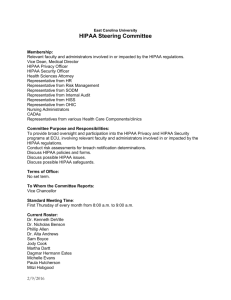
hippa
advertisement

1 A Model for HIPPA Security Policy Deployment Can the cost of HIPAA security compliance be quantified? Introduction This research examines the issues related to the cost of compliance for the HIPAA security regulation. The cost to comply, while relevant to any organization affected by this ruling, was slightly neglected by the legislature as the rule was being drafted. Quite simply, the rule provides no insight into the costs associated with complying with its statutes. This leads the authors to focus on several questions concerning this issue. First, is there a method for quantifying the risk of not being compliant with the HIPAA security rule, and is there a way to indicate what risk a health organization inherits by ignoring their responsibilities to this rule? Second, based on the quantified risk for a specific organization, is there any method, model, or equation that can be utilized to calculate a reasonable IT security budget earmarked for this effort? Finally, given a budget, is there a model or procedure for dispersing this monetary resource in the most effective and constructive manner? These questions provide the context from which the authors approached this paper. It is divided into three parts. The first part provides a concise introduction to the HIPAA security rule. The second part introduces a model for estimating the cost of not properly complying with the HIPAA security rule. The third part discusses our Policy Deployment Model for Minimum HIPPA Security. Part I - The HIPAA Final Security Rule The Health Insurance Portability and Accountability Act (HIPAA), passed in 1996 by the Senate and House of Representatives, charged the Department of Health and Human Services (HHS) with the implementation and enforcement of its measures.1 The purpose, as originally drafted, had four primary objectives: To assure health insurance portability by eliminating job lock due to pre-existing medical conditions; to reduce healthcare fraud and abuse; to enforce standards for health information; and finally, to guarantee security and privacy of health information. 2 As articulated by Blue Cross Blue Shield: Brian Lemoine. “HIPAA compliance cost may exceed Y2K,” Triangle Business Journal In Depth: Health 13 March 2000, 18 Nov. 2003 <http://www.bizjournals.com/triangle/stories/2000/03/13/focus6.html>. 2 45 CFR Part 160 and Subparts A and E of Part 164 1 2 “The Health Insurance Portability and Accountability Act of 1996 is intended to reduce the costs and administrative burdens of health care by making possible the standardized, electronic transmission of many administrative and financial transactions that are currently carried out manually on paper.” 3 Because the scope of the HIPAA rules are so broad and comprehensive, the focus of this paper is limited to the final security rule, published by the Department of Health and Human Services on February 20 th, 2003. The final security rule mandates that all covered entities provide confidentiality, integrity, and availability of all electronic protected health information (EPHI) that is collected, maintained, used, or transmitted. 4 A covered entity is defined as a health plan, a healthcare clearinghouse, or a healthcare provider that stores or transmits EPHI.5 The security rules were written to adhere to three basic tenets. Each tenet focuses on providing a regulatory architecture that can be applied to entities of any size. The regulation must be comprehensive, scalable, and technology neutral. 6 To achieve these three principals, the rule was written more as a set of generally enforceable guidelines, intended to require each covered entity to interpret how this rule should apply to their own best security controls. Because of its tone, these general statutes lack a level of granularity, which would help guide organizations on how to implement them. Each security standard is broken down into required and addressable implementation specifications. Covered entities must implement required specifications and have a choice to implement the addressable specifications.7 “The entity must decide whether a given addressable implementation specification is a reasonable and appropriate security measure to apply within its particular security framework.”8 The regulation declares four actions that a covered entity may take for addressing the implementation specifications: (1) implement one or more of the addressable implementation specifications; (2) implement one or more alternative security measures; (3) implement a combination of both; or (4) not implement either an addressable implementation specification or an alternative security measure. 9 The focus of this paper addresses how to determine, based off of risk, how much in resources should be spent, to comply with these rules. The nature of the rule requires that each covered entity acknowledge 3 EDI Glossary. BlueCross BlueShield of Kansas. 9 Nov. 2003 <http://wwww.bcbsk.com/prviders/edi/edi_glossary.htm>. 4 45 CFR Part 164 Introduction 5 45 CFR Part 160.103 6 HIPAA Consensus Research Project. 27 March 2003. SANS Institute. 13 Oct. 2003 <http://www.sans.org/projects/hipaa.php>. 7 45 CFR Part 160. FR 8335 8 Id. at FR 8336 9 Id. 3 that the rules must be addressed, but leaves great freedom as to how to address them. This situation calls for some type of decision matrix and risk analysis model that would help guide organizations on how their particular entity should account for these rules from both a risk perspective and from a policy deployment perspective. It is the intent of the authors to articulate that by combining both methods, an organization is given a greater understanding of how they should act and spend money towards compliance with these rules. The following sections provide two models, that when used together, provide a clear way of addressing these problems. Part II - A Model for Estimating the Cost of Non-Compliance of HIPAA Security A major hindrance overshadowing the issue of network security, and more specifically HIPPA security, is convincing executives that securing their networks is a prudent and necessary investment. A 1999 Information Security Magazine Survey indicates that 69% of respondents feel that the greatest obstacle towards better network security lies with senior management.10 “One of the biggest challenges is getting senior management to take the problem seriously, and to commit resources to it.” 11 More recently, executives have focused an increasing amount of attention on the issue due to recent regulation. Another study encompassing 7,500 senior