802.x
advertisement

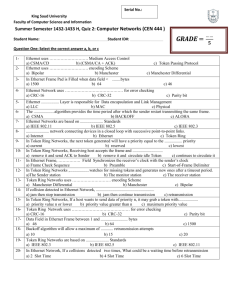
IEEE 802 LANs • LAN: Local Area Network • What is a local area network? – A LAN is a network that resides in a geographically restricted area – LANs usually span a building or a campus HMG/HUT MAC Protocols (802.x) June 2004 1 Characteristics of LANs • Short propagation delays • Small number of users • Single shared medium (usually) • Inexpensive HMG/HUT MAC Protocols (802.x) June 2004 2 Common LANs • Bus-based LANs – Ethernet (*) – Token Bus (*) • Ring-based LANs – Token Ring (*) • Switch-based LANs – Switched Ethernet – ATM LANs (*) IEEE 802 LANs HMG/HUT MAC Protocols (802.x) June 2004 3 IEEE 802 Standards 802.1: Introduction 802.2: Logical Link Control (LLC) 802.3: CSMA/CD (Ethernet) 802.4: Token Bus 802.5: Token Ring 802.6: DQDB 802.11: CSMA/CA (Wireless LAN) HMG/HUT MAC Protocols (802.x) June 2004 4 IEEE 802 Standards (cont’d) • 802 standards define: – Physical layer protocol – Data link layer protocol • Medium Access (MAC) Sublayer • Logical Link Control (LLC) Sublayer HMG/HUT MAC Protocols (802.x) June 2004 5 OSI Layers and IEEE 802 OSI layers Higher Layers IEEE 802 LAN standards Higher Layers 802.2 Logical Link Control Data Link Layer Physical Layer 802.3 802.4 802.5 Medium Access Control CSMA/CD Token-passing Token-passing bus bus ring HMG/HUT MAC Protocols (802.x) June 2004 6 IEEE 802 LANs (cont’d) • Ethernet • Token Ring HMG/HUT MAC Protocols (802.x) June 2004 7 Ethernet (CSMA/CD) • IEEE 802.3 defines Ethernet • Layers specified by 802.3: – Ethernet Physical Layer – Ethernet Medium Access (MAC) Sublayer HMG/HUT MAC Protocols (802.x) June 2004 8 Ethernet (cont’d) • Possible Topologies: 1. Bus 2. Branching non-rooted tree for large Ethernets HMG/HUT MAC Protocols (802.x) June 2004 9 Ethernet: MAC Layer • Data encapsulation – Frame Format – Addressing – Error Detection • Link Management – CSMA/CD – Backoff Algorithm HMG/HUT MAC Protocols (802.x) June 2004 10 Ethernet Frame Format Bytes: 7 1 Preamble SFD Preamble SFD 1. 2. 3. 4. 5. 6. 6 6 DA DA SA SA 2 Type Type 0-1500 Data Data 0-46 4 Pad CRC Pad CRC Preamble: trains clock-recovery circuits Start of Frame Delimiter: indicates start of frame Destination Address: 48-bit globally unique address assigned by manufacturer. 1b: unicast/multicast 1b: local/global address Type: Indicates protocol of encapsulated data (e.g. IP = 0x0800) Pad: Zeroes used to ensure minimum frame length Cyclic Redundancy Check: check sequence to detect bit errors. HMG/HUT MAC Protocols (802.x) June 2004 11 Ethernet MAC Frame Address Field • Destination and Source Addresses: – 6 bytes each • Two types of destination addresses – Physical address: Unique for each user – Multicast address: Group of users – First bit of address determines which type of address is being used 0 = physical address 1 = multicast address HMG/HUT MAC Protocols (802.x) June 2004 12 Ethernet MAC Frame Other Fields • Length Field – 2 bytes in length – determines length of data payload • Data Field: between 0 and 1500 bytes • Pad: Filled when Length < 46 • Frame Check Sequence Field – 4 bytes – Cyclic Redundancy Check (CRC-32) HMG/HUT MAC Protocols (802.x) June 2004 13 CSMA/CD • Recall: – CSMA/CD is a “carrier sense” protocol. • If channel is idle, transmit immediately • If busy, wait until the channel becomes idle – CSMA/CD can detect collections. • Abort transmission immediately if there is a collision • Try again later according to a backoff algorithm HMG/HUT MAC Protocols (802.x) June 2004 14 CSMA/CD (cont’d) • Carrier sense reduces the number of collisions • Collision detection reduces the impact of collisions HMG/HUT MAC Protocols (802.x) June 2004 15 CSMA/CD and Ethernet • Ethernet: – Short end-to-end propagation delay – Broadcast channel • Ethernet access protocol: – 1-Persistent CSMA/CD – with Binary Exponential Backoff Algorithm HMG/HUT MAC Protocols (802.x) June 2004 16 Ethernet Backoff Algorithm: Binary Exponential Backoff • If collision, – Choose one slot randomly