C O M P U T E R C R I M E oo.N.. PARKER and SUSAN H. NYCUM
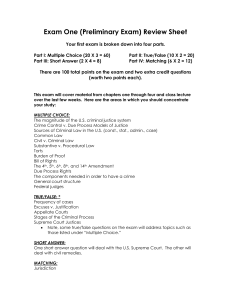
advertisement

Reports and Articles search Staff of The Rand Corporation. In 1967 he brought the issue of computer security to the attention of the technical field by organizing a special session on the subject at the Spring Joint Computer Conference. Subsequently he chaired a Defense Science Board committee, which took the first comprehensive look anywhere in Government at computer security. The report entitled "Security Controls for Computer Systems" was a definitive treatment of the subject, and to this day remains an excellent primer. In the early 1970s, Ware was asked to join a special advisory group to the Secretary of HEW, and subsequently became its chairman. Its report, "Records, Computers and the Rights of Citi- COMPUTER CRIME oo.N.. PARKERandSUSANH. NYCUM As we enter the information age, business and whitecollar crime is changing significantly. Valuable assets are increasingly represented by information, an intangible property, and its processing, transmission, and storage are rapidly becoming the targets of crime. Such crime includes fraud, theft, embezzlement, larceny, sabotage, espionage, extortion, and conspiracy. Because of increasing automation throughout society, the following changes are occurring: New and greater demand for trustworthy employees. Data processing employees are entrusted with their employer's information assets in an environment where there is little likelihood of any wrongdoing being discovered. New environment for business and white-collar crime. The mechanisms by which automated information crimes are enacted within computers are sometimes invisible to the corporate or organizational victims. Moreover, the evidence of loss can sometimes be electronically erased, in the normal course of events, before it can be captured as evidence. New forms of assets subject to criminal attacks. Financial as well as inventory, marketing, and other data stored in computers and on computer media such as magnetic tapes make computers the new business vaults. New criminal methods. The most widely used technical methods are impersonating another computer user and data diddling (false data entry). These techniques are far safer for perpetrators than the less frequently reported and more exotic and complex methods of programmed fraud such as Trojan horse attacks (inserting secret instructions in legitimate computer programs), superzapping (unauthorized use of utility programs), or wiretapping. New time scale. Although business crime has traditionally been measured in minutes, hours, days, and weeks, © I984 ACM 0001-0782/84/0400-0313 75¢ April 1984 Volume27 Number 4 zens," was the first comprehensive treatment of privacy at the federal level. It provided the intellectual foundation for the Federal Privacy Act of 1974, which among other things created the Privacy Protection Study Commission of which Ware was a member and vice-chairman. The following testimonies have been edited for publication. The views presented in the following two articles are solely the personal views of the authors. They in no way reflect positions of The Rand Corporation, SRI International, Gaston, Snow and Ely Bartlett, ACM, or any of their clients. Peter J. Denning we now measure some automated crimes in the scale of a few thousandths and millionths of a second. New, wider geographical area. The geography of business crime has broadened. A fraud in a computer connected to the dial-up telephone system in Washington, D.C., could be committed from a terminal in a telephone booth in Japan or anyplace else in the world. The Nature of Computer Crime For purposes of criminal justice, computer crime is defined as any illegal act where a special knowledge of computer technology is essential for its perpetration, investigation, or prosecution. Computer crime is not considered a single type of crime that is different from other crimes. Rather, nearly all kinds of crimes can be committed through computers or be computer mediated. In fact, we have documentation of almost every known type of crime involving computers (except, of course, for a few violent crimes such as rape and aggrevated assault). People can use computers in essentially four ways to commit criminal acts: A computer can be the object of attack. Over the past few years, international terrorists have used bombs and submachine guns to attack at least 28 computer centers belonging to multinational companies and government agencies in Italy and France. A computer can be the subject of a crime by providing the automated mechanisms to modify and manipulate new forms of assets such as computer programs and information representing money. The computer can be used as a tool for conducting or planning a crime. A stockbroker used a computer to prod.uce forged investment statements showing huge profits to deceive his clients and steal $53 million. The symbol of the computer itself can be used to intimidate or deceive. The same stockbroker told his clients that he was able to make such huge profits on rapid stock Communications of the ACM 313 Reports and Articles option trading by using a secret computer program in a giant computer in a Wall Street brokerage firm. Although he had no such program nor access to the computer in question, hundreds of clients were convinced enough to invest a minimum of $100,000 each. Computer criminals have tended to be young, highly motivated, trusted employees without prior criminal records. Specific computer crime statutes are likely to have greater deterrent value for these individuals (who see themselves as problem solvers, not as crooks) than for career criminals. The first class of offenders is convinced that they do not hurt people or even organizations, just computers. However, more career criminals are engaging in computer crime as they find their typical environments being saturated with computers. As computer technology advances, a new kind of computer criminal, the malicious system hacker, has emerged as an outgrowth of the "phone phreaks" of the 1960s. A serious epidemic of system hacking and computer program piracy is evident across the country as high school and college students learn