information technology executives, found that 62 percent of these companies will increase spending on security for 2003, compared to 50 percent in 2002.12 Roughly two-thirds of those polled said they adopted security measures to limit liability, and almost half said it was to comply with regulations such as Sarbanes-Oxley and HIPAA.13 Legal and regulatory requirements for data integrity/confidentiality and consumer privacy are seen as the most compelling arguments for a strong security program.14 But even with this new found compliance, it seems that few executives truly understand how their efforts, and dollars, will pay off. Management cannot draw a clear connection between the dollars spent on securing and fortifying networks, and the intrinsic return on this type of investment. Given that many executives focus undying CBL 7 – The survey’s actual results state that only 14 percent of the respondents identify senior management as the primary obstacle. The report indicates that 29 percent of respondents identify budget constrains as the primary issues, 10 percent identify unclear responsibilities, eight percent state it is a result of lack of internal policies and yet another eight percent attributed the problem to lack of centralized authority. The authors of this paper infer that all four other issues are a direct result of senior management’s attitude towards information and network security at the time and then can all be attributed to a senior management bottleneck. 11 “Some way to go Readers still doubtful over HIPAA rules.” SC Online Magazine March 2003. 20 Oct. 2003 <http://www.scmagazine.com/scmagazine.2003_03/special/02.html>. HGL 10 12 Robert Lemos. “US execs go security spending crazy.” Silicon.com 30 Sept. 2003. 2 Nov. 2003 <http://www.silicon.com/software/security/0,39024655,10006206,00.htm>. 13 Id. 14 Andy Briney. “2001 Industry Survey.” Information Security Oct. 2001. 15 Oct. 2003 <http://infosecuritymag.techtarget.com/articles/october01-/images/survey.pdf>. 10 4 attention to the bottom line; their aversion to this type of investment is understandable. Network security is viewed today, as fire sprinklers were viewed a century ago; a waste of money. In 1882, sprinklers were considered to be as dubious an investment as information security is today. CEOs and CFOs want to see quantifiable proof of their return on investment before they outlay any funds. 15 In some ways, their argument is as sound as the one supporting network security. However, the number of successful security breaches continues to rise.16 For example, the number of verifiable worldwide hacker incidents for the month of January 2003 is about 20,000, which far exceeds the previous record of 16,000 set in October of 2002. 17 According to the Computer Security Institute’s Computer Crime and Security 2003 Survey, 80 percent of the respondents acknowledged financial losses to computer breaches with each intrusion averaging in the millions of dollars. 18 Even with the potential for the tremendous financial losses illustrated in the previous paragraph, there is still no complete model designed to suggest and justify how much money should be spent to help negate these risks. “Lacking any way to translate such statistics into expenditures and losses per organization, per computer, or per user, the true impact of these figures remains uncertain.” 19 In 1882, a man named George Parmalee set a Bolton, England, cotton factory on fire to help sell his newly invented sprinkler system.20 His intention was to convince the factory owner that while the probability of fires may be remote, the damage incurred from just one incident could be devastating; and that any investment aimed at deterring such an event was well worth it. While the approach introduced in this paper excludes the utilization of any combustible devices, some of the underlying concepts remain similar to what George Parmalee tried in the late 1800s. This model intends to articulate what costs and liability factors are presented to CIOs who do not take HIPAA compliance seriously. The authors call this model, the “Cost of Non-Compliance HIPAA Security Model”. The specifics of this model are detailed below. Explanation of the Model Scott Berinato. “Finally, a Real Return on Security Spending.” CIO Magazine 15 Feb. 2002. 2 Nov. 2003 <http://www.cio.com/archive/021502/security.html>. 16 The authors recognize that this statement is more of a generalization than anything, but the statistics that follow it support its merit. However, the authors also recognize that a portion of the reported increase may simply be a result of an increased rate of reported incidents and a more comprehensive use of the tools to actually detect these breaches. With more tools being used, there should be more comprehensive results. 17 Bob Tedeschi. “Cybercrime, they just don't mention it.” The Age 30 Jan. 2003. 19 Oct. 2003 <http://www.theage.com.au/articles/2003/01/30/1043804447447.html>. 18 Id. 19 Rebecca Mercuri. “Analyzing Security Costs” Communications of the ACM Vol. 46, No. 6 June 2003: 15-18. 19 Oct. 2003 <http://www.notablesoftware.com/Papers/SecCost.html>. 20 Scott Berinato. 15 5 ”Hand in hand with the increase in awareness of the need for computer security has come the need for a method of quantifying the impact of potential threats on organizations.” The underlying framework of this model is centered on a general risk analysis. Risk analysis is defined as: The process of identifying security risks, determining their magnitude, and identifying areas needing safeguards. It is a tool used as part of any risk management system and is synonymous with risk assessment.21 The first major publication addressing the topic of risk analysis, 22 was the Federal Information Processing Standards (FIPS) Publication Number 65.23 Published in August of 1979, the FIPS Publication became the de facto standard from which all subsequently published Risk Assessment methodologies are compared. The end results of the FIPS risk analysis model are annual loss exposure values based on estimated costs and recognized potential losses. 24 Since the publication of the 1979 FIPS model, there have been various other approaches and models designed to attack this issue from alternate angles. The FIPS model uses a quantitative approach, while other, newer models, use a qualitative approach for ease of preparation and speed of execution. 