. Get a new ISP B. PAT C. Request additional IP addresses from your ISP D. NAT 54. What three purposes does the failover cable serve? (choose all that apply) Author: Bill Buchanan A. Power status of the other unit B. Communication link C. Unit identification of both units D. Stateful information 55. Which PIX interface(s) do you apply the crypto map statements? Author: Bill Buchanan A. To the outside interface B. To the inside interface C. To any interfaces that IPSec packets will traverse D. All PIX interfaces 56. What is the purpose of authentication proxy? Author: Bill Buchanan A. Proxy of user logins B. To enable AAA C. Policies on per user basis D. For user accounting 57. You are required to have two crypto access-list for IPSec. One is to identify outbound traffic to be encrypted, and the other is to identify inbound traffic that should be encrypted. Author: Bill Buchanan A. False B. True 58. PAT is not supported with the "fixup protocol rtsp" command. Author: Bill Buchanan A. True B. False 59. How do you configure a pool of public IP addresses? Author: Bill Buchanan A. Global command B. Pool command C. NAT command. D. Static command 60. What is the purpose of the "logging trap" command? Author: Bill Buchanan A. Enables syslog traps B. This is not a valid PIX command C. Sends logs to a host named trap D. Enables SMTP traps 61. The inbound access-list or conduit statements must include permit statements for all IPSec traffic. Author: Bill Buchanan A. False B. True 62. What is one difference between conduit statements and access-list? Author: Bill Buchanan A. Conduit statements can only contain permit statements B. Conduit statements list the destination address before the source address and accessC. Conduit statements do not contain the implicit deny any at the end D. Access-list cannot be applied to the interfaces of the PIX 63. How do you configure a Web sense server on the PIX? Author: Bill Buchanan A. server 10.1.1.1 B. websense-server 10.1.1.1 C. url-server 10.1.1.1 D. websense 10.1.1.1 64. How many hosts will PAT support? Author: Bill Buchanan A. 1024 B. unlimited C. 64000 D. 1 65. When configuring a security association in IPSec, the global lifetime default (the time when the security association is renegotiated) is 28,800 seconds. Author: Bill Buchanan A. True B. False 66. What is the goal of a DDOS attack? Author: Bill Buchanan A. To use the network to attack another network B. To steal vital information C. To take control of the network D. To stop the network from working 67. What is required for stateful failover? (choose all that apply) Author: Bill Buchanan A. FDDI interface B. 1 interface interconnected C. PIX failover cable. D. 3 interfaces interconnected 68. What does ACS stand for? Author: Bill Buchanan A. Another Cisco Server B. Authentication, Control, Secure C. Access Control Server D. Access, Control, Security 69. With the PIX Firewall, you can configure: Author: Bill Buchanan A. Separate groups of TACACS+ or RADIUS servers for specifying different types of B. None of the above. PIX does not support TACACS+ or RADIUS. C. Only TACACS+ for inbound & outbound connections D. Only RADIUS for inbound & outbound connections 70. What command applies CBAC to an interface? Author: Bill Buchanan A. router# ip inspect NAME in interface outside B. router(conf)#ip inspect NAME in C. router(conf-if)#ip inspect NAME in D. router(conf)#ip inspect NAME out 71. In CBAC, where does the router get the state table information? Author: Bill Buchanan A. By inspecting the packet B. From a PIX firewall C. From routing tables D. Configured by administrator 72. What three protocols does the PIX provide credential prompts, with the proper configuration of an AAA server? (choose 3) Author: Bill Buchanan A. HTTP B. TFTP C. FTP D. HTTPS E. Telnet F. SSL 73. What command is required to save the configuration to a remote device? Author: Bill Buchanan A. radius-server B. Copy C. Save D. write 74. Authentication proxy only works with TACACS+. Author: Bill Buchanan A. False B. True 75. What is a dynamic crypto map? Author: Bill Buchanan A. There is no such thing as a dynamic crypto map B. When the PIX gets the entire crypto map configuration from a CA C. A crypto map created solely by the PIX upon negotiation with an IPSec peer D. A crypto map without all the parameters configured 76. What command displays the authentication proxy configuration? Author: Bill Buchanan A. Show version proxy-authentication B. Show proxy-authentication C. Show all proxy-authentication D. Show ip proxy-authentication 77. What is a false-positive alarms? Author: Bill Buchanan A. Alarms that do not reach their intended destination B. Legitimate alarms that are not triggered C. Alarms caused by legitimate traffic D. Alarms that an administrator ignores 78. What is data confidentiality? Author: Bill Buchanan A. IPSec receiver can detect & reject replayed packets B. Receiver authenticates packets to ensure no alterations have been made C. Packets are encrypted before they are transmitted across a network D. Receiver can authenticate source of IPSec packets 79. You can configure conduit statements on a PIX Firewall, but not access-list. Author: Bill Buchanan A. False B. True 80. How is inbound access controlled? (choose all that apply) Author: Bill Buchanan A. Global B. Access-list C. Static D. NAT 81. How is outbound access enabled? (choose all that apply) Author: Bill Buchanan A. Global B. Static C. NAT D. Access-list 82. In CBAC, how are dynamic access-list entries saved? Author: Bill Buchanan A. They are not saved B. Write memory C. Write tftp D. Save access-list 83. The PIX is a single point of failure and has no solution for redundancy. Cisco is working on a solution for this right now. Author: Bill Buchanan A. True B. False 84. A crypto map statement can contain multiple access-lists. Author: Bill Buchanan A. False B. True 85. How do you apply conduit statements to the outside interface? Author: Bill Buchanan A. With the use of the conduit-outside statement B. With the use of the conduit-group statement C. No configuration required D. Conduit statements cannot be applied to the outside interface 86. What does the "clear filter" command accomplish? Author: Bill Buchanan A. Clears all filter counters displayed by the show filters command B. Resets all filters to their original state C. Invalid PIX command D. Removes all filters from the PIX configuration 87. What two commands are needed for outbound access? (choose 2) Author: Bill Buchanan A. PAT B. Access list C. NAT D. Global 88. How does CBAC handle ICMP? Author: Bill Buchanan A. Only ICMP echo packets are inspected B. All ICMP traffic is inspected by CBAC C. ICMP traffic is not inspected by CBAC D. ICMP traffic is denied by CBAC 89. What two commands enable viewing the url filtering information? (choose 2) Author: Bill Buchanan A. show url-cache stats B. show url-filtering C. show filter-url D. show perfmon 90. What are the two types of global timeouts for IPSec on the PIX? (choose 2) Author: Bill Buchanan A. bandwidth B. uptime C. number of PPTP connections D. time 91. What command is utilized to upgrade the IOS version of the PIX? Author: Bill Buchanan A. Copy tftp flash B. Copy flash tftp C. Write tftp flash D. Save tftp flash 92. What is the command to assign an IP address to an interface? Author: Bill Buchanan A. nameif inside IP address 10.1.1.1 255.255.255.0 B. ip address inside 10.1.1.1 255.255.255.0 C. inside address 10.1.1.1 255.255.255.0 D. inside ip address 10.1.1.1 255.255.255.0 93. How do you reset a security association with an IPSec peer? Author: Bill Buchanan A. Clear ipsec sa <peer name> B. Disconnect the PIX from the network C. Delete security-association D. You must delete all IPSec configurations and reconfigure 94. How is URL filtering accomplished? Author: Bill Buchanan A. With a Web sense server B. With a Cisco IDS C. With a PIX failover unit D. URL filtering is not supported 95. What is the default time-out for authentication proxy? Author: Bill Buchanan A. 60 seconds B. 6 minutes C. 60 minutes D. 360 seconds 96. What traffic is identified in the inbound accesslist on a CBAC router? Author: Bill Buchanan A. Permitting traffic to be inspected by CBAC B. FTP C. Denying traffic to be inspected by CBAC D. HTTP 97. How do you map a port to a specific host? Author: Bill Buchanan A. You cannot map to a specific host B. IP port-map http port 81 host 10.1.1.1 C. An access-list permitting the host is required D. IP port-map http port 81 10.1.1.1 98. What command displays all security associations? Author: Bill Buchanan A. show ipsec security-associations B. show ipsec security-associations C. show ip security-associations D. show ipsec security-associations all 99. When do you need an access-list applied inbound to the inside interface? Author: Bill Buchanan A. When you want to block all outbound traffic B. When you want to control the outbound traffic C. Access-list cannot be applied to the inside interface D. When you want to control inbound public traffic 100. What does CBAC stand for? Author: Bill Buchanan A. Control Based on Access list B. Cisco Based Accounting Control. C. Context Based Access Control D. Cisco Based Access Control 101. How does the PIX initiate new IPSec security associations using dynamic crypto maps? Author: Bill Buchanan A. By sending its public key to the remote peer B. By sending an IKE key to the remote peer C. By sending security association request to the remote peer D. The PIX cannot initiate an IPSec sa using dynamic crypto maps 102. What is the purpose of a Web sense server? Author: Bill Buchanan A. To host our website B. It is a syslog server for the PIX C. URL filtering D. To monitor the state of your Internet connection 103. How are outbound UDP sessions handled? Author: Bill Buchanan A. A connection state is maintained on the PIX. B. All UDP traffic is permitted inbound unless blocked with an access-list C. The PIX does not recognize UDP sessions D. All UDP traffic is blocked outbound unless permitted with an access-list 104. How does a user receive a login screen through authentication proxy? Author: Bill Buchanan A. Clicking on the authentication proxy icon on the desktop B. They do not, as authentication proxy uses their NT login C. By opening a Internet browser D. From a command prompt 105. What command enables AAA on a Cisco router? Author: Bill Buchanan A. aaa radius B. aaa enable C. enable aaa D. aaa new-model 106. What does the "conduit" command do? Author: Bill Buchanan A. Nothing, the conduit is not a valid command on the PIX B. Enables the conduit interface on the PIX. C. Permits/denies traffic if the specified conditions are met. D. Maps a local address to a global address. 