Power Link+ 1.22 1. Introduction. The software program Power Link+
advertisement

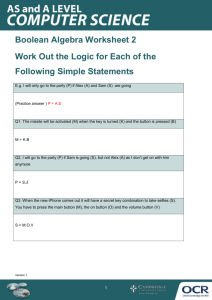
Power Link+ 1.22 1. Introduction. The software program Power Link+ is designed to serve companies acting in the field of monitoring of objects, by centralized monitoring systems. 1.1. Software modules. The driver program commanding the operation of the basic station on the phone line. Driver program receiving signals from a central station type IGP8000, RLS200, CD 1000. MySQL Server SQL server for maintenance operation of the relational database with local and net clients. Power Link+ Monitoring program for ensuring operator's activity. Power Manager Managers program for organizing the work regarding entering and updating information about the protected objects as well as creating reports from the incoming signals in the archive. Test Program stimulating signals from the protected objects in the database. For better understanding we will call the program MySQL SERVER and all other programs – clients. BS Quatro Guard IGP8000 1.2. Database. The data which is stored and operated by the SQL server can be divided into two groups: 1.2.1. Information about signals received from the objects. Date and time of the message; type of the message (OPENING OF THE OBJECT, ALARM IN THE OBJECT, FAILURE IN THE 220V). number of the central station which received the message; the channel used to receive the message (for phone station BS Quatro Guard); communication format (for phone station BS Quatro Guard). 1.2.2. Information about the protected objects. The information about a protected object is divided into: Static information about the object: Number of the object; Name of the object; Type of the object (residence, shop, office …); Address of the object; Phone of the object; Location of the object; Date of the object starting; Owners of the object (name, address, contact phone); Operational information about the object; Type of the transmitter sending messages to the central surveillance system (radio transmitter, phone communicator). Information about the messages expected from the object: Type of the message; Code of the alarming and restoring message; Text message in case of alarm and restoration. Information about the protected zones according to the alarm station: Number of the zone in the alarm station; Name of the protected zone. Graphic of the object. 1.3. Operational sequence The driver programs serving the information flow from the central stations, save the incoming messages from the objects in the relational database operating in the core of MySQL server. One or more Power manager programs update the information about the protected objects or provide reports about previous messages. In real time the monitoring software Power Link+ shows the statistical information about the incoming from the receiving stations messages, makes the reports for the status of the objects and provides the operator with updated information. When a change of the data about a specific object is made by the Power manager, the information in the Power Link + is updated at the same time. It is possible to run all these attachments on separate machines, communicating with the server by means of TCP/IP network protocol, which is a standard in the Internet communications, i.e. the separate client's programs (BS quatro guard, Power Link+, Power Manager) can communicate through the server out of the physical parameters of the office. 1.4. Requirements to the PC. The requirements are basically determined by the Operation system to be installed. In our case this is Windows 95/98/ NT. Processor - Pentium MMX-200, AMD К6-200, Cyrix 6х86 MX-200; Video card - PCI; Monitor - 14" 640х480; RAM - 32 Мb; Sound card; Free disk space - 40Mb; Mouse (PS2 if possible); Note: Better configuration is an advantage for the good function of the memory. 1.5. Diagram for the organization of a monitoring activity. We take as granted that in each company acting in the field of monitoring objects and using centralized monitoring system, there is: an operative officer requiring operative information about the protected objects; technical staff maintaining the efficiency of the central and local equipment, and an operator in demand of the actual information. In such a case the optimal working procedure, regarding the information medium, is as follows; PC 1: Called SERVER. This is the major component of the system. Windows 95/ NT is installed on it, My SQL server with a relational database. This machine must be equipped with UPS, since it will provide the information about the protected objects and the archive signals. The requirements to the hardware are not high except for the 32 MB RAM. PC 2: Called OPERATOR'S COMPUTER. Windows 95/ NT, clients program Power Link+ and clients driver programs (BS Quatro Guard, IGP8000 etc.), receiving information from the basic stations, are installed on it. This computer needs a good video card and monitor, as well as a sound card for better image of the incoming messages. PC 3: Called MANAGER'S COMPUTER. Windows 95/NT and the client Power Manager are installed. Provides service to the operational and technical staff. They take care of the actual static information and the signals expected from the objects. They make reports and organize the operator's work. All the machines are connected to a network and exchange data with the server. 2. Installation. 