E-Core Values: Ethical, Legal, Taxation, and International Issues
advertisement

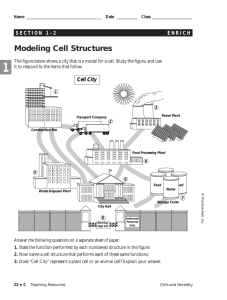
ELC 200 Day 21 ELECTRONIC COMMERCE From Vision to Fulfillment Third Edition Elias M. Awad © 2007 Prentice-Hall, Inc 12-1 Agenda • Assignment 7 Due • Assignment 8 Posted – Due April 21 @ 3:35 Pm • Quiz 3 Corrected – I am aware that I few questions were scored incorrectly, that has been addressed. – 6 A’s, 8 B’s & 3 C’s • ECommerce Initiative Frameworks – Guidelines – Due MAY 7 @ 10 AM © 2007 Prentice-Hall, Inc 12-2 End of days? (subject to change) • April 10 & 14 – Finish Chap 16 – Chap 13 eSecurity and the USA Patriot Act – Assignment 7 due April 10 – Assignment 8 Posted • April 17 & 21 – Chap 14 Encryption – Assignment 8 Due April 21 • April 24 & 28 – Chap 15 getting the money – Optional Assignment 9 • Due May 1 • May 1 – Quiz 4 – Chapters 12 16 – 20 M/C and 4 short essay • May 7 @ 10 AM – eCommerce frameworks due – Student presentations • 5 Mins! © 2007 Prentice-Hall, Inc 12-3 Going Online ELECTRONIC COMMERCE From Vision to Fulfillment Third Edition Elias M. Awad © 2007 Prentice-Hall, Inc 12-4 The focus of this chapter is on several learning objectives • How to build a business on the Internet - from beginning to end • What it takes to plan effectively • The hardware, software, security, and setup considerations in e-commerce infrastructure • The critical elements in the design of an ebusiness • How to market e-presence • How to manage customer feedback © 2007 Prentice-Hall, Inc 12-5 Building an Internet Business The Life Cycle © 2007 Prentice-Hall, Inc 12-6 The Marketing Phase (4) • Providing good site service • Advertising • Know your customer • Making the sale – Stock control – Collecting the cash • Delivering the goods and following up © 2007 Prentice-Hall, Inc 12-7 Cultural marketing Blunders © 2007 Prentice-Hall, Inc 12-8 The Marketing Phase © 2007 Prentice-Hall, Inc 12-9 The Fulfillment Phase (5) • Fulfillment is what happens after a sale is made – Packing up the merchandise – Shipping the merchandise – Answering questions about the order – Sending out the bill or verifying e-payment – Following up to see if the customer is satisfied • Fulfillment is honoring a commitment to deliver goods or services after payment has been assured • To the customer order fulfillment is the most important business activity of all © 2007 Prentice-Hall, Inc 12-10 Fulfillment Issues • Product availability • Matching the products for sale to the products in the inventory • Out-of-stock notice • Back orders • Processing orders • Controls © 2007 Prentice-Hall, Inc 12-11 The Maintenance and Enhancement Phase (6) • Maintenance means keeping a system or business on course, based on the initial design or plan • The goal of maintenance is to ensure the usability of the Web site • Enhancement means implementing upgrades or changes that are designed to improve the system’s productivity • The goal of enhancement is to upgrade the Web site and the business-to-consumer connection to meet the latest standards and customer expectations © 2007 Prentice-Hall, Inc 12-12 Important Tips for Managing Customer Feedback • Set up a list of frequently asked questions and post the list in a prominent location on the homepage • Make sure the information can be accessed easily and quickly • Make sure any page downloads within eight seconds and test it on slow, older computers • Avoid unnecessarily large images or bandwidth-hogging elements • Answer e-mail © 2007 Prentice-Hall, Inc 12-13 Important Items for Managing Customer Service • Updating orders • Order status • Technical support • Localization • Handling customer expectations © 2007 Prentice-Hall, Inc 12-14 SWOT • An analytic method used to determine competitive advantage – Strengths – Weakness – Opportunities – Threats © 2007 Prentice-Hall, Inc 12-15 STRENGHTS (internal) • Define areas you excel in – What will your initiative do better than others? – What are your core competencies (things you are good at)? – Do you have a clear strategic direction? – What resources do you have that competitors may not have? © 2007 Prentice-Hall, Inc 12-16 WEAKNESSES (internal) • Evaluate your liabilities – Where are you weak in relation to your competitors? – What skills and resources are you lacking? – What needs to be improved in your initiative? – Why were not able to improve the weaknesses you discovered? © 2007 Prentice-Hall, Inc 12-17 OPPORTUNITIES (external) • Analyze your customers and market potential – Identify favorable market conditions – Identify emerging technologies in support of your initiative – Identify changes in legislation and public policy that will have a supporting effect on your initiative © 2007 Prentice-Hall, Inc 12-18 THREATS (external) • Analyze potential challenges – What are your obstacles? – What are your competitors doing? – Identify changes in legislation and public policy that will have an adverse effect on your initiative. © 2007 Prentice-Hall, Inc 12-19 SWOT Analysis © 2007 Prentice-Hall, Inc 12-20 Google SWOT (2005) • • Strengths: 1. 