Introduction to UNIX OS: Kernel, Shell, and File System
advertisement
mohsin Sheikh
Page 1
Chapter 1
Introduction to UNIX OS
What is UNIX?
UNIX is an operating system which was first developed in the 1960s, and has been under constant development ever since.
By operating system, we mean the suite of programs which make the computer work. It is a stable, multi-user, multi-tasking
system for servers, desktops and laptops.
UNIX systems also have a graphical user interface (GUI) similar to Microsoft Windows which provides an easy to use
environment. However, knowledge of UNIX is required for operations which aren't covered by a graphical program, or for
when there is no windows interface available, for example, in a telnet session.
Types of UNIX
There are many different versions of UNIX, although they share common similarities. The most popular varieties of UNIX
are Sun Solaris, GNU/Linux, and MacOS X.
The UNIX operating system
The UNIX operating system is made up of three parts; the kernel, the shell and the programs.
The kernel
The kernel of UNIX is the hub of the operating system: it allocates time and memory to programs and handles the filestore
and communications in response to system calls.
As an illustration of the way that the shell and the kernel work together, suppose a user types rm myfile (which has the effect
of removing the file myfile). The shell searches the filestore for the file containing the program rm, and then requests the
kernel, through system calls, to execute the program rm on myfile. When the process rm myfile has finished running, the
shell then returns the UNIX prompt % to the user, indicating that it is waiting for further commands.
The shell
The shell acts as an interface between the user and the kernel. When a user logs in, the login program checks the username
and password, and then starts another program called the shell. The shell is a command line interpreter (CLI). It interprets the
commands the user types in and arranges for them to be carried out. The commands are themselves programs: when they
terminate, the shell gives the user another prompt (% on our systems).
The adept user can customise his/her own shell, and users can use different shells on the same machine. Staff and students in
the school have the tcsh shell by default.
The tcsh shell has certain features to help the user inputting commands.
Filename Completion - By typing part of the name of a command, filename or directory and pressing the [Tab] key, the tcsh
shell will complete the rest of the name automatically. If the shell finds more than one name beginning with those letters you
have typed, it will beep, prompting you to type a few more letters before pressing the tab key again.
History - The shell keeps a list of the commands you have typed in. If you need to repeat a command, use the cursor keys to
scroll up and down the list or type history for a list of previous commands.
Why Use Shells?
mohsin Sheikh
Page 2
Well, most likely because the are a simple way to string together a bunch of UNIX commands for execution at any time
without the need for prior compilation. Also because its generally fast to get a script going. Not forgetting the ease with
which other scripters can read the code and understand what is happening. Lastly, they are generally completely portable
across the whole UNIX world, as long as they have been written to a common standard.
The Shell History:
The basic shells come in three main language forms. These are (in order of creation) sh, csh and ksh. Be aware that there are
several dialects of these script languages which tend to make them all slightly platform specific. Where these differences are
known to cause difficulties I have made special notes within the text to highlight this fact. The different dialects are due, in
the main, to the different UNIX flavours in use on some platforms. All script languages though have at their heart a common
core which if used correctly will guarantee portability.
Bourne Shell:
Historically the sh language was the first to be created and goes under the name of The Bourne Shell. It has a very compact
syntax which makes it obtuse for novice users but very efficient when used by experts. It also contains some powerful
constructs built in. On UNIX systems, most of the scripts used to start and configure the operating system are written in the
Bourne shell. It has been around for so long that is it virtually bug free. I have adopted the Bourne shell syntax as the defacto
standard within this book.
C Shell:
Next up was The C Shell (csh), so called because of the similar syntactical structures to the C language. The UNIX man
pages contain almost twice as much information for the C Shell as the pages for the Bourne shell, leading most users to
believe that it is twice as good. This is a shame because there are several compromises within the C Shell which makes using
the language for serious work difficult (check the list of bugs at the end of the man pages!). True, there are so many functions
available within the C Shell that if one should fail another could be found. The point is do you really want to spend your time
finding all the alternative ways of doing the same thing just to keep yourself out of trouble. The real reason why the C Shell
is so popular is that it is usually selected as the default login shell for most users. The features that guarantee its continued use
in this arena are aliases, and history lists. There are rumours however, that C Shell is destined to be phased out, with future
UNIX releases only supporting sh and ksh. Differences between csh and sh syntax will be highlighted where appropriate.
Korne Shell:
Lastly we come to The Korne Shell (ksh) made famous by IBM's AIX flavour of UNIX. The Korne shell can be thought of
as a superset of the Bourne shell as it contains the whole of the Bourne shell world within its own syntax rules. The
extensions over and above the Bourne shell exceed even the level of functionality available within the C Shell (but without
any of the compromises!), making it the obvious language of choice for real scripters. However, because not all platforms are
yet supporting the Korne shell it is not fully portable as a scripting language at the time of writing. This may change however
by the time this book is published. Korne Shell does contain aliases and history lists aplenty but C Shell users are often put
off by its dissimilar syntax. Persevere, it will pay off eventually. Any sh syntax element will work in the ksh without change.
Files and processes
Everything in UNIX is either a file or a process.
A process is an executing program identified by a unique PID (process identifier).
A file is a collection of data. They are created by users using text editors, running compilers etc.
mohsin Sheikh
Page 3
Examples of files:
a document (report, essay etc.)
the text of a program written in some high-level programming language
instructions comprehensible directly to the machine and incomprehensible to a casual user, for example, a collection
of binary digits (an executable or binary file);
a directory, containing information about its contents, which may be a mixture of other directories (subdirectories)
and ordinary files.
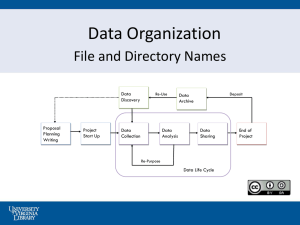
The Directory Structure
All the files are grouped together in the directory structure. The file-system is arranged in a hierarchical structure, like an
inverted tree. The top of the hierarchy is traditionally called root (written as a slash / )
In the diagram above, we see that the home directory of the undergraduate student "ee51vn" contains two sub-directories
(docs and pics) and a file called report.doc.
The full path to the file report.doc is "/home/its/ug1/ee51vn/report.doc"
General Unix Information
There are numerous flavours of Unix; AIX (IBM), Solaris (SUN), Xenix, Linux etc. all of which conform to the Posix
standard. Unix often comes with a number of command shells, e.g. Bourne Shell ($ prompt) or C shell (% prompt with
enhancements on the Bourne Shell) or Korn shell ($ prompt) which have slightly differing command syntax, although
principally they are the same. The shell interprets the commands that you type. The 'Tea Sea Shell' (tcsh) is often used in the
Linux environment and contains useful attributes such as 'up-arrow' and 'down-arrow' recall of previous command entries,
and the use of the TAB key to complete commands (much like the Cisco IOS!). The shell interprets commands with the
mohsin Sheikh
Page 4
operating system kernel. The beauty of Unix is that hundreds of people can access one box at once and each one can run a
number of programs, a separate shell opens for each log on that occurs, and each user can have a completely different
'environment' setup, different colours, priviledges, file and directory access and different shell.
Unix file names can be up to 14 characters long and include the _ and the . characters.
Every Unix command or filename is case sensitive, unlike DOS, this is the most common error to be aware of. Commands
leave 'notes' for programs (such as printing) that are 'buried' in the Unix system. This is so that one user does not hog one
program, many people can access it. Such a program is called a 'daemon'.
Below is a diagram illustrating a typical Unix file system structure on a box:
An Absolute Pathname starts from the root directory e.g. /user/bin. The Relative pathname points to a file or directory that
is relative to the position that you are in within the directory tree and this does not start with a /.
Information about users is kept in the passwd file which sits in the /etc directory along with the other configuration files. For
each user there are seven fields separated by colons:
User name (first part of e-mail address).
Encrypted password.
UID (Users ID) needed by the Unix system. User names can change without changing user permissions.
GID (Group ID). A user may be a member of several groups each having different permissions.
Comment containing more detail on the user if desired.
User's home directory.
The shell to be used by the particular user.
Nowadays, when you are confronted with a Unix box you will come across an X-windows interface. To get to a command
line interface, grab the three button mouse click the right button and select programs clicking on it with the left mouse
button. In the list of programs that appear select either shell or command to open a command line window (much like a DOS
box in Microsoft Windows). You normally need to click on the title bar or border before you can type in the window,
sometimes the X-window interface has been set up such that the mouse moving over the window is enough to highlight the
box. Any number of these command line windows can be opened. Resizing them is achieved by selecting the bottom right
hand corner with the left mouse button (a circle appears) and dragging the window edges to the required size. Minimising a
window is achieved by 'left-clicking' on the top left corner of the menu bar and selecting close. Selecting quit closes the
window.
Keystrokes
mohsin Sheikh
Page 5
Ctrl-c :-Stops a command or program that is currently being executed.
Ctrl-d:-Removes you from the current environment, this will log you out of the system if you are at a shell prompt.
Ctrl-h, Del:-Deletes the last character typed and moves back one space. Unlike DOS, the backspace key does not work!
Ctrl-q:-Resumes the command that was halted by Ctrl-s.
Ctrl-s:-Temporarily halts the current command being executed, e.g. scrolling of text on the screen.
Ctrl-u, Ctrl-x, @:-Cancels what you have just typed, so that you can start again.
Ctrl-x:-Deletes the current line of text being entered.
mohsin Sheikh
Starting an UNIX terminal
To open an UNIX terminal window, click on the "Terminal" icon from Applications/Accessories menus.
An UNIX Terminal window will then appear with a % prompt, waiting for you to start entering commands .
Page 6
mohsin Sheikh
Page 7
Chapter 2
The vi Editor
The UNIX full screen editor `vi' is a tightly designed editing system in which almost every letter has a function and the
function is stronger for upper than lower case. However, a letter and its actual function are usually closely related. It is
important to remember that the `(Esc)' escape key ends most functions and a `(Esc), (Esc)' double application certainly ends
the function with the ring of a bell. The subcommand `u' undoes the last function (presumably an error). Use `:q! (CR)' to end
with out saving, especially in hopeless situations. Use `:wq (CR)' to resave and end {`ZZ' also resaves and ends, but will not
resave if the file has been saved in another file and no further changes have been made}, or `:w (CR)' to only resave. The
character `:' prompts the UNIX line editor `ex' which you can think of as being embedded in `vi'. Some of the above critical
`vi' subcommands are repeated below with others. Most `vi' subcommands are not displayed when used and do not take a
carriage return `(CR)'. The fact that most keys have a meaning both as single characters and as concatenations of several
characters has many benefits, but has disadvantages in that mistakes can turn out to be catastrophic. {Remember that `(Esc),
(Esc), u' key sequence!} {WARNING: `VI' is disabled during an IBM Telnet session.}
(Esc) : End a command; especially used with insert `i', append `a' or replace 'R'.
(Esc), (Esc) : Ensured end of a command with bell; press the Escape-key twice; use it.
u : Undoes last command; usually used after `(Esc)' or `(Esc), (Esc)'; if undoing is worse then repeat `u' again to
undo the undoing.
:set all (CR) : Display all vi options. Use this ex command when your initial vi session is poor. Customized options
are placed in the `.exrc' ex resource configuration profile.
:w (CR) : Save or resave the default file being edited, but do not end.
:w [file] (CR) : Save into a new file [file], but do not end.
:w! [file] (CR) : Save or resave into an existing file [file], but do not end.
:q (CR) : Quit vi without saving, provided no changes have been made since the last save.
:q! (CR) : Quit vi without saving, living the file as it was in the last save.
:wq (CR) : Save the default file being edited, and quit.
ZZ : Save the edited file, provided not changes have been made since the last save of the edited file to any file, and
quit `vi'. {Warning: if you just saved the edited file into any other file, the file will NOT be resaved. `:wq (CR) is
much safer to use.}
h or j or k or l : The arrow keys, such that
k = up
^
|
h = left <-- --> right = l
|
v
j = down
each take a number prefix that moves the cursor that many times.
(CR) : moves cursor a line forward; `+' also does.
mohsin Sheikh
Page 8
-- : Moves cursor a line backward.
[N] (CR) : Moves cursor [N] lines forwards.
[N]-- : Moves cursor [N] lines backwards.
Ctrl-f : Moves cursor a page forward.
Ctrl-b : Moves cursor a page backward.
Ctrl-d : Moves cursor a half page down.
Ctrl-u : Moves cursor a half page up.
[L]G : Go to line [L]. `1G' moves the cursor to the beginning of the file (BOF).
G : Go to the last line just before the end of file (EOF) mark. `$G' does the same thing.
0 : Go to beginning of the line (BOL).
^ : Go to beginning of the nonblank part of the line (BOL).
~ : Got to first nonblank character on a line.
$ : Go to end of the line (EOL).
[N]| : Go to column [N] of the current line.
% : Find the matching parenthesis.
/[string] (CR) : Find the next occurrence of `[string]' forwards. Use `n' to repeat, or `N' to search backwards.