2.1. Installation of the software. This is an automatically performed and easy process. The following steps should be passed through. Insert the CD in the CD ROM device and from the start button of Windows select Run…. Type D:Setup in the command line, where D is the name of the CD ROM device. This operation will start the installation program. The first dialogue window gives an information about the program to be installed and the copy rights of the product. By clicking on the Next> button you go to the next step. You can cancel the installation by clicking on the Cancel button. The next step is to show the installation directory. It is considered to be the folder C:\Program Files\Power Link+. If you do not accept it, please click on the Browse… button and type the new installation directory. Click on the Next> button if you want to go to the next step. In this window you select what you want to install. Three options are available: Typical installs the whole package on a local working station; Compact installs only the controller module, the SQL server, and the driver programs BS Guard for communication with the central station ; Custom – if you select this field, in the next step you define which modules would be installed, especially Server, Power Link+, BSGuard, Power Manager. You can go to the next step by clicking on the Next> button. Here you define the folder name which will be added to the program menu from the Start button of Windows. The next step is to copy the files on the hard disk and to configure the system ready for operation. The software installation will cause a creation of a folder on the hard disk, which structure will be as follows: Subfolder BDE: Here you can find programs to work with database. Subfolder Images: Here you can find a library with pictures, which can represent the signal types, adequate current state of the object according to the type of the alarming message. Subfolder MySQL: This is the server directory with the relational database. Subfolder Sounds: You can find four types of sound, which can represent the different messages. The installation is made from the folder Sounds of the Windows control panel. The following standard sounds are used from the program software: Asterisk – it is activated by the BS Guard program in case of a phone line failure. Exclamation – it is activated when a signal is received or when a phone line is in use by a driver program BSGuard, IGP8000 etc. Critical Stop is accompanied by showing dialogue window for error. Question – it is activated by the Power Link+ when an alarm signal is received. If an option for an operator's reaction is set, then the sound is periodical in intervals of 2 seconds. Subfolder Graph: The graphs of the monitored objects are saved here (if necessary). The graph itself is a BMP file created with a program for graphics processing (Paint, Coreflow…). The name of this file must be the number of the object with zeros up to four symbols added (e.g. For object No.101, the file with a graphic must be named 0101.BMP). If the server has an installation activated, the installation will create a Start Server file in the folder Windows\Start Menu\Programs\StartUp, which will be started with the Windows startup. It activates the server and defines the required parameters. When the work of the program Start Server is completed, it is necessary to close the window. This is done in the following way: Startup the Microsoft Explorer, then go to folder Windows\Start Menu\Programs\StartUp, click the mouse right button on the Start Server file, select Properties from the pop-up menu in the folder Program of the dialogue window and Close on exit field is set. If Windows NT is installed the installation process takes some more time and it is necessary that a system administrator would do it. 2.2. Installation of TCP/IP protocol for communication with the SQL server. This is a process which is performed only if an operation of the client's software in a network is required (the server is not on the computer where the clients applications are installed) It is recommended this process to be done by a network administrator. 2.2.1. Adding and setup of the communication protocol TCP/IP. 1. Start the Windows Control Panel and the folder Network is activated. Click on the Add… button. 2. Select Protocol from the dialogue window Select Network Component Type and click on the Add… button. 3. Select Microsoft from the window Select Network Protocol in the list Manufacturers and select TCP/IP in the list Network Protocols. Click on the OK button. It takes us back again to the dialogue window from item 1 . 4. In the components list select TCP/IP protocol for the network controller and click on the Properties button. 5. In the group Specify an IP address type mask 255.255.255.0, and in the field IP address – 10.1.1.1 The last figure in the IP address must be specific for each computer, connected to the network. For the computer "Server" it will be "10.1.1.1" for "Baza" – "10.1.1.2", for "Manager" – "10.1.1.3" … After all the steps in the 5 items are passed the computer must be restarted, and after that it should be defined in Widows which IP address to which computer corresponds. 2.2.2. Setup of the OBDC. The ODBC driver program must be setup and configured so that the clients program can find the server with the relational database. It is automatically installed together with the installation of the software. The following steps should be followed: 1. Start the Control Panel of Windows and activate the folder 32bit ODBC Select the MySQL driver and click on the button Setup…. 2. In the MySQL host field (name or IP) the name or the IP address of the computer, on which the server is installed, is entered. 