25 It was felt by some security experts that the quantitative approach was too complicated and time consuming to implement on a mass scale, and sought out to find an easier approach to implement. This resulted in the creation of several new qualitative approaches. The authors identify two of these methods. The first was a replacement to the FIPS 65 publication, released in 2001, and titled “Risk Management Guide for Information Technology Systems”. The second is the Facilitated Risk Analysis Process (FRAP). The authors chose, for this paper, a model created by Rita C. Summers, which is based on the original FIPS 65 framework. This model provides the underlying architecture for the cost model discussed in this paper.26 Summers’ model proposes a simple four step method towards risk analysis. First, identify an organization’s assets that could possibly be compromised by security breaches, and assign monetary values to them. Second, identify the threats and the vulnerabilities faced by this organization. Third, calculate the annual loss expectancy (ALE) for each threat. Finally, identify potential safeguards and estimate how much each one would help reduce exposures.27 21 Glossary of Vulnerability Testing Terminology. 28 May 2002. University of Oulu. 19 Oct. 2003 <http://www.ee.oulu.fi/research/ouspg/sage/glossary/>. 22 See Will Ozier. “Issues in Quantitative Versus Qualitative Risk Analysis.” (Datapro 4 May 1999) 2. - First formal recognition in the information technology environment was with the publication of the Federal Information Processing Standard (FIPS) 31 titled, Automated Data Processing Physical Security and Risk Management 23 United States. National Bureau of Standards. Federal Information Processing Standards Publication. FIPS PUB 65. 1 Aug 1979. 24 Federal Information Processing Standards Publication 1. 25 Will Ozier 4. 26 Summer’s model is described in detail in his book: Secure Computing - Summers, Rita. C. Secure Computing. New York. Mcgraw Hill, 1997. 27 Olivia Carter, Deb Frinke, Chris Ritter, and Huaqiang Wei. CSI 28th Annual Computer Security Conference, October 29-31, 2001: Cost-Benefit Analysis for Network Intrusion Detection Systems. (University of Idaho: Center for Secure and Dependable Software, 2001) 6 The Cost of Non-Compliance HIPAA Security Model uses the first three steps that Summers proposes as its foundation, but replaces the fourth step with an alternate approach. Instead of analyzing how different safeguards will help reduce exposure, the authors are interested in using this model for a different kind of output. As the title suggests, the output provided by the fourth step of this model will articulate how much could be lost by a particular organization, if investments are not made to help secure a given network for HIPAA compliance. Therefore, this model’s final step quantifies the risk of doing nothing to influence executives to spend the appropriate dollars towards this effort. The next several paragraphs will describe each step in greater detail. Step I - Identify Assets “The Task of identifying assets that need to be protected is a less glamorous aspect of information security. But unless we know these assets, their locations and value, how are we going to decide the amount of time, effort or money that we should spend on securing the assets?” 28 The first step to identifying assets attempts to answer the question, “what are a given organization’s critical assets?” In other words, which assets are critical and essential for the day to day operation of the business and which help maintain the businesses long term viability? Once these assets are identified, they then must be classified into distinct categories. This paper classifies all assets into one of five categories; Network Assets; Software Assets; Equipment Assets; Data/Information; and Other. 29 The organization’s identified tangible and intangible assets such as software, information, and personnel would be placed into their appropriate categories.30 Appendix A provides a comprehensive diagram with a hypothetical organization’s assets identified and classified into their respective categories. Once identified, all assets then need to be assigned an estimate of their intrinsic value. “The value of an asset consists of its intrinsic value and the near-term impacts and long-term consequences of its compromise.”31 In reference to the scope of this model, it should be noted that a covered entity is only responsible for those assets that are under their direct ownership. Other property that can be placed on the balance sheet as assets, but are rented or obtained through some sort of partnership, such as any off premise <http:///wwwcsif.cs.ucdavis.edu/~balepin/new_pubs/costbenefit.pdf> 28 Avinash Kadam - Published Network Magazine - December 2002 29 James Meritt. “A Method for Quantitative Risk Analysis.” 5 Oct 2003 <http://cswww.ncsl.nist.gov/nissc/1999/proceeding/papers/p28.pdf>. 30 Will Ozier 31 United States. National Institute of Standards and Technology. Generally Accepted Principles and Practices for Securing Information Technology Systems. SP 800-14 (Sept.1996. comp. Barbara Guttman, and Marianne Swanson) 19. 7 networks, or leased business machines, do not need to be included for this analysis. Finally, while business partners whom the covered entity shares Personal Health Information (PHI) with, are not included in this assessment, their compliance with the HIPAA standards is still mandatory. 32 Step II - Identify Threats and Vulnerabilities Once the critical assets of a particular organization have been identified and values have been associated to them, a comprehensive list of threats and vulnerabilities for each asset must be identified. A threat is an entity or event with the potential to harm the system. Threats come in many forms, but typical ones may be: simple or hidden errors, fraud, disgruntled employees, hackers, or viruses. 33 “Threats should be identified and analyzed to determine the likelihood of their occurrence and their potential to harm assets.”34 Table B.1 provides a more comprehensive list of threats. Step III - Calculate Annualized Loss Expectancy After the list of the threats and vulnerabilities has been compiled, the next step is the calculation of the annual loss expectancy. The annualized loss expectancy equation is: 35 Figure 2.1 SLO AV EF ALE =Annualized Loss Expectancy ALE SLO ARO ARO =Annualized Rate of Occurrence ALE AV EF ARO AV =Asset Value EF =Exposure Factor SLO Single Loss Exposure “Exposure factor is the measure of damage, harm, or loss resulting from a threat or event usually expressed as a percent (0%-100%).”36 Exposure factor is the value lost from the threat in relation to a specific asset. Figure C.2 provides a comprehensive list of exposure factors. The annualized rate of occurrence estimates how often a threat might be expected to occur, expressed on an annualized basis 3245 CFR 164.314 RF 8358 Generally Accepted Principles and Practices for Securing Information Technology Systems 19. 