Unix Biography
advertisement

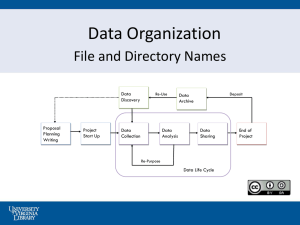
Unix Biography Unix is a powerful and popular multi-user operating system developed in AT & T’s Bell laboratories. The origin of Unix can be traced back to 1965, when a joint venture was undertaken by Bell Telephone Laboratories, the General Electric Company and Massachusetts Institute of Technology. The aim was to develop an operating system that could serve a large community of users and allow them to share data if need be. That version is known as Multics (for multiplex information and computing service). Dennis Ritchie and Ken Thompson did this. In 1969 the two evolved the first version of the multi-user system Unix. At that time all its assembly code being machine dependent, the version was not portable. To remedy this, Ken Thompson created a new language ‘B’ and set about the task of rewriting the whole Unix code in this high level language. Language ‘B’ lacked in several aspects necessary for real life programming. Dennis Ritchie sifted the inadequacies of B and modified it to a new language, which is named as ‘C’ – the language that finally enabled Unix to stand tall on any machine. By the mid eighties there were more than a hundred thousand Unix installations running on anything from a micro to a mainframe computer and over numerous varying architectures. Almost a decade later Unix still holds the record for being the soul of more computer networks than any other OS is. Features of Unix The important feature of Unix is discussed here. 1. Multi-user Capability In a multi-user system, the same computer resources – hard disk, memory etc. are accessible to many users. Each user will be given a terminal to operate from. A terminal, in turn is a keyboard and a monitor, which are the I/O devices for that user. All terminals are connected to the main computer whose resources are availed by all users. All terminals are connected to a host machines known as a server or a console. There are several types of terminals that can be attached to the host. a. Dump Terminals – These terminals consist of a keyboard and a display unit with no memory or disk of its own. These can never act as independent machines. If they are to be used they have to be connected to the host machine. b. Terminal Emulation – A PC has its own microprocessor, memory and disk drives. By attaching this PC to the host through a cable and running software from this PC we can emulate it to work as if it is a dump terminal. At such times, the memory and the disk are not in use and the CP cannot carry out any processing on its own. The software the makes the PC work like a dump terminal is called Terminal Emulation Software. VTERM and XTALK are two such popularly used software. c. Dial-In Terminals – These terminals use telephone lines to connect with the host machine. To communicate over telephone lines it is necessary to attach a modem to the terminal as well as to the host. 2. Multitasking Capability Another highlight of Unix is that it is multitasking, implying that it is capable of carrying out more than one job at the same time. It allows you to type in a program in its editor while it simultaneously executes some other command you might have given earlier. 3. Communication Unix has excellent provision for communication with fellow users. The communication may be within the network of a single main computer, or between two or more such computer networks. The users can easily exchange mail, data, programs through such networks. 4. Security Unix allows sharing of data, but not indiscriminately. Unix has three provisions for protecting data. Assigning passwords and login names to individual users ensuring that not anybody can come and have access to your work provides the first. At the file level, there are read, write and execute permission to each file which decide who can access a particular file, who can modify it and who can execute. The file encryption utility encodes your file into an unreadable format, so that even if someone succeeds in opening it, your secrets are safe. 5. Portability One of the main reasons for the universal popularity of Unix is that it can be ported to almost any computer system, with only the bare minimum of adaptations to suit the given computer architecture. System Organization Tools and Applications Shell Kernel Hardware The kernel has various functions. It manages files, carries out all the data transfer between the file system and the hardware and also manages memory. The shell, or the command interpreter as it is called, is the mediator, which interprets the commands that we give and then conveys them to the kernel that ultimately executes them. Types of Shells 1. Bourne Shell – Steve Bourne’s creation, known after him as the Bourne Shell, is the most popular shell in Unix that’s why it is bundled with every Unix system. 