?[string] (CR) : Find the next occurrence of` [string]' backwards.
n : Repeat last `/[string] (CR)' or `?[string] (CR)'; think of the file as being wrapped around from end to beginning,
so that when you return to the start you know that you have found all occurrences.
N : Repeat last `/[string] (CR)' or `?[string] (CR)', but in reverse.
. : Repeat last change. This is best used along with the repeat search `n' or `N'.
i[string](Esc) : Insert a string `[string]' before current character at the cursor; the subcommand `i' itself and other
subcommands are not displayed; a `(CR)' in the string during the insert is used to continue input on additional lines;
end with the escape key `(Esc)' or `(Esc), (Esc)'.
o[string](Esc) : Opens a new line below the current line for insertion of string `[string]'; end with `(Esc)' or `(Esc),
(Esc)'; use for POWER TYPING input for an old or new file; `O[string](Esc)' opens a new line above the current
line for insertion.
I[string](Esc) : Insert a string at the beginning of the current line (BOL), else is like insert `i';a `(CR)' in the string
during the insert is used to continue input on additional lines; end with `(Esc)' or `(Esc), (Esc)'.
J : Joins next line to current line.
mohsin Sheikh
Page 9
a[string](Esc) : Appends a string `[string]' following the current character at the cursor, else it works like insert `i';
use `(CR)' in the string to continue input onto new lines; end with `(Esc)'; also use for POWER TYPING.
A[string](Esc) : Appends a string `[string]' at the end of a line (EOL), works like `i' or `a'; use `(CR)' in the string to
continue input onto new lines; end with `(Esc)'; also use for POWER TYPING.
r[C](SPACE) : Replace a single character over the cursor by the single character [C]; finalize with the Space-bar.
R[string](Esc) : Replace a string of characters by `[string]' in until `(Esc)' is typed to end.
s[string](Esc) : Substitutes the string `[string]' for the single character at the cursor. The multiple form
`[N]s[string](Esc)' substitutes `[string]' for the `[N]' characters starting at the cursor.
x : Delete the current character at the cursor.
d(SPACE) : Deletes a single character. `[N]d(SPACE)' deletes `[N]' characters.
dd : Deletes the current line. `[N]dd' deletes `[N]' lines.
D : Deletes from the cursor to the end of line (EOL).
dw : Deletes the current word; `[N]dw' deletes `[N]' words.
w : Move cursor to the beginning of the next word. `[N]w' moves the cursor `[N]' words forward. `[N]b' moves it
`[N]' words backward. `[N]e' moves it to the end of the word.
[N]y(SPACE) : Yanks `[N]' characters starting at the cursor and puts them into the default buffer. `[N]yy' yanks
`[N]' lines.
p : Puts the current contents of the default buffer after the cursor if characters or after the current line if lines.
Helpful to use right after a character yank `y' or a character delete `d' or a line yank `yy' or a line delete `dd', along
with a search `/[string](CR)' or repeat search `n'. and a repeat change `.'. `P' puts the contents of the default buffer
before the current line.
"b[N]Y : Yank [N] lines starting with the current line to the buffer labeled b; the double quote {"} is used to avoid
an id conflict with subcommand names; any letter other than `x' can be used to name the buffer; safer than the line
yank `yy' because it is very easy to accidentally change the default buffer.
"b[N]dd : Deletes [N] lines starting with the current line to the buffer labeled `b'.
"bp : Put back lines from the buffer labeled `b' after or below the cursor; use after a yank or delete to a labeled buffer
to move groups of lines from one location to another.
"bP : Put back lines from the buffer labeled `b' before or above the cursor; use after a yank or delete to a labeled
buffer to move groups of lines from one location to another.
Some `ex' editor commands that are useful in `vi' follow the `:' prompt. See the previous section on `ex' for more commands.
:nu (CR) : Number current line.
:[L1],[L2] d (CR) : Deletes lines `[L1]' to `[L2]'.
:[L1],[L2] m [L3] (CR) : Move lines `[L1]' to `[L2]' to after line `[L3]'.
:[L1],[L2] t [L3] (CR) : Take [copy] lines `[L1]' to `[L2]` to `[L3]'; destination `[L3]' can not be in `[L1]' to `[L2]-1'.
mohsin Sheikh
Page 10
:[L1],[L2]s/[string1]/[string2]/g (CR) : Substitute `[string2]' for all `[string1]' in lines `[L1]' to `[L2]' only.
:s/[string1]/[string2]/gp (CR) : Substitute `[string2]' for all `[string1]' in current line only and print change(s).
:g/[string1]/s/{/}[string2]/gp (CR) : Globally substitute `[string2]' for each `[string1]' in all lines and print changes;
works globally; use `?' in place of `/' if `[string*]' contains a `/'.
:[L]r [file] (CR) : Append file [file] at line `[L]'.
mohsin Sheikh
Page 11
Chapter 3
Generic Commands
cat --- for creating and displaying short files
chmod --- change permissions
cd --- change directory
cp --- for copying files
date --- display date
echo --- echo argument
ftp --- connect to a remote machine to download or upload files
grep --- search file
head --- display first part of file
ls --- see what files you have
lpr --- standard print command (see also print )
more --- use to read files
mkdir --- create directory
mv --- for moving and renaming files
ncftp --- especially good for downloading files via anonymous ftp.
print --- custom print command (see also lpr )
pwd --- find out what directory you are in
rm --- remove a file
rmdir --- remove directory
rsh --- remote shell
setenv --- set an environment variable
sort --- sort file
tail --- display last part of file
tar --- create an archive, add or extract files
telnet --- log in to another machine
wc --- count characters, words, lines
cat
This is one of the most flexible Unix commands. We can use to create, view and concatenate files. For our first example we
create a three-item English-Spanish dictionary in a file called "dict."
% cat >dict
red rojo
green verde
blue azul
<control-D>
%
<control-D> stands for "hold the control key down, then tap 'd'". The symbol > tells the computer that what is typed is to be
put into the file dict. To view a file we use cat in a different way:
% cat dict
red rojo
green verde
blue azul
%
If we wish to add text to an existing file we do this:
% cat >>dict
mohsin Sheikh
Page 12
white blanco
black negro
<control-D>
%
Now suppose that we have another file tmp that looks like this:
% cat tmp
cat gato
dog perro
%
Then we can join dict and tmp like this:
% cat dict tmp >dict2
We could check the number of lines in the new file like this:
% wc -l dict2
8
The command wc counts things --- the number of characters, words, and line in a file.
cat is one of the most frequently used commands on Unix-like operating systems. It has three related functions with regard to
text files: displaying them, combining copies of them and creating new ones.
cat's general syntax is
cat [options] [filenames] [-] [filenames]
The square brackets indicate that the enclosed items are optional.
Reading Files
The most common use of cat is to read the contents of files, and cat is often the most convenient program for this purpose.
All that is necessary to open a text file for viewing on the display monitor is to type the word cat followed by a space and the
name of the file and then press the ENTER key. For example, the following will display the contents of a file named file1:
cat file1
The standard output (i.e., default destination of the output) for cat, as is generally the case for other command line (i.e., alltext mode) programs, is the monitor screen. However, it can be redirected from the screen, for example, to another file to be
written to that file or to another command to use as the input for that command.
In the following example, the standard output of cat is redirected using the output redirection operator (which is represented
by a rightward pointing angular bracket) to file2:
cat file1 > file2
That is, the output from cat is written to file2 instead of being displayed on the monitor screen.
The standard output could instead be redirected using a pipe (represented by a vertical bar) to a filter (i.e., a program that
transforms data in some meaningful way) for further processing. For example, if the file is too large for all of the text to fit on
the monitor screen simultaneously, as is frequently the case, the text will scroll down the screen at high speed and be very
difficult to read. This problem is easily solved by piping the output to the filter less, i.e.,
cat file1 | less
mohsin Sheikh
Page 13
This allows the user to advance the contents of the file one screenful at a time by pressing the space bar and to move
backwards by pressing the b key. The user can exit from less by pressing the q key.
The standard input (i.e., the default source of input data) for cat, as is generally the case for other commands on Unix-like
systems, is the keyboard. That is, if no file is specified for it to open, cat will read whatever is typed in on the keyboard.
Typing the command cat followed by the output redirection operator and a file name on the same line, pressing ENTER to
move to the next line, then typing some text and finally pressing ENTER again causes the text to be written to that file. Thus,
in the following example the text that is typed on the second line will be written to a file named felines:
cat
This is not about a feline.
>
felines
The program is terminated and the normal command prompt is restored by pressing the CONTROL and d keys
simultaneously.
Repeating the above example without using a redirection operator and specifying a destination file, i.e.,
cat
This is not about a feline.
causes the text to be sent to standard output, i.e., to be repeated on the monitor screen.
Concatenation
The second role of cat is concatenation (i.e., stringing together) of copies of the contents of files. (This is the source of cat's
curious name.) Because the concatenation occurs only to the copies, there is no effect on the original files.
For example, the following command will concatenate copies of the contents of the three files file1, file2 and file3:
cat file1 file2 file3
The contents of each file will be displayed on the monitor screen (which, again, is standard output, and thus the destination of
the output in the absence of redirection) starting on a new line and in the order that the file names appear in the command.
This output could just as easily be redirected using the output redirection operator to another file, such as file4, using the
following:
cat file1 file2 file3 > file4
In the next example, the output of cat is piped to the sort filter in order to alphabetize the lines of text after concatenation and
prior to writing to file4:
cat file1 file2 file3 | sort > file4
File Creation
The third use for cat is file creation. For small files this is often easier than using vi, gedit or other text editors. It is
accomplished by typing cat followed by the output redirection operator and the name of the file to be created, then pressing
ENTER and finally simultaneously pressing the CONTROL and d keys. For example, a new file named file1 can be created
by typing
cat > file1
mohsin Sheikh
Page 14
then pressing the ENTER key and finally simultaneously pressing the CONTROL and d keys.
If a file named file1 already exists, it will be overwritten (i.e., all of its contents will be erased) by the new, empty file with
the same name. Thus the cautious user might prefer to instead use the append operator (represented by two successive
rightward pointing angular brackets) in order to prevent unintended erasure. That is,
cat >> file1
That is, if an attempt is made to create a file by using cat and the append operator, and the new file has the same name as an
existing file, the existing file is, in fact, preserved rather than overwritten, and any new text is added to the end of the existing
file.
Text can be entered at the time of file creation by typing it in after pressing the ENTER key. Any amount of text can be
typed, including text on multiple lines.
cat can also be used to simultaneously create a new file and transfer to it the data from an existing file. This is accomplished
by typing cat, the name of the file from which the output will come, the output redirection operator and the name of the file to
be created. Then pressing ENTER causes the new file to be created and written to. For example, typing the following and
then pressing ENTER creates a new file named file2 that contains a copy of the contents of file1:
cat file1 > file2
There is no effect on the contents of file1. (The same thing can, of course, be accomplished just as easily using cp command,
which is used to copy files, i.e., cp file1 file2, but the above example does illustrate the great versatility of cat.)
A slight modification to the above procedure makes it possible to create a new file and write text into it from both another file
and the keyboard. A hyphen surrounded by spaces is added before the input file if the typed-in text is to come before the text
from the input file, and it is added after the input file if the typed-in text is to go after the text from the input file. Thus, for
example, to create a new file file6 that consists of text typed in from the keyboard followed by the contents of file5, first enter
the following:
cat - file5 > file6
Or to create a new file file8 that consists of the contents of file7 followed by text typed in from the keyboard, first enter the
following:
cat file7 - > file8
In either case, then press ENTER to move to a new line and type the desired text on any number of lines. Finally press
ENTER once more followed by pressing the CONTROL and d keys simultaneously to execute (i.e., run) the command.
An example of a practical application for this use of cat is the creation of form letters (or other documents) for which only the
top parts (e.g., dates and names) are customized for each recipient.
chmod
This command is used to change the permissions of a file or directory. For example to make a file essay.001 readable by
everyone, we do this:
% chmod a+r essay.001
mohsin Sheikh
Page 15
To make a file, e.g., a shell script mycommand executable, we do this
% chmod +x mycommand
Now we can run mycommand as a command.
To check the permissions of a file, use ls -l . For more information on chmod, use man chmod.
cd
Use cd to change directory. Use pwd to see what directory you are in.
% cd english
% pwd
% /u/ma/jeremy/english
% ls
novel poems
% cd novel
% pwd
% /u/ma/jeremy/english/novel
% ls
ch1 ch2 ch3 journal scrapbook
% cd ..
% pwd
% /u/ma/jeremy/english
% cd poems
% cd
% /u/ma/jeremy
Jeremy began in his home directory, then went to his english subdirectory. He listed this directory using ls , found that it
contained two entries, both of which happen to be diretories. He cd'd to the diretory novel, and found that he had gotten only
as far as chapter 3 in his writing. Then he used cd .. to jump back one level. If had wanted to jump back one level, then go to
poems he could have said cd ../poems. Finally he used cd with no argument to jump back to his home directory.
cp
Use cp to copy files or directories.