3. IGP 8000. The driver program is designed to receive data on the asynchronous interface adapter from Central station IGP 8000, CD 1000. It supports a one-way protocol – ELECTRONIC LINE. After it is started, an image appears on the task bar. Whenever a signal is received its colour turns red. When the mouse right button is clicked a pop-up menu is opened on the image, which contains two fields: Tools and Exit. The program setup includes a selection of the communication port and the speed of the data transfer. It is possible to restrict the sound when a signal is received. Note: The central station IGP 8000 should be set to a data format: 8 bits information + 1 stop bit. 4. BS Guard. 4.1. Startup and initialization. The startup of the program is made with an initialization of the central station with data from the INI file PowLink.INI or with data by default, if the file does not exist. If a problem appears when the parameters are defined, an error message will be displayed and the whole operation might be repeated. In case that after a number of consecutive attempts the initialization is impossible, then the error is ignored and appears the control panel for the definition of the parameters (see the control panel). The proper connection of the central station to the computer is checked, as well as the number of the communication port, used as a connection, and the initialization of the central station is started again. If it does not help, the following problems are possible: damaged communication port or damaged central station. 4.2. Process of data receiving. After the initialization of the central station has been completed, four squares appear in the Task Bar window. All they represent the current state of each phone line. The following conditions are possible: (green) - the line is free: (yellow) - the line is busy by an incoming call: (red) - the line is out of order, no line can be found; (gray) - the line is not allowed to be used, not connected: The incoming message on the phone line is accompanied by a change in the status of the phone line and a one time sound signal EXCLAMATION (see Sounds in the Control panel). If a phone line which is not restricted for use fails, it changes its status and starts generating a sound signal ASTERISK (See Sounds in the Control panel) every 15 seconds. In case that the link between the program and the central station is disconnected a second initialization must be made. If it does not help an error message in communication is displayed and all the lines are set in restricted condition. 4.3. Control panel of the central station. The control panel is activated from Tools of the pop-up menu, by clicking the mouse right button on any telephone line from the window with tasks in the Task Bar. It contains two folders Tools and Options. After the parameters are set, the control panel is closed. This causes pre-initialization of the central station and saving the data to the PowLink.INI. file. Tools: The parameters for initialization of the central station and communication port are set from this folder. Port The number of the communication port which will command the central station is entered. Format Format of the incoming data from the object (4 or 3 digit number of the object) Durability of HS What should be the Handshake durability (from 0,6 to 3 seconds) Time of transmitting The maximum time a phone line can be kept busy (from 0 to 99 minutes) Priorities of HS The sequence for the Handshake spotting the alarm station. Options: Sounds This field is defined in a way to choose or not a sound when a phone line is in use or fails. The selection of specific sounds is set from the control panel of the operational system – Sounds folder. ASTERISK is used to release and EXCLAMATION to engage a telephone line. Used lines Here are defined the used and operational lines. If any line fails its state is defined as restricted for use. 4.3. Log file. Use the View button to display the contents of the BSGuard.log file which is in the program directory. In this file are saved problems and warnings occurred during the program performance: Phone line failure; Phone line in use; Reading the parameters from the central station; Setting-up the sentral station parameters The central station does not respond to requirements from the program; Initialization of the communication port impossible. Delete the LOG file. Exit the program; The file can be deleted by the Delete button. 4.5. Messages for errors while working with the program Error: Error: Error: ComPort :N initialization impossible – when the number of the communication port is improperly entered. It is necessary to check for conflicts with mouse, modem or some other device. The central station does not respond – it occurs when the central station is in a process of initialization. Make another attempt and if still impossible, check the connection and the efficiency of the station. It is possible that a problem exists in the efficiency of the communication port. No communication with the central station – it may occur while the program is in operation and the central station does not respond to the enquiries for status of the telephone lines. It checks the correct connection and efficiency of the station and then the station is initialized again. It is possible that a problem may exist in the efficiency of the communication port. 5. Power Link +. All the objects which are connected to the monitoring system must be entered and configured. This does not mean that a signal from not configured object will not be received, operated and stored. The message from such an object will be displayed as unknown. The data which is received contains the number of the object and the status of the signal. The program searches the database with information about all objects. Provided that a message with a status for an object is defined, the same is displayed in the statistical information window (archive window). If Operator's reaction in the dialogue window Operations is activated, and the message is alarming, a sound signal is switched on until the operator reacts, by clicking on the Ins button or on the Tools - Reacting menu. Each incoming message causes a change in the object status and updates the information in the windows for current state. 