2. C Shell – was created by Bill Joy, it has two advantages over Bourne shell. First it allows aliasing of commands. You can decide what name you want to call a command by. The second benefit is it has a command history feature. 3. Korn Shell – it is a superset of Bourne Shell but not-so-widely used. It was designed to be so by David Korn. Unix Commands Things to remember when issuing commands a. All Unix commands must always be entered in small case letters. b. Between the command name ant the options that may be available with the command there must always be a space or a tab Ex. ls –l. The option is usually preceded by a minus (-) sign. The options available with a command are often known as switches. c. Two or more options available with the command can usually be combined. For example, the command ls –l-a is same as ls –la. d. If you make a typing mistake, press Backspace to erase characters. e. To cancel the entire command before you press Enter, press the Del key. 1. $who am i – displays the information about the user. Sample output: aa1 tty3a Jun 10 09:15 aa1 – login name; tty3a – the terminal number or the serial port line by which your terminal is connected to the host machine. The date and time at which you logged in 2. $who – displays data about all the users who have logged into the system currently. Sample output: aa1 tty3a Jun aa2 tty3c Jun inti tty3a Jun hari tty3a Jun 10 09:15 10 09:25 10 08:45 10 07:10 Exercise Pick up the correct answers for each of the following questions: 1. Unix OS was first developed by a. Dennis Ritchie b. Bjarne Stroustrup c. Ken Thompson d. Brian Kernighan 2. Unix OS was first developed at a. Microsoft Corp., USA b. AT & T Bell Labs, USA c. IBM, USA d. Borland International, USA 3. Unix OS cannot run on which of the following microprocessor a. 8086 b. 80286 c. 80386 d. Pentium e. None of the above 4. Unix is written in a. B language b. C language c. Ada language d. Perl language 5. Unix is a. Single user, single tasking OS b. Single user, multitasking OS c. Multi-user, multitasking OS d. None of the above 6. If every user working on a Unix setup is to use the printer, then the printer should be attached to a. The host machine b. Any of the terminal c. The terminal from where the first login was made d. None of the above 7. For dial-in terminal facility which of the following is a must a. Multimedia kit b. Modem c. Printer d. Terminal emulator 8. In a typical Unix setup the host machine is attached to the terminal through a. I/O card b. Sound blaster card c. Disk controller card d. 4/8 - port controller card 9. Which of the following is a popular terminal emulation software a. VTERM b. VT100 c. COMIT d. Perl 10. Which of the following shells are used in Unix a. K shell b. Born shell c. Den shell d. C shell File System of Unix Users and Groups The top level user is know an System administrator Several groups are there under him. Each user belongs to one group. The following figure shows the organization of the users and groups. System Administrator Group1 User1 User2 User 3 Group2 User4 User 4 Group3 User6 User7 User8 Creation of a user account involves the following activities: 1. Providing login name to the user 2. Providing initial password to the user 3. Putting the user in one of the groups 4. Proving a default working shell to the user 5. Providing a default working directory to the user File System Unix treats everything it knows and understands, as a file. All utilities, applications, data in Unix is stored as files. Even a directory is treated as a file, which contains several other files. The Unix file system resembles an upside down tree. Thus, the file system begins with a directory called root. The directory is denoted as slash (/). Branching from the root there are several other directories called bin, lib, usr, etc, tmp and dev. The root directory also contains a file called unix which is Unix kernel itself. These directories are called sub-directories, their parent being the root directory. Each of these sub directories contain several files and directories called sub-sub-directories. The below figure shows the basic file structure of the Unix file system. / (root) unix bin lib dev usr tmp etc user1 user2 user3 bin Main reason behind creation of directories is to keep related files together and separate them from other group of related files. The bin directory contains executable files for most of the Unix commands. Unix commands can be either C programs or shell programs. The lib directory contains all the library functions provided by Unix for programmers. The programs written under Unix make user of these library functions in the lib directory. The dev directory contains files that control various I/O devices like terminals, printer, disk drives etc. In the usr directory there are several directories, each associated with a particular user. These directories are created by the