% cp foo foo.2
This makes a copy of the file foo.
% cp ~/poems/jabber .
This copies the file jabber in the directory poems to the current directory. The symbol "." stands for the current directory. The
symbol "~" stands for the home directory.
date
Use this command to check the date and time.
% date
Fri Jan 6 08:52:42 MST 1995
mohsin Sheikh
Page 16
echo
The echo command echoes its arguments. Here are some examples:
% echo this
this
% echo $EDITOR
/usr/local/bin/emacs
% echo $PRINTER
b129lab1
Things like PRINTER are so-called environment variables. This one stores the name of the default printer --- the one that
print jobs will go to unless you take some action to change things. The dollar sign before an environment variable is needed
to get the value in the variable. Try the following to verify this:
% echo PRINTER
PRINTER
ftp
Use ftp to connect to a remote machine, then upload or download files. See also: ncftp
Example 1: We'll connect to the machine fubar.net, then change director to mystuff, then download the file homework11:
% ftp solitude
Connected to fubar.net.
220 fubar.net FTP server (Version wu-2.4(11) Mon Apr 18 17:26:33 MDT 1994) ready.
Name (solitude:carlson): jeremy
331 Password required for jeremy.
Password:
230 User jeremy logged in.
ftp> cd mystuff
250 CWD command successful.
ftp> get homework11
ftp> quit
Example 2: We'll connect to the machine fubar.net, then change director to mystuff, then upload the file collected-letters:
% ftp solitude
Connected to fubar.net.
220 fubar.net FTP server (Version wu-2.4(11) Mon Apr 18 17:26:33 MDT 1994) ready.
Name (solitude:carlson): jeremy
331 Password required for jeremy.
Password:
230 User jeremy logged in.
ftp> cd mystuff
250 CWD command successful.
ftp> put collected-letters
ftp> quit
The ftp program sends files in ascii (text) format unless you specify binary mode:
ftp> binary
ftp> put foo
ftp> ascii
ftp> get bar
mohsin Sheikh
Page 17
The file foo was transferred in binary mode, the file bar was transferred in ascii mode.
grep
Use this command to search for information in a file or files. For example, suppose that we have a file dict whose contents
are
red rojo
green verde
blue azul
white blanco
black negro
Then we can look up items in our file like this;
% grep red dict
red rojo
% grep blanco dict
white blanco
% grep brown dict
%
Notice that no output was returned by grep brown. This is because "brown" is not in our dictionary file.
Grep can also be combined with other commands. For example, if one had a file of phone numbers named "ph", one entry per
line, then the following command would give an alphabetical list of all persons whose name contains the string "Fred".
% grep Fred ph | sort
Alpha, Fred: 333-6565
Beta, Freddie: 656-0099
Frederickson, Molly: 444-0981
Gamma, Fred-George: 111-7676
Zeta, Frederick: 431-0987
The symbol "|" is called "pipe." It pipes the output of the grep command into the input of the sort command.
For more information on grep, consult
% man grep
head
Use this command to look at the head of a file. For example,
% head essay.001
displays the first 10 lines of the file essay.001 To see a specific number of lines, do this:
% head -n 20 essay.001
This displays the first 20 lines of the file.
ls
Use ls to see what files you have. Your files are kept in something called a directory.
% ls
mohsin Sheikh
Page 18
foo
letter2
foobar letter3
letter1 maple-assignment1
%
Note that you have six files. There are some useful variants of the ls command:
% ls l*
letter1 letter2 letter3
%
Note what happened: all the files whose name begins with "l" are listed. The asterisk (*) is the " wildcard" character. It
matches any string.
lpr
This is the standard Unix command for printing a file. It stands for the ancient "line printer." See
% man lpr
for information on how it works. See print for information on our local intelligent print command.
mkdir
Use this command to create a directory.
% mkdir essays
To get "into" this directory, do
% cd essays
To see what files are in essays, do this:
% ls
There shouldn't be any files there yet, since you just made it. To create files, see cat or emacs.
more
More is a command used to read text files. For example, we could do this:
% more poems
The effect of this to let you read the file "poems ". It probably will not fit in one screen, so you need to know how to "turn
pages". Here are the basic commands:
q --- quit more
spacebar --- read next page
return key --- read next line
b --- go back one page
For still more information, use the command man more.
mohsin Sheikh
Page 19
mv
Use this command to change the name of file and directories.
% mv foo foobar
The file that was named foo is now named foobar
ncftp
Use ncftp for anonymous ftp --- that means you don't have to have a password.
% ncftp ftp.fubar.net
Connected to ftp.fubar.net
> get jokes.txt
The file jokes.txt is downloaded from the machine ftp.fubar.net.
print
This is a moderately intelligent print command.
% print foo
% print notes.ps
% print manuscript.dvi
In each case print does the right thing, regardless of whether the file is a text file (like foo ), a postcript file (like notes.ps, or a
dvi file (like manuscript.dvi. In these examples the file is printed on the default printer. To see what this is, do
% print
and read the message displayed. To print on a specific printer, do this:
% print foo jwb321
% print notes.ps jwb321
% print manuscript.dvi jwb321
To change the default printer, do this:
% setenv PRINTER jwb321
pwd
Use this command to find out what directory you are working in.
% pwd
/u/ma/jeremy
% cd homework
% pwd
/u/ma/jeremy/homework
% ls
assign-1 assign-2 assign-3
% cd
% pwd
/u/ma/jeremy
mohsin Sheikh
Page 20
%
Jeremy began by working in his "home" directory. Then he cd 'd into his homework subdirectory. Cd means " change
directory". He used pwd to check to make sure he was in the right place, then used ls to see if all his homework files were
there. (They were). Then he cd'd back to his home directory.
rm
Use rm to remove files from your directory.
% rm foo
remove foo? y
% rm letter*
remove letter1? y
remove letter2? y
remove letter3? n
%
The first command removed a single file. The second command was intended to remove all files beginning with the string
"letter." However, our user (Jeremy?) decided not to remove letter3.
rmdir
Use this command to remove a directory. For example, to remove a directory called "essays", do this:
% rmdir essays
A directory must be empty before it can be removed. To empty a directory, use rm.
rsh
Use this command if you want to work on a computer different from the one you are currently working on. One reason to do
this is that the remote machine might be faster. For example, the command
% rsh solitude
connects you to the machine solitude. This is one of our public workstations and is fairly fast.
See also: telnet
setenv
% echo $PRINTER
labprinter
% setenv PRINTER myprinter
% echo $PRINTER
myprinter
mohsin Sheikh
Page 21
sort
Use this commmand to sort a file. For example, suppose we have a file dict with contents
red rojo
green verde
blue azul
white blanco
black negro
Then we can do this:
% sort dict
black negro
blue azul
green verde
red rojo
white blanco
Here the output of sort went to the screen. To store the output in file we do this:
% sort dict >dict.sorted
You can check the contents of the file dict.sorted using cat , more , or emacs .
tail
Use this command to look at the tail of a file. For example,
% tail essay.001
displays the last 10 lines of the file essay.001 To see a specific number of lines, do this:
% tail -n 20 essay.001
This displays the last 20 lines of the file.
tar
Use create compressed archives of directories and files, and also to extract directories and files from an archive. Example:
% tar -tvzf foo.tar.gz
displays the file names in the compressed archive foo.tar.gz while
% tar -xvzf foo.tar.gz
extracts the files.
telnet
Use this command to log in to another machine from the machine you are currently working on. For example, to log in to the
machine "solitude", do this:
% telnet solitude
See also: rsh.
wc
mohsin Sheikh
Page 22
Use this command to count the number of characters, words, and lines in a file. Suppose, for example, that we have a file dict
with contents
red rojo
green verde
blue azul
white blanco
black negro
Then we can do this
% wc dict
5
10
56 tmp
This shows that dict has 5 lines, 10 words, and 56 characters.
The word count command has several options, as illustrated below:
% wc -l dict
5 tmp
% wc -w dict
10 tmp
% wc -c dict
56 tmp
Some Useful Commands
Word Count, or "wc"
A helpful UNIX command is the "word count" program that can count how many words are in the file.
wc -w <filename> counts the number of words in a file
wc -l <filename> counts lines in a file.
Grab Regular Expression, or "grep"
Another helpful command is "grep" for grabbing lines from a file that contain a specific string pattern, or regular
expression. The command grep <string> <files> looks through a list of files and finds lines that contain the specific
word in the string argument.
grep pvm_pack *.cpp will look for occurrences of the string "pvm_pack" in all files ending in ".cpp".
grep "My name is" * will look in all files in a directory trying to find the string "My name is".
Input / Output Redirection
The UNIX operating system has a number of useful tools for allowing other programs to work with one another.
One of the ways to handle screen input and output with I/O Redirection, and ways to link several programs together
with "pipes".
With the use of the > for sending output to a file, a user can easily covert from screen display programs to ones that
save the output without major changes in rewriting code. It is also very convenien for grabbing the output from
various UNIX commands, too.
myprogram > myoutfile
This takes the output of "myprogram" and sends it a file called "myoutfile".
mohsin Sheikh
Page 23
ls -alF > filelist
This runs the command "ls", but saves the directory listing to a file rather than displaying it on the screen.
In order to convert a program that originally required lots of user input into one that runs on its own, the input
redirection symbol < can be used to say where to get the values.
program2 < myinput
This runs "program2" but takes any keyboard input from the file "myinput". It is important the input values are in
the proper sequence in the file "myinput" since there will not be ways to reply to prompts at the console.
Pipes
The vertical bar "|" is called the pipe symbol, and it is designed for linking commands together to make them more
powerful. The way it works is that the output from one command is sent as input to the next, thus creating a new
command.
ls -alF | grep ".cpp"
This will list all files in a directory, and will then grab the names of only the ones that contain the string ".cpp" in the
name, or the C++ source files.
The system() command in C
The system() command is actually a C function that is very valuable for accessing UNIX commands from within a
C program. It can also be used to run other programs you have already written. Be careful with extensive use of this
command because according to the online manual pages (man), there are a few bugs such as not being able to break
out of infinite loops because interrupts are not processed, and some other security issues. For many of the things we
will be doing in this class, though, this command will be quite useful.
system( "ls - alF");
This will run the "ls" command from within a C program and display the results to the screen.
system ( "ps -aux | grep dhyatt > outfile");
This will run the "ps" command, the will send that output to "grep" which will look for occurrences of "dhyatt", and
finally will print the results to a file called "outfile" rather than displaying anything on the screen.
Directory Commands
cd
Stands for change directory, e.g.
cd /user/dave
takes you to dave's personal directory. The first / refers to root. Root is the equivalent of / in DOS. Typing cd without a path
takes you back to your home directory, i.e. where you arrive when you first log on. Typing cd.. takes you up one directory,
whereas typing cd ../user/dave, takes you up one directory and then right down to the '/user/dave' directory.
df -k
Stands for disk free, gives you the amount of space available on the disk that you are currently on.
mkdir
Means 'make directory', e.g.
mohsin Sheikh
Page 24
mkdir user
creates a directory called user in the directory you are in when you issue the command.
pwd
Stands for print working directory and prints the directory that you are in to the screen.
rmdir
Means remove directory e.g.
rmdir user
removes the directory user provided that it is empty!
Some More System Commands
-&
Using this switch after a command causes it to operate in the background, allowing you to continue using the same command
line window without having to open another one.
*
This wildcard character matches any number of characters and is useful in searches, e.g.
g*
matches all files beginning with 'g'.
?
This wildcard character matches any single character, e.g.
g??
matches all three character files beginning with 'g'.
>
Redirect output from a program to a file, e.g.
ls -l > listing
redirects the listing of ls -l into a file called 'listing'.
<
Redirect output from a file into a program, e.g.
mail john < hello
redirects the greeting letter called 'hello' to John, rather than you having to type it.
|
Pipe output from one program to another, e.g.
who | wc -l
gives a count of the users on the system.
>>
This append adds the input to an existing file without overwriting the original, e.g.
postcript >> letter
adds the contents of 'postscript' to an existing file called 'letter'.
mohsin Sheikh
Page 25
chsh
Means change shell and changes the shell that the user is using. The user will be prompted for a password since the 'passwd'
file is being changed, then the user will need to type the path to the shell e.g. /bin/bash.
echo
This 'echoes' arguments to the screen, e.g.
echo $SHELL
displays the value of the environment variable SHELL. This could return /bin/tcsh (Linux often uses this shell) or /bin/bash.
echo $PATH displays the current path.
env
The environment gives you the variables set up for the particular user that issues the command.
exit, Ctrl-d
Logs you out.
jobs
This lists the jobs running under the current shell in 'job ID' order. You can type bg %jobid to put a particular job running in
the background. Ctrl Z also suspends a job. Typing fg %jobid brings the job back to the foreground.
kill
This kills a process e.g.
kill 5173
kill the process which has been given the temporary number 5173. This process number is found by using the ps command.
