Wireless Communications & SPAM
advertisement

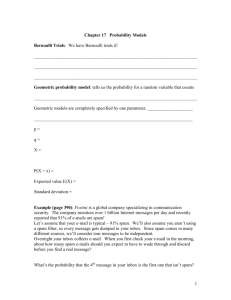
CS 305 Social, Ethical, and Legal Implications of Computing Chapter 3 WWW to Wireless Communication Herbert G. Mayer, PSU CS Status 7/29/2012 Slides derived from prof. Wu-Chang Feng 1 Syllabus Spam Electronic Mail Why Spam? How Done? Spam and Ethics CAN Spam Class Exercise Solutions to Spam World-Wide Web Censorship Freedom of Expression Discussions in Class 2 Spam SPAM? No: Spam! Spam is not an acronym Spam is unsolicited bulk information sent indiscriminately Possibly derived as a second meaning of derided product: Spam from Hormel Corp. known as SPiced hAM Spam is one of email’s not so desired side-effects SPIT is Spam over Internet Telephony In 2000 Spam accounted for 8% of all email In 2003 Spam accounted for 40% of all email In 2009 Spam accounted for 90% of all email In 2011 Spam is estimated to account for ~7 Trillion emails In my last year working at Intel, I received ~200 emails a day on average; a week of vacation turned into an email disaster; I treated some like SPAM: Delete! Delete! Delete! 3 Electronic Mail outgoing message queue user mailbox Three major components: user agents mail servers Simple Mail Transfer Protocol: SMTP user agent mail server SMTP User Agent SMTP a.k.a. “mail reader” composing, editing, reading mail messages mail server e.g., Eudora, Outlook, elm, Mozilla Thunderbird outgoing, incoming messages stored on server user agent 4 SMTP user agent user agent mail server user agent user agent Electronic Mail: Mail Servers Mail Servers user agent mailbox contains incoming messages for user mail server message queue of outgoing (to be sent) mail messages SMTP e.g. sendmail, postfix, Exchange SMTP SMTP protocol Between mail servers to send email messages Mail servers are both clients and servers mail server user agent 5 SMTP user agent user agent mail server user agent user agent Electronic Mail: SMTP [RFC 821] Uses Transmission Control Protocol (TCP) to reliably transfer message from client to server, port 25 User agent to sending server (sometimes) Sending server to receiving server (always) Command-Response interaction commands: composing, reading, sending, sending with acknowledgment, replying, replying to all … response: status code and phrase 6 Alice emails Bob 4) SMTP client sends Alice’s message over the TCP connection 5) Bob’s mail server places the message in Bob’s mailbox 6) Bob invokes his user agent to read message 7) More complex scenarios with ACK possible 1) Alice uses UA to compose message, “to” bob@someschool.edu 2) Alice’s UA sends message to her mail server; message placed in message queue 3) Client side of SMTP opens TCP connection with Bob’s mail server 1 user agent 2 mail server 3 mail server 4 7 5 6 user agent Spam Today By the end of 2011, the majority of all email received is unwanted Unwanted email can mean Informative for our genuine interests, and thus be enjoyed A bother, since the subject is not of interest Some topics even can be strongly offensive First level protection: Have tools to re-direct spam to junk mail boxes Error-prone, and places some good mail into junk boxes Happened to this instructor with this CS class’s homework; but also due to computer change: MS->Apple How do we achieve real protection? Through laws? Then they need enforcement By tools? They need to be strongly refined spammers will find ways around the tools, and around the laws 8 Why Spam? Let’s say I want to send an advertisement to 1,000,000 “targeted” people To send by regular bulk mail, this will cost ~$200-300 k To send by email, it will cost ~$1 k, i.e. the cost to buy a list of email addresses from an Internet company email addresses harvested from web sites, mailing lists, chat rooms, and newsgroups, then sold to Spammers Dictionary attacks trying lots of plausible address combinations keeping the ones not bouncing back Thus putting added strain (bandwidth) to the network 9 How Done? Run their own server farms for sending Spam Typically located off-shore Use ISPs that do not care about Spam Less effective now with proliferation of blacklists With efforts to shut down rogue ISPs Locate open mail proxies and bounce Spam through them Less effective Use networks of compromised machines (botnets) Single, most popular use for a botnet Monetization of botnet to send Spam drives malware effort Some steps taken to prevent (i.e. ISPs allowing direct port 25 access only to their own mail servers) 10 How Done? Definition: Phishing is fraudulent acquisition of sensitive (e.g. confidential) information thru internet Phishing accounts Trick legitimate user to give up username/password Send as the user (reputation hijacking) to avoid blacklisting based on IP addresses Creating bogus webmail accounts Rely on good reputation of popular webmail services such as Gmail and Yahoo! Mail, to avoid blacklisting based on IP addresses 11 Spam and Ethics Kantian evaluation of Spam Act guided by moral principles that can at the same time be used as base for a universal code of law A simple legal way of saying this: Act in good faith! However, every simple phrase invites mis-interpreters! Another way of saying this: Act so that you treat yourself as well as others as ends in themselves; never purely as means to another end Scenario: Suppose I have a