system administrator when he creates accounts for different users. With in the usr directory there is another bin directory which contains additional Unix command files. The tmp directory contains the temporary files created by Unix or by the users. The etc directory contains binary executable files usually required for system administration. File system features a. It has hierarchical file structure b. Files can grow dynamically c. Files have access permissions d. All devices are implemented as files Creating Files There are 2 commands to create files: touch and cat. $ touch filename – creates a file with the given file name. The size of the file would be zero bytes since touch doesn’t allow you to store anything in a file. If you want to create several empty files quickly follow the below command $touch filename1 filename2 filename3 filename4 $ ls lists the contents of a directory If you want to creates a file to store a few lines in a file. Type the following $cat > test press the Enter key, type in two lines of text: Valderama, Valderama pass the ball to Asprilla Asprilla, Asprilla shoot the ball into the net Once you are through with this press the keys Ctrl d which indicates the EOF character. To see the contents of the file test type the below $ cat test $ cat sample1 sample2 > newsample – which concatenates the contents of sample1 and sample2 and store them in the file newsample. If the file newsample already contains something it would be overwritten. If you want that it should remain intact and contents of sample1 and sample 2 should get appended to it then try the following. cat sample1 sample2 >> newsample cat > .cricket Surat is different than Sharjah So sixes don’t come so easily at Sharjah Ctrl+d The above cat command will create the file by the name cricket. But if you try to list the files you can’t. Because this is know as a hidden file. $ clear used to clear the previous screen Directory related commands $ pwd stands for “present working directory” , which is used to find in which directory the user is working currently. $ mkdir directory-name used to create a new directory $ mkdir –p works/bpb/unix/book to create sub-sub directories in one shot. $ cd new-dir used to change over to a new directory $ cd .. will take you back to the parent directory. $ cd will change over to the current users home directory. $ rmdir directory-name used to remove an existing directory. Removing a File/Directory $ rm filename/directory removes the given file, files or directory supplied to it. $ rm –i removes files interactively. You are asked for confirmation before deleting the file. $ rm –r dir1 recursively removes all contents of dir1 and also dir1 itself. Listing Files and Directories $ls lists the contents of the current or specified directory. There are around two dozen options to go with ls that list the contents in ways to suit every fancy of yours. i. $ ls –a lists the hidden files in that directory which we created using cat > .cricket. ii. $ ls – l gives a long listing. Sample output follows Total 4 - rwxr-x--x 1 user1 group1 Total 4 rwxr-x--x 1 user1 group1 24 May14 10:20 example1 24 May14 10:20 example1 total number of disk blocks occupied by the files. file type file permission number of links owner of the file group the owner belongs to size of the file in bytes date and time when the file was last modified file name File Permissions in detail rwx | rwx | rwx First 3 permissions held by owners Second 3 permissions for the other users in the group Next 3 permissions for users outside the group Example: rwxr-x--x Caribbean Owner can read, write as well as execute the Caribbean Members of the group can read and execute the file Caribbean, but can not write to it. A – indicates that the permission is denied All others can only execute Caribbean. Changing file permissions File permissions are encoded numerically. The weights assigned to the three permissions (rwx) are: Permission Weight Read (r) 4 Write (w) 2 Execute (e) 1 When all three permissions are available, the total weight age or value is 4+2+1, i.e. 7, as is the case with the owner of Caribbean. The group permissions or Caribbean are r-x, hence the value is 4+0+1, i.e. 6. the permissions for the rest are --x, thus the value assigned is 0+0+1=1. Therefore we can say that Caribbean has the permission 761. when everybody has all the permissions, rwxrwxrwx, they would amount to 777. The existing file permissions can be changed by the owner of the file or by the super user by using chmod command. If we want the owner of Caribbean to have all the permissions and the group and others none, we say, $ chmod 700 Caribbean This way of changing file permissions is referred as the absolute mode. There is another syntax for chmod that changes permissions, which constitutes the symbolic mode. Its general form is, $ chmod [who] [+/-/=] [permission] file The who