5.1. Tools. From the Tools – Options... menu it is possible to configure the desktop of the windows displayed on the program interface. When the menu is selected, the dialogue window which contains the following fields is activated: 5.1.1. General group. Operator's reaction – activates or inactivates the alarm messages panel. When it is activated, the operator reacts to each alarming message; Info about alarming in an active state and when an alarm signal is received, informatio about the protected object is automatically opened. Save desktop when exiting the program if this field is active when you exit the program, the position and the windows setup on the desktop of the program will be saved to the disk; Number of signals in the archive – the maximum number of signals viewed in the archive window. 5.1.2. Archive window. Font – select the font which will be used to type messages in the archive window; Size – the character size in the archive window; Info message – the line colour and background when receiving an info message; Unreaction message – the colour and the background of the alarming message, which will be reacted to by the operator; Reaction message – the colour and the background of the alarming message which was reacted to. Note: The colour of the windows is the colour of the background of the info message and the text colour in the alarming messages panel is the colour of the background for unreaction message. 5.1.3. Other windows ( State and Object list ). Font – select the font which will be used for windows State and Object list; Size – the size of the characters in the windows State and Object list; Filtered text – the field colour and background of the windows State and Object list by which the content is sorted; Unfiltered text - the text colour and background of the windows State and Object list by which the content is sorted; Gridlines in the tables – removes or displays the vertical and horizontal gridlines and the field titles in the windows lists. Note: The windows colour is the background colour of the unfiltered text. 5.2. Windows. 5.2.1. Archive window. This window is constantly activated and can not be removed but only minimized. It shows messages from the objects by the order they are received in the central stations. It is possible to setup which restoring messages to be displayed, and the alarming ones must be viewed. The information is divided into fields: Type of the signal (graphic image representing the signal type, as an opening, siren switching on, sabotage in the system, etc. The image is visible only for alarming messages.) Number of the object, Time of arrival, Name of the object and Message. If a signal is received from an object for which no information is available in the database, the same is displayed as unknown message. Upon active operator's reaction in Tools – Options and when an alarming message is received, the whole row is displayed as an unreaction message, which is normalized (attributes for reacted signal) when the operator reacts (Reacting button, button Ins or Tools – Reaction). Doubleclick of the mouse left button on a message opens a window (refreshes it if it is active) with information about the particular object. By using Signals from the Archive menu or from the pop-up menu of the Archive window you choose the restoring signals, which to be displayed in the Arcive window. The list of these restoring signals is desplayed on the right panel. 5.2.2. Window States. It is activated from the Windows – States menu. There may exist several such windows. They are setup to show in real time the current state of objects satisfying certain criteria. By using Signals it is possible to select signals for filtering, and title for the relevant window. In the window there will be included those objects that have active current state and satisfy the selected criteria. The information in the table can be sorted by the objects number, the signal type, the time the message occurred, or by object name. Example: In the window shown, it is indicated to display all the objects where a technical problem exists, and the information is sorted by time. At this setup of the window we have a variation of the statistical (archive) window only for objects having technical problems. Doubleclick of the mouse left button on a message, opens (refreshes if it is active) a window with information on the particular object. 5.2.3. Window Objects list. It is activated from the menu Windows – Object list and represents table-information about the protected objects. By using this window it is possible to search objects by numbers and names. When you enter the filtration criteria and click on the Find button, the required report is made. When clicking on the All button, the report is cancelled and all the objects are viewed. Doubleclick of the mouse left button on a row, opens (refreshes, if it is active) a window with information about the particular object. 