great new product I wish to advertise. I send an unsolicited email to a large group of people knowing that only a tiny fraction is interested Is that ethical under Kant’s CI? Students discuss in class 7/17/2012 12 Spam and Ethics Act Utilitarian evaluation of Spam An action is right (or wrong) to the extent that it increases (or decreases) the total happiness of the affected parties. Scenario: A product that costs $10 to make, is sold for $25, purchasers value at $30 (i.e. their derived happiness) 100 million bulk messages being sent costs lost time and bandwidth for those, who receive it and are not interested As a result each of those has $0.01 of unhappiness (time wasted) 10,000 customers purchase product and get full happiness Is that ethical under Act Utilitarianism? Students discuss … and compute amount of satisfaction, here AKA happiness 13 Spam and Ethics Rule Utilitarian evaluation of Spam We should adopt moral rules which, if followed by everyone, will lead to greatest increase in overall happiness Scenario: Products being advertised, where only a small fraction of targets is known to be interested What if only 1% of all small businesses in the US email you 1 Spam advertisement per year? There are 24,000,000 small businesses in America 1% => 240,000 emails per year 240,000 / 365 = 657 emails per day for each person You are one of these persons! Do you feel happy about 657 unwanted emails every day? Is sending Spam ethical under Rule Utilitarianism? Students discuss … and assess overall happiness again! 14 Spam and Ethics Social Contract Theory evaluation of Spam Morality is the set of rules, governing how people are to treat one another, rules that rational people will agree to accept, for their mutual benefit, on the condition that others follow those rules as well Right to free speech as applied to mass communication Is sending Spam ethical under Social Contract Theory? Students discuss … also think of enforcement! And why we have Spam in our current society? 15 CAN Spam of 2003 Federal Law Controlling Assault of Non-Solicited Pornography & Marketing Largely unenforced Difficult, time-consuming, and resource intensive to track the sources of Spam Some successes Greco (2/2004), Goodin (1/2006) JumpStart (3/2006) $900k judgment But largely ignored Spam 75% of all messages in 2006, more AND larger percentage today in 2012 0.27% of Spam was compliant with guidelines for Spam Divides email into 3 categories; Spam should adhere to guidelines of these 3 categories, to be: 1. Transactional, 2. commercial, 3. unsolicited advertisement 16 CAN Spam 1. Transactional Sender and receiver have an established business or personal relationship Header, sender, and organization must be correct Can’t disguise identity of the sender from which message was sent 2. Commercial Commercial email messages to which user has consented to receive Same as above and must provide option to remove from list Mechanism to opt-out must include an Internet based method i.e. not an 800 number of the kind: “Your call is important to us!” Unsubscribe must be effective almost immediately, not in weeks Must contain the postal address of sender 3. Unsolicited Advertisement Must meet requirements of category 1 and 2 and: Must include clear and conspicuous evidence that the message is an advertisement 17 CAN Spam Critics call this the “You can” Spam Act You get one free shot at a user’s Inbox Does not prevent sending of Spam, but forces such messages into complying with defined rules Unsolicited messages must comply with all 3 types of rules Unsubscribe compliance Visible, operable opt-out (unsubscribe) mechanism for all types of messages with requests honored within 10 days Content compliance Accurate “From:” lines with relevant “Subject:” lines Legitimate physical address of publisher/advertiser If applicable, a label is present for adult content Sending behavior compliance No sending through open relays –i.e. server that blindly pass on/through email messages No sending via harvested email No deceiving, false headers 18 CAN Spam Exemptions Religious messages Political messages Content that complies with lawful marketing mechanisms National security messages Transactional or relationship messages from companies to existing customers Overrides state law Rushed passage to supercede a tougher California law Prohibits recipients from suing senders directly!! Penalties Misdemeanor to send with falsified header 19 CAN Spam Problems with the “opt out” provision in CAN Spam? For illegal email sender, your opting out means they know you exist; so they can and will send you more email May unsubscribe you, and send Spam from a different entity! Time provisions on length of unsubscription Allowable delay in unsubscription Create many LLCs to keep user receiving Spam?? What about a legitimate company? Is there a potential problem with opting out? Can they then sell your email address to another company? Is your email address your possession or theirs to use? What about non-US Spammers? 20 Class Exercise Step 1: Select a discussion leader in class room! How do you suggest to solve the problem of Spam in an ethical manner? Students propose a practical, legal method of curbing Spam, in a way that the Internet remains usable! Discuss Pros Discuss Cons Enforceable? Would this be an improvement over current situation? 