34 Id. 35 Will Ozier 2. 36 Id. at 3. 33 8 (e.g., a threat that is expected to occur once every ten years would have a threat frequency of one tenth or 0.1).37 The best way to calculate the ALE, is to create four matrices in a spreadsheet. Each matrix will represent one of the following: asset value, exposure factor, annualized rate of occurrence, or annualized loss expectancy. Each matrix would include assets on the column headers and threats and vulnerabilities on the row header. The intersection of the matrix would include asset value, exposure factor, annualized rate of occurrence, or annualized loss expectancy. The ALE matrix would be the multiplication of the asset value, the exposure factor, and the annualized rate of occurrence. An example of how these matrices would be formatted is illustrated below in Figure 2.2. Appendix C contains a more comprehensive example Accidental Errors Computer Virus AV Accidental Errors Computer Virus EF Accidental Errors Computer Virus ARO at io Accidental Errors Computer Virus tw a Eq re ui pm en Da t ta n /In fo rm = Annualized Loss Expectancy Data Integrity Loss So f X Annualized Rate of Occurrence Data Integrity Loss So ftw a Eq re ui pm en Da t ta n /Inf or m at io Asset Value Data Integrity Loss tw a Eq re ui pm en Da t ta n /In fo rm at io X So f So f Asset Value Data Integrity Loss tw a Eq re ui pm en Da t ta n /Inf or m at io Figure 2.2 ALE Step IV – Summarize Total ALE for Organization This step calculates the total ALE for the covered entity and consists of a summation of all the intersections in the ALE matrix. The output of the Cost of Non-compliance HIPAA Security Model is this single number. This determines how much risk one is exposed to, expressed in monetary terms for not being compliant to HIPAA Security. The total ALE for an Organization would provide the business case needed to get executives to focus more resources towards HIPAA security compliance. It was the intention of the authors to use this model, in conjunction with a formula, to come up with specified monetary levels that a particular organization should spend to avoid a certain degree of liability or potential loss. Essentially, based on the Cost of NonCompliance HIPAA Security Model, a consulting firm would be able to calculate potential losses for a particular organization and using a formula, could calculate the budget needed to mitigate degrees of risk. This formula would be able to provide the ROI on security investments that every organization has had to do without. It would provide a direct correlation between the amount of money spent, and the level of risk 37 Id. 9 and liability assumed, providing each CIO or CSO with a justifiable budget that would provide the ROI that CEOs and CFOs want to see.38 Given this budget, we adjust our focus towards the second model introduced in this paper, which is able to take this figure and allocate each dollar et, most efficiently. Part III - The Policy Deployment Model for Minimum HIPPA Security The Policy Deployment Model for Minimum HIPAA Security consists of several interrelated management concepts that will be discussed prior to the model itself. For ease of comprehension, each of the three concepts will be contained within its own section. The first discusses the management concept of Hoshin Kanri. The second articulates how Hoshin Kanri is modeled using matrices. Finally, the last section will discuss the theory of closed loop planning, and its role within the Hoshin Kanri management concept. Hoshin Kanri Hoshin Kanri - also called Hoshin Planning - or just Hoshin, is a Management System best used for determining the appropriate course of action for any given organization and its set of unique circumstances. 39 It provides, “an extended period of time for the organization to focus its breakthrough effort while continuously improving key business processes day to day.” 40 The importance of this type of management system is that it focuses a series of short-term projects on long term goals. Using these projects, Hoshin Planning aligns an organization with the goals that are identified as being most critical to its success. Hoshin Planning uses Key Performance Indicators to measure progress towards the goal.41 Hoshin Planning has been applied in many Japanese companies such as Toyota, Honda and Mitsubishi. US companies such as Hewlett Packard, Intel, and Proctor and Gamble have also implemented Hoshin Planning.42 Matrices A fully implemented Hoshin Planning model consists of many levels of matrices that drill down predefined goals into clearly defined tasks.43 The top or highest level matrix provides a general overview of how far along an organization is in meeting its goals. This level defines goals and metrics that help 38 The authors fell short of providing this equation do to lack of time and real attainable data. Therefore this portion of the paper is of a purely academic nature. 39 Michael Cowley, and Ellen Domb. Beyond Strategic Vision: (Effective Corporate Action with Hoshin Planning. Newton: Butterworth-Heinemann, 1997) 4. 40 “Breakthrough Effort” is the process of focusing the resources of a given business towards one strategic, well defined vision. It is a long term, clearly ingrained goal of an organization. See David A. Kenyon. “Strategic Planning With the Hoshin Process.” Quality Digest Magazine 1997. 26 Oct. 2003 <http://www.qualitydigest.com/may97/html/hoshin.html>. 41 John Reh. “Key Performance Indicators (KPI).” About.com. 22 Oct. 2003 <http://management.about.com/cs/generalmanagement/a/keyperfindic.htm>. 42 “Catchball Processes.” Baldrigeplus.com 1999. 28 Oct 2003 <http://www.baldrigeplus.com/Exhibits/Exhibit%20%20Catchball%20processes.pdf>. 43 “Hoshin Kanri.“ Pdponline 2002. 9 Nov. 2003 < http://www.geocities.com/parthadeb/hosinkanri.html>. 