5.2.4. Window Timer. Shows or hides the program timer. The size of the figures depends on the width of the window. 5.2.5. Information about an object. This information may be viewed (by doubleclicking the mouse left button or Enter) from any window relevant to a protected object. The current state of the object is graphically viewed on the lowest panel. The information window contains four folders: Folder Information Contains the static information about the protected object. Folder Messages: All possible signals from an object, sorted by type are viewed here. If any state is active, it is marked with attributes for filtered text and an alarm message is put in the message field. The field time shows the date and the time of the last message of the same type. The table contains the fields: signal type, zone or user attached to the message, time and message adequate to the current state. Note: the field zone/ user is usable only if it is received from the objects via Protocol Contact ID. Folder Archive: All the messages received in the last 24 hours from the object are viewed in this folder. Alarming messages have attributes for filtered text. The first row displays the last message and the last the first message. Folder Graph: Graphic of the object will be only viewed if BMP file exists in folder GRAPH with the same name as the number of the object but added with zeros up to four digits. If these conditions are not fulfilled, you will see a message, saying that no graphic is available for the object. 6. Power Manager. The program is a client's application. It offers tools for updating information about the objects and making reports from the database archive. Each change made by the Power Manager updates in real time the information in the operator's module Power Link+. Eleven different types of signals are normally defined in the database. These are 11 types of messages which are possible to be registered in a protected object. It is possible that the number of the types can be increased or corrected. The software supports processing of incoming messages from the central station BS Quadro Guard with communication protocol Contact ID. The whole table with possible messages is entered, which, according to the type of the alarm systems installed in the objects, might be submitted to a development. Each message by Contact ID is attached to a defined type of signal. Types of the protected objects can be entered for better convenience. Typification can be made by the object category, by region, by the method of communication with the central station, etc. The program is divided into three folders: Tools, Repords and About the program. 6.1. Tools. Objects types. When clicking on the button Object types, a dialogue window is opened for setup of the object types. Here, in the example, the objects are classified by category (apartment, warehouse, shop...) They are edited directly in the table. Buttons: Insert Edit Delete Close Insert new type; Edit the type name; Delete type. Delete is not possible if the type is in use by an object; Close the window. 6.2. Tools. Signals. The dialogue window is activated in the Tools folder with the button Signals. It is used for definition of the standard signal types, which will be used in the messages from the objects. With their help, typification of the information coming from the alarm system is achieved. This information can be corrected later on. Buttons: Insert Edit Delete From File type; Close Insert new signal; Edit mode of the selected signal is switched on; Delete signal. If this signal is in use it is not possible to be deleted; BMP image is selected from the dialogue window which will represent the signal Close the window. Fields: Code The code is entered in 16 digit type for alarming and restoring message by default. This code is expected from the alarm panel. If Signals from KEL is active then the message from transmitter KEL780 is selected from the popup menu. Message The alarming and restoring message by default. Testing Upon activating it shows that the alarming signal will be generated by the computer when certain time (in minutes) elapses. Restore all It is activated, if necessary, to restore automatically all the signals of the type for the specific object when a restoring signal of this type is received. It is used at signal Arm/Disarm. Restore after If for a certain signal in the computer only alarming message is received, it may appear that this state of the object is restored after some time. Example: In many stations panic from the keyboard is accompanied only by sending an alarming message. In order to eliminate manual delete of the current state of the object after receiving such a message, you state that the panic will be restored automatically in 1 hour (enough time for the operator and the patrol to react to the signal). Signal type If it is necessary to define an alarm message of a signal as a warning or info message, this has to be stated in the popup list. Example: When an object opens, it is not necessary for the operator to react and the alarm cycle to be activated in the operator's program, but it is enough only to warn the operator with a single sound signal and the message will be shown with attributes for the reaction message. 6.3. Tools. Contact ID. The table with the messages on protocol Contact ID is viewed in this window. If it is necessary to edit the name of the alarming and restoring message this is made in the text fields in the lower part. If an edit of the signal type is needed this can be done by selection of the type and the button Each edit causes correction of this signal in all the objects using it. . 