107. What are the two ways security associations can be established? (choose 2) Author: Bill Buchanan A. Manual B. CRYPTO C. ISAKMP D. IKE. 108. How do you determine the amount of memory and flash installed in the PIX? Author: Bill Buchanan A. show flash B. show dram C. show version D. show memory 109. What is the purpose of PAM? Author: Bill Buchanan A. To identify users via port mapping B. To create address pools for NAT C. There is no such feature D. To customize TCP & UDP port numbers 110. Which interfaces does the PIX send "hello" packets out of for failover? Author: Bill Buchanan A. Only interfaces directly connected to each other B. Inside C. All including the failover cable D. None, just over the failover cable 111. What is the purpose of the xlate command? Author: Bill Buchanan A. To configure translations B. To configure PIX global timeouts C. Xlate is not a valid command D. To view and clear translations 112. How do you clear the logging buffer? Author: Bill Buchanan A. clear buffer B. delete log C. clear logging D. delete log 113. What command saves the CA settings & policies? Author: Bill Buchanan A. ca save all B. save ca C. Write memory D. They cannot be saved 114. How is the configuration maintained between the primary PIX and the standby unit? Author: Bill Buchanan A. Standby is configured and configuration is replicated to primary B. Primary is configured and configuration is replicated to standby C. Both must be configured separately D. The standby does not maintain a current configuration until failover occurs 115. How does CBAC allow traffic through the router? Author: Bill Buchanan A. All traffic is blocked by the router B. Traffic must be permitted in the pre-configured access-list C. All traffic is allowed through D. Using access-list entries 116. In the following command, what does the keyword "http" represent? Ip port-map http port 81 Author: Bill Buchanan A. It identifies the table for the port-mapping to reference B. Nothing, the command is invalid C. it identifies the application name D. it redirects all http traffic from port 80 117. What is the purpose of the "nameif" command? Author: Bill Buchanan A. To shutdown an interface on the PIX B. To enable an interface on the PIX C. The nameif is not a valid PIX command. D. To assign a security level and name to an interface. 118. How do you view the running configuration? Author: Bill Buchanan A. write terminal B. show running-configuration C. show all-configuration D. show configuration 119. What platforms support CBAC? (choose all that apply) Author: Bill Buchanan A. PIX 515 B. 1600 C. PIX 506 D. 2500 120. By default what are the two interface names on the PIX Firewall? (choose 2) Author: Bill Buchanan A. Ethernet B. DMZ C. Serial D. 100Mb E. Inside F. Outside 121. What command clears the IPSec security associations? Author: Bill Buchanan A. clear ipsec sa B. clear security-associations C. clear ipsec D. clear sa 122. How does activex blocking affect activex traffic to servers identified by an alias command? Author: Bill Buchanan A. Allows activex traffic to the server B. Inspects the activex applet from the servers C. Does not block activex traffic from the server D. Blocks all activex traffic from the server Test 1 Author: Bill Buchanan Author: Prof Bill Buchanan 1. In which type of attack does the potential intruder attempt to discover and map out systems, services, and vulnerabilities? stake out reconnaissance tapping sniffing Author: Bill Buchanan A B C D 1. In which type of attack does the potential intruder attempt to discover and map out systems, services, and vulnerabilities? stake out reconnaissance tapping sniffing Author: Bill Buchanan A B C D 2. Which type of attack prevents a user from accessing the targeted file server? Reconnaissance attack Denial of service attack Prevention of entry attack Disruption of structure attack Author: Bill Buchanan A B C D 2. Which type of attack prevents a user from accessing the targeted file server? Reconnaissance attack Denial of service attack Prevention of entry attack Disruption of structure attack Author: Bill Buchanan A B C D 3. Which type of action does the "ping sweep" pose to an organization? eavesdropping reconnaissance denial of service unauthorized access Author: Bill Buchanan A B C D 3. Which type of action does the "ping sweep" pose to an organization? eavesdropping reconnaissance denial of service unauthorized access Author: Bill Buchanan A B C D 3. Which type of action does the "ping sweep" pose to an organization? eavesdropping reconnaissance denial of service unauthorized access Author: Bill Buchanan A B C D 4. An employee of ABC Company receives an e-mail from a co-worker with an attachment. The employee opens the attachment and receives a call from the network administrator a few minutes later, stating that the employee's machine has been attacked and is sending SMTP messages. Which category of attack is this? denial of service trojan horse port scanning password attack social engineering Author: Bill Buchanan A B C D E 4. An employee of ABC Company receives an e-mail from a co-worker with an attachment. The employee opens the attachment and receives a call from the network administrator a few minutes later, stating that the employee's machine has been attacked and is sending SMTP messages. Which category of attack is this? denial of service trojan horse port scanning password attack social engineering Author: Bill Buchanan A B C D E 5. What is a major characteristic of a Worm? Author: Bill Buchanan A malicious software that copies itself into other executable programs B tricks users into running the infected software C a set of computer instructions that lies dormant until triggered by a specific event D exploits vulnerabilities with the intent of propagating itself across a network 5. What is a major characteristic of a Worm? Author: Bill Buchanan A malicious software that copies itself into other executable programs B tricks users into running the infected software C a set of computer instructions that lies dormant until triggered by a specific event D exploits vulnerabilities with the intent of propagating itself across a network 6. A large investment firm has been attacked by a worm. In which order should the network support team perform the steps to mitigate the attack? A B C D E C,A,D,B A,B,C,D A,C,B,D D,A,C,B C,B,A,D Author: Bill Buchanan A. inoculation B. treatment C. containment D. quarantine 6. A large investment firm has been attacked by a worm. In which order should the network support team perform the steps to mitigate the attack? A B C D E C,A,D,B A,B,C,D A,C,B,D D,A,C,B C,B,A,D Author: Bill Buchanan A. inoculation B. treatment C. containment D. quarantine At XYZ Company, the policy for network use requires that employees log in to a Windows domain controller when they power on their work computers. Although XYZ does not implement all possible security measures, outgoing traffic is filtered using a firewall. Which security model is the company using? A B C D open access closed access hybrid access restrictive access Author: Bill Buchanan 7 At XYZ Company, the policy for network use requires that employees log in to a Windows domain controller when they power on their work computers. Although XYZ does not implement all possible security measures, outgoing traffic is filtered using a firewall. Which security model is the company using? A B C D open access closed access hybrid access restrictive access Author: Bill Buchanan 7 8 Which three of these are common causes of persistent vulnerabilities in networks? (Choose three.) new exploits in existing software misconfigured hardware or software poor network design changes in the TCP/IP protocol changes in the core routers on the Internet end-user carelessness Author: Bill Buchanan A B C D E F 8 Which three of these are common causes of persistent vulnerabilities in networks? (Choose three.) new exploits in existing software misconfigured hardware or software poor network design changes in the TCP/IP protocol changes in the core routers on the Internet end-user carelessness Author: Bill Buchanan A B C D E F 9. A new network administrator is assigned the task of conducting a risk assessment of the company's network. The administrator immediately conducts a vulnerability assessment. Which important task should the administrator have completed first? threat identification security level application patch and update deployment asset identification perimeter security upgrade Author: Bill Buchanan A B C D E 9. A new network administrator is assigned the task of conducting a risk assessment of the company's network. The administrator immediately conducts a vulnerability assessment. Which important task should the administrator have completed first? threat identification security level application patch and update deployment asset identification perimeter security upgrade Author: Bill Buchanan A B C D E 10.A company deployed a web server on the company DMZ to provide external web services. While reviewing firewall log files, the administrator discovered that a connection was made to the internal e-mail server from the web server in DMZ. After reviewing the e-mail server logs, the administrator discovered that an unauthorized account was created. What type of attack was successfully carried out? phishing port redirection trust exploitation man-in-the-middle Author: Bill Buchanan A B C D 10.A company deployed a web server on the company DMZ to provide external web services. While reviewing firewall log files, the administrator discovered that a connection was made to the internal e-mail server from the web server in DMZ. After reviewing the e-mail server logs, the administrator discovered that an unauthorized account was created. What type of attack was successfully carried out? phishing port redirection trust exploitation man-in-the-middle Author: Bill Buchanan A B C D 11.Users are unable to access a company server. The system logs show that the server is operating slowly because it is receiving a high level of fake requests for service. Which type of attack is occurring? reconnaissance access DoS worms, viruses, and Trojan horses Author: Bill Buchanan A B C D 11.Users are unable to access a company server. The system logs show that the server is operating slowly because it is receiving a high level of fake requests for service. Which type of attack is occurring? reconnaissance access DoS worms, viruses, and Trojan horses Author: Bill Buchanan A B C D 12.Which two are examples of Distributed Denial of Service attacks? (Choose two.) SYN Flood Stacheldraht Ping of Death Smurf WinNuke Targa.c Author: Bill Buchanan A B C D E F 12.Which two are examples of Distributed Denial of Service attacks? (Choose two.) SYN Flood Stacheldraht Ping of Death Smurf WinNuke Targa.c Author: Bill Buchanan A B C D E F 13.Which two of these are examples of DDoS network attacks? (Choose two.) smurf attack Tribal Flood Network (TFN) teardrop.c man-in-the-middle attack port redirection social engineering Author: Bill Buchanan A B C D E F 13.Which two of these are examples of DDoS network attacks? (Choose two.) smurf attack Tribal Flood Network (TFN) teardrop.c man-in-the-middle attack port redirection social engineering Author: Bill Buchanan A B C D E F 14.Which Cisco tool can be used to convert Cisco PIX Security Appliance conduit statements to equivalent access-list statements? Cisco AutoSecure Output Interpreter Cisco Router Audit Tool Microsoft Baseline Security Analyzer PIX Outbound/Conduit Conversion Tool Author: Bill Buchanan A B C D E 14.Which Cisco tool can be used to convert Cisco PIX Security Appliance conduit statements to equivalent access-list statements? Cisco AutoSecure Output Interpreter Cisco Router Audit Tool Microsoft Baseline Security Analyzer PIX Outbound/Conduit Conversion Tool Author: Bill Buchanan A B C D E 15.Which tool is used to test security by rapidly performing a port scan of a single host or a range of hosts? Cisco Router Audit Tool (RAT) Microsoft Baseline Security Analyzer Network Mapper (Nmap) Cisco AutoSecure Author: Bill Buchanan A B C D 15.Which tool is used to test security by rapidly performing a port scan of a single host or a range of hosts? Cisco Router Audit Tool (RAT) Microsoft Baseline Security Analyzer Network Mapper (Nmap) Cisco AutoSecure Author: Bill Buchanan A B C D 16.Which two are technological weaknesses that can lead to a breach in an organization's security? (Choose two.) software compatibility weakness DHCP security weakness TCP/IP protocol weakness operating system weakness LDAP weakness Author: Bill Buchanan A B C D E 16.Which two are technological weaknesses that can lead to a breach in an organization's security? (Choose two.) software compatibility weakness DHCP security weakness TCP/IP protocol weakness operating system weakness LDAP weakness Author: Bill Buchanan A B C D E Test 2 Author: Bill Buchanan Author: Prof Bill Buchanan 1 What is the effect of applying this command to a Cisco router? router(config)# no service finger UNIX commands are disabled on the router. All TCP/IP services are disabled. PING usage is disabled. Users logged into the router remotely will not be able to see if other users are logged into the router. Author: Bill Buchanan A B C D 2 Why does SSH provide better security than Telnet? Author: Bill Buchanan A SSH compresses data while Telnet does not compress data. B SSH encrypts data with private key while Telnet uses public key. C SSH encrypts data while Telnet uses clear text in transmitting data. D SSH encrypts data with public key while Telnet uses hashing algorithm. 