2. Strong brand recognition and recall Brand equity (Ranked #1 among online brands by EquiTrend) 3. Talented employee base 4. Access to Google available to anyone with Internet access 5. Good cash reserves ($426,900,000) 6. Strong revenues (117 percent over previous year) 7. Strong profits (profits increased 106 percent over previous year) 8. Relationships with major corporations like AOL 9. Culture of innovation and accountability 10. Products based on solving consumer needs Weaknesses: 1. 2. 3. 4. 5. 6. 7. 8. © 2007 Prentice-Hall, Inc Corporate governance minimizes power of nonemployee shareholders Lack of independence on board of directors Vision for company may be unclear Fast growth may be unmanageable and unsustainable Technology that supports targeting advertising can result in inappropriate positioning (e.g., Kraft ad on the Web site for a White Nationalist group) Net profit margin is weak (12.51 percent) compared to Yahoo! (23.00 percent) Company is smaller and less profitable compared to Yahoo! (e.g., Yahoo! revenues were $3,574,517,000 compared to $3,189,223 for Google; Yahoo! spent $368,760,000 on research development while Google spent $225,632,000; Yahoo! net income was $839,553,000 while Google’s was $399,100,000.) Little physical presence (offices) in Asia and none in South America or Africa 12-21 Google SWOT (Part 2) • • Opportunities: 1. Internet-based technologies and businesses continue to develop 2. Worldwide growth in Internet coverage and use 3. Large market still to be tapped (currently only 15.7 percent of the world has Internet access). Asia, in particular, is a valuable potential market. It makes up 56.4 percent of the world’s population, but only 9.9 percent of its population is online (according to www.internetworldstats.com). 4. Increasing demand for Webbased business and consumer solutions 5. Advertising spending declining in other media but increasing online 6. Potential to expand into other media © 2007 Prentice-Hall, Inc Threats: 1. Microsoft has stated its plans to threaten Google’s future 2. Other competitors (Yahoo, eBay, MSN, and others) 3. Potential for click fraud 4. Potential for attacks on Google’s servers 5. Legal constraints in the area of intellectual property rights 6. Consumer attitudes toward online advertising 12-22 Chapter Summary • Launching a business on the Internet involves a life cycle • Strategizing means evaluating a company’s position and the competition, setting a course for the years ahead, and determining how to get it done • Specific goals need to be considered when planning e-business © 2007 Prentice-Hall, Inc 12-23 Chapter Summary (Cont’d) • The hardware, software, security, and set-up phase focuses on: – Hardware to buy – Software to buy – Where to buy • Four essentials of launching a business on the Internet are – – – – Security Shopping carts Payments Marketing • Behind every Web site are programs stored on a Web server © 2007 Prentice-Hall, Inc 12-24 Chapter Summary (Cont’d) • In Web design, the focus is on – – – – – – user control and freedom Consistency and standards Recognition Aesthetic design Recovery from error Help desk to handle customer queries and complaints • Marketing phase includes: – – – – – Advertising Knowing the customer Making the sale Getting the goods Follow-up procedures after the sale © 2007 Prentice-Hall, Inc 12-25 Chapter Summary (Cont’d) • Fulfillment phase typically includes: – – – – Packing up the merchandise Shipping the goods Answering questions about the order Sending out the bill or a copy of the bill • Maintenance and Enhancement Phase addresses the need to keep the Web storefront up to date and to make any changes that will enhance the use and effectiveness of the Web site © 2007 Prentice-Hall, Inc 12-26 E-Security and the USA Patriot Act ELECTRONIC COMMERCE From Vision to Fulfillment Third Edition Elias M. Awad © 2007 Prentice-Hall, Inc 12-27 Assignment 8 Security for Your eBusiness 1. Identify and quantify in monetary terms the critical assets in your company that may be at risk form the dangers listed in Chapter 13. (you should identify at a bare minimum 5 assets) 2. For each of the critical assets at risk, what steps could you take to protect your company from the risks? 