Do not use kill 1 as this kills the system scheduler! If a process refuses to die you can type kill -KILL [PID] to stop a
process immediately without any tidying up on exitting. Finally, kill -HUP [PID] tells the process that an event has occurred,
or a configuration file change has occurred and needs to br reread.
man
The manual command is very useful for finding out comprehensive information on an individual command e.g.
man cd
gives all the information on the command cd. Typing man -k mail lists the Unix commands that relate to the word mail.
passwd
Allows you or the administrator to change passwords.
printenv
The 'prints the environment' variables to the screen.
ps
The process status command shows the programs currently running. ps -a shows all the processes being run by all users. An
example is the following:
ps -ef | grep erpcd
where '-ef' gets the process number and pipes it to grep which filters on the following word, in this case for the program
'erpcd'.
mohsin Sheikh
Page 26
The following information is shown:
PID Process ID.
TTY Each shell opened has a 'character special' called a 'tty' (held in '/dev').
STAT State, either 'S', sleeping, or 'R', running.
TIME CPU time that the process is taking up.
COMMAND The command running.
Typing ps x shows all the processes relating to X windows, whereas ps ax shows all the processes being run by everybody.
Typing ps ux gives even more information such as the user.
setenv
The command set environment variable, sets aside a small amount of memory to hold paths etc. e.g.
setenv GUI /usr/utility/gui_r4
sets a variable 'GUI' with the path that follows to the actual program. This program can now be run by typing 'GUI'.
setenv DISPLAY :0.0
sets an X window session locally.
These settings are commonly setup permanently in the user's .profile (located in the '/etc' directory). This can be edited with
any text editor.
The following are common environment variables:
SHELL The current shell.
HOME The current user's home directory.
HOSTNAME The name of the computer.
DISPLAY The X display that the applications are to use.
LD_LIBRARY_PATH The search path for libraries.
PATH The search path for applications.
If you wish to append directories to the path then type setenv PATH ${PATH} : /search/here. In order to use it then you
need to cache the new path by typing rehash.
The DISPLAY variable is made up of three parts 'hostname : displaynumber : screennumber'. The hostname is the computer,
whilst the other variables are '0' unless several machines are connected. X windows looks to this variable to find out where to
send the X Windows traffic.
set path
Sets a path where regularly used programs or data are found e.g.
set path=($path /usr/utility/gui_r4/bin)
sets the path '/usr/utility/gui_r4/bin'.
Some commands used to set the environment come from the C shell. In order to check which shell you are running type echo
$SHELL, if this does not return '/sbin/csh' then you type /bin/csh.
su
The command switch user switches the login user to another user, e.g.
su root
switches to the 'root' login.
top
mohsin Sheikh
Page 27
Gives a constantly updating view of the top 20 processes (a real time version of 'ps'), i.e. those that are using the CPU the
most.
who
This displays the users currently logged on the system.
whoami
Displays who you are currently logged on as. (e.g. 'root', a user etc.)
xhost +
Opens an X window for a program to run in. After issuing this you would then run the program (e.g. Netscape).
Some More File Commands
.
The dot is not a command as such. If a file is spelled with a dot at the beginning, Unix treats it as a hidden file. Configuration
files are often preceded with a dot.
chown
Use this to change ownership of a file e.g.
chown dave myfile
changes the ownership of the file 'myfile' to dave. This can only be carried out by the owner of the original file. A way
around this is for the recipient to copy the file, then the copied file becomes their own.
chgrp
Use this to change group ownership of a file.
compress
This compresses a file e.g.
compress myfile
results in a file called 'myfile.Z'. The command uncompress can be used to uncompress the file.
file
This returns information on the content of a file, e.g.
file myletter
might return 'ASCII' to say that Unix guesses that 'myletter' contains ASCII.
find
This finds a file or directory, e.g.
find / -name na -print &
this finds a file with name 'na' starting the search from the 'root' and printing the result to the shell window, whilst still
allowing you to carry on using it.
grep
mohsin Sheikh
Page 28
This stands for global regular expression and print and is a search utility, e.g.
grep "325 Victory"
searches the current directory for files containing the text '325 Victory'.
gzip
GNU zip compresses files to create a '**.gz' file.
head
This command followed by a filename, displays the first ten lines of that file.
less
This is a way of displaying a file, it will give a percentage of file so far displayed at the bottom of the screen, and you can
progress through reading the file by pressing the space bar.
ln
The command link, links files and directories, e.g.
ln -s/export/home/fred usr/fred
creates a copy of 'fred' in the '/export/home/' directory in the 'usr/fred' directory. A 'hard link' is like a Windows 'shortcut',
there can be a number of them, with different names and they take up little space. A 'soft link' is identified with the '-s' switch
and creates a copy of the file elsewhere.
lp (for System V) or lpr (for BSD)
The command line printer, prints a file, e.g.
lp newletter
prints 'newletter'.
lpstat -a all
The line printer stats command checks the printer queue in System V Unix.
pg filename
Displays the content of the file one page at a time. You advance pages by pressing 'Return'. Option -l displays one more line,
option n moves you to the page number specified by n and options +n and -n moves you forward or backward the number of
pages specified by n.
touch
This just creates an empty file for appending to later on e.g.
touch log
creates an empty file called 'log' that needs to be available for another program to write to it perhaps.
uncompress
This command uncompresses a 'gzip' file, e.g.
uncompress myfile.gz
uncompresses the file 'myfile.gz'.
mohsin Sheikh
Page 29
Networking Commands
arp
Displays the 'Address Resolution Protocol' table e.g.
arp -a
displays all arp entries for all connected devices.
arp -d <ip address>
deletes the arp entry for that particular IP address.
ftp
The command file transfer protocol attaches you to another IP device e.g.
ftp 141.205.15.154
attaches you to the device with address 141.205.15.154. You are normally presented with a login and password screen.
Commands that are used in FTP are:
dir - directory listing.
quit - quit from ftp.
cd - change directory.
get or mget - get a file (or multiple files).
put or mput - put a file (or multiple files).
bin - sets up your system to receive binary files.
hash - displays hashes whilst files are being transferred.
lcd - local change directory changes the directory on your local machine to which you are sending and receiving
files. This is useful as it saves you having to quit ftp to carry out the directory change.
The Hosts file can be found in the directory '/etc'.
netstat
This stands for network statistics, e.g.
netstat -r
displays the routing table of the Unix box.
netstat -a
displays alll network information.
Unix uses routed to listen to RIP in order to discover the Default Gateway.
ping
Ping an IP device e.g.
ping 141.205.51.26
rlogin
This works like telnet, e.g.
rlogin 141.205.52.16
takes you to another Unix machine only. To quit you press 'return', '~', .' and 'return' again.
telnet
Ctrl-6 and then Ctrl-] gets you to the telnet> prompt where typing close gets you out of telnet.
mohsin Sheikh
vstat
This displays CPU utilisation and gives a list of processes and their share of CPU utilisation, e.g.
vstat 10
displays the CPU utilisation every 10 seconds.
ifconfig
This displays the IP configuration of the box, e.g.
ifconfig -a
displays all IP configuration.
If you want to look at the routing process you can type:
ps -ef type grep routed
to send the 'routed' information to a file.
snoop
This command captures the network packets in a readable format, e.g.
snoop -p 23
captures all IP traffic using port 23 (Telnet). use Ctrl-C to stop the snoop.
Page 30
mohsin Sheikh
Page 31
Part -II
Chapter 4
mohsin Sheikh
Page 32
The mount command
All files accessible in a Unix system are arranged in one big tree, the file hierarchy, rooted at /. These files can be spread out
over several devices. The mount command serves to attach the file system found on some device to the big file tree.
Conversely, the umount(8) command will detach it again.
The Unix command line utility mount instructs the operating system that a file system is ready to use, and associates it with a
particular point in the system's file system hierarchy (its mount point). The counterpart umount [sic] instructs the operating
system that the file system should be disassociated from its mount point, making it no longer accessible. The mount and
umount commands require root user privilege or the corresponding fine-grained privilege, unless the file system is defined as
"user mountable" in the /etc/fstab file (which can only be modified by the root user).
mount [-lhV]
mount -a [-fFnrsvw] [-t vfstype] [-O optlist]
mount [-fnrsvw] [-o options [,...]] device | dir
mount [-fnrsvw] [-t vfstype] [-o options] device dir
Example
The second partition of a hard disk is mounted with the command:
$ mount /dev/hda2 /new/subdir
and unmounted with the command:
$ umount /dev/hda2
or
$ umount /new/subdir
To list all mounted file systems:
$ mount
To remount a partition with specific options:
$ mount -o remount,rw /dev/hda2
To mount an ISO file (Linux):
$ mount -o loop <isofile-source> <mount-point>
To mount all filesystems listed in fstab:
$ mount -a
pmount
mohsin Sheikh
Page 33
pmount is a wrapper around the standard mount program which permits normal users to mount removable devices without a
matching /etc/fstab entry. This provides a robust basis for automounting frameworks like GNOME's Utopia project and
confines the amount of code that runs as root to a minimum.
This package also contains a wrapper "pmount-hal" which reads information such as device labels and mount options from
HAL and passes them to pmount.
To configure, the administrator would add a list of devices to /etc/pmount.allow that non-root users can mount:
echo /media/cdrom >> /etc/pmount.allow &&
echo /media/dvd >> /etc/pmount.allow &&
echo /media/thumbdrive >> /etc/pmount.allow
gnome-mount
The gnome-mount package contains programs for mounting, unmounting and ejecting storage devices. The goal for gnomemount is for GNOME software such as gnome-volume-manager and GNOME-VFS to use this instead of invoking
mount/umount/eject/pmount or direct HAL invoking methods (GNOME previously used pmount). gnome-mount is not
intended for direct use by users.
All the gnome-mount programs utilize HAL methods and as such run unprivileged. The rationale for gnome-mount is to have
a centralized place (in GConf) where settings such as mount options and mount locations are maintained
mount -t type device dir
This tells the kernel to attach the file system found on device (which is of type type) at the directory dir. The previous
contents (if any) and owner and mode of dir become invisible, and as long as this file system remains mounted, the pathname
dir refers to the root of the file system on device.
Three forms of invocation do not actually mount anything:
mount -h
prints a help message;
mount -V
prints a version string; and just
mount [-l] [-t type]
lists all mounted file systems (of type type). The option -l adds the (ext2, ext3 and XFS) labels in this listing. See below.
Since Linux 2.4.0 it is possible to remount part of the file hierarchy somewhere else. The call is
mount --bind olddir newdir
After this call the same contents is accessible in two places. One can also remount a single file (on a single file).
This call attaches only (part of) a single filesystem, not possible submounts. The entire file hierarchy including submounts is
attached a second place using
mount --rbind olddir newdir
mohsin Sheikh
Page 34
Note that the filesystem mount options will remain the same as those on the original mount point, and cannot be changed by
passing the -o option along with --bind/--rbind.
Since Linux 2.5.1 it is possible to atomically move a mounted tree to another place. The call is
mount --move olddir newdir
Since Linux 2.6.15 it is possible to mark a mount and its submounts as shared, private, slave or unbindable. A shared mount
provides ability to create mirrors of that mount such that mounts and umounts within any of the mirrors propagate to the
other mirror. A slave mount receives propagation from its master, but any not vice-versa. A private mount carries no
propagation abilities. A unbindable mount is a private mount which cannot cloned through a bind operation. Detailed
semantics is documented in Documentation/sharedsubtree.txt file in the kernel source tree.
mount
mount
mount
mount --make-unbindable mountpoint
--make-shared
--make-slave
--make-private
mountpoint
mountpoint
mountpoint
The following commands allows one to recursively change the type of all the mounts under a given mountpoint.
mount
mount
mount
"mount --make-runbindable mountpoint"
--make-rshared
--make-rslave
--make-rprivate
mountpoint
mountpoint
mountpoint
The proc file system is not associated with a special device, and when mounting it, an arbitrary keyword, such as proc can be
used instead of a device specification. (The customary choice none is less fortunate: the error message 'none busy' from
umount can be confusing.)
Most devices are indicated by a file name (of a block special device), like /dev/sda1, but there are other possibilities. For
example, in the case of an NFS mount, device may look like knuth.cwi.nl:/dir. It is possible to indicate a block special device
using its volume label or UUID (see the -L and -U options below).
The file /etc/fstab (see fstab(5)), may contain lines describing what devices are usually mounted where, using which options.
This file is used in three ways:
(i) The command
mount -a [-t type] [-O optlist]
(usually given in a bootscript) causes all file systems mentioned in fstab (of the proper type and/or having or not having the
proper options) to be mounted as indicated, except for those whose line contains the noauto keyword. Adding the -F option
will make mount fork, so that the filesystems are mounted simultaneously.
(ii) When mounting a file system mentioned in fstab, it suffices to give only the device, or only the mount point.
(iii) Normally, only the superuser can mount file systems. However, when fstab contains the user option on a line, anybody
can mount the corresponding system.