2 Why does SSH provide better security than Telnet? Author: Bill Buchanan A SSH compresses data while Telnet does not compress data. B SSH encrypts data with private key while Telnet uses public key. C SSH encrypts data while Telnet uses clear text in transmitting data. D SSH encrypts data with public key while Telnet uses hashing algorithm. 3 The network administrator of company XYZ likes to secure routers by disabling the password recovery procedure for anyone who gains physical access to the router. Which command would be used to achieve this goal? router(config)# no rommon-mode router(config)# no password-recovery router(config)# no service password-recovery router(config)# no rommon-password recovery Author: Bill Buchanan A B C D 3 The network administrator of company XYZ likes to secure routers by disabling the password recovery procedure for anyone who gains physical access to the router. Which command would be used to achieve this goal? router(config)# no rommon-mode router(config)# no password-recovery router(config)# no service password-recovery router(config)# no rommon-password recovery Author: Bill Buchanan A B C D 4 A partial router configuration is shown in the graphic. The network administrator adds the following command at the router prompt. A B C D Which of the following is correct? The current password will continue to be used as a valid password until changed. No password is required. The current password is invalid and will not allow a login. A password that is at least ten characters long must immediately be implemented for a successful login. version 12.3 hostname router line con 0 line aux 0 line vty 0 4 login password cisco Author: Bill Buchanan router(config)# security passwords min-length 10 4 A partial router configuration is shown in the graphic. The network administrator adds the following command at the router prompt. A B C D Which of the following is correct? The current password will continue to be used as a valid password until changed. No password is required. The current password is invalid and will not allow a login. A password that is at least ten characters long must immediately be implemented for a successful login. version 12.3 hostname router line con 0 line aux 0 line vty 0 4 login password cisco Author: Bill Buchanan router(config)# security passwords min-length 10 Which two steps are necessary to ensure that your HIDS and HIPS do not miss any exploits? (Choose two.) A upgrade the HIDS and HIPS software as new versions are released perform periodic vulnerability assessment monitor alerts and logs update signatures on a regular basis ensure that all security patches are loaded on the host machine B C D E Author: Bill Buchanan 5 Which two steps are necessary to ensure that your HIDS and HIPS do not miss any exploits? (Choose two.) A upgrade the HIDS and HIPS software as new versions are released perform periodic vulnerability assessment monitor alerts and logs update signatures on a regular basis ensure that all security patches are loaded on the host machine B C D E Author: Bill Buchanan 5 6 The Security Wheel promotes a continuous process to retest and reapply updated security measures. What is the core or “hub” component of the Security Wheel? testing policy monitor improve security policy Author: Bill Buchanan A B C D 6 The Security Wheel promotes a continuous process to retest and reapply updated security measures. What is the core or “hub” component of the Security Wheel? testing policy monitor improve security policy Author: Bill Buchanan A B C D After providing for all operational requirements of the network, the network support team has determined that the servers should be hardened against security threats so that the network can operate at full potential. At which stage of the network life cycle does server hardening occur? A B C D E planning design implementation operation optimization Author: Bill Buchanan 7 After providing for all operational requirements of the network, the network support team has determined that the servers should be hardened against security threats so that the network can operate at full potential. At which stage of the network life cycle does server hardening occur? A B C D E planning design implementation operation optimization Author: Bill Buchanan 7 8 What are three major functions performed by the security management subsystem, CiscoWorks VMS? (Choose three.) Author: Bill Buchanan A to manage access control lists for Cisco PIX Security Appliances B to enforce access control policies between two processes running on a server C to capture and analyze network traffic, and respond to network intrusions D to identify sensitive network resources E to respond to first-stage denial of service network attacks F to monitor and log access to network resources 8 What are three major functions performed by the security management subsystem, CiscoWorks VMS? (Choose three.) Author: Bill Buchanan A to manage access control lists for Cisco PIX Security Appliances B to enforce access control policies between two processes running on a server C to capture and analyze network traffic, and respond to network intrusions D to identify sensitive network resources E to respond to first-stage denial of service network attacks F to monitor and log access to network resources 9 A network administrator has just completed security training and has decided to change from HIDS to HIPS to protect hosts. Which of these would be a major advantage gained from the change? Author: Bill Buchanan A HIPS does not require host-based client software. B HIPS would prevent the need to update signature files as often. C HIPS would be able to prevent intrusions. D HIPS would consume fewer system resources. 9 A network administrator has just completed security training and has decided to change from HIDS to HIPS to protect hosts. Which of these would be a major advantage gained from the change? Author: Bill Buchanan A HIPS does not require host-based client software. B HIPS would prevent the need to update signature files as often. C HIPS would be able to prevent intrusions. D HIPS would consume fewer system resources. 10 A network administrator installs a new stateful firewall. Which type of security solution is this? Author: Bill Buchanan A secure connectivity B threat defense C policy enforcement D trust and identity E authentication 10 A network administrator installs a new stateful firewall. Which type of security solution is this? Author: Bill Buchanan A secure connectivity B threat defense C policy enforcement D trust and identity E authentication 11 XYZ Company recently adopted software for installation on critical servers that will detect malicious attacks as they occur. In addition, the software will stop the execution of the attacks and send an alarm to the network administrator. Which technology does this software utilize? Author: Bill Buchanan A host-based intrusion detection B host-based intrusion protection C host-based intrusion prevention D host-based intrusion notification 11 XYZ Company recently adopted software for installation on critical servers that will detect malicious attacks as they occur. In addition, the software will stop the execution of the attacks and send an alarm to the network administrator. Which technology does this software utilize? Author: Bill Buchanan A host-based intrusion detection B host-based intrusion protection C host-based intrusion prevention D host-based intrusion notification 12 A security team is charged with hardening network devices. What must be accomplished first before deciding how to configure security on any device? Author: Bill Buchanan A Audit all relevant network devices. B Document all router configurations. C Create or update security policies. D Complete a vulnerability assessment. 12 A security team is charged with hardening network devices. What must be accomplished first before deciding how to configure security on any device? Author: Bill Buchanan A Audit all relevant network devices. B Document all router configurations. C Create or update security policies. D Complete a vulnerability assessment. 13 On a Monday morning, network engineers notice that the log files on the central server are larger than normal. Examining the log reveals that the majority of the entries are from sensors deployed on the perimeter of the network. The logs reveal that a worm attack was successfully stopped by the perimeter devices. Based on this information, which of these technologies is this company using? Author: Bill Buchanan A NIDS using passive technology B HIPS using passive technology C NIDS using active technology D HIDS using passive technology E HIPS using active technology 13 On a Monday morning, network engineers notice that the log files on the central server are larger than normal. Examining the log reveals that the majority of the entries are from sensors deployed on the perimeter of the network. The logs reveal that a worm attack was successfully stopped by the perimeter devices. Based on this information, which of these technologies is this company using? Author: Bill Buchanan A NIDS using passive technology B HIPS using passive technology C NIDS using active technology D HIDS using passive technology E HIPS using active technology 14 Which two objectives must a security policy accomplish? (Choose two.) Author: Bill Buchanan A provide a checklist for the installation of secure servers B describe how the firewall must be configured C document the resources to be protected D identify the security objectives of the organization E identify the specific tasks involved in hardening a router 14 Which two objectives must a security policy accomplish? (Choose two.) Author: Bill Buchanan A provide a checklist for the installation of secure servers B describe how the firewall must be configured C document the resources to be protected D identify the security objectives of the organization E identify the specific tasks involved in hardening a router 15 Which router command will result in the router only accepting passwords of 16 characters or more? Author: Bill Buchanan A service password-encryption B enable secret min-length 16 C security passwords min-length 16 D security passwords max-length 16 15 Which router command will result in the router only accepting passwords of 16 characters or more? Author: Bill Buchanan A service password-encryption B enable secret min-length 16 C security passwords min-length 16 D security passwords max-length 16 16 Which command will encrypt all passwords in the router configuration file? Author: Bill Buchanan A enable secret B password encrypt all C enable password-encryption D service password-encryption E no clear-text password 16 Which command will encrypt all passwords in the router configuration file? Author: Bill Buchanan A enable secret B password encrypt all C enable password-encryption D service password-encryption E no clear-text password 17 MD5 can be used for authenticating routing protocol updates for which three protocols? (Choose three.) Author: Bill Buchanan A RIPv1 B RIPv2 C IGRP D EIGRP E BGP 17 MD5 can be used for authenticating routing protocol updates for which three protocols? (Choose three.) Author: Bill Buchanan A RIPv1 B RIPv2 C IGRP D EIGRP E BGP Which configuration will allow an administrator to access the console port using a password of password? A router(config)# line aux 0 router(config-line)# login router(config-line)# password password router(config)# line console 0 router(config-line)# login router(config-line)# password password router(config)# line console 0 router(config-line)# password password D router(config)# line console 0 router(config-line)# access router(config-line)# password password router(config)# line vty 0 router(config-line)# password password router(config)# line vty 0 router(config-line)# access router(config-line)# password password B C D E F Author: Bill Buchanan 18 Which configuration will allow an administrator to access the console port using a password of password? A router(config)# line aux 0 router(config-line)# login router(config-line)# password password router(config)# line console 0 router(config-line)# login router(config-line)# password password router(config)# line console 0 router(config-line)# password password D router(config)# line console 0 router(config-line)# access router(config-line)# password password router(config)# line vty 0 router(config-line)# password password router(config)# line vty 0 router(config-line)# access router(config-line)# password password B C D E F Author: Bill Buchanan 18 19 Which command sets the inactivity timer, for a particular line or group of lines, to four minutes and fifteen seconds? router(config)# line-timeout 4 15 router(config-line)# line-timeout 4 15 router(config-line)# exec-timeout 255 router(config-line)# timeout 255 router(config-line)# exec-timeout 4 15 router(config-line)# line-timeout 255 Author: Bill Buchanan A B C D E F 19 Which command sets the inactivity timer, for a particular line or group of lines, to four minutes and fifteen seconds? router(config)# line-timeout 4 15 router(config-line)# line-timeout 4 15 router(config-line)# exec-timeout 255 router(config-line)# timeout 255 router(config-line)# exec-timeout 4 15 router(config-line)# line-timeout 255 Author: Bill Buchanan A B C D E F 20 Which encryption type uses the MD5 hash algorithm? Author: Bill Buchanan A Type 0 B Type 1 C Type 5 D Type 7 20 Which encryption type uses the MD5 hash algorithm? Author: Bill Buchanan A Type 0 B Type 1 C Type 5 D Type 7 21 Real-time intrusion detection occurs at which stage of the Security Wheel? Author: Bill Buchanan A securing stage B monitoring stage C testing stage D improvement stage E reconnaissance stage 21 Real-time intrusion detection occurs at which stage of the Security Wheel? Author: Bill Buchanan A securing stage B monitoring stage C testing stage D improvement stage E reconnaissance stage 22 Which privilege level has the most access to the Cisco IOS? Author: Bill Buchanan A level 0 B level 1 C level 7 D level 15 E level 16 F level 20 22 Which privilege level has the most access to the Cisco IOS? Author: Bill Buchanan A level 0 B level 1 C level 7 D level 15 E level 16 F level 20 Author: Bill Buchanan Which algorithm implements stateful connection control through the PIX Security Appliance? A B C D E Network Address Translation Algorithm Access Control Security Algorithm Adaptive Security Algorithm Spanning Tree Protocol Algorithm Author: Bill Buchanan 1 Once the SDM startup wizard has been completed for the first time, which two are required on a host PC for connection to the Cisco router via HTTP or HTTPS using SDM? (Choose two.) A B C D E F IP address from 10.10.10.2 to 10.10.10.254 IP address from 10.0.0.2 to 10.0.0.254 IP address from 10.10.10.1 to 10.10.10.254 SSL capability Java and JavaScript enabled on the browser VPN connection Author: Bill Buchanan 2 The Cisco Security Device Manager (SDM) allows administrators to securely configure supported routers by using which security protocol in Microsoft Internet Explorer? A B C D E IPSec SSL SSH L2TP PPTP Author: Bill Buchanan 3 The network administrator for a small technology firm needs to implement security on the network. The administrator needs a PIX Security Appliance that will handle three Ethernet interfaces. Which PIX model would be the best choice for the company? A B C D 506E 515E 525 535 Author: Bill Buchanan 4 What is the maximum number of licensed users supported by the Cisco 501 Security Appliance? A B C D E F 25 100 250 1000 2500 unlimited Author: Bill Buchanan 5 A network administrator has received a Cisco PIX Security Appliance from another division within the company. The existing configuration has IP addresses that will cause problems on the network. What command sequence will successfully clear all the existing IP addresses and configure a new IP address on ethernet0? A pix1(config)# clear ip all pix1(config)# interface ethernet0 pix1(config-if)# ip address 192.168.1.2 pix1(config)# clear ip pix1(config)# interface ethernet0 pix1(config-if)# ip address 192.168.1.2 255.255.255.0 pix1(config)# no ip address pix1(config)# interface ethernet0 pix1(config-if)# ip address 192.168.1.2 255.255.255.0 pix1(config)# clear ip pix1(config)# interface ethernet0 pix1(config-if)# ip address 192.168.1.2 0.0.0.255 B C D Author: Bill Buchanan 6 A network team is configuring a Cisco PIX Security Appliance for NAT so that local addresses are translated. The team is creating a global address pool using a subnet of network 192.168.5.0 with a 27-bit mask. What is the proper syntax to set up this global address pool? A B C D E F pix1(config)# global (inside) 1 192.168.5.33-192.168.5.62 pix1(config)# global (outside) 1 192.168.5.33-192.168.5.62 pix1(config)# global (inside) 1 192.168.5.65-192.168.5.95 pix1(config)# global (outside) 1 192.168.5.65-192.168.5.95 pix1(config)# global (inside) 1 192.168.5.64-192.168.5.127 pix1(config)# global (outside) 1 192.168.5.65-192.168.5.127 Author: Bill Buchanan 7 8 Which command displays the value of the activation key? write net show version show terminal show configure Author: Bill Buchanan A B C D A network administrator has configured an access control list on the Cisco PIX Security Appliance that allows inside hosts to ping outside hosts for troubleshooting. Which debug command can be used to troubleshoot if pings between hosts are not successful? A B C D debug icmp inside outside debug ping debug icmp trace debug trace icmp Author: Bill Buchanan 9 10 Which protocol provides time synchronization? STP TSP NTP SMTP L2TP Author: Bill Buchanan A B C D E 11 Which command would configure a PIX Security Appliance to send syslog messages from its inside interface to a syslog server with the IP address of 10.0.0.3? pixfirewall(config)# pixfirewall(config)# pixfirewall(config)# pixfirewall(config)# syslog inside 10.0.0.3 logging inside 10.0.0.3 syslog host inside 10.0.0.3 logging host inside 10.0.0.3 Author: Bill Buchanan A B C D 12 The configuration in the graphic has been entered into a PIX Security Appliance with three interfaces. The interfaces are inside, outside, and DMZ. What source address range will the traffic from inside devices use when they access devices in the DMZ? 10.0.0.1 to 10.0.0.254 172.16.0.20 to 172.16.0.254 172.16.0.1 to 172.16.0.254 192.168.0.20 to 192.168.0.254 10.0.0.1 to 10.255.255.254 Author: Bill Buchanan A B C D E 13 What source IP address will the traffic from devices in the 10.0.2.0 network have when they leave the trusted network? D 192.168.0.8 always 192.168.0.9 always 192.168.0.8 if ports are available, or 192.168.0.9 if 192.168.0.8's ports are exhausted 192.168.0.9 if ports are available, or 192.168.0.8 if 192.168.0.9's ports are exhausted Author: Bill Buchanan A B C 14 The commands in the graphic have been entered into a PIX Security Appliance. Which two statements are accurate descriptions of what will happen to outgoing traffic when it leaves the trusted network? (Choose two.) B C D E The source IP address will be from a pool of addresses in the 192.168.0.3 to 192.168.0.254 range. The source port will be a random port above port 1023. The source IP address will be 192.168.0.2 for all outgoing traffic. The source port will be port 1024. The source IP address will be in the range 10.0.0.1 to 10.0.255.254. Author: Bill Buchanan A 15 Which three are requested by the Cisco PIX Security Appliance setup dialog? (Choose three.) domain name outside IP address inside IP address hostname date and time Author: Bill Buchanan A B C D E 16 Interface Ethernet3 on a PIX Security Appliance has been configured with three subinterfaces to pass tagged traffic from three different VLANs. What protocol will be used to tag the VLAN traffic? ISL 802.1x VTP 802.1q Author: Bill Buchanan A B C D 17 Which two commands will configure a static default route on the PIX Security Appliance in the network shown in the graphic? (Choose two.) route inside outside 0.0.0.0 0.0.0.0 172.16.0.2 1 route outside 0.0.0.0 0.0.0.0 172.16.0.2 1 ip route inside outside 0 0 192.168.0.2 1 route outside 0 0 172.16.0.2 1 ip route inside outside 0 0 172.16.0.2 1 route outside 0 0 192.168.0.2 1 Author: Bill Buchanan A B C D E F 18 Which command will produce output, similar to that shown in the graphic, to verify the installation of a FWSM on a router? show port show module show firewall show interface Author: Bill Buchanan A B C D Author: Bill Buchanan Test 4 How are transactions between a RADIUS client and a RADIUS server authenticated? A by using a shared secret which is never sent over the network by hashing the secret using MD5 and then sending it over the network by hashing the secret using MD4 and then sending it over the network by using a clear-text password and then sending it over the network B C D Author: Bill Buchanan 1 2 The S/KEY system involves three main components. There is a client and a host. What is the third component? A B C D a plain text password a password calculator a public and private key biometric authentication Author: Bill Buchanan Client, host, password calculator 3 RADIUS uses which transport layer protocol? IP TCP UDP ICMP DLC Author: Bill Buchanan A B C D E 4 Which authentication method is susceptible to playback attacks? passwords using S/KEY passwords using token card passwords requiring periodic change passwords using one-time password technology Author: Bill Buchanan A B C D 5 Which authentication method sends passwords over the network in clear text yet protects against eavesdropping and password cracking attacks? authentication with FTP authentication with Telnet authentication with S/KEY authentication in POP3 e-mail Author: Bill Buchanan A B C D After a security audit, network managers realized that the authentication method used by their telecommuting employees needed to be improved. They set up a server and installed client