6.4. Tools. Objects. Using the Objects button in the folder Tools a dialogue window is opened for entering static information about the objects separated in folders by themes. By using Insert and Delete buttons an object is inserted or deleted. Duplication of the objects numbers is admitted. This is an advantage, because it allows to receive information from several objects combined by one transmitter. By using the buttons the group Positioning on the table is viewed or hidden. It is possible and to choose the first or the last object, as well as search by a specific number (type the field number in the Search object and click on the Enter button"). Insert or edit (by using the button doubleclick the mouse left button on the object or Enter) of the object opens a dialogue window Objects which contains three folders: 6.4.1. Folder Information. Static information about the object is entered there. If the desired type is not yet defined this can be done by the button . The information about the owners is typed in the relevant table. Their number is unlimited. According to the way the signals are received from the objects (radio transmitter using transmitter type KEL780 or telephone communicator) the transmitter type field is set. This field is relevant to the expected messages for the object and to the period of tests when a new test signal is inserted. 6.4.2. Folder Messages: In this folder are defined the messages, which are expected from the protected object, by using the preliminary set signal types. Note: If messages on protocol Contact ID are received from the object, it is not necessary to define messages to receive, the software will automatically attach the incoming messages to this object. Buttons: Insert new message of the selected signal type; Delete the selected message; Opens a dialogue window Signals for predefinition and corrections. Fields: Code The code is entered in 16 digit type for alarming and restoring message. If in the transmitter type is stated radio transmitter then message from transmitter is entered in this field. Messages Type the text that we want to be viewed when the message is received: Active now Activates or inactivates the current state of the object for this type of signal. Test time It is activated in case of text message. The period for sending a text signal from the central station is selected from a list. If the transmitter is a telephone communicator the time varies from 1 to 31 days, and for a radio transmitter from 5 minutes to 24 hours. 6.4.3. Folder Zones: Here is viewed the actual location of each zone in the alarm station of the object. This folder is relevant only in case when data will be received by the protocol Contact ID. 6.5. Reports. Archive. By clicking on the Archive button in the Reports folder a dialogue window is activated where it is possible to view the archive of messages by preliminary set criteria. The same can be printed. The last report is saved as a text file in the program folder (Power Link+). When having problems with the printer, this file can be opened in a word processing program or to be analysed in an excell type program. Fields: For a period of time – A report can be made for a certain month. You can choose for a whole month or a period in the month. In the second case you must define and the initial and the final date and the time interval is entered. If From is not entered the report begins with the first signal received in the archive, it is analogical with the time To. List of all the objects - there are two tables in this field. The above is a list of all objects, sorted by number, and the below is a list of the selected objects. These are the objects we want to be included in the report. In order to add or remove information from the table below the buttons and are used. The button removes all the objects that are selected beforehand. Transmitter – This is a list with numbers of transmitters, from which message has been received (this information is taken from the archive of the message) and thus by using the buttons and an information about a particular transmitter is viewed but not about an object. The difference between this and the above field is that it is possible to have several objects with one and the same transmitter i.e. with one and the same number. Note: It is not admitted to use simultaneously the fields objects and transmitters. Signals – By using this field it is defined which type of signals should be viewed in the report. This is done by using the buttons and Note: If a certain field remains empty it is not taken into consideration and is accepted that all its elements are chosen.. Buttons: Switches between two windows a large and a small one. When clicking on the button View on the small one are viewed all the messages for the period which are not entered. View a report according to the criteria and the conditions which we have entered in the window fields; Close window. 6.6. Report. For object types. This window is used to analyse the distribution of the objects by types. By doubleclick of the mouse left button on any object it is possible to correct its information. A verification is made for the objects of unknown type. 7. Test. This is a program for simulating messages from objects. It contains two folders: Folder "telephone link" here you must enter the number of the object and the 16 digit code of the message and then click on the "Signal" button; Folder "radio link" dial the number of the object, define the signal from the transmitter and click on the "Signal" button.