3. For of the steps and possible solutions you identify in question 2, find out how much it would cost to implement the steps or solution. 4. Is the cost of fixing the problems make sense in relation to potential monetary loss of not fixing the security problem? 5. Could you purchase anti-hacker insurance for your company? If so, from where and how much would it cost? © 2007 Prentice-Hall, Inc 12-28 The focus of this chapter is on several learning objectives • What is involved in designing for security • The many faces of viruses and other contaminants on the Internet • How to build a secure system and recover from disaster • How biometrics contributes to security • The makeup of the USA Patriot Act and its contribution to security via the Internet © 2007 Prentice-Hall, Inc 12-29 Abuse and Failure in ECommerce • Fraud, resulting in direct financial loss • Theft of confidential, proprietary, technological, or marketing information belonging to the firm or to the customer • Disruption of service, resulting in major losses to the business or inconvenience to the customer • Loss of customer confidence stemming from illegal intrusions into customer files or company business – Hannaford Hack – http://www.news.com/8301-10784_3-99059917.html?tag=blog.promos © 2007 Prentice-Hall, Inc 12-30 Paper-based versus Electronic Commerce Attributes © 2007 Prentice-Hall, Inc 12-31 Conceptualizing Security • Security addressing risk and protection from the unknown • Risk is a matter of degree • The biggest risk in e-commerce is fraudulent credit card usage and the mishandling of personal e-mail information • The first issue in security is identifying the principals © 2007 Prentice-Hall, Inc 12-32 Security Concerns 1. Confidentiality 2. Authentication 3. Integrity 1. Auditable 4. Access control 5. Nonrepudiation © 2007 Prentice-Hall, Inc 12-33 General Security Issues at E-Commerce Sites © 2007 Prentice-Hall, Inc 12-34 Privacy • The ability to control who may see certain information and on what terms • Lack of privacy has been more of a problem with the Internet than it has with any other medium invented to date • Every time the issue of security surfaces, privacy is involved • A Web site should post the vendor’s privacy policy for the consumer to evaluate © 2007 Prentice-Hall, Inc 12-35 Basic Steps to Protect Your Privacy Online • Send anonymous e-mail through remailers • Improve security through your Web browser; deactivate or block cookies • Use a secondary free e-mail service • Stay away from filling out any form or questionnaire online • Consider using privacy software – http://privacy-software-review.toptenreviews.com/ • Install a firewall program – http://www.firewallguide.com/ © 2007 Prentice-Hall, Inc 12-36 The Password • Passwords have been used for decades to protect files from unauthorized use • Password cracking programs and user carelessness are rendering passwords ineffective • Alternatives to passwords – Public-key encryption – Biometrics – Smart cards that can store a password to perform complex encryption on the card – Two-factor solutions • One time passwords © 2007 Prentice-Hall, Inc 12-37 Ideas to Improve Security Systems • Limit the number of times a password can be repeated in accessing a sensitive system • Train employees, customers, and the general public in more advanced methods like biometrics, PKE, and smart cards • Ensure that systems designers and systems analysts are well versed in security issues and security procedures as part of every future application • Review and evaluate the strength of the current password schemes used by customers and employees alike © 2007 Prentice-Hall, Inc 12-38 Identity Theft and Phishing • ID theft has become a societal and governmental concern • ID theft has gone electronic • Viruses and worms carrying Trojan horse code are powering massive ID theft rings • Thieves are using wireless devices to impersonate legitimate Internet access points with the intent to steal credit card numbers and other privileged information © 2007 Prentice-Hall, Inc 12-39 Identity Theft and Phishing (Cont’d) • Phishing is a relatively recent phenomenon • Phishing characteristics: – Trojan horses are installed on vulnerable machines to gather data – “Harvest” user names and passwords to distribute to attackers – Users’ PCs are compromised without their knowledge – Software vulnerabilities force PCs to download code © 2007 Prentice-Hall, Inc 12-40 Basic Guidelines for Protecting Yourself from Identity Theft • Protect your social security number by supplying it only when absolutely necessary • Check your credit reports at least once a year. Check your statements for unexplained charges or unusual withdrawals from your bank accounts – Check Credit reports every year • https://www.annualcreditreport.com/cra/index.jsp • Be careful whom you talk to on the telephone – telemarketers, ISP employees, or even members of government agencies could all be disguised criminals • Use shredders to get rid of your statements or receipts. When using ATMs, never leave your receipts behind © 2007 Prentice-Hall, Inc 12-41 Basic Guidelines for Protecting Yourself from Identity Theft (Cont’d) • If you carry a laptop around, use “strong” passwords (combination of upper and lowercase characters, symbols, numbers, etc.) Don’t use the last four digits of your social security number, date of birth, or your mother’s maiden name • Remove your mail from your mailbox promptly, especially while on vacation. Thieves could make a habit of following the mail carrier for rifling through your mail. • Place a fraud alert on your credit reports by calling Equifax (888-766-0008) or Experian (888-EXPERIAN) © 2007 Prentice-Hall, Inc 12-42 The Security Assessment Life Cycle © 2007 Prentice-Hall, Inc 12-43 Designing for Security • Design process begins with a chief security officer • Five major steps – Assessing the security needs of the firm – Establishing a good policy – Fulfilling Web security needs – Structuring the security environment – Monitoring the system © 2007 Prentice-Hall, Inc 12-44 Designing the Security Environment • The design begins with the sequence and parameters in the security network based on the security policy and requirements of the e-commerce system • How much security depends on how much risk the company is willing to take, the security policy it is willing to adopt, and the present state of security practices • A security perimeter generally includes firewalls, authentication, virtual private networks (VPNs), and intrusion detection devices • The first line of defense is the firewall • Another technology protecting the perimeter is authentication © 2007 Prentice-Hall, Inc 12-45 Security in the Middle Ages © 2007 Prentice-Hall, Inc 12-46 The Security System Design Process © 2007 Prentice-Hall, Inc 12-47 Monitoring the Security System • Separation of responsibilities • Security system must be monitored via feedback mechanisms to ensure that the entire system is working properly • Monitoring – Capture processing details for evidence – Verify that e-commerce is operating within the security policy – Verify that attacks have been unsuccessful © 2007 Prentice-Hall, Inc 12-48 How Much Risk Can You Afford? • How secure are we? How much will it cost to secure our system? • Estimate the pain threshold your company and the attacker are willing to tolerate • Goal of security strategies, methods, and procedures is to raise the threshold of pain an attacker must endure to access and cause damage to a system • What is the level of protection required against the risks the merchant is willing to assume? © 2007 Prentice-Hall, Inc 12-49 Kinds of Threats or Crimes • Those that are physically related – Steal & damage information on a computer • Those that are order related – Misused credit cards – Insider tampering • Those that are electronically related – Manipulate or steal data “in-flight” – A sniffer is a person or a program that uses the Internet to record information that transmits through a router from its source to its destination © 2007 Prentice-Hall, Inc 12-50 Snoop and Sniff © 2007 Prentice-Hall, Inc 12-51 Client/Server Security Threats • Client attacks – Sheer nuisance – Deliberate corruption of files – Rifling stored information • How are the attacks done? – Physical attacks – Viruses – Computer-to-computer attacks • Server security threats – Denial of service (DOS) is an attack by a third party that prevents authorized users from