software on the employee laptops of their remote users. They also provided a device for each remote user that generated a password every time they needed to make a remote network connection. Which A B C D authentication technology does this process describe? authentication with S/KEY authentication with token card authentication with encrypted password authentication with compressed password Author: Bill Buchanan 6 7 What function does a digital certificate offer to information security? authorization accounting nonrepudiation intrusion prevention Author: Bill Buchanan A B C D Bookline Inc., an online bookstore, recently installed a web server running Microsoft Windows 2003 Server. Where should the company obtain a digital signature for the web server in order to assure customers that they are connecting to Bookline's server and not an impersonating web server? A a digital signature generated by the CA in Microsoft's corporate headquarters a digital signature generated by the CA from a trusted third party a digital signature generated by the CA from a government agency a digital signature generated by any CA that establishes a secure connection B C D Author: Bill Buchanan 8 A large law firm wishes to secure dialup access to its corporate network for employees working at home. Since much of the data to be transmitted is highly confidential, the firm requires a high level of encryption and also prefers that each component of AAA be provided separately. Which security protocol best meets these requirements? A B C D TACACS XTACACS TACACS+ RADIUS Author: Bill Buchanan 9 10 Which two statements are true of Cisco Identity Based Networking Services (IBNS)? (Choose two.) Cisco IBNS uses Cisco-proprietary protocols. Cisco IBNS is a standards-based solution. Cisco IBNS associates users with physical ports. Cisco IBNS associates policies with physical ports. Cisco IBNS associates policies with users. Author: Bill Buchanan A B C D E 11 The administration manager has decided to implement Network Admission Control (NAC) on the corporate network. The Cisco Trust Agent software and NAC-compliant routers and switches have been installed. Which two additional NAC components are required to implement the NAC solution? (Choose two.) access control policy server TACACS+ server NAC cosponsor application server VPN systems remote access server posture validation management system Author: Bill Buchanan A B C D E F 12 What are three reasons TACACS+ is preferred over RADIUS for authentication services? (Choose three.) E F RADIUS has limited name space for attributes. RADIUS is not an industry supported standard. TACACS+ encrypts the entire TACACS+ packet. TACACS+ authentication is included with more recent Windows Server versions. TACACS+ separates authentication and authorization. RADIUS uses TCP as a transport protocol creating additional overhead. Author: Bill Buchanan A B C D 13 A static username/password authentication method is susceptible to which three types of attacks? (Choose three.) playback theft teardrop syn flood eavesdropping Author: Bill Buchanan A B C D E 14 Company security policy requires the use of a centralized AAA server for network access authentication. Which two protocols are supported by the AAA server? (Choose two.) IPSec SSL RADIUS TACACS+ SSH Author: Bill Buchanan A B C D E 15 Which three are functions of AAA? (Choose three.) accounting availability authentication architecture authorization accessibility Author: Bill Buchanan A B C D E F Test 4 16 A network administrator wishes to use port-level authentication technology to determine network access and assign IP addresses from different DHCP pools to authenticated and unauthenticated users. What standardized framework supports this objective? IEEE 802.1x IEEE 802.11af IEEE 802.1q IEEE 802.1p Author: Bill Buchanan A B C D Author: Bill Buchanan Test 5 Test 5 1 What will be the result of executing the command in the graphic? Author: Bill Buchanan A The default login method will use TACACS+ only. B TACACS+ accounting will be enabled at login. C The enable password will be used if a TACACS+ server is not available. D The default TACACS+ user shell will be enabled. 2 A network administrator is setting up a computer to run Cisco Secure ACS to support a Cisco VPN 3000 concentrator. Which protocol does the administrator need to enable on CSACS? A B C D E MD5 HMAC RADIUS TACACS+ IEEE 802.1X Author: Bill Buchanan Test 5 3 Which AAA service reduces IT operating costs by providing detailed reporting and monitoring of network user behavior, and also by keeping a record of every access connection and device configuration change across the network? A B C D authentication accreditation accounting authorization Author: Bill Buchanan Test 5 4 Cisco Secure ACS can use a number of databases for username and password authentication. Which three databases does Cisco Secure ACS support? (Choose three.) A B C D E Windows 2000 server user database NDS database Windows 2000 server authentication database Microsoft Access database Cisco Secure ACS user database Author: Bill Buchanan Test 5 5 After Cisco Secure ACS is implemented, users report that they are restricted from accessing the network. The Cisco Secure ACS switches and routers are communicating properly. What is the first step for troubleshooting the problem? A B Execute debug commands on the router. Check the available logs in CSACS Reports and Activity for abnormalities. Verify that the administrator has an account allowing remote access to the CSACS. Verify that the CSACS user database is enabled. C D Author: Bill Buchanan Test 5 Test 5 6 What tool should you use to add a single user account to the Cisco Secure ACS for Windows user database? database replication Unknown User Policy RDBMS Synchronization Cisco Secure ACS HTML interface Author: Bill Buchanan A B C D 7 Which two actions are available when using the Cisco Secure ACS database replication features? (Choose two.) A update of configuration items from a late release to an earlier release of Cisco Secure ACS bidirectional database replication between a primary and a secondary Cisco Secure ACS scheduled replication of part of the database from a primary to a secondary Cisco Secure ACS export of configuration items from a primary to a secondary Cisco Secure ACS B C D Author: Bill Buchanan Test 5 8 Refer to the exhibit. Which two services can the network access server use to direct requests from the remote user to the Cisco Secure ACS authentication service? (Choose two.) A B C D E CSAuth CSUtil RADIUS RDBMS TACACS+ Author: Bill Buchanan Test 5 Test 5 9 RTA(config)# tacacs-server key 2bor!2b@? RTA(config)# tacacs-server host 10.1.2.4 RTA(config)# tacacs-server host 10.1.2.5 What will be the effect of these commands on router RTA? B C D The TACACS+ server is now authenticating for the hosts 10.1.2.4 and 10.1.2.5. The TACACS+ server key has been exported to the hosts 10.1.2.4 and 10.1.2.5. The TACACS+ servers 10.1.2.4 and 10.1.2.5 and the router have been set to share the same authentication key. The TACACS+ servers are 10.1.2.4 and 10.1.2.5 and the configuration adds router RTA as a third TACACS+ server Author: Bill Buchanan A Test 5 10 RTA(config)# aaa new-model RTA(config)# aaa authentication login default group tacacs+ enable After entering the configuration shown, the administrator loses the connection to the router before having the chance to create a new TACACS+ account. What is the easiest way for the administrator to regain administrative access to router RTA? B C D Connect to the router, and use the default TACACS+ username and password. Erase NVRAM, and redo the configuration from scratch. Connect to the router, and supply the enable password. Perform a password recovery procedure on the router. Author: Bill Buchanan A Test 5 11 Which two user databases does Cisco Secure ACS for Windows use to authenticate users? (Choose two.) external user database with appropriate API RADIUS user database TACACS+ user database Windows 2000 Server user database Windows XP user database Author: Bill Buchanan A B C D E Test 5 12 An information technology organization uses Cisco Secure ACS for Windows Server version 3.2. The system administrators want to provide a method for users to change their own passwords without intervention from the IT organization. What is required to allow users to change passwords with a web-based utility? Enable UCP on Windows 2000 Server. Configure a Microsoft IIS 4.0 or later. Enable UCP on Cisco Secure ACS for Windows. Configure IIS logging with the user Secure ACS password. Author: Bill Buchanan A B C D Test 5 13 Which tool is used to set up CSACS for Windows Server after the initial installation is completed? web browser telnet session command line interface on the Windows server router configured as an AAA client Author: Bill Buchanan A B C D Test 5 14 Which basic user-network security protocol is supported by Cisco Secure ACS and requires a single log in by users? CHAP IPSec RADIUS PAP Author: Bill Buchanan A B C D Test 5 15 In the Cisco Secure ACS Windows architecture CSRadius provides communication between RADIUS AAA clients and which service? CSAdmin CSAuth CSLog CSMon Author: Bill Buchanan A B C D Test 5 16 There are five ways to create user accounts in the Cisco Secure ACS for Windows 2000 Servers. Which two support importing user accounts from external sources? (Choose two.) Cisco Secure ACS HTML interface Unknown User Policy RDBMS Synchronization CSUtil.exe Database Replication Author: Bill Buchanan A B C D E Author: Bill Buchanan Test 6 1 Which command associates the group MYGROUP with the AAA server using the TACACS+ protocol? A B C D Pixfirewall(config)# aaa-server MYGROUP tacacs+ protocol Pixfirewall(config)# aaa-server protocol tacacs+ MYGROUP Pixfirewall(config)# aaa-server tacacs+ protocol MYGROUP Pixfirewall(config)# aaa-server MYGROUP protocol tacacs+ Author: Bill Buchanan Test 6 2 Which configuration command defines the association of initiating HTTP protocol traffic with an authentication proxy name MYPROXY? A B C D Router(config)# ip auth-proxy MYPROXY http Router(config)# auth-proxy MYPROXY ip http Router(config)# ip auth-proxy name MYPROXY http Router(config)# auth-proxy name MYPROXY ip http Author: Bill Buchanan Test 6 Test 6 3 With the following configuration command, how long does the PIX Security Appliance try to access the AAA server 10.0.1.10 before choosing the next AAA server if there is no response from 10.0.1.10? aaa-server MYTACACS (inside) host 10.0.1.10 secretkey 12 seconds 15 seconds 20 seconds 30 seconds Author: Bill Buchanan A B C D Test 6 4 Which command will enable AAA services on a router? Router(config)# aaa enable Router(config)# aaa new-model Router(config)# aaa set enable Router(config)# aaa new-model enable Author: Bill Buchanan A B C D 5 What is the default timeout in minutes for the inactivity-timer parameter of the ip auth-proxy command? A B C D E 15 30 45 60 90 Author: Bill Buchanan Test 6 Test 6 6 The network administrator configured the aaa authorization command below on the PIX Security Appliance. What is the effect of this command? pix(config)# aaa authorization include tcp/22 outside 0.0.0.0 0.0.0.0 0.0.0.0 0.0.0.0 auth1 FTP traffic from outside is subject to authorization by the AAA server. SSH traffic from outside is subject to authorization by the AAA server. HTTP traffic from outside is subject to authorization by the AAA server. SMTP traffic from outside is subject to authorization by the AAA server. Author: Bill Buchanan A B C D 7 Which type of authentication is