computer methods and gain access to telephone terminals and personal microcomputers. Sometimes, students are even encouraged by their instructors to engage in technological trespassing, electronic vandalism, and violation of proprietary rights through copying. One computer program manufacturer estimates that two out of three of the copies of their products in use have not been paid for, although their profits are still so large they do not worry about it very much. We believe that specific criminal statutes will act as an important deterrent and help solve these problems. No valid statistics exist on the extent of computer crime or the losses incurred. The numbers quoted in the news media are not representative because acceptable mechanisms for collecting comprehensive or valid statistical samples have not been established. A lack of concurrence for a definition of computer crime precludes comprehensive statistical evaluation. According to our definition, SRI has the largest collection of documentation of reported cases; yet SRI's tabulations of more than 1,000 cases of computer abuse that have occurred since 1958 worldwide represent only a fraction of all suspected cases. In total, more money is probably lost from errors and omissions in the use of computers than is lost by intentional acts. Nevertheless, we can and have controlled errors, and their cost is budgeted into the process. We do not predict or budget for fraud; its perpetration always comes as an unpleasant surprise. Moreover, the size of an individual, large-loss crime for an institutional victim will in many cases surpass the total accidental loss experienced by that organization. Computer crime has been identified as relatively easy to commit. This is a great oversimplification. Some computer crimes have been relatively simple and safe to perpetrate, but only by those few people with sufficient skills, knowledge, resources, and access. They would have been very difficult for anyone else. Although certain minor computer crimes have been corn- 314 Communications of the ACM mitted by clerical employees with limited technical capabilities and minimal difficulty of access, other crimes have been very complex. Automated crime is relatively insensitive to the size of the loss. Once a criminal act has been planned, taking $100,000 or increasing it to $1,0o0,o00 is sometimes only a matter of adding three zeros. All prosecutors I have questioned indicate that they have been (or would be) able to prosecute all known computer crimes using existing criminal statutes. However, many of them also indicate difficulty in applying those statutes for purposes never anticipated when the statutes were created, and few prosecutors understand the possibilities for new crimes not covered by existing statutes. The conviction rate of those indicted is very high based on limited known experience. Without specific computer crime statutes, it is easier for victims not to report their loss to avoid embarrassment or unwanted attention and for prosecutors to avoid prosecuting the crime from a lack of knowledge about computers. The Future of Computer Crime On the basis of case-by-case studies working with victims and investigators, interviews with more than 30 perpetrators, and computer security reviews for clients, we make the following projections: • The incidence of computer crime will increase because of the increasing number of computers and the automation of business activities. • The use of computers for criminal purposes in bookmaking, drug distribution and sales, scams, and prostitution will grow beyond the few known cases. Electronic funds transfer systems offer attractive opportunities for fraud and rapid laundering of money as $400 billion per day domestically and $600 billion per day internationally are exchanged among interconnected bank computers and automated teller machines. Increasing use of data communications, voice data entry and computer output, optical data storage, video systems, and robots will also attract new forms of criminal activity. This requires that criminal statutes be comprehensive and technology independent to avoid further rapid obsolescence of the law. • The size of losses in significant cases will increase dramatically because of the concentration of information assets in fragile forms subject to manipulation via computers. Consider the $200 million Equity Funding Insurance fraud, the $21 million bank embezzlement in Los Angeles, the $10 million funds transfer fraud also in Los Angeles, the $53 million securities fraud in Florida, the $50 million commodity futures fraud in Denver, and the $67 million inventory fraud in New York--all record-breaking cases of their types. On the basis of the different definitions of computer crime currently in use, some analysts have disputed whether these cases are in fact computer crimes. Moreover, each of the 22 states with a computer crime statute has a different legal definition, and no federal legislation has yet been April 1984 Volume 27 Number 4 Reports and Articles promulgated to settle the issue. Clearly, however, the use of computers in these cases contributed to creating the special environments, tools, and access to large amounts of financial assets in an environment with limited prevention and detection controls. • The potential for increased protection of automated business activities is far greater than was ever possible in manually performed activities. This potential is now beginning to be realized in modern computers. Computer manufacturers and service companies are providing more safeguards today to meet the new and growing user demands for security. Although significant cases of business and white-collar crime will probably decrease, the losses per case will probably increase significantly. We refer to this anticipated condition as the escalation of business crime. • Even though a recent study by an American Federation of Information Processing Societies Task Group concluded that the resiliency of society and its limited dependence on computers preclude major problems today, we believe that escalating computer use could soon change this. However, by using technical safeguards like cryptography, advanced management controls, and codes of