accessing the infrastructure – Distributed denial of service attacks © 2007 Prentice-Hall, Inc 12-52 DDOS http://www.cs3-inc.com/pk_whatisddos.html © 2007 Prentice-Hall, Inc 12-53 Hacker Strategies • Social engineering • Shoulder surfing • Dumpster diving • Whacking (wireless hacking) © 2007 Prentice-Hall, Inc 12-54 Hacker Prevention • Perform an online security checkup or install a firewall on your computer workstation • Intrusion detection is sensing when a system is being used without authorization • Hire a hacker who works at foiling the efforts of the troublemakers while not hacking • Conduct cyber-forensic investigations and hire cyberinvestigators to set up alarms and traps to watch and catch intruders and criminals within the networks © 2007 Prentice-Hall, Inc 12-55 The Players: Hackers, Crackers, and Other Attackers • Hackers – Original hackers created the Unix operating system and helped build the Internet, Usenet, and World Wide Web; and, used their skills to test the strength and integrity of computer systems – Over time, the term hacker came to be applied to rogue programmers who illegally break into computers and networks – Hacker underground • http://www.defcon.org/ • http://www.blackhat.com/ • http://www.2600.com/ © 2007 Prentice-Hall, Inc 12-56 The Players: Hackers, Crackers, and Other Attackers (cont.) • Uber Haxor – Wizard Internet Hackers – Highly capable attackers – Responsible for writing most that the attacker tools • Crackers People who engage in unlawful or damaging hacking short for “criminal hackers” • Other attackers – “Script kiddies” are ego-driven, unskilled crackers who use information and software (scripts) that they download from the Internet to inflict damage on targeted sites – Scorned by both the Law enforcement and Hackers communities © 2007 Prentice-Hall, Inc 12-57 Script Kiddies • script kiddies: pl.n. 1. [very common] The lowest form of cracker; script kiddies do mischief with scripts and rootkits written by others, often without understanding the exploit they are using. Used of people with limited technical expertise using easy-to-operate, pre-configured, and/or automated tools to conduct disruptive activities against networked systems. Since most of these tools are fairly well-known by the security community, the adverse impact of such actions is usually minimal. 2. People who cannot program, but who create tacky HTML pages by copying JavaScript routines from other tacky HTML pages. More generally, a script kiddie writes (or more likely cuts and pastes) code without either having or desiring to have a mental model of what the code does; someone who thinks of code as magical incantations and asks only “what do I need to type to make this happen?” • • Source: http://www.catb.org/jargon/html/S/script-kiddies.html More info: http://www.tamingthebeast.net/articles/scriptkiddies.htm © 2007 Prentice-Hall, Inc 12-58 How Hackers Hack • Many Techniques – Social Engineering • Get someone to give you their password – Cracking • • Guessing passwords A six letter password (no caps) – > 300 million possibilities • Merriam-Webster's citation files, which were begun in the 1880s, now contain 15.7 million examples of words used in context and cover all aspects of the English vocabulary. – http://www.m-w.com/help/faq/words_in.htm – Buffer Overflows • Getting code to run on other PCs – Load a Trojan or BackDoor – Snoop and Sniff • Steal data – Denial of Service (DOS) • Crash or cripple a Computer from another computer – Distributed Denial of Service (DDOS) • Crash or cripple a Computer from multiple distributed computers © 2007 Prentice-Hall, Inc 12-59 Maine’s Anti-Hacker laws §432. Criminal invasion of computer privacy 1. A person is guilty of criminal invasion of computer privacy if the person intentionally accesses any computer resource knowing that the person is not authorized to do so. [1989, c. 620 (new).] 2. Criminal invasion of computer privacy is a Class D crime. [1989, c. 620 (new).] §433. Aggravated criminal invasion of computer privacy 1. A person is guilty of aggravated criminal invasion of computer privacy if the person: A. Intentionally makes an unauthorized copy of any computer program, computer software or computer information, knowing that the person is not authorized to do so; [1989, c. 620 (new).] B. Intentionally or knowingly damages any computer resource of another person, having no reasonable ground to believe that the person has the right to do so; or [1989, c. 620 (new).] C. Intentionally or knowingly introduces or allows the introduction of a computer virus into any computer resource, having no reasonable ground to believe that the person has the right to do so. [1989, c. 620 (new).][1989, c. 620 (new).] 