from 2k slots, where k is the number of collisions the frame has suffered. – One contention slot length = 2 x end-to-end propagation delay This algorithm can adapt to changes in network load. HMG/HUT MAC Protocols (802.x) June 2004 17 Binary Exponential Backoff (cont’d) slot length = 2 x end-to-end delay = 15 µs A t=0µs: t=30µs: t=45µs: t=75µs: B Assume A and B collide (kA = kB = 1) A, B choose randomly from 21 slots: [0,1] Assume A chooses 1, B chooses 1 A and B collide (kA = kB = 2) A, B choose randomly from 22 slots: [0,3] Assume A chooses 2, B chooses 0 B transmits successfully A transmits successfully HMG/HUT MAC Protocols (802.x) June 2004 18 Binary Exponential Backoff (cont’d) • In Ethernet, – Binary exponential backoff will allow a maximum of 15 retransmission attempts – If 16 backoffs occur, the transmission of the frame is considered a failure. HMG/HUT MAC Protocols (802.x) June 2004 19 Ethernet Performance HMG/HUT MAC Protocols (802.x) June 2004 20 Ethernet Features and Advantages 1. Passive interface: No active element 2. Broadcast: All users can listen 3. Distributed control: Each user makes own decision Simple Reliable Easy to reconfigure HMG/HUT MAC Protocols (802.x) June 2004 21 Ethernet Disadvantages • Lack of priority levels • Cannot perform real-time communication • Security issues HMG/HUT MAC Protocols (802.x) June 2004 22 Ethernet Switching • Recent development: Connect many Ethernet segments or subnets through an “Ethernet switch” to segment 4 to segment 1 to segment 3 to segment 2 HMG/HUT MAC Protocols (802.x) June 2004 23 Why Ethernet switching? • LANs may grow very large – The switch has a very fast backplane – It can forward frames very quickly from one segment to another • Cheaper than upgrading all host interfaces to use a faster network HMG/HUT MAC Protocols (802.x) June 2004 24 Token Ring • IEEE 802.5 Standard • Layers specified by 802.5: – Token Ring Physical Layer – Token Ring MAC Sublayer HMG/HUT MAC Protocols (802.x) June 2004 25 Token Ring (cont’d) • Token Ring, unlike Ethernet, requires an active interface Ring interface Host HMG/HUT MAC Protocols (802.x) June 2004 26 Token Ring Configuration HMG/HUT MAC Protocols (802.x) June 2004 27 Token Ring Configuration HMG/HUT MAC Protocols (802.x) June 2004 28 Token Ring MAC Sublayer • Token passing protocol • Frame format • Token format HMG/HUT MAC Protocols (802.x) June 2004 29 Token Passing Protocol • A token (8 bit pattern) circulates around the ring • Token state: – Busy: 11111111 – Idle: 11111110 HMG/HUT MAC Protocols (802.x) June 2004 30 Token Passing Protocol (cont’d) • General Procedure: – Sending host waits for and captures an idle token – Sending host changes the token to a frame and circulates it – Receiving host accepts the frame and continues to circulate it – Sending host receives its frame, removes it from the ring, and generates an idle token which it then circulates on the ring HMG/HUT MAC Protocols (802.x) June 2004 31 Token Ring Frame and Token Formats Bytes 1 1 1 SD AC ED Token Format 1 1 1 SD AC FC 2/6 2/6 Destination Address Source Address unlimited Data 4 Checksum 1 1 ED FS Frame Format HMG/HUT MAC Protocols (802.x) June 2004 32 Token Ring Delimiters SD AC ED SD AC FC Destination Address Source Address Data Checksum ED FS • SD = Starting Delimiter • ED = Ending Delimiter • They contains invalid differential Manchester codes HMG/HUT MAC Protocols (802.x) June 2004 33 Token Ring Access Control Field SD AC ED (Note: The AC field is also used in frames) PPPTMRRR • P = Priority bits – provides up to 8 levels of priority when accessing the ring • T = Token bit – T=0: Token – T=1: Frame HMG/HUT MAC Protocols (802.x) June 2004 34 Token Ring Access Control Field (cont’d) SD AC ED PPPTMRRR • M = Monitor Bit – – – – – Prevents tokens and frames from circulating indefinitely All frames and tokens are issued with M=0 On passing through the “monitor station,” M is set to 1 All other stations repeat this bit as set A token or frame that reaches the monitor