10.4 Which of the following programming techniques and structures
advertisement

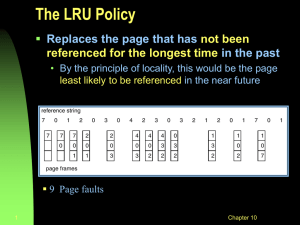
10.4 Which of the following programming techniques and structures are “good” for a demand-paged environment ? Which are “not good”? Explain your answers. a. Stack b. Hashed symbol table c. Sequential search d. Binary search e. Pure code f. Vector operations g. Indirection Answer: a. Stack—good. b. Hashed symbol table—not good. c. Sequential search—good. d. Binary search—not good. e. Pure code—good. f. Vector operations—good. g. Indirection—not good. 10.5 Assume we have a demand-paged memory. The page table is held in registers. It takes 8 milliseconds to service a page fault if an empty page is available or the replaced page is not modified, and 20 milliseconds if the replaced page is modified. Memory access time is 100 nanoseconds. Assume that the page to be replaced is modified 70 percent of the time. What is the maximum acceptable page-fault rate for an effective access time of no more than 200 nanoseconds? Answer: 0.2 sec = (1 P) 0.1 sec + (0.3P) 8 millisec + (0.7P) 20 millisec 0.1 = 0.1P + 2400 P + 14000 P 0.1 16,400 P P 0.000006 _ _ _ _ _ _ _ ' ' 10.6 Consider the following page-replacement algorithms. Rank these algorithms on a five point scale from “bad” to “perfect” according to their page-fault rate. Separate those algorithms that suffer from Belady’s anomaly from those that do not. a. LRU replacement b. FIFO replacement c. Optimal replacement d. Second-chance replacement Answer: Rank Algorithm Suffer from Belady’s anomaly 1 Optimal no 2 LRU no 3 Second-chance yes 4 FIFO yes 10.7 When virtual memory is implemented in a computing system, there are certain costs associated with the technique and certain benefits. List the costs and the benefits. Is it possible for the costs to exceed the benefits? If it is, what measures can be taken to ensure that this does not happen? Answer: The costs are additional hardware and slower access time. The benefits are good utilization of memory and larger logical address space than physical address space. 10.11 Consider the following page reference string: 1, 2, 3, 4, 2, 1, 5, 6, 2, 1, 2, 3, 7, 6, 3, 2, 1, 2, 3, 6. How many page faults would occur for the following replacement algorithms, assuming one, two, three, four, five, six, or seven frames? Remember all frames are initially empty,so your first unique pages will all cost one fault each. LRU replacement FIFO replacement Optimal replacement Answer: Number of frames LRU FIFO Optimal 1 20 20 20 2 18 18 15 3 15 16 11 4 10 14 8 5 8 10 7 6 7 10 7 7 7 7 7 _ _ _ 10.16 A page-replacement algorithm should minimize the number of page faults. We can do this minimization by distributing heavily used pages evenly over all of memory, rather than having them compete for a small number of page frames. We can associate with each page frame a counter of the number of pages that are associated with that frame. Then, to replace a page, we search for the page frame with the smallest counter. a. Define a page-replacement algorithm using this basic idea. Specifically address the problems of (1) what the initial value of the counters is, (2) when counters are increased, (3) when counters are decreased, and (4) how the page to be replaced is selected. b. How many page faults occur for your algorithm for the following reference string, for four page frames? 1, 2, 3, 4, 5, 3, 4, 1, 6, 7, 8, 7, 8, 9, 7, 8, 9, 5, 4, 5, 4, 2. c. What is the minimum number of page faults for an optimal page-replacement strategy for the reference string in part b with four page frames? Answer: a. Define a page-replacement algorithm addressing the problems of: i. Initial value of the counters—0. ii. Counters are increased—whenever a new page is associated with that frame. iii. Counters are decreased—whenever one of the pages associated with that frame is no longer required. iv. How the page to be replaced is selected—find a frame with the smallest counter. Use FIFO for breaking ties. b. 14 page faults c. 11 page faults 10.17 Consider a demand-paging system with a paging disk that has an average access and transfer time of 20 milliseconds. Addresses are translated through a page table in main memory, with an access time of 1 microsecond per memory access. Thus, each memory reference through the page table takes two accesses. To improve this time, we have added an associative memory that reduces access time to one memory reference, if the page-table entry is in the associative memory. Assume that 80 percent of the accesses are in the associative memory and that, of the remaining, 10 percent (or 2 percent of the total) cause page faults. What is the effective memory access time? Answer: effective access time = (0.8) (1 sec) + (0.1) (2 sec) + (0.1) (5002 sec) = 501.2 sec = 0.5 millisec _ _ _ _ _ _ _ 10.20 What is the cause of thrashing? How does the system detect thrashing? Once it detects thrashing, what can the system do to eliminate this problem? Answer: Thrashing is caused by underallocation of the minimum number of pages required by a process, forcing it to continuously page fault. The system can detect thrashing by evaluating the level of CPU utilization as compared to the level of multiprogramming. It can be eliminated by reducing the level of multiprogramming. 11.5 What are the advantages and disadvantages of recording the name of the creating program with the file’s attributes (as is done in the Macintosh Operating System)? Answer: By recording the name of the creating program, the operating system is able to implement features (such as automatic program invocation when the file is accessed) based on this information. It does add overhead in the operating system and require space in the file descriptor, however. 11.11 In some systems, a subdirectory can be read and written by an authorized user, just as ordinary files can be. a. Describe the protection problems that could arise. b. Suggest a scheme for dealing with each of the protection problems you named in part a. Answer: a. One piece of information kept in a directory entry is file location. If a user could modify this location, then he could access other files defeating the access-protection scheme. b. Do not allow the user to directly write onto the subdirectory. Rather, provide system operations to do so. 11.12 Consider a system that supports 5000 users. Suppose that you want to allow 4990 of these users to be able to access one file. a. How would you specify this protection scheme in UNIX? b. Could you suggest another protection scheme that could be used more effectively for this purpose than the scheme provided by UNIX? Answer: a. There are two methods for achieving this: i. Create an access control list with the names of all 4990 users. ii. Put these 4990 users in one group and set the group access accordingly. This scheme cannot always be implemented since user groups are restricted by the system. b. The universe access information applies to all users unless their name appears in the access-control list with different access permission. With this scheme you simply put the names of the remaining ten users in the access control list but with no access privileges allowed. 12.4 Why must the bit map for file allocation be kept on mass storage rather than in main memory? Answer: In case of system crash (memory failure), the free-space list would not be lost as it would be if the bit map had been stored in main memory. 12.5 Consider a system that supports the strategies of contiguous, linked, and indexed allocation. What criteria should be used in deciding which strategy is best utilized for a particular file? Answer: Contiguous—if file is usually accessed sequentially, if file is relatively small. Linked—if file is large and usually accessed sequentially. Indexed—if file is large and usually accessed randomly. _ _ _ 12.9 How do caches help improve performance? Why do systems not use more or larger caches if they are so useful? Answer: Caches allow components of differing speeds to communicate more efficiently by storing data from the slower device, temporarily, in a faster device (the cache). Cachesare, almost by definition, more expensive than the device they are caching for, so increasing the number or size of caches would increase system cost.