refers to whom the permissions are to be assigned? It may be the user or owner (u), the group (g) or others (o). if none is specified, all are assumed. The + refers to add permission, - refers to remove permission and = instructs chmod to add the specified permission and take away all others, if present. The specified permission can be r, w or x. The command to give write permission to all would be $ chmod +w Caribbean In order to take away execute permission from others and group we would say $ chmod go-x myfile What if we are to give read permission to group and others and take away their write permission for a file called Yankees? In such case we should use chmod as follows: $ chmod go+r,go-w yankkes The following command removes all existing permissions and replaces them with read permission for group and others and read & write permission for owner of the file file1. $ chmod go=r,u=rw file1 Instead of using u/g/o and +/-/= we can straightaway use the weight (read=4, write=2, execute=1) associated with each permission. That is the easy way to do. iii. $ ls –c list entries by column iv. $ ls –g like –l without owner v. $ ls –o like –l without group vi. $ ls –Q enclose entry names in double quotes vii. $ ls –r reverse order while sorting viii. $ ls –R list subdirectory contents ix. $ ls –s size of each file in blocks x. $ ls –S sort by file size xi. $ ls - -help display help and exit xii. $ ls p* lists all files whose name begin with p Copying and moving a file In DOS we copy a file, while in Unix we cp it. For example, $ cp letter.a letter.b This will copy the contents of letter.a into a file letter.b. If letter.b does not exist, it will be created. If it exist then it will overwrite letter.b without warning you. $ cp letter.a letter.b letters In such a use of cp, all files mentioned are copied to the indicated directory letters. Provided the directory letters exists, both the files letter.a and letter.b would be copied to it. Just as in DOS, in Unix too you can copy files from or to different directories by specifying their name along with the path. For example: $ cp /usr/aa16/chapter1 /usr/aa16/book/chap1 Here the file chapter1 is copies from the directory /user/aa16 to the directory /usr/aa16/newbook. When copied to this directory it would have the name chap1 instead of chapter1. Moving files If you want to move the files from one directory to another you have to type the following command $ mv letter.a letter.b letters On execution of this command letter.a and letter.b are not longer present at their original location, but are moved to the directory letters. Renaming the file or folder Suppose we want to rename the file test to sample we should say, $ mv test sample The mv command also has the power to rename directories. $ mv olddir newdir olddir will be renamed to newdir, provided newdir is not already existing. Creating a link To establish one more link to a file we have to use the following command $ ln old new creates a new link for old Miscellaneous commands $ lc list files in columnar fashion $ lf lists and puts a * after all executable files and a / after all sub-directories present in the current directory. $ logname prints the name of the current user $ uname prints the name of the Linux system. It supports the following options also. -s prints the kernel name -n network node hostname -r kernel release -v kernel version no. -m machine H/W name -p processor type -I hardware platform $ date displays the current date and time $ cal prints calendar for any year in the range 1 to 9999 $ cal 2 2002 returns calendar for February 2002 $ bc takes you to the calculator mode (best calculator). You can perform the basic arithmetic operations (+,-,*,/) and sqrt() function. $ bc -l invokes the calculator with the trigonometric or scientific mode. With this mode you can find log, sin, cos, atan, and exponent values. To call these function use the function’s first letter with the argument. Example: s(2) – returns sin value of 2. $ wc counts the number of lines, words and characters in the specified file. The options –l, -w and –c which allow the user to obtain the number of lines, words or characters individually or in any desired combination. $ sort used for sorting the contents of a file. $ sort myfile sort the contents of myfile and display the sorted output. $ sort file1 file2 file3 sort the contents of several files at once shot. $ sort –o result file1 file2 file3 sorts the files file1, file2 and file3, and saves the result in a file called result. Grep – “globally search a regular expression and print it” $ grep searches the specified input fully for a match with the supplied pattern and display it. $ grep picture newsfile search the word ‘picture’ in the file newsfile and if found, the lines containing it would be displayed of the screen. $ grep picture newsfile storyfile search a pattern in several files.