10 identify when each individual goal or step has been met. Each subsequent level takes the metrics specified in the model’s previous level, and makes them the new goals with a new set of metrics. In short, the first level of the matrix can identify what the problem is and the current progress made in solving this problem. The next level will indicate where, more specifically, the problem lies, and the last or lowest level will pinpoint which group within the company, the problem belongs to. Closed Loop Planning Embedded within the Hoshin model, is a concept titled Closed Loop Planning and the PDCA cycle. Closed Loop Planning is the lifecycle used to execute a Hoshin model. PDCA, diagramed in Figure 3.1, is simply an acronym, which stands for Plan, Do, Check, Act. The purpose of the closed loop model is to provide continuous improvement to an organization’s bottom line, and the business processes that support it. Figure 3.1 47 In theory, the Closed Loop Planning process is easily understandable, and corresponds well with what has already been explained in this section. Using the goals defined through the Hoshin model, management defines tasks or plans that help the organization meet these goals. This process takes place in the “Plan” stage of the PDCA cycle. The employees of the organization then take these plans and implement them in the “DO” stage. Next, management uses the metrics defined in the Hoshin model and measures the results of the tasks that were implemented against the stated goals. This is the “Check” phase. In the “Act” stage, the results from the metrics are analyzed, and any unwanted consequence or shortcomings from the executed plan are acted upon. Finally, the process comes full circle, and new tasks or plans are defined, implemented, checked and acted upon in a continuous fashion; always improving the organization and its business processes. Four Issues Regarding HIPAA Security Addressed by This Model “Without a proactive metric tracking process, you cannot quantify the incremental level of effort, or incremental expense, involved in maintaining your organization's compliance with the HIPAA Privacy Regulations. Having such a process allows you to measure and validate your ongoing compliance with the regulation.”44 “Monitoring your Privacy Compliance.” HIPAAnotes Volume Three, June 2003. 1 Nov. 2003 <http://www.hipaadvisory.com/note/vol3/june03.htm>. 44 11 There are four issues regarding the implementation of the final HIPAA security rule that the authors wish to identify and discuss.45 First, while the final rule provides general requirements or guidelines towards compliance, it fails to clarify how these rules apply to specific organizations. 46 Second, the rule is lacking specific metrics that help organizations visualize their effort towards compliance, or lack there of, for each requirement. Third, the rules do nothing to address the prioritization of these requirements based on the organization that is implementing them. Finally, the rules fail to quantify even the most basic of costs associated with becoming compliant. The Policy Deployment Model for Minimum HIPAA Security is uniquely designed to address these four points. The model addresses the first point by defining the minimum requirements, using Hoshin Planning, in an easily understandable format that can be observed and fully consumed at a moment’s glance. To address the second point, the model then identifies metrics for each of the defined requirements that provide data and information about key processes, outputs, and results critical to the success of deploying any policy within an organization. 47 Through the use of Hoshin Planning, the model solves the third issue, by prioritizing each of the defined requirements, based on their specific importance to the organization. Finally, the model addresses the last issue by providing qualified estimates of the implementation costs for each requirement. Each of these four points is discussed in more detail below. Defining Minimum Requirements Minimum security requirements are interpretations taken from the HIPAA security rules. Each requirement is either a required implementation specification or an implied intent of the final rule that was not directly translated into a required implementation specification. 48 This model takes these minimum security requirements, and matches them to a series of best practices. “Best practices represent proven methodologies for consistently and effectively achieving a business objective.” 49 Defining Metrics Essential to the deployment of any policy throughout an organization, is the ability to define and measure key performance indicators (KPI) and non financial indicators (NFI).50 When implemented properly, KPIs 45 This list of problems is not all inclusive Richard Marks, and Paul Smith. “Analysis and Comments On HHS’s Just-Released HIPAA Security Rules.” Davis Wright Tremaine LLP 17 Feb. 2003. 3 Nov. 2003 <http://www.nacua.org/documents/DWT_Security_Rules_Initial_Analysis_021703.pdf>. 47 James Evans, and James Dean. Total Quality: Management, Organization, and Strategy. 3 Ed. (Harrisonburg: South-Western 2003) 23. 48 An implied intent is a requirement that is specified within the rule, but was not actually indicated as a required implementation specification. As an example, the final security rule has the implementation specification of training as “addressable”, yet in the introduction, HHS regards training as a need for the rules. 49 “What are Best Practices?” Siebel Systems 2003. 5 Nov. 2003 <http://www.siebel.com/bestpractices/whatare.shtm>. 50 Key Performance Indicators, also known as KPI or Key Success Indicators (KSI), help an organization define and measure progress toward organizational goals. They are quantifiable measurements, agreed to beforehand, that reflect the critical success factors of an organization See 46 12 and NFIs possess the ability of keeping management up to the minute on how an organization is progressing towards a specified goal. As Peter Drucker, a prolific writer on subjects relating to management, stated in his famous quote, “If you can’t measure it, you can’t manage it” 51 A critical step in the policy deployment process is deciding what metrics are going to be used to accurately asses the progress towards compliance. If the wrong KPIs of NFIs are used, the perceived progress could be misleading, and result in costly mistakes and errors. In some circumstances, poorly chosen KPIs or NFIs lead organizations to grossly miss their identified goals. This point only reinforces that careful consideration should be put towards defining the KPIs and NFIs used to measure performance. With this in mind, the authors decided that the Policy Deployment Model for Minimum HIPPA Security would use security metrics defined by the National Institute for Standards and Technology (NIST). Deployment Prioritization of Minimum Requirements As with any policy deployment model, an organization must develop strategies to reach their selected goals. Strategies are organized by importance and supported by facts and data that is obtained from careful research and study of the relevant technical and/or managerial disciplines. 