conduct stimulated in part by strong criminal statutes, we can continue to limit the risks inherent in the use of computer technology to an acceptable level. Recommendations In conclusion, we recommend careful legislative action to advance federal criminal laws that will deter and help prosecute crime in the information age. Such legislation should focus on the protection of information as a valuable asset that is subject to criminal misuse by people with new technical capabilities, and not just focus on rapidly changing computer technology. However, before enactment, all of the implications and effects of information age crime and proposed legislation should be identified and thoroughly reviewed in public by a national commission of inquiry to assure adequate attention from and support of the stakeholders. We believe that such a commission should focus squarely on computer crime; if privacy also requires further study, that should be done by a separate commission. Authors' Present Addresses: Donn B. Parker, SRI International, 333 Ravenswood Avenue, Menlo Park, CA 94025. Susan H. Nycum, Gaston, Snow and Ely Bartlett, 2 Palo Alto Square, Suite 550, Palo Alto, CA 94306. Permission to copy without fee all or part of this material is granted provided that the copiesare not made or distributed for direct commercial advantage, the ACM copyrightnotice and the title of the publication and its date appear, and notice is given that copyingis by permissionof the Associationfor ComputingMachinery.To copy otherwise, or to republish, requires a fee and/or specificpermission. INFORMATION SYSTEMS SECURITY A N D P RIVACY W,LL,S.. WARE The subject of computer security is of great importance, not only to me professionally but also to the country. The following presentation is mostly a hopscotch over a variety of points and ideas that I think will be of significance for the hearing. Let me first clarify the relationship between security and privacy. I use the term privacy in the context of record-keeping privacy to refer to the use of information about people to make decisions and judgments about them. Record-keeping privacy means protecting the personal information kept in computer-based systems and controlling its use for authorized purposes only. In contrast, computer security is that body of technology, techniques, procedures, and practices that provides the protective mechanisms to assure the safety of both the systems themselves and the information within them, and limits access to such information solely to authorized users. Computer security is of importance whether the information to be protected is personal in nature and therefore related to privacy concerns, whether it is defense in nature and therefore related to the security of the country, or w h e t h e r it is sensitive in nature from a business point of view and April 1984 Volume 27 Number 4 therefore relevant to corporate well-being. The important point is that a comprehensive set of security safeguards within and around a computer-based information system is an essential prerequisite for assuring personal privacy. To operate without such relevant safeguards is a sham against privacy assurance. The computer security issue must be seen as analogous to the classic offense and defense situation. As computer security safeguards become stronger, the offenses against them will become more sophisticated and the cycle will repeat itself. The computer security issue is not one that can be looked at and forgotten. Security first surfaced as a concern on the professional . scene only fifteen years ago, and we still have much to learn about how to incorporate comprehensive protection mechanisms in our computer systems. It is an evolving issue, not a static end-of-the-road one. I would, therefore, recommend to you that Computer security be a standing agenda item for this or other committees of the Congress to look at every year or so for at least the next five and possibly the next ten years. Next, let me contrast the security situation in the Communications of the ACM 315 Reports and Articles defense environment with that in the commercial and industrial worlds. In defense, the threat against computer-based systems involves the full technical resources of advanced major world powers whose offensive moves can be mounted with substantial funding and other resources. In the defense context, therefore, the threat includes not only the possibility of highly sophisticated technical incursions but also the "people problem," which in this case might include motivating people with money to commit subversive acts. On the other hand, the defense community does go through an investigative process to grant formal clearances to its personnel and therefore has some assurance of their trustworthiness. THE PRIVATE SECTOR In the commercial sector, on the other hand, the technical threat is at present relatively minimal, the big threat being people working within the systems themselves. An examination of Donn Parker's SRI database of computer-related criminal actions reveals that the great bulk of these crimes has been committed by individuals who were authorized to interact with the system and who knew enough about it to exploit its possibilities for personal gain. Furthermore, there is generally little attention paid in the commercial world to establishing the trustworthiness of individuals in critical and sensitive positions within a computer-based information system. Some corporations do essentially nothing by way of assessing the integrity of critical individuals; others take the minimal step of requiring that individuals be bondable--a really minimum level of assurance. Very few, perhaps none, engage in a comprehensive background investigation. When the private sector gets the "people problem" dimension of the threat under control and has deterred the simple technical intrusions, then sophisticated technical threats will become more important. What can we do about the simple technical threats such as those committed in the Milwaukee-414 caper or those documented on the SRI database? The point is that technology is not really the issue. There are ample technological safeguards that can be installed that would be effective against many of