Thus, given a line
/dev/cdrom /cd iso9660 ro,user,noauto,unhide
mohsin Sheikh
Page 35
any user can mount the iso9660 file system found on his CDROM using the command
mount /dev/cdrom
or
mount /cd
For more details, see fstab(5). Only the user that mounted a filesystem can unmount it again. If any user should be able to
unmount, then use users instead of user in the fstab line. The owner option is similar to the user option, with the restriction
that the user must be the owner of the special file. This may be useful e.g. for /dev/fd if a login script makes the console user
owner of this device. The group option is similar, with the restriction that the user must be member of the group of the
special file.
The programs mount and umount maintain a list of currently mounted file systems in the file /etc/mtab. If no arguments are
given to mount, this list is printed.
When the proc filesystem is mounted (say at /proc), the files /etc/mtab and /proc/mounts have very similar contents. The
former has somewhat more information, such as the mount options used, but is not necessarily up-to-date (cf. the -n option
below). It is possible to replace /etc/mtab by a symbolic link to /proc/mounts, and especially when you have very large
numbers of mounts things will be much faster with that symlink, but some information is lost that way, and in particular
working with the loop device will be less convenient, and using the "user" option will fail.
Options
The full set of options used by an invocation of mount is determined by first extracting the options for the file system from
the fstab table, then applying any options specified by the -o argument, and finally applying a -r or -w option, when present.
Options available for the mount command:
-V
Output version.
-h
Print a help message.
-v
Verbose mode.
-a
Mount all filesystems (of the given types) mentioned in fstab.
-F
(Used in conjunction with -a.) Fork off a new incarnation of mount for each device. This will do the mounts on
different devices or different NFS servers in parallel. This has the advantage that it is faster; also NFS timeouts go in
parallel. A disadvantage is that the mounts are done in undefined order. Thus, you cannot use this option if you want
to mount both /usr and /usr/spool.
-f
Causes everything to be done except for the actual system call; if it's not obvious, this ''fakes'' mounting the file
system. This option is useful in conjunction with the -v flag to determine what the mount command is trying to do.
It can also be used to add entries for devices that were mounted earlier with the -n option.
-i
Don't call the /sbin/mount.<filesystem> helper even if it exists.
-l
Add the ext2, ext3 and XFS labels in the mount output. Mount must have permission to read the disk device (e.g. be
suid root) for this to work. One can set such a label for ext2 or ext3 using the e2label(8) utility, or for XFS using
xfs_admin(8), or for reiserfs using reiserfstune(8).
-n
Mount without writing in /etc/mtab. This is necessary for example when /etc is on a read-only file system.
-pnum
In case of a loop mount with encryption, read the passphrase from file descriptor num instead of from the terminal.
-s
Tolerate sloppy mount options rather than failing. This will ignore mount options not supported by a filesystem type.
Not all filesystems support this option. This option exists for support of the Linux autofs-based automounter.
mohsin Sheikh
Page 36
-r
Mount the file system read-only. A synonym is -o ro.
-w
Mount the file system read/write. This is the default. A synonym is -o rw.
-L label
Mount the partition that has the specified label.
-U uuid
Mount the partition that has the specified uuid. These two options require the file /proc/partitions (present since
Linux 2.1.116) to exist.
-t vfstype
The argument following the -t is used to indicate the file system type. The file system types which are currently
supported include: adfs, affs, autofs, cifs, coda, coherent, cramfs, debugfs, devpts, efs, ext, ext2, ext3, hfs, hpfs,
iso9660, jfs, minix, msdos, ncpfs, nfs, nfs4, ntfs, proc, qnx4, ramfs, reiserfs, romfs, smbfs, sysv, tmpfs, udf, ufs,
umsdos, usbfs, vfat, xenix, xfs, xiafs. Note that coherent, sysv and xenix are equivalent and that xenix and coherent
will be removed at some point in the future -- use sysv instead. Since kernel version 2.1.21 the types ext and xiafs do
not exist anymore. Earlier, usbfs was known as usbdevfs.
For most types all the mount program has to do is issue a simple mount(2) system call, and no detailed knowledge
of the filesystem type is required. For a few types however (like nfs, nfs4, cifs, smbfs, ncpfs) ad hoc code is
necessary. The nfs ad hoc code is built in, but cifs, smbfs, and ncpfs have a separate mount program. In order to
make it possible to treat all types in a uniform way, mount will execute the program /sbin/mount.TYPE (if that
exists) when called with type TYPE. Since various versions of the smbmount program have different calling
conventions, /sbin/mount.smbfs may have to be a shell script that sets up the desired call.
If no -t option is given, or if the auto type is specified, mount will try to guess the desired type. If mount was
compiled with the blkid library, the guessing is done by this library. Otherwise, mount guesses itself by probing the
superblock; if that does not turn up anything that looks familiar, mount will try to read the file /etc/filesystems, or, if
that does not exist, /proc/filesystems. All of the filesystem types listed there will be tried, except for those that are
labeled "nodev" (e.g., devpts, proc, nfs, and nfs4). If /etc/filesystems ends in a line with a single * only, mount will
read /proc/filesystems afterwards.
The auto type may be useful for user-mounted floppies. Creating a file /etc/filesystems can be useful to change the
probe order (e.g., to try vfat before msdos or ext3 before ext2) or if you use a kernel module autoloader. Warning:
the probing uses a heuristic (the presence of appropriate 'magic'), and could recognize the wrong filesystem type,
possibly with catastrophic consequences. If your data is valuable, don't ask mount to guess.
More than one type may be specified in a comma separated list. The list of file system types can be prefixed with no
to specify the file system types on which no action should be taken. (This can be meaningful with the -a option.)
For example, the command:
mount -a -t nomsdos,ext mounts all file systems except those of type msdos and ext.
-O
Used in conjunction with -a, to limit the set of filesystems to which the -a is applied. Like -t in this regard except
that it is useless except in the context of -a. For example, the command:
mount -a -O no_netdev mounts all file systems except those which have the option _netdev specified in the options field in
the /etc/fstab file.
It is different from -t in that each option is matched exactly; a leading no at the beginning of one option does not negate the
rest.
The -t and -O options are cumulative in effect; that is, the command
mount -a -t ext2 -O _netdev
mounts all ext2 filesystems with the _netdev option, not all filesystems that are either ext2 or have the _netdev option
specified.
-o
mohsin Sheikh
Page 37
Options are specified with a -o flag followed by a comma separated string of options. Some of these options are only
useful when they appear in the /etc/fstab file. The following options apply to any file system that is being mounted
(but not every file system actually honors them - e.g., the sync option today has effect only for ext2, ext3, fat, vfat
and ufs):
async
All I/O to the file system should be done asynchronously.
atime
Update inode access time for each access. This is the default.
auto
Can be mounted with the -a option.
defaults
Use default options: rw, suid, dev, exec, auto, nouser, and async.
dev
Interpret character or block special devices on the file system.
exec
Permit execution of binaries.
group
Allow an ordinary (i.e., non-root) user to mount the file system if one of his groups matches the group of the device.
This option implies the options nosuid and nodev (unless overridden by subsequent options, as in the option line
group,dev,suid).
mand
Allow mandatory locks on this filesystem. See fcntl(2).
_netdev
The filesystem resides on a device that requires network access (used to prevent the system from attempting to
mount these filesystems until the network has been enabled on the system).
noatime
Do not update inode access times on this file system (e.g, for faster access on the news spool to speed up news
servers).
nodiratime
Do not update directory inode access times on this filesystem.
noauto
Can only be mounted explicitly (i.e., the -a option will not cause the file system to be mounted).
nodev
Do not interpret character or block special devices on the file system.
noexec
Do not allow direct execution of any binaries on the mounted file system. (Until recently it was possible to run
binaries anyway using a command like /lib/ld*.so /mnt/binary. This trick fails since Linux 2.4.25 / 2.6.0.)
nomand
Do not allow mandatory locks on this filesystem.
nosuid
Do not allow set-user-identifier or set-group-identifier bits to take effect. (This seems safe, but is in fact rather
unsafe if you have suidperl(1) installed.)
nouser
Forbid an ordinary (i.e., non-root) user to mount the file system. This is the default.
owner
Allow an ordinary (i.e., non-root) user to mount the file system if he is the owner of the device. This option implies
the options nosuid and nodev (unless overridden by subsequent options, as in the option line owner,dev,suid).
remount
Attempt to remount an already-mounted file system. This is commonly used to change the mount flags for a file
system, especially to make a readonly file system writeable. It does not change device or mount point.
ro
Mount the file system read-only.
rw
Mount the file system read-write.
suid
Allow set-user-identifier or set-group-identifier bits to take effect.
sync
All I/O to the file system should be done synchronously. In case of media with limited number of write cycles (e.g.
some flash drives) "sync" may cause life-cycle shortening.
mohsin Sheikh
Page 38
dirsync
All directory updates within the file system should be done synchronously. This affects the following system calls:
creat, link, unlink, symlink, mkdir, rmdir, mknod and rename.
user
Allow an ordinary user to mount the file system. The name of the mounting user is written to mtab so that he can
unmount the file system again. This option implies the options noexec, nosuid, and nodev (unless overridden by
subsequent options, as in the option line user,exec,dev,suid).
users
Allow every user to mount and unmount the file system. This option implies the options noexec, nosuid, and nodev
(unless overridden by subsequent options, as in the option line users,exec,dev,suid).
context=context, fscontext=context and defcontext=context
The context= option is useful when mounting filesystems that do not support extended attributes, such as a floppy
or hard disk formatted with VFAT, or systems that are not normally running under SELinux, such as an ext3
formatted disk from a non-SELinux workstation. You can also use context= on filesystems you do not trust, such as
a floppy. It also helps in compatibility with xattr-supporting filesystems on earlier 2.4.<x> kernel versions. Even
where xattrs are supported, you can save time not having to label every file by assigning the entire disk one security
context.
A commonly used option for removable media is context=system_u:object_r:removable_t.
Two other options are fscontext= and defcontext=, both of which are mutually exclusive of the context option. This
means you can use fscontext and defcontext with each other, but neither can be used with context.
The fscontext= option works for all filesystems, regardless of their xattr support. The fscontext option sets the
overarching filesystem label to a specific security context. This filesystem label is separate from the individual
labels on the files. It represents the entire filesystem for certain kinds of permission checks, such as during mount or
file creation. Individual file labels are still obtained from the xattrs on the files themselves. The context option
actually sets the aggregate context that fscontext provides, in addition to supplying the same label for individual
files.
You can set the default security context for unlabeled files using defcontext= option. This overrides the value set for
unlabeled files in the policy and requires a file system that supports xattr labeling.
For more details see selinux(8)
--bind
Remount a subtree somewhere else (so that its contents are available in both places). See above.
--move
Move a subtree to some other place. See above.
Filesystem Specific Mount Options
The following options apply only to certain file systems. We sort them by file system. They all follow the -o flag.
What options are supported depends a bit on the running kernel. More info may be found in the kernel source subdirectory
Documentation/filesystems.
Mount options for fat
(Note: fat is not a separate filesystem, but a common part of the msdos, umsdos and vfat filesystems.)
blocksize=512 / blocksize=1024 / blocksize=2048
Set blocksize (default 512).
uid=value and gid=value
Set the owner and group of all files. (Default: the uid and gid of the current process.)
umask=value
mohsin Sheikh
Page 39
Set the umask (the bitmask of the permissions that are not present). The default is the umask of the current process.
The value is given in octal.
dmask=value
Set the umask applied to directories only. The default is the umask of the current process. The value is given in
octal.
fmask=value
Set the umask applied to regular files only. The default is the umask of the current process. The value is given in
octal.
check=value
Three different levels of pickyness can be chosen:
r[elaxed]
Upper and lower case are accepted and equivalent, long name parts are truncated (e.g. verylongname.foobar
becomes verylong.foo), leading and embedded spaces are accepted in each name part (name and extension).
n[ormal]
Like "relaxed", but many special characters (*, ?, <, spaces, etc.) are rejected. This is the default.
s[trict]
Like "normal", but names may not contain long parts and special characters that are sometimes used on Linux, but
are not accepted by MS-DOS are rejected. (+, =, spaces, etc.)
codepage=value
Sets the codepage for converting to shortname characters on FAT and VFAT filesystems. By default, codepage 437
is used.
conv=b[inary] / conv=t[ext] / conv=a[uto]
The fat file system can perform CRLF<-->NL (MS-DOS text format to UNIX text format) conversion in the kernel.
The following conversion modes are available:
binary
no translation is performed. This is the default.
text
CRLF<-->NL translation is performed on all files.
auto
CRLF<-->NL translation is performed on all files that don't have a "well-known binary" extension. The list of
known extensions can be found at the beginning of fs/fat/misc.c (as of 2.0, the list is: exe, com, bin, app, sys, drv,
ovl, ovr, obj, lib, dll, pif, arc, zip, lha, lzh, zoo, tar, z, arj, tz, taz, tzp, tpz, gz, tgz, deb, gif, bmp, tif, gl, jpg, pcx, tfm,
vf, gf, pk, pxl, dvi).