52 This model extends this principal in order to show which metrics, relating to a certain criteria, have the highest degree of relevance. This allows an organization to appropriate funds towards compliance, based on the rating of the metric’s importance for the implementation specification. Multiple metrics can be used to measure the success of the compliance effort. When one or more of the implementation specifications are non-compliant for multiple related metrics, an organization needs to prioritize its efforts in resolving this issue. The priority is determined through the perceived importance that each of the metrics has on reaching the compliance goal of the implementation specification. Initially, this prioritization comes from within the organization and has no formalized procedure specifying which metrics map most closely to the implementation specifications. 31 What this means is that the first round of prioritization is carried out by individuals and their understanding of the organization. Once these metrics are chosen, an analysis of variance (ANOVA) is used to measure the relevance of each metric to the given implementation specification.53 ANOVA is used to uncover the main John Reh. “About Peter Drucker.“ The Business World According to Peter F. Drucker. 1 Nov. 2003. <http://www.peterdrucker.com/about.html>. 52 Cowley, Michael and Ellen Domb. Beyond Strategic Vision: Effective Corporate Action with Hoshin Planning. Newton, MA. Copyright 1997. 53 Professor Jeffrey Luftig. Personal Interview. 3 Nov. 2003. Leeds School of Business – University of Colorado at Boulder. 51 13 interaction effects of categorically independent variables 54 (called "factors") on an interval dependent variable.55 Estimating cost of Implementation “Different industry surveys indicate widely varying results pertaining to security costs vs. return on investment (ROI).”56 While these surveys provide some cost guidance for HIPAA compliancy, the majority of expenditures are based on the current problems that the organization faces, which leaves them open to risk.57 The Policy Deployment Model for Minimum HIPAA Security Compliance uses prioritization to measure the current problems in compliance faced by an organization, and then gives an estimate for the associated costs in becoming compliant. In the event that an organization is not compliant for a given HIPAA requirement, this model can be used to identify the problem by looking at the metrics that are not meeting the target amount and then show an estimate of the costs that should be spent in order to become compliant. The Policy Deployment Model for Minimum HIPPA Security The model uses three levels of matrices to create a compliancy plan. The breakthrough focus, based on the minimum requirements of the security rules, represents compliance, and is defined in the matrix by the column heading in level 1 depicted in Figure 3.1. The row headings for level one translates the standards and required specifications into best practices that correlate to one or more column headings. The row also defines metrics to measure the implementation performance of each row. The intersections of the row and column headings are linked with a prioritization weight. In relation to the PDCA cycle, these metrics are then used in the check phase, and are prioritized for budgeting and resource allocation purposes. Level 2, depicted in Figure 3.2 links the requirements of the security rules to the clearly defined tasks through the intermediary of best practices. Level 3, shown in Figure 3.3, identifies best practices with even more granularity, and defines tasks more specifically, which again are quantified by metrics and weights. Figure 3.1 (Level 1) 54 Figure 3.2 (Level 2) Figure 3.3 (Level 3) Independent variables that have no relation to one another. Interval independent variables can predict the dependent variables but dependent variables cannot be used to predict them. 55 Interval dependent variables are influenced by independent variables. Changing an independent variable that corresponds to one of these will have an effect on it. (reword / get source) See “ANOVA.” Quantitative Research in Public Administration. 21 Oct. 2003 <http://www2.chass.ncsu.edu/garson/pa765/anova.htm>. 56 “Security Budgeting.” HIPAAnotes Volume Three, August 2003. 21 Oct. 2003 <http://www.hipaadvisory.com/note/vol3/june03.htm>. 57 James Morrison. “From Strategic Planning to Strategic Thinking.” HORIZON Site 2003. 6 Nov. 2003 <http://horizon.unc.edu/projects/OTH/2-3.asp>. 14 Compliance Yes 3 Compliance Yes 2 100% Y Mon An 90% Y 1 $50 0 2 $100 0 Yes N An Y 3 $300 0 The model identifies the tasks required to meet compliance through these varying levels of granularity. Level one looks at the entire problem from a birds eye view. Each subsequent level, focuses on one small portion of the problem, until eventually the root cause is identified. For accountability, each task will have a specified owner, who is responsible for its success. Costing starts at the lowest level, where each specified task is given a cost estimate. Costs start at the bottom and are aggregated upwards because of the nature of the model. Each task is defined most specifically at the lowest level, so it becomes clear as to where money is spent by applying costs at this level. As the levels aggregates up, the total for all tasks on the lower level is summarized for the more general tasks on the next higher level . Conclusion The authors’ original intent was to create a business case for compliance of the HIPAA security rule, establish a security budget, and provide a way to optimize that budget’s allocation. The business case would produce an input to establish a security budget. In turn the security budget would be inputted into the policy deployment model for minimum HIPPA security. This task proved to be extraordinarily difficult due to the infancy of the rule and the apparent drought of real world data. The end result of this paper is two models of a much more academic and theoretical nature that the authors believe will produce terrific results when given real data. The first model estimates costs incurred by non-compliance. These costs would then theoretically be fed into an equation that’s output would provide a budget to be put towards compliance towards the HIPAA security rule. Due to the lack of real world data, this equation was not included in this paper. It was realized by the authors that in order to formulate such an equation, several iterations of this model would have to be tested in real world scenarios. This is a task that reaches outside the scope of this paper. The second model would then Result Hours of Labor