the crimes and many of the mischievous pranks that have occurred. There are also procedural and administrative safeguards that can be important deterrents. In the private sector, we need only the corporate will to address the problem and the corporate commitment to put the issue on the same level of concern as that of protecting other valuable resources. By implication, that also means the corporate commitment to spend the modest sums needed. To ensure that this happens, private sector users of computers must signal the computer industry that technical safeguards are wanted, are essential, and will be paid for. Do not underestimate the last point. Until the IBMs, the DECs, the Burroughs, the UNIVACs and other computer manufacturers understand that their respective customer bases demand technical security safeguard 316 Communications of the ACM features, the product lines will not have them. I would suggest that the government has major leverage on this issue; it can make mandatory the inclusion of appropriate technical security features in the systems it procures. The "people aspect" of the problem is a more difficult one because one cannot legislate trustworthiness or morality, and even the most extensive background investigation may not reveal deeply hidden or latent subversive tendencies. Nonetheless, to start with, we must do all that is possible in terms of technical and procedural safeguards, a good array of which will fend off many people problems. We might take legal steps to motivate system designers to include security safeguards in their products. One way of encouraging private sector response might be to create the legal basis for acting against a particular record-keeping installation in the case of a security breach (e.g., a suit for negligent behavior should state-of-the-art security safeguards not be in place). For the most part we are not talking about large dollar investments. Clearly, if an organization operates its computer center behind a window and encourages casual visitors to wander among the equipment, there might be a significant initial investment to physically secure the facility and provide it with appropriate physical and fire protection. Beyond this phase, though, many organizations find that important security safeguards can be installed as part of changes that are made for other reasons and that the costs of such security changes are frequently unnoticeable. The cost will not be zero but neither will it be burdensome. The "People Threat" There are several attractive options for technical safeguards against the "people threat." For example, an individual logging onto a computer system is normally requested to supply personal identification and a password, which in effect is an authentication of identity. Someone attempting to penetrate a computer system often tries to masquerade as a legitimate user. Since too many of today's systems permit an indefinite number of log-on trials, it is sometimes feasible for the perpetrator to program a small computer to systematically try words, combinations of letters and characters, or other possible passwords until one is found that works. The movie WarGames showed the details of such a penetration very realistically and accurately. Clearly, this is an undesirable and unsafe arrangement. There is no reason why a computer should not disconnect an individual after some number of attempts, such as three or five, and keep him disconnected until his authenticity has been certified or for some fairly long period of time. The approach used at the Los Alamos National Laboratory is a good example of what can be done. At Los Alamos, if an individual--even a respected, established senior reseacher of national repute--fails to log on after a number of tries, such as three or five, his account is completely disabled until he personally appears at the security office and explains why he was unable to type April 1984 Volume 27 Number 4 Reports and Articles his password successfully after the prescribed number of tries. If he fails to log on successfully in a second series of attempts, his supervisor is required to explain in writing why the individual in question seems unable to type correctly. Although this process might seem stringent and is undoubtedly annoying, the disabling of repeated failed log-on attempts is an appropriate technique for fending off penetration attempts based on guessing. Technical safeguards can go a long way toward reducing the "people threat." A second example of people-proof safeguards is protection against unwarranted copying of records. Every computer system contains a mechanism for accomplishing the "initial software load." This mechanism is activated by a button, a switch, or a sequence of actions by the console operator. Imagine a scenario in which an operator on the graveyard shift finds the machine inactive and decides to do something in his own behalf such as illegally copying a file of sensitive information. Having done so, the operator simply reloads the machine as though it had stopped for some reason. He disables the operating system and uses a standalone utility program to accomplish his purpose. For many machines there will be no record of what he has surreptitiously done. Although there are obvious technical offsets to such malfeasance by operators, they do not often exist in marketed machines. The procedure of two-person control as used by the military would also be a deterrent against individual misbehavior in many cases. A third, almost whimsical example of an imaginative and appropriate deterrent is provided by the Security Pacific National Bank. According to the media, Security Pacific diverted a presumed penetrator by offering him a game to play while tracing the origin of his call. What we need is a menu of technical features that machines should have in order to help offset aspects of the people-threat problem. Let me offer a recommendation: dural, personnel, and administrative implications. Each aspect has to be attended to, particularly the last three. A computer system with the best possible technical safeguards can be readily penetrated if it is operated in an environment with sloppy and careless procedural and administrative arrangements by people