2. Aggravated criminal invasion of computer privacy is a Class C crime. [1989, c. 620 (new).] © 2007 Prentice-Hall, Inc 12-60 The National Strategy to Secure Cyberspace • Create a cyberspace surety response system • Establish a threat and vulnerability reduction program • Improve security training and awareness • Secure the government’s own systems • Work internationally to solve security issues (U.S. Department of Homeland Security) • http://www.whitehouse.gov/pcipb/ • http://www.dhs.gov/xprevprot/programs/editorial_ 0329.shtm © 2007 Prentice-Hall, Inc 12-61 CYBER Warfare • Russia – Estonia Cyber war • Taught at US Military academies – http://www.dean.usma.edu/Teams/CyberDefens e/Default.cfm – bh-fed-03-dodge.pdf – iwar_wise.pdf http://www.itoc.usma.edu/ragsdale/ © 2007 Prentice-Hall, Inc 12-62 The Virus: Computer Enemy Number One • Most serious attack on a client computer or a server in an Internet environment is the virus • A virus is a malicious code that replicates itself and can be used to disrupt the information infrastructure • Viruses commonly compromise system integrity, circumvent security capabilities, and cause adverse operation by taking advantage of the information system of the network © 2007 Prentice-Hall, Inc 12-63 Types of Viruses • File virus is one that attacks executable files • Boot virus attacks the boot sectors of the hard drive and diskettes • Macro virus exploits the macro commands in software applications such as Microsoft Word © 2007 Prentice-Hall, Inc 12-64 Levels of Virus Damage © 2007 Prentice-Hall, Inc 12-65 Steps for Antivirus Strategy • Establish a set of simple enforceable rules for others to follow • Educate and train users on how to check for viruses on a disk • Inform users of the existing and potential threats to the company’s systems and the sensitivity of information they contain • Periodically update the latest antivirus software © 2007 Prentice-Hall, Inc 12-66 Getting Rid of Viruses • Get a good Virus Projection Software – Free (not Recommended) • Anti-Vir • Avast • AVG – Not Free • Norton AntiVirus • MacAfee – Free for UMFK students and staff • http://www.umfk.maine.edu/it/antivirus/ • Update definition files often © 2007 Prentice-Hall, Inc 12-67 Spyware • • • • • Software that sits on your computer – Monitors everything that you do and sends out reports to Marketing agencies – Usually ties to a POP-UP server Top Spyware – I-Look Up – CoolWebSearch – N-CASE – GATOR – DoubleClick If you have ever loaded up ICQ Loaded on your PC you have Spyware If you have ever had KAZAA loaded on your PC you have Spyware If you have loaded Quicken or TurboTax you have Spyware – C-Dilla © 2007 Prentice-Hall, Inc 12-68 Spyware infestation. Taken by Brandon Waddell. © 2007 Prentice-Hall, Inc 12-69 Spyware and Adware • Spyware is software the user unknowingly installs through an e-mail attachment or downloading an infected file that could be used for illicit reasons • Adware is software that sneaks into a user’s hard disk installed by Internet advertising companies to promote pop-up ads and release information for advertisers on the outside © 2007 Prentice-Hall, Inc 12-70 Spyware Solutions • Enforce strict user Web policies on surfing and downloading activities • Install a desktop firewall on every laptop and desktop http://www.zonelabs.com • Do not give users administrator privileges • Configure an e-mail gateway to block all executable e-mail attachments • Ensure desktop antivirus software signatures are up to date - http://www.grisoft.com © 2007 Prentice-Hall, Inc 12-71 Spyware Solutions (Cont’d) • Use commercial antispyware sofware to detect and remove existing spyware program - http://www.spybot.com – Keeping Your PC Spyware Free.pdf • Enforce the usage of higher security settings in Internet browsers to prevent sites that cause spyware infection • Use pop-up blockers that lead to Web sites low trustworthiness • Educate your employees and staff about spyware threats be creating an active out-reach with groups and organizations, including the Consortium of Anti-Spyware Technology (COAST) © 2007 Prentice-Hall, Inc 12-72 Compliance Legislation • The Gramm-Leach-Billey Act – Protects personal data • The VISA USA Cardholder Information Security Program – Personal data must be encrypted • The Sarbanes-Oxley Act – Executives must vouch for effectiveness of controls • The Basel II Capital Accords – Internal accord specifying cash and risk reporting © 2007 Prentice-Hall, Inc 12-73 Steps to Prevent E-Commerce Fraud • Be aware of corporate critical assets and who might be after the assets • Investigate common attacks and electronic-fraud schemes that could be used against the company’s critical assets • Install strong encryption such as public key infrastructure (PKI) • Develop a program for evidence collection (called forensics) via committed investigators © 2007 Prentice-Hall, Inc 12-74 Steps to Prevent E-Commerce Fraud (Cont’d) • Ensure maintenance of strong and reliable transaction, network, and Internet service provider logs • Conduct penetration testing to judge the integrity of existing security • Investigate the availability of cyber-fraud insurance to provide coverage for potential losses © 2007 Prentice-Hall, Inc 12-75 Security Protection and Recovery • Install proper firewall(s) to protect data • Ensure that your network is configured properly • Protect your most sensitive data through encryption • Maintain and update all antivirus programs on your PC or terminal • Restrict access to your files by “need to know’ • Assign unique IDs to authorized personnel and track all IDs on a daily basis • Ensure that your system administrators have contemporary security skills • Enforce and update company information security policy and inform employees of any changes in policy © 2007 Prentice-Hall, Inc 12-76 Firewalls and Security • Firewalls can be used to protect a corporation’s network in a number of ways – Protect against authenticated log-ins – Block all unsecured access to the internal network – Separate groups within an organization • Firewalls ensure – Data integrity – Authentication – Confidentiality © 2007 Prentice-Hall, Inc 12-77 Firewall Design and Implementation Issues • Design Issues – Policy – Level of monitoring and control the organization wants – Financial and administrative – Whether the company wants internal firewalls installed • Firewall Design features – Security policy – Deny policy – Filtering ability – Scalability – Authentication – Recognizing dangerous services – Effective audit logs © 2007 Prentice-Hall, Inc 12-78 Corporate Networks and Firewalls © 2007 Prentice-Hall, Inc 12-79 How Firewalls Work • Firewall check Packets in and out of Networks – Decide which packets go through and which don’t – Work in both directions – Only one part of Security © 2007 Prentice-Hall, Inc 12-80 Firewalls Attack Prevention System Attack Message Hardened Client PC Firewall Attack Message X Hardened Server With Permissions Internet Stops Most Attack Messages Attacker Corporate Network © 2007 Prentice-Hall, Inc 12-81 How Personal Firewalls work • Software version of a standard Hardware firewall • Controls packets in and out of one PC in much the same way as a Hardware Firewall does © 2007 Prentice-Hall, Inc 12-82 Privativate Lines CSU/DSU ROUTER Internet CSU/DSU ROUTER VPN Concentratror CSU/DSU ROUTER VPN Concentratror CSU/DSU ROUTER Router Load balancer Router Server Server Server Server Server Server Server Server Server Server Server Server Server Server Server Server CSU/DSU ROUTER Load balancer CSU/DSU ROUTER Switch Firewall Load balancer Server Server CSU/DSU ROUTER Msg Server Farm Firewall Firewall CSU/DSU ROUTER Load balancer Firewall switch Switch Switch Firewall Switch Minicomputer Firewall Minicomputer Disk array Server Server Server Server Minicomputer Server Server Server Server Server Server Server Server Server Server Minicomputer Server Server Server Server Server Server Server Server Server ServerServer Server Server Switch Switch Switch Web Server farm © 2007 Prentice-Hall, Inc Switch Disk array Server Switch Application Server farm Switch 12-83 DB SERVER FARM Cycle of Recovery from Attack • Attack detection and vulnerability assessment • Damage assessment <> evidence collection • Correction and recovery • Vigilance and corrective feedback © 2007 Prentice-Hall, Inc 12-84 Biometric Security • Biometrics is the science and technology of quantifying and statistically scrutinizing biological data • Biometrics enhance authentication • Biometric devices ensure that the person who encrypts data is the only one who can decrypt and has