21 Solutions to Spam 1. Require explicit opt-in to email lists 2. Require labeling of email advertising, e.g. “AAA subscription” in the subject line 3. Add a cost to every email that is sent 4. Ban all unsolicited email 5. 1991 – Telephone consumer protection act, included a provision against junk faxes 6. Provide fast method of unsubscribing: not 10 days! Do you see problems with these methods? All? Any? 22 Ethics & World-Wide Web 23 World-Wide Web Invented by Timothy Berners-Lee Proposed 1989, published 1991 Co-invented with Robert Cailliau Ref: http://en.wikipedia.org/wiki/Tim_Berners-Lee Hypertext system that is Decentralized Uniquely addressable (via URLs) Ubiquitous, internet based Applications E-commerce Social networks Content creation (wikis, blogs) News, Advertise Distance learning Pay taxes, shop at Amazon, Gamble, … 24 WWW & Censorship Should the Internet be filtered/censored? In our times, access to the internet is tightly controlled in some countries: e.g. North Korea, Cuba, China, Myanmar In others the content is tightly controlled, e.g.: Saudi Arabia (centralized control center in Riyadh blocks pornography, gambling, and sites offensive to Islam, government, royal family) China’s Great Firewall (human censors who perform similar functions) Special interesting cases of censorship: Germany: » Bans neo-Nazi web sites » Bans message denying Holocaust; denial illegal in 16 EU countries USA: » Controls pornography (Children’s Internet Protection Act) 25 Censorship During History Direct censorship Since the 4th century, the Catholic Church banned reading and possession of certain books List of books named Index, short for “Index Librorum Prohibitorum” List officially maintained by the Vatican, later by those cardinals who were “Inquisition Officials” Maintained until the mid 20th century --NOT a typo!! http://en.wikipedia.org/wiki/Index_Librorum_Prohibitorum During history: State execution, Church control, University responsibility for “Index” enforcement Catholic church did not have the executive arm in most countries to enforce that all books on “Index” be collected and burnt Was the duty of catholic states, delegated generally to the universities Last issue of “Index” was in the 1960s! Seriously, the 20th century! Today the Caßtholic church has no such official list Autocratic states like Saudi Arabia, North Korea, Myanmar, etc. today maintain similar prohibited lists of select Internet sites 26 Censorship Direct censorship Government information monopoly enables censorship Government controls all means of communication e.g. Soviet television stations, radio, etc. Hard to do with Internet; but being attempted! Prepublication review Sensitive classified documents must go through process to become declassified and publishable Licensing and registration Controlling who gets access (i.e. television stations being granted electromagnetic spectrum in exchange for something) Note that “selling frequencies” is a huge source of tax/income potential Self censorship Suppressing information as a means to an end CNN suppressed negative government info in Iraq to retain its office in Baghdad Voluntary rating systems so users can avoid certain content What is “voluntary?” 27 Practical Censorship Issues Many-to-many communication Prevents governments from controlling the content Gutenberg’s printing press invention raised difficulty of controlling books Note: printing was known in China before Gutenberg Dynamic New web sites opened and content continuously published New site-names created and deleted constantly Size Millions of sites, numerous pieces of information, mirror sites See WikiLeaks: shows Department of State content: ¼ million files, 1 event Global Limited authority for any government to restrict activities around the world Many countries have server farms; impossible to shut all down! Identity Difficult to distinguish children from adults, criminals from bona-fide users 28 Censorship & Ethics Where does censorship leave “freedom of expression”? Kant Censorship is clearly a backwards step Prevents people from getting information they need to make their own decisions John Stuart Mill, 1806 – 1873, British philosopher: None of us is infallible and knows the whole truth. Censorship may be silencing the voice of truth Majority opinion is not necessarily the whole truth Must allow others to express their opinions to get a better sense of truth Majority opinion must be tested and validated. Otherwise it is prejudice 29 Censorship & Ethics Is censorship of books, films, internet, posters practiced in the USA? Aside from limiting a.) pornography at internet sites, b.) offensive language, and c.) libel, there seems to be no censorship; see freedom of expression below! 