with questionable motives or allegiance. Where will the government develop the guidance that it needs on these many dimensions? Many solutions are already in hand because they are understood for other reasons. For example, the Department of Defense certainly knows how to deal with physical and personnel security, and its experience is available to other agencies of government as might be needed. The TEMPEST emanation issue is understood and safeguards against it exist. There are many private organizations today that can advise on fire protection, physical protection, personnel control, and the like. But, in government, where will the technical software/ hardware expertise and the administrative and management guidance come from? With regard to computer matters, the government's principal assets are the Computer Security Center (CSC) of the National Security Agency, the Institute of Computer Science and Technology (ICST) of the National Bureau of Standards, and the General Services Administration (GSA). Their expertise on questions of security should be harnessed to provide some level of leadership in these matters. Computer Security Center. Task the Institute of Computer Science and Technology of the National Bureau of Standards to produce such a list of options, and consider making it mandatory in government acquisitions of computer systems. The focus of concern at CSC is "trusted systems" and especially "trusted software," meaning that the system or software can with high confidence be relied on to do what it is supposed to do and not do what it is not supposed to do. Keep in mind that CSC is a Department of Defense entity whose focus of concern is defense systems and particularly sophisticated technical incursions, and therefore it has some expertise to share on the software/hardware question. I believe that because the problem of incorporating security safeguards in software--and of knowing they are really there and functioning correctly--is so difficult technically and the country's expertise so minimal, we can reasonably staff only one such Security Center at the moment. We would be wise to place all our eggs in this one basket with regard to the "trusted software" technology until additional expertise can be developed over the next five to ten years. Although CSC will be concerned with other aspects of security involving both computers and communications, it will not be concerned with the general administrative and procedural environment in which secure systems must operate. THE QUESTION OF LEADERSHIP Institute of Computer Science and Technology. Now I turn to the question of where the wisdom will come from within government to deal with the broad dimensions of computer security. Besides the technical aspects that relate not only to hardware and software but also to communications and emanation security (e.g., TEMPEST), there are also the physical, proce- April 1984 Volume 27 Number 4 The ICST is also involved in technical work. It published the Data Encryption Standard (DES) about five years ago, making a very significant contribution to the protection of information while in transit through a communication network. It also issues the Federal Information Processing Standards, which deal with such issues Communications of the ACM 317 Reports and Articles as the use of DES, the management of keys for it, risk assessment, and risk management. However, neither the ICST nor the CSC is providing the comprehensive overview that can stipulate • how to run a computer system securely, • what procedural and administrative safeguards must be in place, • what specific risks people represent, • what countermeasures can be taken against the nontechnical threats, • what management mechanisms should oversee security safeguards, and • what general protective precautions can be taken. No government entity has yet addressed the general policy issue of what constitutes a comprehensive, topto-bottom prescription for installing security controls, or identified the many dimensions of such a policy and made it available as guidance. Instead, security is being done piecemeal in the sense that each agency is either inventing it for itself or doing nothing. There is some policy guidance issued by the DoD in the form of general regulations and directives, and there are interagency committees and technical organizations in which people can trade ideas and talk, but there is little coordinated leadership. In the private sector, major corporations have built their own policy structures and devised implementation details. The government truly needs a comprehensive "howto-do-it" document that sets forth preferred practices and procedures for operating a secure computer system. The private sector could well use the same thing. Many ideas and much information exist but everything is scattered. The information is not collected and coordinated; it resides in people's heads or is embodied in daily activities and not otherwise documented. W e - the country--need to organize the collective wisdom of what is known and what is being done, and make it widely available. Both government and the private sector need a comprehensive handbook describing how to run computer systems securely. It would not be a momentous chore to collect this information. General Services Administration. As a first step, I would recommend that since the GSA has had a major role in the computer affairs of government, the GSA be tasked to compile such a comprehensive handbook of preferred practices and procedures for running a computer center securely. It is not a big undertaking. It is not an endeavor for tens or dozens of people working for many years. A team of 318 Communications of the ACM a few people could survey the federal agencies and a selected set of large corporations, assemble the composite wisdom of what is being done and what is known, and get it written down, probably in about a year or so. In testimony before this committee on September 26, 1983, Stephen Walker suggested that a federal center be set up to do some of the tasks suggested above. Such a federal center would undoubtedly be a good idea, and we clearly should have one in the long run. The idea is appealing because clearly CSC cannot do