Programs that do computed lseeks won't like in-kernel text conversion. Several people have had their data ruined by this
translation. Beware!
For file systems mounted in binary mode, a conversion tool (fromdos/todos) is available.
cvf_format=module
Forces the driver to use the CVF (Compressed Volume File) module cvf_module instead of auto-detection. If the
kernel supports kmod, the cvf_format=xxx option also controls on-demand CVF module loading.
cvf_option=option
Option passed to the CVF module.
debug
Turn on the debug flag. A version string and a list of file system parameters will be printed (these data are also
printed if the parameters appear to be inconsistent).
fat=12 / fat=16 / fat=32
Specify a 12, 16 or 32 bit fat. This overrides the automatic FAT type detection routine. Use with caution!
iocharset=value
Character set to use for converting between 8 bit characters and 16 bit Unicode characters. The default is iso8859-1.
Long filenames are stored on disk in Unicode format.
quiet
Turn on the quiet flag. Attempts to chown or chmod files do not return errors, although they fail. Use with caution!
sys_immutable, showexec, dots, nodots, dotsOK=[yes|no]
Various misguided attempts to force Unix or DOS conventions onto a FAT file system.
mohsin Sheikh
Page 40
Mount options for nfs
Instead of a textual option string, parsed by the kernel, the nfs file system expects a binary argument of type struct
nfs_mount_data. The program mount itself parses the following options of the form 'tag=value', and puts them in the
structure mentioned: rsize=n, wsize=n, timeo=n, retrans=n, acregmin=n, acregmax=n, acdirmin=n, acdirmax=n,
actimeo=n, retry=n, port=n, mountport=n, mounthost=name, mountprog=n, mountvers=n, nfsprog=n, nfsvers=n,
namlen=n. The option addr=n is accepted but ignored. Also the following Boolean options, possibly preceded by no are
recognized: bg, fg, soft, hard, intr, posix, cto, ac, tcp, udp, lock. For details, see nfs(5).
Especially useful options include
rsize=32768,wsize=32768
This causes the NFS client to try to negotiate a buffer size up to the size specified. A large buffer size does improve
performance, but both the server and client have to support it. In the case where one of these does not support the
size specified, the size negotiated will be the largest that both support.
intr
This will allow NFS operations (on hard mounts) to be interrupted while waiting for a response from the server.
nolock
Do not use locking. Do not start lockd.
Mount options for ntfs
iocharset=name
Character set to use when returning file names. Unlike VFAT, NTFS suppresses names that contain unconvertible
characters. Deprecated.
nls=name
New name for the option earlier called iocharset.
utf8
Use UTF-8 for converting file names.
uni_xlate=[0|1|2]
For 0 (or 'no' or 'false'), do not use escape sequences for unknown Unicode characters. For 1 (or 'yes' or 'true') or 2,
use vfat-style 4-byte escape sequences starting with ":". Here 2 give a little-endian encoding and 1 a byteswapped
bigendian encoding.
posix=[0|1]
If enabled (posix=1), the file system distinguishes between upper and lower case. The 8.3 alias names are presented
as hard links instead of being suppressed.
uid=value, gid=value and umask=value
Set the file permission on the filesystem. The umask value is given in octal. By default, the files are owned by root
and not readable by somebody else.
the Loop Device
One further possible type is a mount via the loop device. For example, the command
mount /tmp/fdimage /mnt -t msdos -o loop=/dev/loop3,blocksize=1024
will set up the loop device /dev/loop3 to correspond to the file /tmp/fdimage, and then mount this device on /mnt.
This type of mount knows about three options, namely loop, offset and encryption, that are really options to losetup(8).
(These options can be used in addition to those specific to the filesystem type.)
If no explicit loop device is mentioned (but just an option '-o loop' is given), then mount will try to find some unused loop
device and use that. If you are not so unwise as to make /etc/mtab a symbolic link to /proc/mounts then any loop device
allocated by mount will be freed by umount. You can also free a loop device by hand, using 'losetup -d', see losetup(8).
mohsin Sheikh
Page 41
Return Codes
mount has the following return codes (the bits can be ORed):
1.
2.
3.
4.
5.
6.
7.
8.
success
incorrect invocation or permissions
system error (out of memory, cannot fork, no more loop devices)
internal mount bug or missing nfs support in mount
user interrupt
problems writing or locking /etc/mtab
mount failure
some mount succeeded
Files
/etc/fstab
file system table
/etc/mtab
table of mounted file systems
/etc/mtab~
lock file
/etc/mtab.tmp
temporary file
/etc/filesystems
a list of filesystem types to try
Bugs
It is possible for a corrupted file system to cause a crash.
Some Linux file systems don't support -o sync and -o dirsync (the ext2, ext3, fat and vfat file systems do support
synchronous updates (a la BSD) when mounted with the sync option).
The -o remount may not be able to change mount parameters (all ext2fs-specific parameters, except sb, are changeable with
a remount, for example, but you can't change gid or umask for the fatfs).
Mount by label or uuid will work only if your devices have the names listed in /proc/partitions. In particular, it may well fail
if the kernel was compiled with devfs but devfs is not mounted.
It is possible that files /etc/mtab and /proc/mounts don't match. The first file is based only on the mount command options,
but the content of the second file also depends on the kernel and others settings (e.g. remote NFS server. In particular case the
mount command may reports unreliable information about a NFS mount point and the /proc/mounts file usually contains
more reliable information.)
Checking files on NFS filesystem referenced by file descriptors (i.e. the fcntl and ioctl families of functions) may lead to
inconsistent result due to the lack of consistency check in kernel even if noac is used.
Helpful Files
The following files may be useful when trying to write your PVM programs in this class.
The online UNIX Dictionary of over 40,000 words:
/usr/dict/words The UNIX dictionary
mohsin Sheikh
Page 42
Some useful system files in the directory /etc or /usr/games/lib/fortune:
/etc/passwd The password file
/etc/HOSTNAME The name of the computer
/etc/issue The logon banner
/usr/games/lib/fortunes/fortune The source for UNIX fortunes
mohsin Sheikh
Page 43
Chapter 5
Useful vi commands
Each command needs to be preceded by pressing the escape key!
i
<esc>
a
o
O
<shift>g
r
x
dd
yy
p
P
:wq
:wq!
:w!
:q
:q!
/
insert mode.
leave insert mode and go into command mode.
append characters to the end of the line.
open a line below your cursor.
open a line above.
go to the bottom of the file.
replace the letter that you are on with the one you type next.
erase the character that you are on.
delete the line that you are on. A number before dd deletes that number of lines.
copy the line you are on. A number before yy copies that number of lines.
paste the line you are on below you.
paste the line you are on above you.
write and quit the file that you are editing.
write and quit the file that you are editing, even if it is designated as read only!
write to a read only file.
quit.
discard any editing and quit.
this takes you to the bottom of the window where you can type a string and return to perform a search in the file.
(The character ! is often referred to as pling)
You can use vedit which is vi with more user friendly additions and also ed, or emacs.
The * wildcard
The character * is called a wildcard, and will match against none or more character(s) in a file (or directory) name. For
example, in your unixstuff directory, type
% ls list*
This will list all files in the current directory starting with list....
Try typing
% ls *list
This will list all files in the current directory ending with ....list
The ? wildcard
The character ? will match exactly one character.
So ?ouse will match files like house and mouse, but not grouse.
Try typing % ls ?list
mohsin Sheikh
Page 44
Filename conventions
We should note here that a directory is merely a special type of file. So the rules and conventions for naming files apply also
to directories.
In naming files, characters with special meanings such as / * & % , should be avoided. Also, avoid using spaces within
names. The safest way to name a file is to use only alphanumeric characters, that is, letters and numbers, together with _
(underscore) and . (dot).
Good filenames
Bad filenames
project.txt
project
my_big_program.c my big program.c
fred_dave.doc
fred & dave.doc
File names conventionally start with a lower-case letter, and may end with a dot followed by a group of letters indicating the
contents of the file. For example, all files consisting of C code may be named with the ending .c, for example, prog1.c . Then
in order to list all files containing C code in your home directory, you need only type ls *.c in that directory.
Getting Help
On-line Manuals
There are on-line manuals which gives information about most commands. The manual pages tell you which options a
particular command can take, and how each option modifies the behaviour of the command. Type man command to read the
manual page for a particular command.
For example, to find out more about the wc (word count) command, type
% man wc
Alternatively
% whatis wc
gives a one-line description of the command, but omits any information about options etc.
Apropos
When you are not sure of the exact name of a command,
% apropos keyword
will give you the commands with keyword in their manual page header. For example, try typing
% apropos copy
quota
All students are allocated a certain amount of disk space on the file system for their personal files, usually about 100Mb. If
you go over your quota, you are given 7 days to remove excess files.
mohsin Sheikh
Page 45
To check your current quota and how much of it you have used, type
% quota -v
df
The df command reports on the space left on the file system. For example, to find out how much space is left on the
fileserver, type
% df .
du
The du command outputs the number of kilobyes used by each subdirectory. Useful if you have gone over quota and you
want to find out which directory has the most files. In your home-directory, type
% du -s *
The -s flag will display only a summary (total size) and the * means all files and directories.
gzip
This reduces the size of a file, thus freeing valuable disk space. For example, type
% ls -l science.txt
and note the size of the file using ls -l . Then to compress science.txt, type
% gzip science.txt
This will compress the file and place it in a file called science.txt.gz
To see the change in size, type ls -l again.
To expand the file, use the gunzip command.
% gunzip science.txt.gz
zcat
zcat will read gzipped files without needing to uncompress them first.
% zcat science.txt.gz
If the text scrolls too fast for you, pipe the output though less .
% zcat science.txt.gz | less
file
file classifies the named files according to the type of data they contain, for example ascii (text), pictures, compressed data,
etc.. To report on all files in your home directory, type
mohsin Sheikh
Page 46
% file *
diff
This command compares the contents of two files and displays the differences. Suppose you have a file called file1 and you
edit some part of it and save it as file2. To see the differences type
% diff file1 file2
Lines beginning with a < denotes file1, while lines beginning with a > denotes file2.
find
This searches through the directories for files and directories with a given name, date, size, or any other attribute you care to
specify. It is a simple command but with many options - you can read the manual by typing man find.
To search for all fies with the extention .txt, starting at the current directory (.) and working through all sub-directories, then
printing the name of the file to the screen, type
% find . -name "*.txt" -print
To find files over 1Mb in size, and display the result as a long listing, type
% find . -size +1M -ls
history
The C shell keeps an ordered list of all the commands that you have entered. Each command is given a number according to
the order it was entered.
% history (show command history list)
If you are using the C shell, you can use the exclamation character (!) to recall commands easily.
% !! (recall last command)
% !-3 (recall third most recent command)
% !5 (recall 5th command in list)
% !grep (recall last command starting with grep)
You can increase the size of the history buffer by typing % set history=100
mohsin Sheikh
Page 47
Chapter 6
Comparison Unix/Dos
DOS Command
DIR
UNIX or Bash Command
Action
ls -l (or use ls -lF)(-a all files)
(df -k Space remaining on
filesystem)
List directory contents
ls -tr
ls -ls
ls -R
ls -a
List directory contents by reverse time of
modification/creation.
List files and size
List directory/sub-directory contents recursively.
List hidden files.
TREE
ls -R
List directory recursivly
CD
cd
Change directory
MKDIR
MD
mkdir
Make a new directory
ASSIGN
ln
Create a file or directory link
RMDIR
RD
rmdir
Remove a directory
CHDIR
pwd
Display directory location
DEL
ERASE
rm -iv
Remove a file
RMDIR /S (NT)
DELTREE (Win 95...)
rm -R
Remove all directories and files below given directory
COPY
cp -piv
Copy a file
XCOPY
cp -R
Copy all file of directory recursivly
RENAME or MOVE
mv -iv
Rename/move a file
TYPE
cat
Dump contents of a file to users screen
MORE
more
Pipe output a single page at a time
HELP or COMMAND /?
man
Online manuals
CLS
clear
ctrl-l
Clear screen
EXIT
EXIT0
exit
exit 0
Exit a shell
FIND
FINDSTR
grep
Look for a word in files given in command line
COMP
diff
Compare two files and show differences. Also see comm, cmp,
mgdiff and tkdiff.
FC
diff
Compare two files and show differences. Also see comm, cmp,
mgdiff and tkdiff.
SET
set and env
List all environment variables
SET variable=value
echo %variable%
set
Set environment variables
Show environment variables
DIR *.* /o-d
DIR *.* /v /os
DIR /s
DIR /aa
export variable=value
echo $variable
ECHO text
echo text
Echo text to screen
mohsin Sheikh
Page 48
SET variable
setenv (for C shell) or export
VAR=val (for Korn shell. Also
VAR=val)
Set environment variables
PATH
PATH %PATH%;C:\DIR
echo $PATH
PATH=$PATH:/dir
Display search path for executables.