access to the data • Applying biometric technology on a smart card also would increase the level of confidence in the security • When considering biometric technologies for future use, management does need to implement a cost-effective system appropriate for their particular circumstance © 2007 Prentice-Hall, Inc 12-85 Types of Biometrics and Select Application Areas © 2007 Prentice-Hall, Inc 12-86 Types of Biometrics and Select Application Areas (Cont’d) © 2007 Prentice-Hall, Inc 12-87 Terrorism How Modern Terrorism Uses the Internet • • • • • • • • • • • • • • • • • • • • • • http://www.state.gov/s/ct/rls/fs/37191.htm Abu Nidal Organization (ANO) Abu Sayyaf Group Al-Aqsa Martyrs Brigade Ansar al-Islam Armed Islamic Group (GIA) Asbat al-Ansar Aum Shinrikyo Basque Fatherland and Liberty (ETA) Communist Party of the Philippines/New People's Army (CPP/NPA) Continuity Irish Republican Army Gama’a al-Islamiyya (Islamic Group) HAMAS (Islamic Resistance Movement) Harakat ul-Mujahidin (HUM) Hizballah (Party of God) Islamic Jihad Group Islamic Movement of Uzbekistan (IMU) Jaish-e-Mohammed (JEM) (Army of Mohammed) Jemaah Islamiya organization (JI) al-Jihad (Egyptian Islamic Jihad) Kahane Chai (Kach) Kongra-Gel (KGK, formerly Kurdistan Workers' Party, PKK, KADEK • • • • • • • • • • • • • • • • • • • • • © 2007 Prentice-Hall, Inc Lashkar-e Tayyiba (LT) (Army of the Righteous) Lashkar i Jhangvi Liberation Tigers of Tamil Eelam (LTTE) Libyan Islamic Fighting Group (LIFG) Moroccan Islamic Combatant Group (GICM) Mujahedin-e Khalq Organization (MEK) National Liberation Army (ELN) Palestine Liberation Front (PLF) Palestinian Islamic Jihad (PIJ) Popular Front for the Liberation of Palestine (PFLF) PFLP-General Command (PFLP-GC) al-Qa’ida Real IRA Revolutionary Armed Forces of Colombia (FARC) Revolutionary Nuclei (formerly ELA) Revolutionary Organization 17 November Revolutionary People’s Liberation Party/Front (DHKP/C) Salafist Group for Call and Combat (GSPC) Shining Path (Sendero Luminoso, SL) Tanzim Qa'idat al-Jihad fi Bilad al-Rafidayn (QJBR) (al-Qaida in Iraq) (formerly Jama'at alTawhid wa'al-Jihad, JTJ, al-Zarqawi Network) United Self-Defense Forces of Colombia (AUC) 12-88 National Strategy to Secure Cyberspace The National Strategy to Secure Cyberspace articulates five national priorities including: I. A National Cyberspace Security Response System; II. A National Cyberspace Security Threat and Vulnerability Reduction Program; III. A National Cyberspace Security Awareness and Training Program; IV. Securing Governments’ Cyberspace; V. National Security and International Cyberspace Security Cooperation. cyberspace_strategy.pdf © 2007 Prentice-Hall, Inc 12-89 USA Patriot Act • • • • Uniting and Strengthening America by Providing Appropriate Tools Required to Intercept and Obstruct Terrorism Act of 2001 Enacted Oct, 2001 and was to last for 4 years USA Patriot Act Improvement And Reauthorization Act Of 2005 – Signed March 2006 ACLU repsonse – Expands terrorism laws to include “domestic terrorism” which could subject political organizations to surveillance, wiretapping, harassment, and criminal action for political advocacy. – Expands the ability of law enforcement to conduct secret searches, gives them wide powers of phone and Internet surveillance, and access to highly personal medical, financial, mental health, and student records with minimal judicial oversight. – Allows FBI Agents to investigate American citizens for criminal matters without probable cause of crime if they say it is for “intelligence purposes.” – Permits non-citizens to be jailed based on mere suspicion and to be denied re-admission to the US for engaging in free speech. Suspects convicted of no crime may be detained indefinitely in six month increments without meaningful judicial review. © 2007 Prentice-Hall, Inc 12-90 Implications for Management • The Internet is becoming an increasingly filtered channel of communication • Information security continues to be deemphasized or ignored by management at all levels of the organization • Changes in the identification of threats, the growing advancement of technologies, and the identification of new threats continue to shift the organizational security focus • Any serious profile should begin with a valid security policy, which is then translated into an effective security plan with a focus on prevention, detection, and ©correction of threats 2007 Prentice-Hall, Inc 12-91