station with M=1 is considered invalid and is purged HMG/HUT MAC Protocols (802.x) June 2004 35 Token Ring Access Control Fields (cont’d) SD AC ED PPPTMRRR • R = Reservation Bits – Allows stations with high priority data to request (in frames and tokens as they are repeated) that the next token be issued at the requested priority HMG/HUT MAC Protocols (802.x) June 2004 36 Token Ring Frame Control Field SD AC FC Destination Address Source Address Data Checksum ED FS • FC = Frame Control Field – Defines the type of frame being sent – Frames may be either data frames or some type of control frame. Example control frames: • Beacon: Used to locate breaks in the ring • Duplicate address test: Used to test if two stations have the same address HMG/HUT MAC Protocols (802.x) June 2004 37 Token Ring Address & Data Fields SD AC FC Destination Address Source Address Data Checksum ED FS • Address Fields: – Indicate the source and destination hosts – Broadcast: • Set all destination address bits to 1s. • Data – No fixed limit on length – Caveat: Hosts may only hold the token for a limited amount of time (10 msec) HMG/HUT MAC Protocols (802.x) June 2004 38 Token Ring Checksum and Frame Status SD AC FC Destination Address Source Address Data Checksum ED FS • Checksum: 32-bit CRC • FS = Frame Status – Contains two bits, A and C – When the message arrives at the destination, it sets A=1 – When the destination copies the data in the message, it sets C=1 HMG/HUT MAC Protocols (802.x) June 2004 39 The Token Ring Monitor Station • One station on the ring is designated as the “monitor station” • The monitor station: – marks the M bit in frames and tokens – removes marked frames and tokens from the ring – watches for missing tokens and generates new ones after a timeout period HMG/HUT MAC Protocols (802.x) June 2004 40 Using Priority in Token Ring • If a host wants to send data of priority n, it may only grab a token with priority value n or lower. • A host may reserve a token of priority n by marking setting the reservation bits in the AC field of a passing token or frame – Caveat: The host may not make the reservation if the token or frame’s AC field already indicates a higher priority reservation • The next token generated will have a priority equal to the reserved priority HMG/HUT MAC Protocols (802.x) June 2004 41 • When a new token is generated (i.e., when a sender finishes sending and releases an idle token), or when a sender sends a data frame, RRR is set to the lowest priority. HMG/HUT MAC Protocols (802.x) June 2004 42 Priority Transmission: Example A B C D Host B has 1 frame of priority 3 to send to A Host C has 1 frame of priority 2 to send to A Host D has 1 frame of priority 4 to send to A Token starts at host A with priority 0 and circulates clockwise Host C is the monitor station (priority 0: lowest priority in this example) HMG/HUT MAC Protocols (802.x) June 2004 43 Example (cont’d) Event Token/Frame AC Field A generates a token P=0, M=0, T=0, R=0 B grabs the token and sets the message destination to A P=3, M=0, T=1, R=0 Frame arrives at C, and C reserves priority level 2. Monitor bit set. P=3, M=1, T=1, R=2 Frame arrives at D, and D attempts to reserve priority level 4: P=3, M=1, T=1, R=4 Frame arrives at A, and A copies it P=3, M=1, T=1, R=4 Frame returns to B, so B removes it, and generates a new token P=4, M=0, T=0, R=0 Token arrives at C, but its priority is too high. C reserves priority 2. M bit. P=4, M=1, T=0, R=2 HMG/HUT MAC Protocols (802.x) June 2004 44 Example (cont’d) Event Token/Frame AC Field Token arrives at D, and D grabs it, sending a message to A P=4, M=0, T=1, R=0 Frame arrives at A, and A copies it P=4, M=0, T=1, R=0 Frame arrives at B, which does nothing to it P=4, M=0, T=1, R=0 Frame arrives at C, which sets the monitor bit P=4, M=1, T=1, R=2 Frame returns to D, so D removes it and generates a new token with P=2 P=2, M=0, T=0, R=0 etc… Attempt to complete this scenario on your own. HMG/HUT MAC Protocols (802.x) June 2004 