Set PATH environment variable.
PROMPT $p$g
export PS1='\h(\u)\W> '
Set user command prompt.
DATE or TIME
date
Show date. (also set date - DOS only)
DOSKEY /h
history
List command history
DOSKEY
NAME=command
alias NAME=command
Set command alias
BREAK ON
trap
Trap ctrl-break / Trap signals.
SORT
sort
Sort data alphabetically/numerically
EDLIN
ed
Line mode editor
pico, gnp, vi, xedit, xemacs,dtpad
Edit a file. The Linux editor which looks most like DOS edit is
probably Pico. (Not a recomendation!)
tar -cvf /dev/fd0 files
mdir, mcopy
doswrite -a file (AIX only)
Save files to floppy.
See Using DOS floppies
RESTORE A:\ files
tar -xvf /dev/fd0 files
mdir, mcopy
dosread -a file (AIX only)
Read files from floppy.
See Using DOS floppies
ATTRIB [+r|-r] [+a|-a]
[+s|-s] [path\file] /s
chmod
Change file permissions. DOS: +:set to -:remove r:Read only
a:Archive s:System /s:recursively
ATTRIB +h or -h
mv file .file
Change file to a hidden file - rename file with prefix "."
PRINT
lpr
Print a file
CALL
COMMAND /C (DOS),
CMD (NT)
source script (cshrc)
. script (bash)
sh script
Execute script from within batch shell.
MEM
free
top
Show free memory on system
EDIT filename.txt
BACKUP files A:\
TASKLIST (WIN2K, XP) ps -aux
top
List executable name, process ID number and memory usage
of active processes
MSD
lsdev
Show system info (Command borrowed from AIX)
SCANDISK
DEFRAG C:
fsck
debugfs
Check and repair hard drive file system
CHDISK
du -s
Disk usage.
FDISK
fdisk
Tool to partition a hard drive.
SUBST V:
C:\directory\path
mount
Mount a drive letter to a folder/directory on your hard drive.
mke2fs
See: fdformat and mformat for
floppies
Format drive file system.
For floppy drive use see YoLinux Tutorial Using DOS
Floppies with Linux
uname -a
echo $SHELL
cat /etc/issue
Operating system/shell version
tar and zip
Compress and uncompress files/directories. Use tar to create
compilation of a directory before compressing. Linux also has
compress, gzip
FORMAT
VER
pkzip
mohsin Sheikh
Page 49
HOSTNAME
hostname
Print host name of computer
PING
ping
Send packets to a network host
TRACERT
traceroute
Show routes and router hops to given network destination.
IPCONFIG (NT)
WINIPCFG (Win 95...)
ifconfig
Display/configure network interface
NBTSTAT (Netbios info: - nslookup host-name
n, -c)
host host-name
NBTSTAT -A IP-address
Print DNS info for host.
NBTSTAT -a hostname
nmblookup -A hostname
lookup NetBIOS names.
ROUTE PRINT
route -n
Print routing table.
NET HELP START
chkconfig --list |grep on
List services.
NET STARTservice-name service service-name start
NET STOPservice-name service service-name stop
Start/stop service/daemon.
NET SHARES
Show mounted shares/filesystems.
df
smbclient -M MS-Windows-hostNET SEND <node-name>
name
<message> (NT)
talk
Send pop-up to a MS/Windows PC
Send message to another Unix/Linux user. See YoLinux
tutorial
WIN
startx
Start X-Windows.
REBOOT
shutdown -r now
Reboot system.
To find out how to do something on UNIX simply type "man -k subject_matter". This will do a key word search for all
commands dealing with the subject matter. Then use the appropriate command. Online manuals are available on all the
commands by typing "man command_name".
MS/Windows info:
Shell Descriptor/Operators:
DOS
Descriptor/Operator
UNIX or Bash
Descriptor/Operator
Description
\
/
Directory path delimiter
.\
./
Current directory
..\
../
Parent directory
ctrl-z
ctrl-d
End of file/close shell
ctrl-c
ctrl-c
Interrupt/process break
*
*
file name wild card
?
?
Single character wild card
%VAR%
$VAR
Variable prefix
%1 %2 %3
$1 $2 $3
First, second and third shell command line
arguments.
/
-
Command line option flag prefix
|
|
Pipe
>
>
stdout redirection
>>
>>
stdout redirection overwrite
<
<
stdin redirection
mohsin Sheikh
Page 50
Shell Script Operators:
DOS Operator
UNIX or Bash Operator
Description
@
ECHO OFF
set +v
Set verbose mode off. -v: Echo each line of shell script as it is
executed.
%
$
command line argument prefix. DOS: %1 Bash: $1 for firs
argument.
REM
#
Comment. (Not processed.)
==
=
string "equal to" comparison
!==!
!=
string "not equal to" comparison
NOT
!
negative of test expression
CHOICE
case
case/switch statement
IF
if [[ test-resulting-in-bool if-test
]];
then
If file exists
...
elif ...;
If file does not exist.
then
...
else
...
fi
IF EXIST C:\filename
IF NOT EXIST
C:\filename
if [ -e /dir/filename ];
then
if [ ! -e /dir/filename ];
then
GOTO ABC
...
:ABC
goto ABC
...
:ABC
Branch
FOR ... IN ... DO
for ffiillee in lliisstt;
do ...;
done
For loop
FOR %%fff IN
(C:\dir\*.*)
DO echo %%fff
for (( expr1; expr2;
expr3; ))
do ...;
done
ERRORLEVEL
$?
exit status/return code
PAUSE
sleep
sleep for specified interval
mohsin Sheikh
Page 51
Part-III
mohsin Sheikh
Page 52
Chapter 7
Compiling UNIX software packages
We have many public domain and commercial software packages installed on our systems, which are available to all users.
However, students are allowed to download and install small software packages in their own home directory, software
usually only useful to them personally.
There are a number of steps needed to install the software.
Locate and download the source code (which is usually compressed)
Unpack the source code
Compile the code
Install the resulting executable
Set paths to the installation directory
Of the above steps, probably the most difficult is the compilation stage.
Compiling Source Code
All high-level language code must be converted into a form the computer understands. For example, C language source code
is converted into a lower-level language called assembly language. The assembly language code made by the previous stage
is then converted into object code which are fragments of code which the computer understands directly. The final stage in
compiling a program involves linking the object code to code libraries which contain certain built-in functions. This final
stage produces an executable program.
To do all these steps by hand is complicated and beyond the capability of the ordinary user. A number of utilities and tools
have been developed for programmers and end-users to simplify these steps.
make and the Makefile
The make command allows programmers to manage large programs or groups of programs. It aids in developing large
programs by keeping track of which portions of the entire program have been changed, compiling only those parts of the
program which have changed since the last compile.
The make program gets its set of compile rules from a text file called Makefile which resides in the same directory as the
source files. It contains information on how to compile the software, e.g. the optimisation level, whether to include
debugging info in the executable. It also contains information on where to install the finished compiled binaries
(executables), manual pages, data files, dependent library files, configuration files, etc.
Some packages require you to edit the Makefile by hand to set the final installation directory and any other parameters.
However, many packages are now being distributed with the GNU configure utility.
configure
As the number of UNIX variants increased, it became harder to write programs which could run on all variants. Developers
frequently did not have access to every system, and the characteristics of some systems changed from version to version. The
GNU configure and build system simplifies the building of programs distributed as source code. All programs are built using
a simple, standardised, two step process. The program builder need not install any special tools in order to build the program.
The configure shell script attempts to guess correct values for various system-dependent variables used during compilation. It
uses those values to create a Makefile in each directory of the package.
The simplest way to compile a package is:
mohsin Sheikh
1.
2.
3.
4.
5.
6.
Page 53
cd to the directory containing the package's source code.
Type ./configure to configure the package for your system.
Type make to compile the package.
Optionally, type make check to run any self-tests that come with the package.
Type make install to install the programs and any data files and documentation.
Optionally, type make clean to remove the program binaries and object files from the source code directory
The configure utility supports a wide variety of options. You can usually use the --help option to get a list of interesting
options for a particular configure script.
The only generic options you are likely to use are the --prefix and --exec-prefix options. These options are used to specify
the installation directories.
The directory named by the --prefix option will hold machine independent files such as documentation, data and
configuration files.
The directory named by the --exec-prefix option, (which is normally a subdirectory of the --prefix directory), will hold
machine dependent files such as executables.
7.2 Downloading source code
For this example, we will download a piece of free software that converts between different units of measurements.
First create a download directory
% mkdir download
7.3 Extracting the source code
Go into your download directory and list the contents.
% cd download
% ls -l
As you can see, the filename ends in tar.gz. The tar command turns several files and directories into one single tar file. This is
then compressed using the gzip command (to create a tar.gz file).
First unzip the file using the gunzip command. This will create a .tar file.
% gunzip units-1.74.tar.gz
Then extract the contents of the tar file.
% tar -xvf units-1.74.tar
Again, list the contents of the download directory, then go to the units-1.74 sub-directory.
% cd units-1.74
7.4 Configuring and creating the Makefile
The first thing to do is carefully read the README and INSTALL text files (use the less command). These contain
important information on how to compile and run the software.
mohsin Sheikh
Page 54
The units package uses the GNU configure system to compile the source code. We will need to specify the installation
directory, since the default will be the main system area which you will not have write permissions for. We need to create an
install directory in your home directory.
% mkdir ~/units174
Then run the configure utility setting the installation path to this.
% ./configure --prefix=$HOME/units174
NOTE: The $HOME variable is an example of an environment variable. The value of $HOME is the path to your home
directory. Just type
% echo $HOME
to show the contents of this variable. We will learn more about environment variables in a later chapter.
If configure has run correctly, it will have created a Makefile with all necessary options. You can view the Makefile if you
wish (use the less command), but do not edit the contents of this.
7.5 Building the package
Now you can go ahead and build the package by running the make command.
% make
After a minute or two (depending on the speed of the computer), the executables will be created. You can check to see
everything compiled successfully by typing
% make check
If everything is okay, you can now install the package.
% make install
This will install the files into the ~/units174 directory you created earlier.
7.6 Running the software
You are now ready to run the software (assuming everything worked).
% cd ~/units174
If you list the contents of the units directory, you will see a number of subdirectories.
bin
The binary executables
info
GNU info formatted documentation
man
Man pages
share Shared data files
To run the program, change to the bin directory and type
mohsin Sheikh
Page 55
% ./units
As an example, convert 6 feet to metres.
You have: 6 feet
You want: metres
* 1.8288
If you get the answer 1.8288, congratulations, it worked.
To view what units it can convert between, view the data file in the share directory (the list is quite comprehensive).
To read the full documentation, change into the info directory and type
% info --file=units.info
7.7 Stripping unnecessary code
When a piece of software is being developed, it is useful for the programmer to include debugging information into the
resulting executable. This way, if there are problems encountered when running the executable, the programmer can load the
executable into a debugging software package and track down any software bugs.
This is useful for the programmer, but unnecessary for the user. We can assume that the package, once finished and available
for download has already been tested and debugged. However, when we compiled the software above, debugging
information was still compiled into the final executable. Since it is unlikey that we are going to need this debugging
information, we can strip it out of the final executable. One of the advantages of this is a much smaller executable, which
should run slightly faster.
What we are going to do is look at the before and after size of the binary file. First change into the bin directory of the units
installation directory.
% cd ~/units174/bin
% ls -l
As you can see, the file is over 100 kbytes in size. You can get more information on the type of file by using the file
command.
% file units
units: ELF 32-bit LSB executable, Intel 80386, version 1, dynamically linked (uses shared libs), not stripped
To strip all the debug and line numbering information out of the binary file, use the strip command
% strip units
% ls -l
As you can see, the file is now 36 kbytes - a third of its original size. Two thirds of the binary file was debug code!!!
Check the file information again.
% file units
units: ELF 32-bit LSB executable, Intel 80386, version 1, dynamically linked (uses shared libs), stripped
mohsin Sheikh
Page 56
Sometimes you can use the make command to install pre-stripped copies of all the binary files when you install the package.
Instead of typing make install, simply type make install-strip
mohsin Sheikh
Page 57
Chapter 9
UNIX Variables
Variables are a way of passing information from the shell to programs when you run them. Programs look "in the
environment" for particular variables and if they are found will use the values stored. Some are set by the system, others by
you, yet others by the shell, or any program that loads another program.
Standard UNIX variables are split into two categories, environment variables and shell variables. In broad terms, shell
variables apply only to the current instance of the shell and are used to set short-term working conditions; environment
variables have a farther reaching significance, and those set at login are valid for the duration of the session. By convention,
environment variables have UPPER CASE and shell variables have lower case names.
Environment Variables
An example of an environment variable is the OSTYPE variable. The value of this is the current operating system you are
using. Type
% echo $OSTYPE
More examples of environment variables are
USER (your login name)
HOME (the path name of your home directory)
HOST (the name of the computer you are using)
ARCH (the architecture of the computers processor)
DISPLAY (the name of the computer screen to display X windows)
PRINTER (the default printer to send print jobs)
PATH (the directories the shell should search to find a command)
Finding out the current values of these variables.