Total Labor Cost Equipment Cost Total Cost 3 Target 3 2 $300 $100 0 0 Metric 3 $150 0 Target Frequency Result Metric 4 Clearly Defined Task 3 100% 100% Y Ann Ann Ann 95% 100% Y Clearly Defined Task 2 3 Compliance Yes Compliance Yes Yes Level 3 Breakdown Best Practice 1 Breakdown Best Practice 2 Breakdown Best Practice 3 Clearly Defined Task 1 4 Result 2 Target Hours of Labor Total Labor Cost Equipment Cost Total Cost Metric Target Frequency Result Metric Breakdown Best Practice 3 Level 2 Metric 1 Metric 2 Breakdown Best Practice 2 5 $250 0 Compliance Yes Compliance Yes Compliance Yes Breakdown Best Practice 1 3 $300 0 Result 100% Yes Ann Ann 80% Yes Target 4 2 Best Practice 2 Hours of Labor Total Labor Cost Equipment Cost Total Cost 3 Best Practice 1 Best Practice Metric Target Frequency Result Metric Metric 2 Metric 1 Level 1 Security Rule 1 Security Rule 2 Security Rule 3 15 take this budget and prioritize the money using an intricate policy deployment model. The authors believe the work set forth will provide valuable business data when applied to specific covered entities and their real world situations. 16 Appendix A - Assets Figure A.1 – Asset Overview58 Assets Network/ telecommun ications Software Equipment Data/ information Other Figure A.2 – Network/telecommunications59 Network/ telecommun ications Modems This category consists of the various modems both internal and external. Any system used to connect information systems to communication lines is contained within this category Figure A.3 – Software60 58 James Meritt 2-3. IBM Id. 60 Id. 59 Routers This category contains those items of information technology which are identified as routers, gateways, hubs or serve a similar purpose. Cabling Other This category includes special purpose cabling identified for the information technology but does not include that which is installed as part of the operating area (e.g. built in). This category includes those items of information technology that are used for networking and/or telecommunications but do not fit within other designated categories. It includes, but is not limited to, specialpurpose communication cards and adapters. 17 Software Operating System This is the programming, which enables the information technology to operate. The vendor along with the hardware that it operates provides it. Examples are MVS, DOC, UNIX, … Figure A.4 – Equipment61 61 Id. Applications Other This category contains those items of software which are directly necessary for the business operations of the organization. It is usually developed in-house or under contract and does not contain those items of software directly necessary for the operations of systems within it. This includes any programming which is not either identified as a component of a system Operating System or as one of the primary applications. Typical examples are provided by third-party vendors. 18 Equipment Monitors This category covers items which are used to display information from the various units of information technology. It contains, but is not limited to, stand-alone computer monitors and terminals. Figure A.5 – Software62 62 Id. Computers This category includes all information processing equipment maintained by the organization. It contains, but is not limited to, PCs, front-end processors, fileservers, mainframe computers and workstations. Printers This category contains items of information technology used to impress information upon paper. It includes things such as a variety of printers (varying from dot matrix through laserprinters) and plotters. Other This category contains items of equipment not covered by other designated categories. It contains, but obviously is not limited to, such things as memory cards, disk drives, tape units and power supplies. 19 Data/ information System This category includes that information which is maintained for the operation of the information system. It includes, but is not limited to, such things as schedule information, error logs, usage logs, and similar logging data. Figure A.6 – Other63 63 Id. Business This category includes that information maintained for the business purposes of the overall organization. The system business databases, for example, would be included in this category. Other This category includes all information sources not readily identifiable as belonging in one of the other two. 20 Other Facilities Supplies This may be the entire building itself and its supplied services or simply the table the system is on. It depends, of course, on the system being analyzed. This includes supplies for the information system. Included are such things as spare parts, backup components, repair kits, paper, ... It does NOT include supplies for non-IS functions associated with the business. Documentat ion This is the documentation associated with the operation of the information technology. It does NOT include that documentation which may be present for non-IS purposes. Personnel These are the people which work with the information system in all capabilities. It does not include manning at the organization for nonIS duties. As a firstorder estimate the sum of salaries of all operating personnel may be used, as long as you remember that there are non-tangible assets such as experience and loyalty which are not necessarily appropriately priced. Appendix B – Exposure Factors Table B.1 – Exposure Factors64 Threat Data Integrity Loss Accidental Errors Computer Virus Abuse of Access Privileges by Employees Attempted Unauthorized System Access by Outsider Theft or Destruction of Computing Resource 64 Description A realized, or perceived possible, alteration of the data and/or information maintained by or consisting of the specified asset. Improper use of information technology not due to malicious intent but solely through mistaken incorrect use A Program which spreads by attaching itself to "healthy" programs. After infection, the program may perform a variety of non-desirable functions. Employees are authorized by the Security Policy of the organization and further narrowed by their job responsibilities to perform a small selection of functions with the information system. This category covers those acts which may be performed but which are not authorized. Non-employees or personnel not contracted to perform work with or on the information system who are not appropriately authorized yet are attempting, but not succeeding, in gaining access to the information system. A primary resource of the organization is the computing capability of its information systems. This threat addresses the unauthorized use of this resource and the destruction of this resource - through physical or other means. Threats not specific to HIPAA were removed from the list. See James Meritt 4-5. 