being used when authentication is required via the PIX Security Appliance before direct traffic flow is allowed between users and the company web server? A B C D access authentication console access authentication cut-through proxy authentication tunnel access authentication Author: Bill Buchanan Test 6 Test 6 8 What will be the effect in the router after these configuration commands are entered? Router(config)# ip auth-proxy name aprule http Router(config)# interface ethernet0 Router(config-if)# ip auth-proxy aprule B C D An authentication proxy rule called aprule is created making all authentication proxy services available only through the ethernet0 interface. An authentication proxy rule called aprule has been created for the HTTP protocol and is associated with the ethernet0 interface. An authentication proxy rule called aprule has been created for all protocols except the HTTP protocol and is associated with the ethernet0 interface. An authentication proxy rule called aprule has been created for the HTTP server running internally to the router and is associated with anyone attempting to access the web server from the ethernet0 interface. Author: Bill Buchanan A 9 When Cisco IOS Firewall authentication proxy is enabled, a user sends HTTP traffic which will trigger the authentication proxy. What is the first action taken by the proxy? A B The user will be asked to supply a valid username and password. The TACACS+ server will be contacted to see if the user is a valid user. The authentication proxy will check to see if the user has already been authenticated. If the authentication proxy has no user account for the user, it will check to see if a default guest user has been defined. C D Author: Bill Buchanan Test 6 10 A TACACS+ server is configured to provide authentication, authorization, and accounting. The IP address of the server is 192.168.50.1, and the AAA authentication encryption key is S3crtK3y. Which command sequence will configure a Cisco router to communicate with the TACACS+ server? A Router(config)# aaa new-model Router(config)# aaa authentication default group tacacs+ Router(config)# aaa authorization auth-proxy default group tacacs+ Router(config)# aaa tacacs-server host 192.168.50.1 Router(config)# aaa tacacs-server key S3crtK3y Router(config)# aaa enable Router(config)# aaa authentication default group tacacs+ Router(config)# aaa authorization auth-proxy default group tacacs+ Router(config)# tacacs-server host 192.168.50.1 Router(config)# tacacs-server key S3crtK3y Router(config)# aaa enable Router(config)# aaa authentication login default group tacacs+ Router(config)# aaa authorization auth-proxy default group tacacs+ Router(config)# aaa tacacs-server host 192.168.50.1 Router(config)# aaa tacacs-server key S3crtK3y Router(config)# aaa new-model Router(config)# aaa authentication login default group tacacs+ Router(config)# aaa authorization auth-proxy default group tacacs+ Router(config)# tacacs-server host 192.168.50.1 Router(config)# tacacs-server key S3crtK3y B C D Author: Bill Buchanan Test 6 11 The lead network administrator notices that unknown users have made router configuration changes. These changes are adversely affecting the network. Which command can be entered on the router to help identify future configuration changes and who made these changes? A B C D aaa accounting show uauth aaa accounting console aaa accounting match Author: Bill Buchanan Test 6 Test 6 12 Refer to the exhibit. Since ABC, Inc. is strengthening security, a PIX Security Appliance firewall must be configured with AAA services. Accounting should be provided for all FTP and HTTP traffic from any host to the WWW server at 192.168.2.10. Which command sequence would successfully process the desired traffic to the NY_ACS accounting server? B C C pixfirewall(config)# access-list 110 permit tcp any host 192.168.2.10 eq ftp pixfirewall(config)# access-list 110 permit tcp any host 192.168.2.10 eq http pixfirewall(config)# aaa accounting match 110 outside NY_ACS pixfirewall(config)# access-list 110 permit tcp any host 192.168.2.10 eq ftp pixfirewall(config)# access-list 110 permit tcp any host 192.168.2.10 eq http pixfirewall(config)# aaa accounting access-list 110 outside 10.0.0.2 pixfirewall(config)# access-list 110 permit tcp any host 10.0.0.2 eq ftp pixfirewall(config)# access-list 110 permit tcp any host 10.0.0.2 eq http pixfirewall(config)# aaa accounting match 110 outside NY_ACS pixfirewall(config)# access-list 110 permit tcp any host 192.168.2.10 eq ftp pixfirewall(config)# access-list 110 permit tcp any host 192.168.2.10 eq http pixfirewall(config)# aaa accounting match 110 outside 10.0.0.2 Author: Bill Buchanan A Test 6 13 Which command displays the current authenticated users, the host IP to which they are bound, and any cached IP and port authorization information on a Cisco PIX Security Appliance configured for AAA? pixfirewall(config)# pixfirewall(config)# pixfirewall(config)# pixfirewall(config)# show aaa all show uauth show aaa statistics show aaa-server Author: Bill Buchanan A B C D Test 6 14 Which two are functions of accounting on the PIX Security Appliance? (Choose two.) to track user activities on the PIX. to control administration of the PIX. to control user access to the PIX. to create records that are stored on a designated AAA server. to build and maintain tunnel sessions with the PIX. Author: Bill Buchanan A B C D E Test 6 15 Refer to the exhibit. An administrator enters the following configuration to collect accounting statistics for all HTTP traffic to the web server through a PIX Security Appliance. fwl(config)# access-list 110 permit tcp any host 192.168.0.2 eq www fwl(config)# aaa accounting match 110 outside Web_Server The statistics are to be logged to an accounting server as shown in the exhibit. However, after starting the accounting, no data is being logged to the NY_ACS server. D Author: Bill Buchanan A B C What changes to the configuration must the administrator make to correct the problem? Change “192.168.0.2” to “10.0.0.2” in the access-list configuration line. Change “host 192.168.0.2” to “any” in the access-list configuration line. Change “Web_Server” to “NY_ACS” in the aaa-accounting configuration line. Change “outside” to “inside” in the aaa-accounting configuration line. 16 A user has initiated an HTTP session through a firewall and has been authenticated by an authentication proxy. They have not generated any traffic in a while and the idle timer has expired for that user. What will the user have to do to allow them to go through the firewall again? A B C D The user can manually restart the idle timer. The user can simply TFTP their user profile to the proxy. The user must wait two minutes before initiating another session. The user can re-authenticate and initiate another HTTP session through the firewall. Author: Bill Buchanan Test 6 Author: Bill Buchanan Test 7 1 IEEE 802.1x can be used to authenticate users for wireless access to network resources. Which protocol has Cisco incorporated into its Wireless Security Suite to provide mutual authentication between the client and the authentication server? A B C D CHAP EAP PAP WEP Author: Bill Buchanan Test 7 2 Which two sections of Cisco Secure ACS can be used to configure RADIUS profiles? (Choose two.) A B C D E Interface Setup Server Setup Group Setup Network Setup User Setup Author: Bill Buchanan Test 7 Test 7 A B C D A network team has been tasked to develop a Cisco Secure ACS solution for port-based authentication. The network operation center for all three regions is located at Region 1. What is the best solution to ensure availability to a Cisco Secure ACS for port-based authentication? Install a centralized primary and secondary authentication server at Region 1, which Region 2 and 3 will use for authentication. Install a primary authentication server at each region and use one of the authentication servers from another region for redundancy. Install a primary authentication server at Region 1 for Region 2 and 3 to authenticate, and install a secondary authentication server at Region 2 and 3 for redundancy. Install a primary authentication server at each region and a secondary authentication server at Region 1 for the network operation center clients only. Author: Bill Buchanan 3 4 Port-based authentication is implemented as shown in the graphic. What protocol will be required for the client-toswitch connection and the switch-to-Cisco Secure ACS communications? A B C D ISL; RADIUS 802.1x; RADIUS 802.1q; TACACS+ L2TP; TACACS+ Author: Bill Buchanan Test 7 5 In configuring 802.1x authentication method with the aaa authentication dot1x command, at least one of which two possible options must be entered to create a default list when a named list is not specified on a Catalyst switch? (Choose two.) A B C D group tacacs+ group radius local none Author: Bill Buchanan Test 7 6 A network administrator wants to configure a Catalyst switch to use a RADIUS server at 172.16.23.31 or a backup RADIUS server at 172.16.23.32 if the first server is unavailable. The administrator wants to use the default RADIUS UDP port and a shared key of Rad4Me. Which configuration will accomplish this goal? A Switch(config)# radius-server auth-port 1812 key Rad4Me host 172.16.23.31 Switch(config)# radius-server auth-port 1812 key Rad4Me host 172.16.23.32 Switch(config)# radius-server host 172.16.23.31 auth-port 1812 key Rad4Me Switch(config)# radius-server host 172.16.23.32 auth-port 1812 key Rad4Me Switch(config)# radius-server host 172.16.23.31 172.16.23.32 key Rad4Me auth-port 1812 Switch(config)# radius-server host 172.16.23.31 key Rad4Me auth-port 1812 Switch(config)# radius-server host 172.16.23.32 key Rad4Me auth-port 1812 B C D Author: Bill Buchanan Test 7 7 The dot1x port-control auto interface configuration command has been configured on the Catalyst 2950 shown in the graphic. What is the effect of this command when the link between the switch and the end user becomes active? A The end user initiates authentication by sending an EAPOLstart frame once it receives an EAP request from the switch. The authentication server initiates authentication after being notified that the link is active. The switch initiates authentication with the end user. The switch automatically places the connected port in an authorized state. B C D Author: Bill Buchanan Test 7 8 Refer to the graphic. A small company purchased a Cisco Aironet access point to provide wireless connectivity to staff members. Since other companies in the office complex use wireless, the network support staff wants to be certain that only authorized users access the company network through the new access point. For simplicity, they also want a protocol that is used by Aironet wireless access points, requires no certificates, and supports mutual authentication using the logon password for each user. Which protocol should be used? A B C D EAP-MD5 EAP-TLS LEAP PEAP Author: Bill Buchanan Test 7 9 What are three characteristics of PEAP? (Choose three.) A B C authored by Cisco Systems, Microsoft, and RSA Security relies on a shared secret for authentication requires digital certificates for authentication of servers and users supports mutual authentication transports authentication messages through an encrypted tunnel uses a one-way hash of passwords D E F Author: Bill Buchanan Test 7 Test 7 10 If an administrator attempts to configure a switch with 802.1x port-based authentication, which three port types will display an error message? (Choose three.) static access ports trunk