ENVIRONMENT variables are set using the setenv command, displayed using the printenv or env commands, and unset
using the unsetenv command.
To show all values of these variables, type
% printenv | less
Shell Variables
An example of a shell variable is the history variable. The value of this is how many shell commands to save, allow the user
to scroll back through all the commands they have previously entered. Type
% echo $history
More examples of shell variables are
cwd (your current working directory)
home (the path name of your home directory)
path (the directories the shell should search to find a command)
prompt (the text string used to prompt for interactive commands shell your login shell)
mohsin Sheikh
Page 58
Finding out the current values of these variables.
SHELL variables are both set and displayed using the set command. They can be unset by using the unset command.
To show all values of these variables, type
% set | less
So what is the difference between PATH and path ?
In general, environment and shell variables that have the same name (apart from the case) are distinct and independent,
except for possibly having the same initial values. There are, however, exceptions.
Each time the shell variables home, user and term are changed, the corresponding environment variables HOME, USER and
TERM receive the same values. However, altering the environment variables has no effect on the corresponding shell
variables.
PATH and path specify directories to search for commands and programs. Both variables always represent the same directory
list, and altering either automatically causes the other to be changed.
Using and setting variables
Each time you login to a UNIX host, the system looks in your home directory for initialisation files. Information in these files
is used to set up your working environment. The C and TC shells uses two files called .login and .cshrc (note that both file
names begin with a dot).
At login the C shell first reads .cshrc followed by .login
.login is to set conditions which will apply to the whole session and to perform actions that are relevant only at login.
.cshrc is used to set conditions and perform actions specific to the shell and to each invocation of it.
The guidelines are to set ENVIRONMENT variables in the .login file and SHELL variables in the .cshrc file.
WARNING: NEVER put commands that run graphical displays (e.g. a web browser) in your .cshrc or .login file.
Setting shell variables in the .cshrc file
For example, to change the number of shell commands saved in the history list, you need to set the shell variable history. It is
set to 100 by default, but you can increase this if you wish.
% set history = 200
Check this has worked by typing
% echo $history
However, this has only set the variable for the lifetime of the current shell. If you open a new xterm window, it will only have
the default history value set. To PERMANENTLY set the value of history, you will need to add the set command to the
.cshrc file.
First open the .cshrc file in a text editor. An easy, user-friendly editor to use is nedit.
% nedit ~/.cshrc
mohsin Sheikh
Page 59
Add the following line AFTER the list of other commands.
set history = 200
Save the file and force the shell to reread its .cshrc file buy using the shell source command.
% source .cshrc
Check this has worked by typing
% echo $history
Setting the path
When you type a command, your path (or PATH) variable defines in which directories the shell will look to find the
command you typed. If the system returns a message saying "command: Command not found", this indicates that either the
command doesn't exist at all on the system or it is simply not in your path.
For example, to run units, you either need to directly specify the units path (~/units174/bin/units), or you need to have the
directory ~/units174/bin in your path.
You can add it to the end of your existing path (the $path represents this) by issuing the command:
% set path = ($path ~/units174/bin)
Test that this worked by trying to run units in any directory other that where units is actually located.
% cd
% units
To add this path PERMANENTLY, add the following line to your .cshrc AFTER the list of other commands.
set path = ($path ~/units174/bin)
mohsin Sheikh
Page 60
Chapter 9
Shell Script Programming Sessions
Session 1
1.
2.
3.
4.
5.
Sol:
Log in to the system
Use Vi editor to create a file called myfile.txt which contain some text.
Correct typing errors during creation
Save the file
Logout of the file
$ login: <user name>
$ password: ******
$ vi
~ Unix is Case Sensitive
~ Never leave the Computer without logging out when you are working in a time sharing or network
environments.
Type <Esc>
: wq myfile
$
Session 2
1.
2.
3.
4.
5.
6.
7.
Sol:
Log into the system
Open the file created in session 1
Add some text
Change some text
delete some text
Save the changes
Logout of the system
$ login: <user name>
$ password: ******
$ vi myfile
~ Unix is Case Sensitive
~ Never leave the Computer without logging out when you are working in a time sharing or network
environments.
~ Shell Programming
: wq
mohsin Sheikh
Page 61
Session 3 Log into the system
Use the cat command to create a file containing the following data. Call it mutable use tabs to separate the fields
1425
ravi
15.65
4320
ramu
26.27
6830
sita
36.15
1450
raju
21.86
a.
b.
c.
d.
e.
f.
g.
Sol:
use the cat command to display the file, my table
use the vi command to correct any errors in the file, my table
use the sort command to sort the file my table according to the first field. Call the sorted file my
table(same name)
print the file my table
use the cut & paste commands to swap fields 2 and 3 my table. Call it mytable(same name)
print the new file, my table
logout of the system
$ login: <user name>
$ password:******
$ cat –c1-14
1425 <tab>
ravi <tab>
15.65 <tab>
4320 <tab>
ramu <tab>
26.27 <tab>
6830 <tab>
sita <tab>
36.15 <tab>
1450 <tab>
raju <tab>
21.86 <tab>
$ cat myfile
$who|more
$ sort +0 -1 mytable
Session 4
a.
b.
c.
d.
e.
f.
log in the system
use the appropriate commands to determine ur login shell
use the /etc/passwd file to verify the result of step b.
use the who command redirect the result to a file called myfile1.Use the more command to see
the contents of myfile1.
Use the date and who commands in sequence ?(in one line) such that the output of date will
display on the screen and the output of who will be redirected to a file called my file2.Use the
more command to check the contents of myfile2.
write a sed command that deletes the first character in each line in a file
mohsin Sheikh
Page 62
g.
h.
Sol:
write a sed command that deletes the character before the last character in each line in a file.
Write a sed command that swaps the files and second words in each line in a file
$ login: <user name>
$ password:******
$ echo $SHELL
csh
$ who >| myfile1
$ more myfile1
$ date|who >myfile2
$ more myfile2
Session 5
pipe ur /etc/passwd file to awk and print out the home directory of each user.
Develop an interactive grep script that asks for a word and a file name and then tells how many lines contain that
word
Repeat
Part using awk
(d) Sol:
$ awk ‘$2 ==”Computers” && $3 >10000 {print}’Sales.dat
I/P:
O/P:
2
Session 6
1
1
Clothing
Computers
3141
9161
1
Textbooks
21312
2
Clothing 3252
2
Computers
2
Supplies 2242
2
Text books
15462
Computers
1232
1232
mohsin Sheikh
Page 63
a) Write A shell script that takes a command –line argument and reports on whether it is directry ,a file,or something
else
b) Write a shell script that accepts one or more file name as a arguments and converts all of thenm to
uppercase,provided they exits in the current directory
c) Write a shell script that determines the period for which a specified user is working on the system
(a) Sol:
echo "Enter a file name:"
read f
if [ -f $f ]
then
echo "File"
elif [ -d $f ]
then
echo "Directory"
else
echo "Not"
fi
Output:
Directory
Session 7
(a) Write a shell script that accepts a file name starting and ending line numbers as arguments and displays all
the lines between the given line numbers
(b) Write a shell script that deletes all lines containing a specified word I one or more files supplied as arguments
to it.
(a) Sol: $ awk ‘NR<2 || NR> 4 {print $0}’ 5 lines.dat
I/P:
line1
line2
line3
line4
line5
O/P:
line1
mohsin Sheikh
Page 64
line5
(b) Sol:
i=1
while [ $i -le $# ]
do
grep -v Unix $i > $i
done
Session 8
a) Write a shell script that computes the gross salary of a employee according to the following
1) if basic salary is <1500 then HRA 10% of the basic and DA =90% of the basic
2) if basic salary is >1500 then HRA 500 and DA =98% of the basic
The basic salary is entered interactively through the key board
(b)Write a shell script that accepts two integers as its arguments and computes the value of first number raised to the
power of the second number
(a)Sol:-
echo " Enter the Salary "
read sal
if [ $sal<1500] then
da=`expr $sal*90/100`
hra=`expr $sal*10/100`
gsal=’expr $sal +$hra+$da
echo “$gsal”
elif [$sal>1500]
hra=500
da=’expr $sal*98/100’
gsal=’expr $sal+$hra+$da
gross=`expr $sa + $da + $hra`
fi
fi
(b)Sol
mohsin Sheikh
Page 65
a=$1
b=$2
c=pow($a,$b)
echo”$c”
Session 9
(a) Write an interactive file handling shell program. Let it offer the user the choice of copying ,removing
,renaming or linking files. Once the use has made a choice, have the program ask the user for necessary
information, such as the file name ,new name and so on.
(b) Write a shell script that takes a login name as command –line argument and reports when that person logs in
(c) Write a shell script which receives two files names as arguments. It should check whether the two file contents
are same or not. If they are same then second file should be deleted.
PROGRAM
echo "Enter I File Name:"
read f1
echo "Enter II File Name:"
read f2
d=`cmp $f1 $f2`
d1=""
if [ $d -eq $d2 ]
then
echo "Two Files are similar and $f2 is deleted"
rm $f2
else
echo "Two Files differ each other"
fi
Session 10
(a) Write a shell script that displays a list of all files in the current directory to which the user has read write and
execute permissions
(b) Develop an interactive script that asks for a word and file name and then tells how many times that word
occurred in the file.
mohsin Sheikh
Page 66
(c) Write a shell script to perform the following string operations.
1) To extract a sub string from a given string
2) To find the length of a given string
(a) PROGRAM
# File Name : list.sh
#!/bin/bash
read -p "Enter a directory name : " dn
if [ -d $dn ]; then
printf "\nFiles in the directory $dn are :\n"
for fn in `ls $dn`
do
if [ -d $dn/$fn ]; then
printf "<$fn> Directory "
elif [ -f $dn/$fn ]
then
printf "$fn File "
fi
if [ -r $dn/$fn ]; then
printf " Read"
fi
if [ -w $dn/$fn ];then
printf " Write"
fi
if [ -x $dn/$fn ];then
printf " Execute"
fi
printf "\n"
done
else
mohsin Sheikh
Page 67
printf "\n$dn not exists or not a directory"
fi
(b) PROGRAM
# File Name : wcount.sh
#!/bin/bash
read -p "Enter a file name : " fn
if test -f $fn
then
echo "The contents of the file $fn is :"
cat $fn
echo "No. of Line
: `wc -l $fn`"
echo "No. of Words
: `wc -w $fn`"
echo "No. of Characters: `wc -c $fn`"
else
echo "$fn is not exists or not a file"
fi
(c) PROGRAM
Print “Enter the String:\c”
read strIn
strlen=${# strIn}
print the string length is : $strlen
$ strlen.scr
O/P:
Enter the String: Now is the time
The String length : 15
Session 11
mohsin Sheikh
Page 68
Write a C program that takes one or more file or directory names as command line input and reports the following
information on the file.
1.
2.
3.
4.
file type
number of links
read, write and execute permissions
time of last access
(Note: use /fstat system calls)
PROGRAM
#include<stdio.h>
main()
{
FILE *stream;
int buffer_character;
stream=fopen(“test”,”r”);
if(stream==(FILE*)0)
{
fprintf(stderr,”Error opening file(printed to standard error)\n”);
fclose(stream);
exit(1);
}
}
if(fclose(stream))==EOF)
{
fprintf(stderr,”Error closing stream.(printed to standard error)\n);
exit(1);
}
return();
}
Session 12
mohsin Sheikh
Write C program that simulate the following unix commands
(a) mv
(b) cp
/* File Name : bspace1.c */
#include<fcntl.h>
#include<unistd.h>
#include<stdio.h>
main(int argc,char *argv[])
{
FILE *fp;
char ch;
int sc=0;
fp=fopen(argv[1],"r");
if(fp==NULL)
printf("unable to open a file",argv[1]);
else
{
while(!feof(fp))
{
ch=fgetc(fp);
if(ch==' ')
sc++;
}
printf("no of spaces %d",sc);
printf("\n");
fclose(fp);
}
}
Page 69
mohsin Sheikh
Session 13
Write a c program that simulates ls command
(Use system calls /directory API)
PROGRAM:
#include<stdio.h>
#include<fcntl.h>
#include<stdlib.h>
main(int argc,char *argv[])
{
int fd,i;
char ch[1];
if (argc<2)
{ printf("Usage: mycat filename\n");
exit(0);
}
fd=open(argv[1],O_RDONLY);
if(fd==-1)
printf("%s is not exist",argv[1]);
else
{
printf("Contents of the file %s is : \n",argv[1]);
while(read(fd,ch,1)>0)
printf("%c",ch[0]);
close(fd);
}
Page 70
mohsin Sheikh
Page 71
 0
0
advertisement
Download
advertisement
Add this document to collection(s)
You can add this document to your study collection(s)
Sign in Available only to authorized usersAdd this document to saved
You can add this document to your saved list
Sign in Available only to authorized users