21 Destruction of Data Abuse of Access Privileges by Other Authorized User Successful Unauthorized System Access by Outsider Information held by an organization is not only that used by their business applications, but includes that used by the systems to operate, manuals, personal experience and other forms. This threat may destroy that information, or simply prevent the organization from using it. While an employee is authorized to perform - and indeed may be required - to perform many actions using the information system, he or she limited to what may be done through organizational policy, job restrictions and technological controls. But an authorized user - whether an employee or contractor - may attempt to perform operations which are denied them. This covers non-employees and non-contractors using, and possibly destroying, information system resources. "Hackers" fit within this threat description. 22 Qualitative Quantitative Asset Value Data Integrity Loss Accidental Errors Computer Virus Abuse of Access Privileges by Employees N et w ca ork tio /te ns le : M co od mm N et em un w o s i ca rk tio /te ns le : R co ou mm N et te u w rs ni ca ork tio /te ns le : C co ab mm N et lin u w g ni ca ork tio /te ns le : O co th mm So er u ftw ni Sy ar st e: em O pe ra So tin g ftw ar e: Ap pl ic at So io ftw ns ar e: O th er Eq ui pm en t: M on Eq ito rs ui p C m om e n pu t: te rs Eq ui pm en t: Pr in te Eq rs ui pm en t: O th er D at a/ Sy inf st orm em at io n: D at a/ Bu In si form ne ss ati on D : at a/ O In f th o er rm at io n: O th er :F ac ilit ie s O th er :S up pl ie s O th er :D oc um en O ta th tio er n :P er so nn el Bu : si As nes se s: ts M on et ar y Appendix C – Annualized Loss Expectancy Sample Spread Sheets Figure C.1 – Asset Values Attempted Unauthorized System Access by Outsider Theft or Destruction of Computing Resource Destruction of Data Abuse of Access Privileges by Other Authorized User Successful Unauthorized System Access by Outsider Litigation Future Loss of Business Loss of licensee Reputation Accidental Information Sent to Wrong Place Table C.2 – Exposure Factors Values65 65 The values provided in the table are from a number of experts in the arena of information system security. See James Meritt 11. Qualitative Quantitative Exposure Impact Coefficient (Value lost a from threat) Data Integrity Loss Accidental Errors Computer Virus Abuse of Access Privileges by Employees Attempted Unauthorized System Access by Outsider Theft or Destruction of Computing Resource Destruction of Data Abuse of Access Privileges by Other Authorized User Successful Unauthorized System Access by Outsider Litigation Future Loss of Business Loss of Licensee Reputation Accidental Information Sent to Wrong Place N et w ca ork tio /te ns le : M co od mm N et em un w o s i ca rk tio /te ns le : R co ou mm N et te u w rs ni ca ork tio /te ns le : C co ab mm N et lin u w g ni ca ork tio /te ns le : O co th mm So er u ftw ni Sy ar st e: em O pe ra So tin g ftw ar e: Ap pl ic at So io ftw ns ar e: O th er Eq ui pm en t: M on Eq ito rs ui p C m om e n pu t: te rs Eq ui pm en t: Pr in te Eq rs ui pm en t: O th er D at a/ Sy inf st orm em at io n: D at a/ Bu In si form ne ss ati on D : at a/ O In f th o er rm at io n: O th er :F ac ilit ie s O th er :S up pl ie s O th er :D oc um en O ta th ti o er n :P er so nn el Bu si As nes se s: ts M on et ar y 23 0.00 0.10 0.30 0.10 0.10 0.10 0.00 0.30 0.00 0.00 0.20 0.00 0.00 0.10 0.80 0.00 0.40 0.30 0.00 0.10 0.20 0.00 0.10 0.00 0.00 0.70 0.50 0.00 0.10 0.05 0.00 0.20 0.30 0.97 0.50 0.95 0.70 0.50 0.30 0.70 0.50 0.60 0.00 0.50 0.00 0.00 0.10 0.00 0.00 0.11 0.00 0.00 0.10 0.00 0.10 0.20 0.50 0.30 0.20 0.20 0.20 0.00 0.40 0.10 0.10 0.30 0.50 0.30 0.10 0.08 0.10 0.30 0.20 0.10 0.50 0.00 1.00 0.30 1.00 0.00 0.20 0.10 0.10 1.00 0.30 1.00 0.10 0.07 0.00 0.00 1.00 0.00 1.00 0.10 1.00 0.00 1.00 0.00 1.00 0.00 1.00 0.00 1.00 0.00 1.00 0.00 1.00 0.00 1.00 0.00 1.00 0.00 0.02 1.00 0.40 1.00 0.30 1.00 0.20 0.00 0.20 0.00 0.20 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.00 0.30 0.30 0.30 0.00 0.30 0.00 0.30 0.10 0.20 0.50 0.20 0.60 0.60 0.20 0.10 0.80 0.15 0.30 0.70 1.00 0.80 0.30 0.20 0.10 0.30 Figure C.3 Annualized Rate of Occurrence ? ? ? ? ? Qualitative Quantitative Annualized Loss Expectancy Data Integrity Loss Accidental Errors Computer Virus Abuse of Access Privileges by Employees Attempted Unauthorized System Access by Outsider Theft or Destruction of Computing Resource Destruction of Data Abuse of Access Privileges by Other Authorized User Successful Unauthorized System Access by Outsider Litigation Future Loss of Business Loss of licensee Reputation Accidental Information Sent to Wrong Place et w ca ork tio /te ns le : M co od mm N et em un w o s i ca rk tio /te ns le : R co ou mm N et te u w rs ni ca ork tio /te ns le : C co ab mm N et lin u w g ni ca ork tio /te ns le : O co th mm So er u ftw ni Sy ar st e: em O pe ra So tin g ftw ar e: Ap pl ic at So io ftw ns ar e: O th er Eq ui pm en t: M on Eq ito rs ui p C m om e n pu t: te rs Eq ui pm en t: Pr in te Eq rs ui pm en t: O th er D at a/ Sy inf st orm em at io n: D at a/ Bu In si form ne ss ati on D : at a/ O In f th o er rm at io n: O th er :F ac ilit ie s O th er :S up pl ie s O th er :D oc um en O ta th tio er n :P er so nn el Bu : si As nes se s: ts M on et ar y Quantitative N et w ca ork tio /te ns le : M co od mm N et em un w o s i ca rk tio /te ns le : R co ou mm N et te u w rs ni ca ork tio /te ns le : C co ab mm N et lin u w g ni ca ork tio /te ns le : O co th mm So er u ftw ni Sy ar st e: em O pe ra So tin g ftw ar e: Ap pl ic at So io ftw ns ar e: O th er Eq ui pm en t: M on Eq ito rs ui p C m om e n pu t: te rs Eq ui pm en t: Pr in te Eq rs ui pm en t: O th er D at a/ Sy inf st orm em at io n: D at a/ Bu In si form ne ss ati on D : at a/ O In f th o er rm at io n: O th er :F ac ilit ie s O th er :S up pl ie s O th er :D oc um en O ta th tio er n :P er so nn el Bu : si As nes se s: ts M on et ar y Annualized Rate of Occurrence Data Integrity Loss Accidental Errors Computer Virus Abuse of Access Privileges by Employees N Qualitative 24 Attempted Unauthorized System Access by Outsider Theft or Destruction of Computing Resource Destruction of Data Abuse of Access Privileges by Other Authorized User Successful Unauthorized System Access by Outsider Litigation Future Loss of Business Loss of licensee Reputation Accidental Information Sent to Wrong Place Figure C.4 – Annual Loss Expectancy