everything; moreover, some of its technical expertise can never be shared because of national defense reasons. But, in the large, CSC represents an innovative opportunity for interaction between the federal government and the commercial sector and, although it can respond to technical issues and examine and certify commercial software products, it is not likely to take up the less esoteric and more mundane issues that a federal center might accommodate. Meanwhile, until, and if, we get such an organization in place, there is no reason why the ICST and the GSA ought not do what clearly can now be done. PRIVACY I do not want to conclude this testimony without touching briefly on privacy. First, let me respond to a statement that I believe was made here by Congressman Wirth. I disagree strongly with his observation that all the aspects of privacy have now been attended to. In fact, most of the recommendations made by the Privacy Protection Study Commission have not been implemented in law, and moreover there are new dimensions of privacy that the Commission did not even identify or deal with. To date, privacy has largely been interpreted in terms of record-keeping processes, but it is clear that widespread application of computer and communication systems to provide a broad spectrum of services will put on the horizon many new dimensions of the privacy problem. Electronic Mail. We are seeing the emergence of systems that contain vast amounts of information about people but not solely or even essentially for recordkeeping purposes. For example, electronic mail, which the U.S. Postal Service is promoting as "E-COM," transports information from sender to addressee, and, to the extent that such information is personal in nature, the system will contain much information about people (although not for record-keeping purposes). In addition to the actual message content, the system contains information relating addressee to sender, which could be used to establish relationships among groups of people, either as organized groups or circles of acquaintances. Such information might be of great interest to the law enforcement community, among others, but the legal umbrella of protection over it is confused and probably incomplete. Whatever one believes about the security of information held in the hands of the Postal Service's E-COM, the private electronic mail services (e.g., MCI and GTE) April 1984 Volume 27 Number 4 Reports and Articles Who owns the electronic mail in a computer system that provides service to the general public? pose additional questions. 1 In the case of the private carriers, there is little, if any, legal protection for the sanctity of message information. Electronic mail also leaves the door open to unwarranted surveillance. At the Army's DARCOM, the inhouse investigative staff (Criminal Investigation Division) on at least three occasions obtained a complete printout of the electronic mail system that provides internal office-automation support. 2 On at least one occasion, the FBI was also involved. In effect, several hundred workers who use electronic mail in the conduct of their business had all their computer records read; and in at least one instance, an individual was intimidated. The privacy of the workplace records of hundreds of people was invaded, and hundreds of people were caught up in an investigative sweep with no recourse to protect themselves. It all sounds very much like search and seizure without due process of law, or like a fishing expedition to see if something wrong had happened or if some crime had been committed. In this instance, the computer happened to be agency owned; one wonders what might have happened if the mail service had been provided by a commercial vendor whose computer was located on private premises. I do not know the motivations of the investigative groups, and I only know one side of the story. Perhaps they were tracking down hackers, or maybe it had to do with possible fraud or embezzlement. I have no wish to make this incident a cause c~l~bre, but it is useful to underscore the ease with which new privacy issues arise as computer and communications technologies become commonplace and a wide variety of new services is available to an ever-growing population of users. This incident exemplifies a new dimension of priv a c y - a c c e s s without a c t i o n - - w h i c h is also seen in the computer matching of files. Individuals who either happen to keep records in a computer system or who are themselves record subjects in a computer file have their privacy invaded whether or not they have done anything wrong. Private information is exposed to a third party and quite possibly to hostile eyes. In effect, all the hundreds of office workers or all the data subjects in a computer file have, a priori, been assumed to be guilty; the examination of mail or the matching of 1 A New York Times article (J.B. Treaster, Computer intrusion reported in 18 companies and U.S, agencies, Sunday (Oct. 23}, 1983, p. 21) describes the unauthorized penetration of the Telemail service offered by GTE and the subsequent access to the electronic mail of major U.S. companies such as Raytheon, Coca Cola U.S.A., and the 3M Company, as well as several federal agencies such as NASA and the Department of Agriculture. 2 D. Burnham. Can privacy and computer coexist? New York Times, Saturday (Nov. 5), 1983, p. 11. April 1984 Volume 27 Number 4 computer records is to demonstrate that they are not. It sounds like a "back-end-to process" kind of justice. There were some pleasant revelations of this particular office-automation seizure. In a system like this, hundreds of people will keep hundreds of messages each; there will be tens of thousands of messages altogether. Only two aberrant ones were found: a babysitter's phone number and a cooking recipe. The odds are that each item, admittedly personal, was transmitted more efficiently by electronic mail than by a phone call or a walk to another person's desk, and in this sense the electronic mail system surely diverted much less people-time from the job than any other means of interpersonal communication. Although there are certainly management problems involved in assuring that corporate or business resources are not used for personal reasons, I salute the management discipline of an agency that operates such a tight facility--two items out of many tens of thousands is really an infinitesimal ratio; and I also acknowledge the integrity of the hundreds of people who are using it. Let us suppose that a government agency were to use a commercial electronic mail service that is supplied by a computer host that is not in the District of Columbia. 