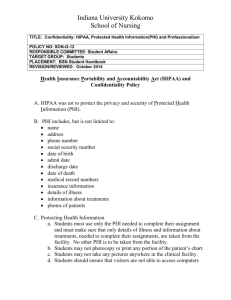
now - Medical Group Management Association
advertisement

May 21, 2009 Charles E. Johnson Acting Secretary The Office for Civil Rights U.S. Department of Health and Human Services Hubert H. Humphrey Building, Room 509F 200 Independence Avenue, SW Washington, DC 20201 Attention: HITECH Breach Notification RE: 45 CFR Parts 160 and 164; Guidance specifying technologies and methodologies that render protected health information unusable, unreadable, or indecipherable to unauthorized individuals for the purposes of the breach notification requirements specified in ARRA Dear Mr. Johnson: The Medical Group Management Association (MGMA) appreciates the opportunity to submit comments on the Department of Health and Human Service’s (HHS) guidance specifying the technologies and methodologies that render protected health information (PHI) unusable, unreadable, or indecipherable to unauthorized individuals to prevent triggering the breach notification requirements specified in the recently enacted “American Recovery and Reinvestment Act of 2009” (ARRA) (Pub. L. 111-5). ARRA defines a breach as the unauthorized acquisition, access, use, or disclosure of PHI which compromises the security or privacy of such information. HHS is required to issue guidance, with annual updates, on the technological solutions for protecting PHI from security breaches. Although HIPAA covered entities are not required to follow HHS’ guidance, HHS’ recommended technologies and methodologies would “create the functional equivalent of a safe harbor” so that HIPAA covered entities and their business associates that implement these measures will not have to issue breach notifications in the event of a breach, as required by ARRA. We offer the following comments: 1. Support of Encryption and Destruction to render PHI Unusable - We support the two identified methods included in the HHS guidance for rendering PHI unusable, unreadable, or indecipherable to unauthorized individuals, (a) encryption, and (b) destruction. It is clear that should PHI be properly encrypted or destroyed prior to disposal, then no breach notification should be required. Similarly, no breach notification should be required if the media on which PHI are stored has been destroyed in such a manner that that the data cannot be retrieved or pieced back together. 2. Limited Data Set to Render PHI “Unusable” - We recommend adding the creation of a limited data set to the list of methods physician practices can employ to render PHI unusable to unauthorized individuals. A “limited data set” is information from which “facial” identifiers have been removed. Specifically, as it relates to the individual or his or her relatives, employers or household members, all the following identifiers must be removed in order for health information to be a “limited data set”: Names; Street addresses (other than town, city, state and zip code); Telephone numbers; Fax numbers; E-mail addresses; Social Security numbers; Medical records numbers; Health plan beneficiary numbers; Account numbers; Certificate license numbers; Vehicle identifiers and serial numbers, including license plates; Device identifiers and serial numbers; URLs; IP address numbers; Biometric identifiers (including finger and voice prints); and Full face photos (or comparable images). As HIPAA expressly set out that limited data sets are exempted from the accounting requirement (45 CFR 164.528(a) (1) (viii)), we contend that the breach notification requirement should not apply to PHI that has been converted to a limited data set. 3. De-identification of PHI – PHI that has been de-identified falls outside the purview of the HIPAA Privacy regulation. However, we encourage the inclusion of the deidentification process as another option for physician practices to employ to render PHI unusable to unauthorized individuals. In addition, no breach notification should be required if the media on which PHI are stored has been de-identified. This additional option, and the impact on breach notification, should be clearly communicated to covered entities impacted by this Guidance. 4. No Breach Notice Required if PHI not Accessed – Should evidence clearly indicate that PHI has not been, or could not reasonably have been, acquired by an unauthorized individual, no breach notification should be required. As an example, should a laptop containing PHI be stolen, and later recovered with evidence that the PHI was never accessed, no breach notification should be required. 5. Identification of Practical Methods to Protect PHI - In developing final guidance on this issue and in developing other guidance documents in support of the privacy and security provisions included in ARRA, HHS should consider practical, inexpensive technological measures and methods that protect PHI. This would ensure that the broadest number of physician practices possible would adhere to the guidance recommendations. HHS should widely disseminate these practical methods of protecting PHI by using, for example, the HHS Website, provider-focused conference calls, and face-to-face meetings. Thank you for the opportunity to comment on this important issue. Should you have any questions regarding our comments please contact Robert Tennant at rtennant@mgma.com or 202293-3450. Sincerely, William F. Jessee, MD, FACMPE President and CEO