ports dynamic ports ports on the same VLAN secure ports ports on different VLANs Author: Bill Buchanan A B C D E F Test 7 11 Refer to the graphic. During 802.1x port-based authentication, each frame exchanged between the end user and the Catalyst 2950 is encapsulated with a frame header. For what protocol are these frames encapsulated? Ethernet RADIUS EAP PPP IP Author: Bill Buchanan A B C D E Test 7 12 Which three conclusions can be made based on the configuration below? (Choose three.) Switch# configure terminal Switch(config)# interface fastethernet0/12 Switch(config-if)# dot1x port-control auto Switch(config-if)# dot1x re-authentication Switch(config-if)# dot1x timeout re-authperiod 180 B C D E F Users connected to the switch will need to be reauthenticated after three hours. Users connected to the switch will need to be reauthenticated after three minutes. The switch has been configured for 802.1x authentication. Port 12 of the switch is not a trunk port. Port 12 of the switch is not a static port. Port 12 of the switch is a dynamic-access port. Author: Bill Buchanan A Author: Bill Buchanan Test 8 1 Which command will turn off CBAC alert messages to the console? A B C D router(config)# ip inspect alert-off router(config)# no ip inspect alert router(config)# no ip inspect alert-off router(config)# ip inspect alert log-only Author: Bill Buchanan Test 8 2 The timeout value in the ip inspect name command is configured in which units? A B C D seconds milliseconds microseconds minutes Author: Bill Buchanan Test 8 3 What does CBAC look for when inspecting TCP sequence numbers? A CBAC uses the sequence numbers to defragment the full packet. CBAC checks that the sequence numbers are within an expected range. CBAC rejects packets that arrive at an unusually high sequence rate. CBAC matches the source sequence numbers to the destination sequence numbers. B C D Author: Bill Buchanan Test 8 4 Which statement is correct concerning CBAC inspection rules? A Alert, audit-trail, and timeout are configurable per protocol and override corresponding global settings. Alert, audit-trail, and timeout are only globally configurable. Alert, audit-trail, and timeout are not configurable globally. Alert, audit-trail, and timeout are configurable only for TCP. B C D Author: Bill Buchanan Test 8 5 Which statement is true concerning CBAC and fragmentation inspection rules? A An inspection rule instructing the router to fragment packets should always be utilized. A fragmentation rule forces fragments to be buffered until the corresponding initial fragment is received. A fragmentation rule forces non-initial fragments to be discarded unless the initial fragment was allowed to pass. A fragmentation rule should not be used on exterior gateways. B C D Author: Bill Buchanan Test 8 6 A network administrator needs to configure the router to redirect incoming HTTP requests to a web server at port 8020. Which command should be used? A B C D Router(config)# ip port-map http eq 8020 Router(config)# ip port-map http port 8020 Router(config)# ip port-map port 8020 http Router(config)# ip port-map port 8020 eq http Author: Bill Buchanan Test 8 7 The IT department has decided to offer web and FTP services using TCP port 8000. The web server IP address is 192.168.3.4 and the FTP server IP address is 192.168.5.6. What commands are required to configure the perimeter router to redirect the web and FTP traffic? A Router(config)# access-list 10 permit 192.168.5.6 Router(config)# access-list 20 permit 192.168.3.4 Router(config)# ip port-map http port 8000 list 10 Router(config)# ip port-map ftp port 8000 list 20 Router(config)# access-list 10 permit 192.168.3.4 Router(config)# access-list 20 permit 192.168.5.6 Router(config)# ip port-map ftp port 8000 list 10 Router(config)# ip port-map http port 8000 list 20 Router(config)# access-list 10 permit 192.168.3.4 Router(config)# access-list 20 permit 192.168.5.6 Router(config)# ip port-map http port 8000 list 10 Router(config)# ip port-map ftp port 8000 list 20 Router(config)# access-list 10 permit 192.168.3.4 Router(config)# access-list 20 permit 192.168.5.6 Router(config)# ip port-map http list 10 port 8000 Router(config)# ip port-map ftp list 20 port 8000 B C D Author: Bill Buchanan Test 8 8 The graphic shows a client opening a Telnet session to a remote host. Which ACL entry will be created by CBAC to allow traffic to return to complete a successful Telnet connection? A access-list 110 permit udp host 10.0.0.5 eq 23 host 192.168.2.50 eq 2447 access-list 110 permit tcp host 10.0.0.5 eq 23 host 192.168.2.50 eq 2447 access-list 110 permit tcp host 192.168.2.50 eq 23 host 10.0.0.5 eq 2447 access-list 110 permit tcp host 10.0.0.5 eq 2447 host 192.168.2.50 eq 23 B C D Author: Bill Buchanan Test 8 9 CBAC is configured on the router shown in the graphic, the statement shown in the graphic is included in access control list 101, and the access control list is applied to interface s0/0 as shown. Single-channel TCP inspection is not included in the CBAC inspection rule. What will happen if the workstation tries to send a Telnet packet to the Internet? A The packet will be forwarded by the router as soon as it matches the ACL statement. The packet will be dropped by the router when no match is found in CBAC. The packet will be forwarded by the router, but return Telnet traffic will not be allowed. The packet will be forwarded after CBAC inspection determines that Telnet is an allowed protocol. B C D Author: Bill Buchanan Test 8 Test 8 10 Which filtering technology maintains complete connection information for each TCP or UDP connection and logs the information in a session flow table? packet filtering stateful filtering ACL directional filtering URL filtering Author: Bill Buchanan A B C D Test 8 11 Which filtering technology is often effective but can be circumvented using packet fragmentation? packet filtering stateful filtering URL filtering ACL directional filtering Author: Bill Buchanan A B C D Test 8 12 What is the result of the command shown below? Router(config)# ip inspect name tester icmp alert on audit-trail on timeout 30 B C D inspects ICMP traffic and sends any alert and audit messages to the log file on tester inspects IP traffic and sends an ICMP alert and audit message to tester if an outgoing IP packet is not acknowledged within 30 seconds inspects ICMP traffic and maintains state information on common types of ICMP traffic inspects ICMP traffic and maintains state information according to the tester rule set Author: Bill Buchanan A Test 8 A B C D E Refer to the graphic. If the complete configuration CBAC on CorpFW is correctly entered, which two statements describe the outcome of the completed configuration? (Choose two.) CBAC will delete all half-open connections necessary to accommodate new connections after 300 users have accessed the servers within the last six minutes. CBAC will delete all half-open connections necessary to accommodate new connections after 150 users have accessed the FTP servers within the last six minutes. CBAC will delete all half-open connections necessary to accommodate new connections after more than 300 users have half-open attempts to reach the corporate web server within the last minute. CBAC will delete all half-open connections necessary to accommodate new connections after 150 users have accessed the network within the last minute. CBAC will stop deleting half-open connections after fewer than 150 users have accessed the network within the last minute. Author: Bill Buchanan 13 Test 8 14 Which two configurations will protect the FTP server in the DMZ from DoS attacks? (Choose two.) B C D E CorpFW(config)# max-incomplete host 142.22.2.10 CorpFW(config)# ip inspect tcp max-incomplete host 60 block-time 0 CorpFW(config)# ip inspect tcp max-incomplete host 60 block-time 0 CorpFW(config)# ip inspect name Protect ftp timeout 3600 CorpFW(config)# interface FastEthernet 0/0 CorpFW(config-if)# max incomplete host 142.22.2.10 CorpFW(config)# ip inspect max-incomplete high 400 CorpFW(config)# ip inspect max-incomplete low 200 CorpFW(config)# ip inspect tcp max-incomplete host 60 block-time 0 CorpFW(config)# ip inspect udp max-incomplete host 60 blocktime 0 Author: Bill Buchanan A Test 8 15 The administrator has two goals. First, the administrator plans to use CBAC to block encapsulated Java applets from IP address 172.16.16.1. Then, the administrator plans to use CBAC to block DoS attacks such as the ping-of-death from external network. Which goals are accomlished when the three commands below are entered? A B C D The first goal is not accomplished because CBAC cannot block encapsulated Java applets. The second goal is accomplished. The first goal is not accomplished because a subnet mask, not a wild card mask, must be used. The second goal is accomplished. The first goal is accomplished. The second goal is not accomplished because CBAC provides limited stateful inspection for ICMP. Both goals are accomplished. Author: Bill Buchanan router(config)# ip access-list 1 deny 172.16.16.1 0.0.0.0 router(config)# ip inspect name FWALL http java-list 1 timeout 120 router(config)# ip inspect name FWALL icmp timeout 50 Test 8 16 Which two are types of port mapping supported by PAM? (Choose two.) host reverse dynamic DNS subnet-specific Author: Bill Buchanan A B C D E Test 8 17 What is the effect after these two commands are configured on a router? router(config)# ip inspect max-incomplete high 300 router(config)# ip inspect max-incomplete low 100 B C D When the combination of half-open TCP and UDP sessions reaches 300, CBAC begins deleting them. When the number falls to 100, CBAC stops deleting them. When the number of half-open sessions per minute reaches 300, CBAC begins deleting them. When the number falls to 100 per minute, CBAC stops deleting them. When the number of half-open sessions reaches 100, CBAC begins deleting them. When the number of cleared sessions equals 300, CBAC stops deleting them. When the number of half-open TCP sessions reaches 300, CBAC begins deleting them. When the number falls to 100, CBAC stops deleting them. Author: Bill Buchanan A Test 8 18 What is indicated if two endpoints in a connection receive reset packets from CBAC? D A session has ended by CBAC's proxy fin method. A DoS attack has been halted by CBAC's threshold method. Sequence checking has occured using CBAC's state table method. Spoofing has been prevented using CBAC's session checking method Author: Bill Buchanan A B C Test 8 19 What happens when the following commands are executed? router(config)# no ip inspect udp idle-time 45 router(config)# ip inspect dns-timeout 10 C D The router will not manage any inactive UDP connections. The only UDP connections that the router will manage are DNS connections. The router proxies DNS requests and manages them for 10 seconds. The router will manage UDP connections for 30 seconds and DNS connections for 10. Author: Bill Buchanan A B Author: Bill Buchanan Test 9 1 Which three statements describe the use of ACLs on a Cisco PIX Security Appliance? (Choose three.) A ACLs are used to restrict outbound traffic flowing from a lower to a higher security level interface. ACLs are used to restrict outbound traffic flowing from a higher to a lower security level interface. If no ACL is attached to an interface, inbound traffic is permitted by default unless explicitly denied. If no ACL is attached to an interface, outbound traffic is permitted by default unless explicitly denied. Cisco PIX Security Appliance ACLs use a wildcard mask like Cisco IOS