3 There is no question that electronic mail is an efficient mechanism to facilitate the conduct of business in any large organization, but let us examine the potential risks to such an arrangement. The observations I make are not critical of any one private sector vendor but are likely true for all. • It is unlikely that the phone lines, whether dial-up or dedicated, between Washington and any other state are protected by an encryption process. Electronic eavesdropping and wiretapping are therefore distinct possibilities. • It is unlikely that the computer system would have special security safeguards because standard commercial equipment is often used for such services. One would assume that the vendor has provided the appropriate physical, administrative, and personnel safeguards. • Since the electronic traffic would flow across state lines, it becomes a matter for federal law; however, currently there is no law protecting electronically transmitted data. • In principle, the body of computer-contained electronic mail would be subject to the same seizure experienced by the DARCOM office workers. The private vendor would have no legal standing to resist such an incursion. Although I am not suggesting for a moment that some agency of government would set out to seize the electronic mail of another, some outside group might, and government mail could get 3 After the presentation of this testimony, the author's attention was called to a New York Times article (D. Burnham. White House link: Computer in Ohio. (July 13), 1983, late city final ed., p. 18, sect. A, col. 4) describing the Executive Data Link System that provides the Executive Branch of government (66 officials in 22 agencies) with electronic mail services from CompuServe, Inc., headquartered in Columbus, Ohio. The article in question also reported by name the officials who were to use it (e.g., Treasury Secretary Regan, Agriculture Secretary Block). Communications of the ACM 319 Reports and Articles caught up in an investigative sweep aimed at someone else. Why all my emphasis on both security and privacy of electronic mail? Electronic mail should not be thought of as simply the electronic analog of the envelope. Perhaps one-fourth of my business interactions and transactions occur electroqic~lly; at the moment there are about 600 messages in my mailbox and it can get as high as a thousand. Why? It represents the written record of my conduct of business with a variety of individuals and organizations and is much more efficient than writing letters, making phone calls, and then writing memoranda-of-record. Moreover, I can organize the messages by folders and subfolders so that the system becomes a comprehensive automated filing and retrieval system. Anyone having access to this body of information might just as well have the key to my office and to its file cabinets. Such a comprehensive business records service is really what electronic mail is all about, and it is a service that will soon be offered by the private sector. Can you imagine the possibilities for various degrees of wrongdoing and snooping when all that information-both private and corporate--gets into electronic mail systems? Can you imagine what a lucrative target it will become for all sorts of reasons? The computer matching of files from different agencies we have seen so far will be nothing compared to what might arise when someone starts comparing files from electronic mail systems. Some of the issues relevant to the information contained in such electronic mail systems are as follows: • It is not clear who owns the information; is it the owner of the computer system per se? Does the owner have the right to hunt through the information in the system as he sees fit? Or when asked to by a third party? • It is not clear if, or by what law, this information is protected. How, legally, will intrastate service offerings differ from interstate offerings or even, in the long run, from international services? • What are the legalities of search-and-seizure? Can, and must, the private vendor resist such overtures? What should be the extent of the vendor's obligations to the users of his system in case of attempted seizure? • What should be the liability of the purveyor of the service in the event that something untoward happens to one's electronic mail records? What is his responsibility or obligation if his system accidentally spills information to the wrong party? What is his responsibility if his staff accidentally sees mail information and uses it for private gain, for purposes of personal embarrassment, for political advantage, or for exposures that represent a breach of national welfare and security? What are the vendor's obligations in terms of providing comprehensive security safeguards for his system? Should they be mandated by law? Should it be 320 Communications of the ACM caveat emptor for both private sector and government alike? Should the government be concerned that so much corporate information is subject to penetration by unfriendly agents? • How should electronic mail be treated relative to telephone conversations? Over the years, certain privacy protections have arisen for telephone billing records; formal legal processes are now necessary to wiretap or to obtain telephone records. Should similar protections exist for electronic mail, and should they apply uniformly in government and the private sector. Many of these same issues will be pertinent in other areas. For example, voice mail, the spoken analog of electronic mail, is actively being promoted by private vendors and by various telephone companies. Voice mail has all the vulnerabilities of electronic mail when offered by public vendors; moreover, an intruder can always claim that a particular individual's voice can be recognized, although