30 Freedom of Expression Mill’s Principle of Harm The only ground on which intervention is justified is to prevent harm to others; the individual’s own good is not a sufficient condition Students: How does this apply to drug users who destroy themselves? How applicable to people, who wish to commit suicide? What ethical framework does Mill’s principle follow? Explains positions of most western democratic governments with regard to pornography Adults viewing hurt mostly themselves by doing so. as opposed to harming others But, what is your position, regarding the creators and publishers of pornography? Do they hurt themselves? Others? Note exception for children 31 Freedom of Expression in US Not an absolute right in eyes of the US Supreme Court See Supreme Court Justice Clarence Thomas’ dissentions Right is balanced against the public good Abuse of such freedom when harming the public can be punishable Libel, reckless or calculated lies, slander, misrepresentation, perjury, false advertising, obscenity and profanity, solicitation of crime, and personal abuse Example: Cigarette advertising on television How many cigarette ads have you seen recently? Ethical argument for why it should not be allowed: Student opinons? 32 FCC v. Pacifica Foundation Radio broadcast of George Carlin’s performance “Filthy Words” in 1973, preceded by warning of sensitive language A man had heard “filthy words” on car radio while driving with his young son; he complained to FCC FCC informed Pacifica Foundation: further complaints would lead to sanctions Pacifica sued FCC, but FCC won in a 5/4 Supreme Court decision of 1978 Note: limitations only for public radio and TV, not for cable and other subscriber programs Ref: http://en.wikipedia.org/wiki/Seven_dirty_words 33 FCC vs. Pacifica Foundation Broadcast media are uniquely pervasive and invasive Indecent material broadcast into privacy of homes People can turn it on-off at any time, making the warning ineffective Damage is done as soon as it is heard, i.e. can not undo its harm by turning off devices retroactively Uniquely accessible to children Can restrict access in bookstores and movie theaters Time of day is an important consideration, however, for broadcast radio/television Students debate and exercise: Ethics analysis! Kant’s CI, Act U., Rule U., Social Contract 34 Censorship and Children Child Internet Protection Act (CIPA) Government requirement for installing anti-pornography filters before receiving federal funds for Internet access Argument for: Libraries do already abstain from offering X-rated magazines or movies So they should not be obliged to filter Internet pornography Argument against: Filters restrict freedom of speech Upheld by U.S. Supreme Court in 2003 It is not the role and function of libraries to provide a public forum for free speech; can be exercised elsewhere 35 Is CIPA Ethical? Kantian evaluation of protecting children from harm using filters Assumption is that some non-pornographic web pages are filtered Filters treat creators of non-offensive, blocked pages as a means to the end for restricting children’s access to pornographic materials Act utilitarian evaluation Up to each of us Enacting CIPA results in fewer children being exposed Some legitimate sites will be filtered accidentally Stigma, discomfort for legitimate users getting sites unfiltered Social contract theory evaluation Private viewing of pornography does not make social living impossible Public libraries offer arguments on both sides (assumption is that filters block some useful sites) 36 Catch Chat-Room Predators Police sting operations to lure pedophiles Ethical? Kantian analysis Is the will leading to the sting action OK? Yes and no: Overall goal is good; but that is not of prime interest to CI Deceptiveness is always wrong to a Kantian! Utilitarian analysis Result is public benefit (OK to harm one pedophile so society benefits) Publicity may deter other pedophiles What is the impact on chat rooms as an effective medium for communication if one knows one is being “watched”? Social contract theory analysis Misrepresentation by pedophile should be punished Police are also misrepresenting themselves Not a clear cut argument under Social Contract theory 37 Discussions Suppose 99% of all email from country X is Spam Discuss the ethics behind blacklisting all email from country X: Kantian Act Utilitarianism Rule Utilitarianism Social Contract 38 Discussions Definition MMORPG: Massively Multiplayer Online RolePlaying Game Discuss the ethics behind a rule in China, mandating a time-limit for playing MMORPGs. Is this law moral? What would the judgment depend upon? Kantian Act Utilitarianism Rule Utilitarianism Social contract theory 39 Discussions Discuss the ethics of posting photos on-line without the permission of those who appear in them Are there situations when it would be unethical? If so, what are they? Kantian Act Utilitarianism Rule Utilitarianism Social contract theory 40 References Spam: http://www.etymonline.com/index.php?search=spam&searchmode=none File Transfer Protocol: http://tools.ietf.org/html/rfc821 SMTP: http://www.smtp2go.com/articles/smtp-protocol.html Mill’s utilitarianism: http://en.wikipedia.org/wiki/John_Stuart_Mill Clarence Thomas supreme court dissentions: http://blog.beliefnet.com/watchwomanonthewall/2011/06/court-rulesagainst-parents-justice-thomas%E2%80%99-dissent-protects-children-bysteve-birn.html MMORGPG: http://en.wikipedia.org/wiki/Massively_multiplayer_online_roleplaying_game FCC vs. Pacifica: http://www.bc.edu/bc_org/avp/cas/comm/free_speech/pacifica.html Phishing at Microsoft: http://www.microsoft.com/security/resources/phishing-whatis.aspx Phishtank: http://www.phishtank.com/what_is_phishing.php Index of Prohibited books: http://www.aloha.net/~mikesch/ILP-1559.htm Holocaust denial: http://www.jewishvirtuallibrary.org/jsource/Holocaust/denial.html 41