45 TOKEN RING Performance • Ring Topology • A bit pattern token (1111 1111) floats on the ring • Station captures token, converts to connector (11 11 1110), transmits frame • Intermediate stations relay message/token. • Token is released when (a) Leading edge of frame is received, and (b) Frame is transmitted. HMG/HUT MAC Protocols (802.x) June 2004 46 Throughput : Simple Analysis Time required by a bit to traverse the whole ring a = ---------------------------------------------------Frame transmission time Number of active stations : N Average time to pass token to the next station: a/N HMG/HUT MAC Protocols (802.x) June 2004 47 t0 t0+a t0+1 t0+a+1 (a) (b) (c) (d) Fig for case 1 HMG/HUT MAC Protocols (802.x) June 2004 48 Case 1 ( a<1) (a) Frame transmission begins (b) Leading edge received. © Total frame is transmitted and token is released. (d) Total frame is received. Average time to transmit frame S = --------------------------------------------------(Time elapsed between a token is transmitted + Average Token Passing Time) 1 S= a 1+ N HMG/HUT MAC Protocols (802.x) June 2004 49 t0 t0+1 t0+a (a) (b) (c) t0+a+1 (d) Fig for case 2 ( a > 1) HMG/HUT MAC Protocols (802.x) June 2004 50 Case 2 (a > 1) (a) Frame transmission begins (b) Frame transmission completed. © Leading edge received and token is released. (d) Total frame is received. S = 1 a+ a N for a > 1 HMG/HUT MAC Protocols (802.x) June 2004 51 Delay and stability No. of stations (equally spaced) = Mean time for token to travel round the ring = Mean Token Cycle Time = Mean Packet Transmission Time = During T • All N queues are served. • Mean number of packets are transmitted = Q N R T X • Token rotates (with mean value R) T= R+QX HMG/HUT MAC Protocols (802.x) June 2004 52 For stable system Departures = Arrivals Q =NλT ρ = λ X (for one station) T (1 − Nρ ) = R - Token is free with probability (1-Nρ) - Token is in use with probability Nρ • Nρ<1 • ρ<1/N HMG/HUT MAC Protocols (802.x) June 2004 53 • Average number of packets transmitted from a queue in T=Q/N • In limited service (IEEE 802.5 has THT) λT < m – m packets served per token visit • Tagged job methodology and residual service time analysis gives Average waiting delay (excluding service delay),W as [ ] ( NρΕ x 2 1 + ρ )R W= + 2 + (1 − Nρ − λR ) 2(1 − Nρ − λR ) HMG/HUT MAC Protocols (802.x) June 2004 54 Flavor #1: Release After Reception (RAR) • Computer captures token, transmits data, waits for data to successfully travel around ring, then releases token again. • Allows computer to detect errored frames and retransmit them. Example time evolution in which host 1 and host 3 have packets to transmit: TRANSP PROP TRANST Data Token l1/c l2/c Token arrives at host 1 TRANST lN/c Data Token l1/c TRANSP l2/c Token arrives Token departs at host 3 from host 1 Token arrives at host 2 HMG/HUT MAC Protocols (802.x) June 2004 l3/c time 55 Efficiency of RAR Recall: Efficiency, η, is the fraction of time spent sending useful data. Define: Ti,j to be the time from when the token arrives at host i until it next arrives at host j. T1, 2 ≤ TRANSP + PROP + TRANST + l1 / c ∴T1,1 ≤ N (TRANSP + PROP + TRANST ) + ∑i li / c = N (TRANSP + PROP + TRANST ) + PROP N (TRANSP ) N (TRANSP + PROP + TRANST ) + PROP 1 PROP ≈ , a= , TRANSP >> TRANST 1+ a TRANSP ∴η RAR ≤ HMG/HUT MAC Protocols (802.x) June 2004 56 Flavor #2: Release After Transmission (RAT) • Computer captures token, transmits data, then releases token again. Example time evolution in which host 1 and host 3 have packets to transmit: TRANSP Data TRANST TRANST Token Token arrives at host 1 Data Token l1/c TRANSP l2/c Token arrives Token departs at host 3 from host 1 Token arrives at host 2 HMG/HUT MAC Protocols (802.x) June 2004 Token time 57 Efficiency of RAT T1, 2 ≤ TRANSP + TRANST + l1 / c ∴T1,1 ≤ N (TRANSP + TRANST ) + ∑i li / c = N (TRANSP + TRANST ) + PROP N (TRANSP ) N (TRANSP + TRANST ) + PROP 1 PROP ≈ , a= , TRANSP >> TRANST 1+ a / N TRANSP ∴η RAT ≤ HMG/HUT MAC Protocols (802.x) June 2004 58