ACLs. Cisco PIX Security Appliance ACLs use a regular subnet mask unlike Cisco IOS ACLs. B C D E F Author: Bill Buchanan Test 9 Test 9 2 The Cisco PIX Security Appliance allows the use of network, protocol, service and ICMP-type object grouping with ACLs. Which statement describes the service object group? Author: Bill Buchanan A It is used to group client hosts, server hosts, or subnets. B It is used to group protocols, such as IP, TCP, and UDP. C It is used to group TCP or UDP port numbers. D It is used to group ICMP message types. Test 9 3 which three channels are used by RTSP applications in standard RTP mode? (Choose three.) master control channel RTP data channel TCP control channel RDT data channel RTP resend channel RTCP reports Author: Bill Buchanan A B C D E F Test 9 4 What is the effect when the command shown in the graphic is configured on a Cisco PIX Security Appliance? Author: Bill Buchanan A ActiveX objects are allowed to local host 192.168.2.5 only. B ActiveX objects are sent to a filtering server at 192.168.2.5. C ActiveX objects are blocked on all inbound connections to local host 192.168.2.5. D ActiveX objects are blocked from local host 192.168.2.5 to all outbound connections. Test 9 5 A network administrator is considering a URLfiltering application server to work with the Cisco PIX Security Appliance running OS version 6.2. Which application would support the filtering of URL strings longer than 1159 bytes? N2H2 Websense either Websense or N2H2 any URL-based filtering application Author: Bill Buchanan A B C D Test 9 6 What is the function of the service-policy command within the Modular Policy Framework? defines a set of services set by policies enables a set of policies on an interface identifies traffic flows according to services groups a set of policies according to services Author: Bill Buchanan A B C D Test 9 7 Which two commands are used to deny a specific SNMP version and then enable SNMP application inspection on a Cisco PIX Security Appliance? (Choose two.) snmp-map snmp inspect inspect snmp inspect snmp-map snmp-map inspect Author: Bill Buchanan A B C D E Test 9 8 The Cisco PIX Security Appliance with software version 6.2 or higher has eliminated the need for the alias command when configuring NAT translation of IP addresses imbedded in DNS messages. Which two commands can now support NAT translation of DNS messages, so that the alias command is no longer required? (Choose two.) dns-route nat route-map static dns Author: Bill Buchanan A B C D E 9 A network administrator configured a Cisco PIX Security Appliance to limit connections to the application server at 192.168.10.5. Which configuration identifies traffic flows for the application server? A PIX(config)# access-list 125 permit tcp any host 192.168.10.5 PIX(config)# class-map APP_Server PIX(config-cmap)# match any PIX(config)# access-list 125 permit tcp any host 192.168.10.5 PIX(config)# service-policy APP_Server PIX(config-smap)# match access-group 125 PIX(config)# access-list 125 permit tcp any host 192.168.10.5 PIX(config)# policy-map APP_Server PIX(config-pmap)# match access-list 125 PIX(config)# access-list 125 permit tcp any host 192.168.10.5 PIX(config)# class-map APP_Server PIX(config-cmap)# match access-list 125 B C D Author: Bill Buchanan Test 9 Test 9 A B C D object-group host 3HOSTS network-object host 10.1.1.1 network-object host 10.1.1.2 network-object host 10.1.1.3 object-group network 3HOSTS network-object host 10.1.1.1 network-object host 10.1.1.2 network-object host 10.1.1.3 object-group network 3HOSTS host-object host 10.1.1.1 host-object host 10.1.1.2 host-object host 10.1.1.3 object-group host 3HOSTS host-object host 10.1.1.1 host-object host 10.1.1.2 host-object host 10.1.1.3 Author: Bill Buchanan 10 A network administrator wants to configure an object group to permit hosts 10.1.1.1, 10.1.1.2, and 10.1.1.3 access to network servers. Which commands must be entered to correctly configure an object group for the three hosts? Test 9 11 A network administrator has created the object group 10HOSTS to allow ten hosts access to specific network services. Which command does an administrator use to verify that the object group has been configured successfully? show access-list show host-group show 10HOSTS show object-group Author: Bill Buchanan A B C D Test 9 12 Which two statements describe the object-group and group-object commands? (Choose two.) Author: Bill Buchanan A The object-group command is a subcommand of the group-object command. B The object-group command defines which type of object group will be created. C The object-group command can contain other group objects. D The group-object command can contain object groups of different types. E The group-object command enables the construction of hierarchical, or nested, object groups. Test 9 13 Which command is used to enable a Turbo ACL after it has been configured in global configuration mode? pixfirewall(config)# access-list compiled pixfirewall(config)# ip access-list compiled pixfirewall(config)# access-group ACL_ID turbo pixfirewall(config)# access-list compiled ACL_ID Author: Bill Buchanan A B C D Test 9 14 Refer to the graphic. What is the result when the network administrator enters the command shown? fw1(config)# access-list aclout line 4 permit tcp any host 192.168.0.9 eq www Author: Bill Buchanan A It will replace the existing line 4 in the ACL. B It will push the current ACL line 4 and all of the lines that follow down one line. C It will require the ACL to be deleted and rewritten because it cannot be inserted as line 4. D It will be appended to the end of the ACL, and the current line 4 will be deleted. Test 9 15 Refer to the configuration shown in the graphic. Both commands have been entered into the Cisco PIX Security Appliance. Why might the administrator have chosen to allow ICMP unreachable traffic to be permitted at the outside interface? Author: Bill Buchanan A Denying ICMP unreachable traffic will disable routing updates. B ICMP unreachable traffic is required by web browsers. C Denying ICMP unreachable traffic can halt PPTP and IPSec traffic. D ICMP unreachable traffic is required for ACLs to work properly. Test 9 16 Which two URL-filtering applications can be used with the PIX Security Appliance? (Choose two.) IIS Websense NetSensor N2H2 Author: Bill Buchanan A B C D Test 9 17 Why would Service object groups be placed in an access list? Author: Bill Buchanan A A Service object group is used to indicate either the source or the destination port in an access list. B A Service object group is used in place of the keyword ip, tcp, udp or icmp. C A Service object group is used in place of source or destination server address. D A Service object group is used in place of listing individual servers that offer the same service. Author: Bill Buchanan Test 9 Test 10 1 A network administrator wants to configure an access switch to protect it from being exploited by attackers sending BPDUs through PortFastenabled ports. Which command implements this security option by putting any attacked port in an error-disabled state? Author: Bill Buchanan A Switch(config)# spanning-tree portfast bpdudisable default B Switch(config)# spanning-tree portfast bpduerror default C Switch(config)# spanning-tree portfast bpdufilter default D Switch(config)# spanning-tree portfast bpduguard default Test 10 2 As shown in the graphic, an intruder has connected to ports on two different access switches and wishes to spoof as the root bridge. What would the attacker send in the indicated direction to complete this exploit? Author: Bill Buchanan A BPDUs with a lower bridge priority B BPDUs with a higher bridge priority C VTP frames with a lower VLAN identity D VTP frames with a higher VLAN identity Test 10 3 A Cisco Catalyst switch is configured as shown in the graphic. Which type of attack is the network administrator trying to prevent? ping flood CAM table overflow MAC spoofing DHCP starvation Author: Bill Buchanan A B C D 4 Which three statements describe a CAM table overflow attack? (Choose three.) A The limitations of the switch software image are exploited via flooding of frames. The limitations of the fixed hardware of the CAM table are exploited via flooding of MAC addresses. The limitations of the switch memory cause the switch to operate like a hub in response to overflowing traffic. The configuration of VLANs on the switch minimizes the exploit by containing the flood of traffic to the VLAN supporting the attacker. The impact of the CAM table overflow attack can be lessened with the implementation of macof. The limitation of CAM table size causes the switch to flood traffic to all VLANs under CAM table overflow attack. B C D E F Author: Bill Buchanan Test 10 Test 10 5 Which two commands can be used to verify port security configuration? (Choose two.) Switch# show cam Switch# show buffer Switch# show port-security interface interface_id Switch# show vlan vlan_id port-security Switch# show port-security vlan vlan_id Author: Bill Buchanan A B C D E Test 10 Author: Bill Buchanan 6 Which type of attack involves an attacking system becoming a member of all VLANs? .. A switch spoofing B double tagging C private proxy D trunk spoofing 7 A B C D The hosts shown in the graphic and all other hosts in the same IP network are members of private VLAN 3 and, by design, should be unable to communicate at Layer 2. What ACL can be configured on the gateway router and applied to interface Fa0/1 to ensure that hosts on the private VLAN are unable to communicate with each other at Layer 3 but are still able to communicate with other networks? Router(config)# access-list 135 deny ip any 192.168.20.0 0.0.0.255 Router(config)# access-list 135 permit ip any any Router(config)# interface fastethernet 0/1 Router(config-if)# ip access-group 135 out Router(config)# access-list 135 deny ip 192.168.20.0 0.0.0.255 any Router(config)# access-list 135 permit ip any any Router(config)# interface fastethernet 0/1 Router(config-if)# ip access-group 135 in Router(config)# access-list 135 deny ip 192.168.20.0 0.0.0.255 192.168.20.0 0.0.0.255 Router(config)# access-list 135 permit ip any any Router(config)# interface fastethernet 0/1 Router(config-if)# ip access-group 135 out Router(config)# access-list 135 deny ip 192.168.20.0 0.0.0.255 192.168.20.0 0.0.0.255 Router(config)# access-list 135 permit ip any any Router(config)# interface fastethernet 0/1 Router(config-if)# ip access-group 135 in Author: Bill Buchanan Test 10 Test 10 8 Which statement describes the purpose of the configuration shown below? Switch(config)# ip dhcp snooping Switch(config)# ip dhcp snooping vlan 3 Switch(config-if)# ip dhcp snooping trust Switch(config-if)# ip dhcp snooping limit rate 30 B C D It is meant to disable any hosts that are attached to VLAN 3 and are configured for DHCP configuration rather than static IP addresses. It is meant to disable any rogue DHCP servers that are attached to VLAN 3. It is meant to monitor VLAN 3 for DHCP attacks that will deplete the DHCP pool. It is meant to monitor VLAN 3 and disable any hosts that are using static IP addresses rather than DHCP addresses. Author: Bill Buchanan A Test 10 9 Which type of output would be produced on a switch after entering the command? Switch# show ip dhcp snooping binding Author: Bill Buchanan A DHCP servers on the snooped network B DHCP clients on all DHCP snooped switches on the network C DHCP clients connected to DHCP snooped ports on the switch D all active protocols on all DHCP clients connected to DHCP snooped ports on the switch