his typed signature can be forged by someone else at the keyboard. Although encryption techniques can be used to protect electronic mail, present systems do not offer sender-to-reader encryption options, and it is even more difficult technically to provide speaker-to-listener protection for voice mail. Furthermore, point-of-sale systems, debit card systems at the merchant's premises, automated checkout stands in grocery stores, and a whole host of other systems all collect and contain information about people as a collateral consequence of their primary intent. But the whole subject of what the future holds for privacy and what its new dimensions will be, is for another day; I have left you just a teaser of what it will be all about. Nonetheless, electronic mail is upon us now. A NATIONAL COMMISSION In the hearings on September 26, 1983, Congressman Wirth and Donn Parker proposed the formation of a National Commission to investigate computer crime. By contrast, a year or so ago I had suggested at a National Computer Conference that a National Commission A National Commission is needed to examine a broad panoply of information and computer-related matters. would be an appropriate forum in which to examine the possible vulnerabilities of our highly computerized society. The fact is that there is a whole set of interrelated issues that could well be collectively examined by a congressionally chartered commission, the common element being the handling of information by computer and communication systems. The Commission could look at such things as computer-related crime, new dimensions of privacy, national vulnerability as a result April 1984 Volume 27 Number 4 Reports and Articles of computerization, representation of information, social consequences of intensive computerization, personal identification in a highly automated society, and dislocations of power as a result of concentrations of information. As such an agenda might be too much for one body, a judgment call is clearly in order to decide whether there should be one or several commissions. My personal experience with the Privacy Protection Study Commission has persuaded me that a congressionally chartered commission is the appropriate mechanism for addressing broad national policy issues that transcend the jurisdictional boundaries of federal agencies and both public and private sector interests. Furthermore, a National Commission can represent an enormous bargain for the country in terms of the work accomplished. For example, the PPSC delivered about 60 person-years of research on the subject of recordkeeping practices in the private sector for about $2.5 million. This represents about $40,000 per person-year of effort or about one-third of what it would have cost if done by a private contractor. In my view there is a right and a wrong way to structure a commission, but that is a subject for another time, should Congress be persuaded to move that way. I have given here a brief overview of a very intricate and complex issue. There must be a national priority to ensure adequate security protection in our public and private information systems and to attend to the new privacy issues that arise. If Congress has the will to pursue the issue and give it the attention it deserves, the time is now right for action. Let's get the GSA going; let's put ICST to work; let's address electronic mail as the most pressing of the new dimensions of privacy. Let's think about making 1984 "the right year" to launch a Commission to comprehensively examine the many issues about which we have talked. Author's Present Address:WillisH. Ware, The Rands Corporation,1700 MainStreet, Santa Monica,CA 90406. Permissionto copy without fee all or part of this material is granted provided that the copiesare not made or distributedfor direct commercial advantage,the ACM copyrightnotice and the title of the publication and its date appear, and noticeis giventhat copyingis by permissionof the Associationfor ComputingMachinery.To copy otherwise, or to republish, requires a fee and/or specificpermission. ACM SPECIALINTERESTGROUPS ARE YOUR TECHNICAL INTERESTS HERE? The ACM Special Interest Groups further the advancement of computer science and practice in many specialized areas. Members of each SlG receive as one of their benefits a periodical exclusively devoted to the special interest. The following are the publications that are available-through membership or special subscription. SIGACT NEWS (Automata and Computability Theory) SIGAPL Quote Quad (APL) SIGARCH Computer Architecture News (Architecture of Computer Systems) SIGART Newsletter (Artificial Intelligence) SIGBDP DATABASE (Business Data Processing) SIGBIO Newsletter (Biomedical Computing) SIGCAPH Newsletter (Computers and the Physically Handicapped) Print Edition April 1984 Volume 27 Number 4 SIGCAPH Newsletter, Cassette Edition SIGCAPH Newsletter, Print and Cassette Editions SIGCAS Newsletter (Computers and Society) SIGCHI Bulletin (Computer and Human Interaction) SIGCOMM Computer Communications Review (Data Communications) SIGCPR Newsletter (Computer Personnel Research) SIGCSE Bulletin (Computer Science Education) SIGCUE Bulletin (Computer Uses in Education) SIGDA Newsletter (Design Automation) SIGDOC Newsletter (Systems Documentation) SIGGRAPH Computer Graphics (Computer Graphics) SIGIR Forum (Information Retrieval) SIGMAP Newsletter (Mathematical Programming) SIGMETRICS Performance Evaluation Review (Measurement and Evaluation) SIGMICRO Newsletter (Microprogramming) SIGMOD Record (Management of Data) SIGNUM Newsletter (Numerical Mathematics) SIGOA Newsletter (Office Automation) SIGOPS Operating Systems Review (Operating Systems) SIGPC Newsletter (Personal Computing) SIGPLAN Notices (Programming Languages) SIGPLAN ADATEC Newsletter (Technical Committee on Ada) SIGPLAN FORTEC Newsletter (Technical Committee on Fortran) SIGSAC Newsletter (Security, Audit and Control) SIGSAM Bulletin (Symbolic and Algebraic Manipulation) SIGSIM Simuletter (Simulation and Modeling) SIGSMALL Newsletter (Small Computing Systems and Applications) SIGSOFT Software Engineering Notes (Software Engineering) SIGUCCS Newsletter (University and College Computing Services) Communications of the ACM 321