Information System Design and Development. Level
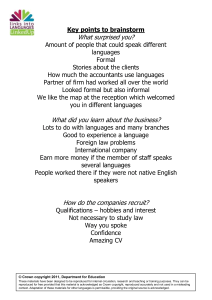
advertisement

Course: Computing Science Information System Design and Development Units Level: National 4/5 April 2013 This advice and guidance has been produced for teachers and other staff who provide learning, teaching and support as learners work towards qualifications. These materials have been designed to assist teachers and others with the delivery of programmes of learning within the new qualifications framework. These support materials, which are neither prescriptive nor exhaustive, provide suggestions on approaches to teaching and learning which will promote development of the necessary knowledge, understanding and skills. Staff are encouraged to draw on these materials, and existing materials, to develop their own programmes of learning which are appropriate to the needs of learners within their own context. Staff should also refer to the course and unit specifications and support notes which have been issued by the Scottish Qualifications Authority. http://www.sqa.org.uk Acknowledgements © Crown copyright 2013. You may re-use this information (excluding logos) free of charge in any format or medium, under the terms of the Open Government Licence. To view this licence, visit http://www.nationalarchives.gov.uk/doc/open-governmentlicence/ or e-mail: psi@nationalarchives.gsi.gov.uk. Where we have identified any third party copyright information you will need to obtain permission from the copyright holders concerned. Any enquiries regarding this document/publication should be sent to us at enquiries@educationscotland.gov.uk. This document is also available from our website at www.educationscotland.gov.uk. 2 SOFTWARE DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 Contents Introduction ................................................................................................... 4 Approaches to learning, teaching and assessment ................................... 8 Subject content ........................................................................................... 13 Staff notes ................................................................................................ 16 What is a database? ................................................................................. 19 What are webpages?................................................................................ 25 Media types .............................................................................................. 30 Macros, scripting languages and HTML.................................................... 35 Design and testing .................................................................................... 38 Hardware and software requirements ....................................................... 41 Computer architecture .............................................................................. 45 Types of computer .................................................................................... 47 Operating systems.................................................................................... 50 Backing storage devices ........................................................................... 51 Networking/connectivity ............................................................................ 54 Security risks ............................................................................................ 57 Computers and the law............................................................................. 60 Computers and the environment............................................................... 63 Glossary ................................................................................................... 65 Qualifications ............................................................................................ 71 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 3 INTRODUCTION Introduction This resource provides advice and guidance for staff delivering Information System Design and Development units at National 4 and 5. Before embarking on these units, staff should be familiar with the contents of the technologies principles and practice paper: http://www.educationscotland.gov.uk/learningteachingandassessment/curricul umareas/technologies/index.asp Staff should also read the computing science professional focus paper produced by Education Scotland to ensure that they have familiarised themselves with the key areas of significant change and potential approaches to teaching and learning. http://www.educationscotland.gov.uk/nationalqualifications/professionalfocusp apers/index.asp?bFilter=1&bSortCD=0&11_subjecttopics=New National Qualifications\|Technologies\|Computing Science (NQ subject) The general unit information that follows has been taken, summarised and adapted from the Computing Science National 4 and 5 course support notes. 4 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 INTRODUCTION Guidance for staff Key skills, knowledge and understanding A broad overview of the subject skills, knowledge and understanding that will be assessed in the Information System Design and Development unit is given below. Mandatory skills and knowledge Applying, with guidance, aspects of computational thinking across a range of straightforward contexts. National 4 Applying aspects of computational thinking across a range of contexts. Designing, implementing and testing, with guidance, digital solutions (including computer programs) to straightforward problems across a range of contemporary contexts. Designing, implementing and testing, digital solutions (including computer programs) to problems across a range of contemporary contexts. Communicating basic understanding of key concepts related to information system design and development clearly and concisely using appropriate terminology. National 5 Communicating understanding of key concepts related to information system design and development clearly and concisely using appropriate terminology. Communicating understanding of key concepts related to software design and development clearly and concisely using appropriate terminology. Basic knowledge of the impact of contemporary technologies on the environment and society. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 5 INTRODUCTION Understanding of the legal implications and environmental impact of contemporary information system technologies. Applying computing science concepts and techniques to create solutions across a range of contexts. Links to prior learning Entry to this unit is at the discretion of the centre. However, learners would normally be expected to have attained some relevant skills and knowledge through prior experience. Skills and knowledge developed through any of the following, while not mandatory, are likely to be helpful as a basis for further learning for this course. Other SQA qualifications For National 4: Computing Science National 3 or relevant component units Numeracy National 3. For National 5: Computing Science National 4 or relevant component units Numeracy National 4. Experiences and outcomes In this course, any of the following Experiences and Outcomes may be relevant. Having investigated a current trend of technological advance in Scotland or beyond, I can debate the short- and long-term possibilities of the technological development becoming a reality. (TCH 4-01a) I can debate the possible future impact of new and emerging technologies on economic prosperity and the environment. (TCH 4-01c) By discussing the business, environmental, ethical and social implications of computer technology, I can begin to gain an understanding of the need for sustainability and accessibility. (TCH 4-05a) 6 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 INTRODUCTION I can compare different forms of security software to gain knowledge and understanding of their functions in protecting contemporary technologies. (TCH 4-08b) I can integrate different media to create a digital solution which allows interaction and collaboration with others. (TCH 4-08c) Through research, I can gain knowledge of computer systems or emerging technologies to understand their differing features and consider their suitability for the world of work. (TCH 4-08d) By learning the basic principles of a programming language or control technology, I can design a solution to a scenario, implement it and evaluate its success. (TCH 4-09a) I can create graphics and animations using appropriate software which utilise my skills and knowledge of the application. (TCH 4-09b) I can use features of software to create my own animation which can then be used to create an animated sequence. (TCH 4-09c) Progression from this unit From National 4 progression may be possible to: Computing Science National 5 National Certificate Group Awards in computing, IT and related disciplines other technological courses at National 4 employment, apprenticeships and/or training in IT and related fields. From National 5 progression may be possible to: Higher Computing Science National Certificate Group Awards in computing, IT and related disciplines other technological courses at National 5 employment, apprenticeships and/or training in IT and related fields. Ultimately, for some, progression may be possible to: Advanced Higher Computing Science a range of computing-related Higher National Diplomas (HNDs) degrees in computing, IT and related disciplines careers in computing, IT and related disciplines. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 7 APPROACHES TO LEARNING, TEACHING AND ASSESSMENT Approaches to learning, teaching and assessment Computing science, like all new and revised national courses, has been developed to reflect Curriculum for Excellence values, purposes and principles. The approach to learning and teaching developed by individual centres should reflect these principles. Learners should be encouraged to participate fully in active learning and practical activities by working together, talking, listening, reading or reflecting on a topic while staff act as a facilitator. An appropriate balance of teaching methodologies should be used in the delivery of the course and a variety of active learning approaches is encouraged, including the following. Activity-based learning Whole-class, direct teaching opportunities should be balanced by activitybased learning and practical tasks. An investigatory approach is encouraged, with learners actively involved in developing their skills, knowledge and understanding by investigating a range of real-life and relevant problems and solutions related to areas of study. Learning should be supported by appropriate practical activities, so that skills are developed simultaneously with knowledge and understanding. Group work Practical activities and investigations lend themselves to group work, and this should be encouraged. Working within a group will encourage learners to collaborate and work co-operatively with others. Learners engaged in groupwork strategies capitalise on one another’s knowledge, resources and skills in questioning, investigating, evaluating and presenting ideas to one another. While working as a team is not specifically identified as one of the skills for life, learning and work for this course, and therefore is not assessed, it is a fundamental aspect of working in the IT and related industries and so should be encouraged and developed by staff. 8 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 APPROACHES TO LEARNING, TEACHING AND ASSESSMENT Problem-based learning Problem-based learning (PBL) is another strategy that will support a learner’s progress through this course. This method may be best utilised at the end of an outcome or a topic where additional challenge is required to ensure learners are secure in their knowledge and understanding, and to develop the ability to apply knowledge and skills in less familiar contexts. Learning through PBL develops a learner’s problem-solving, decision-making, investigative, creative-thinking, team-working and evaluative skills. Computational thinking Computational thinking is recognised as a key skill set for all 21st-century learners – whether they intend to continue with computing science or not. It involves a set of problem-solving skills and techniques used by software developers to write programs. There are various ways of defining computational thinking. One useful structure is to group these problem-solving skills and techniques under five broad headings: Abstraction: seeing a problem and its solution at many levels of detail and generalising the information that is necessary. Abstraction allows us to represent an idea or a process in general terms (eg variables) so that we can use it to solve other problems that are similar in nature. Algorithms: the ability to develop a step-by-step strategy for solving a problem. Algorithm design is often based on the decomposition of a problem and the identification of patterns that help to solve the problem. In computing science as well as in mathematics, algorithms are often written abstractly, utilising variables in place of specific numbers. Decomposition: breaking down a task so that we can clearly explain a process to another person – or to a computer. Decomposing a problem frequently leads to pattern recognition and generalisation/abstraction, and thus the ability to design an algorithm. Pattern recognition: the ability to notice similarities or common differences that will help us make predictions or lead us to shortcuts. Pattern recognition is frequently the basis for solving problems and designing algorithms. Generalisation: realising that a solution to one problem may be used to solve a whole range of related problems. Underpinning all of these concepts is the idea that computers are deterministic: they do exactly what you tell them to do. The corollary of this, of course, is that they can be understood. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 9 APPROACHES TO LEARNING, TEACHING AND ASSESSMENT Whilst computational thinking can be a component of many subjects, computing science is particularly well-placed to deliver it. Staff are encouraged to emphasise, exemplify and make these aspects of computational thinking explicit (at an appropriate level) wherever there are opportunities to do so throughout the teaching and learning of this course and its units. Using online and outside resources Throughout the teaching of this course, the stimulation of learners’ interest and curiosity should be a prime objective. Engagement with outside agencies or industry professionals can greatly enhance the learning process. Online resources, such as those listed in the individual unit support notes, may provide a valuable addition to teaching and learning activities, encouraging research, collation and storage of information and evaluation of these materials. The use of interactive multimedia learning resources, online quizzes and web-based software can also be used to support activity-based approaches. Assessment activities, used to support learning, may be usefully blended with learning activities throughout the course, for example by: sharing learning intentions/success criteria using assessment information to set learning targets and next steps adapting teaching and learning activities based on assessment information boosting learners’ confidence by providing supportive feedback encouraging self- and peer-assessment techniques wherever appropriate. Working towards units and course Learning and teaching activities should be designed to develop: skills and knowledge to the standard required by each unit and to the level defined by the associated outcomes and assessment standards the ability to apply the breadth of knowledge, understanding and skills required to complete the Added Value Unit at National 4 or the course assessment at National 5 successfully. Meeting the needs of all learners Within any class, each learner will have individual strengths and areas for improvement. 10 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 APPROACHES TO LEARNING, TEACHING AND ASSESSMENT For example, within a National 4 class there may be learners capable of achieving National 5 standards in some aspects of the course. Where possible, they should be given the opportunity to do so. Staff need to consider both the outcomes and assessment standards, and the table of content in Appendix 2 of the SQA unit support notes, to identify the differences between National 4 and National 5. In some aspects of the course the difference between National 4 and National 5 is defined in terms of a higher level of skill. For example, in the Information System Design and Development unit, Outcome 1 requires National 4 learners to ‘develop simple information systems using appropriate development tools’, by creating a structure with links, integrating different media types and identifying and rectifying errors, while at National 5 in the similar Outcome 1 learners are also required to create a user interface and write or edit simple code. In other aspects of the course the difference between National 4 and National 5 is defined by additional or more in-depth knowledge. For example, in the Software Design and Development unit, National 4 learners need to report on a contemporary software-based application, while National 5 learners need to compare two different software languages or environments. When delivering this course to a group of learners, with some learners working towards National 4 and others towards National 5, it may be useful for staff to identify activities covering common knowledge and skills for all learners, and additional activities for National 5 learners. This is particularly appropriate where the National 5 learners have come directly from the Broad General Education without previously studying National 4. Where National 5 learners have studied National 4 in a previous year, it is important to provide them with new and different contexts for learning to avoid de-motivation. Learning about Scotland and Scottish culture will enrich the learners' learning experience and help them to develop the skills for learning, life and work they will need to prepare them for taking their place in a diverse, inclusive and participative Scotland and beyond. Where there are opportunities to contextualise approaches to learning and teaching to Scottish contexts, staff should consider this. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 11 APPROACHES TO LEARNING, TEACHING AND ASSESSMENT Gathering evidence Assessment should be an ongoing process that permeates effective learning and teaching. Staff are encouraged throughout the Curriculum for Excellence documentation to adopt imaginative and creative approaches to assessment that take account of learners’ experience in terms of challenge, breadth and application. Staff should refer to the principles of assessment as laid out in Building the Curriculum 5: http://www.educationscotland.gov.uk/thecurriculum/howdoyoubuildyourcurricul um/curriculumplanning/whatisbuildingyourcurriculum/btc/btc5.asp For unit assessment purposes, a variety of methods of assessment should be used to gather a rich range of evidence such as creation of media, written work, role-play and oral presentations. More detail on gathering evidence can be found on the SQA secure website in the unit assessment support notes for National 4 and 5. Staff should share learning and assessment criteria with learners, provide effective feedback, encourage peer- and self-assessment, and use effective questioning techniques. 12 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Subject content Below is a table summarising the content for the Information System Design and Development unit taken from the Computing Science National 4 and 5 course support notes: Information System Design and Development Exemplification and implementation of the following in an application development environment: Topic Structures and links National 4 Database structure: field, record, file Field types: text, numbers, date, time, graphics, calculated Website, page, URL Hyperlink User interface Target audience Structures and links Database structure: field, record, file Field types: text, numbers, date, time, graphics, calculated Website, page, URL Hyperlink National 5 Database structure: flat file, linked tables Field types: text, numbers, date, time, graphics, calculated, link, Boolean Field lengths and range Key field Website, page, URL Hyperlink: internal, external Navigation. User requirements: visual layout, navigation, selection, consistency, interactivity, readability Database structure: flat file, linked tables Field types: text, numbers, date, time, graphics, calculated, link, Boolean Field lengths and range Key field Website, page, URL Hyperlink: internal, external Navigation Frames, sequence INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 13 SUBJECT CONTENT Media types Coding Sound, graphics, video, text Macros Testing Purpose, features, functionality, users Simple descriptions of main features and functionality Technical implementation (hardware and software requirements) Hardware: input and output devices processor clock speed (Hz) memory (RAM, ROM) Software considerations: operating system platform required Technical implementation (storage) Storage devices: built-in, external, portable magnetic, optical capacity, speed rewritable, read-only Technical implementation (networking/ connectivity) Stand-alone or networked LAN/internet Wired/wireless 14 Standard file formats: text: txt, rtf audio: wav, mp3 graphics: jpeg, bmp, gif, png video: mpeg, avi spreadsheet: xls, csv, xml pdf Factors affecting file size and quality, including resolution, colour depth, sampling rate Need for compression Scripting languages (including JavaScript) Mark-up languages Links and navigation Matches user interface design Description of purpose Users: expert, novice, age range Hardware: input and output devices processor type and speed (Hz) memory (RAM, ROM) device type (including supercomputer, desktop, laptop, tablet, smartphone) Software considerations: operating systems Storage devices: built-in, external, portable magnetic, optical solid state capacity, speed rewritable, read-only interface type and speed Peer-to-peer versus client/server Media: wired, optical, wireless Comparison of local versus web/cloud INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Security risks Viruses, worms, Trojans Hacking Security precautions Anti-virus software Legal implications Environmental impact Spyware, phishing, keylogger Online fraud, identity theft. DOS (Denial of Service) attacks Passwords/encryption Biometrics Security protocols and firewalls Use of security suites Computer Misuse Act Data Protection Act Copyright, Designs and Patents Act (plagiarism) Health and safety regulations Energy use Disposal of IT equipment Carbon footprint INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 15 SUBJECT CONTENT Staff notes The main purpose of this text is to provide a single document with the basic theory for the Information System Design and Development unit. It does not provide a step-by-step practical guide in a particular application because there are a variety of excellent resources available already for this purpose and different departments will approach evidence gathering in different ways. The unit assessment support notes for Computing Science National 4 and 5 provide examples of the sort of work learners are expected to be doing to prove that they are working at the correct level. The notes are by no means exhaustive and there are new documents and guides being shared every day on the CAS forum (http://community.computingatschool.org.uk/), which is an excellent community for computing staff to share ideas and resources. Useful websites A short and by no means exhaustive list of useful computing websites. Back issues of Computer & Information Sciences & Engineering newsletters http://www.nsf.gov/cise/csbytes/pastissues.jsp Computer Science Unplugged http://csunplugged.org/activities The Roles of Variables home page http://www.cs.joensuu.fi/~saja/var_roles/ Wikibooks on the topic of computing http://en.wikibooks.org/wiki/Subject:Computing Peer Instruction for Computer Science http://www.peerinstruction4cs.org/ A site which allows staff to create free games, quizzes, activities and diagrams http://www.classtools.net/ BBC site with a collection of excellent video clips to illustrate course theory, with real-life examples http://www.bbc.co.uk/learningzone/clips/ Harvard’s main page of resources for the Scratch programming environment http://cs.harvard.edu/malan/scratch/index.php 16 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Computer Science for Fun magazine http://www.cs4fn.org/teachers/activities/ Online interactive tool for learning programming http://www.codecademy.com/#!/exercises/0 National forum for computing staff to support one another and share resources, experiences and ideas http://community.computingatschool.org.uk/ Home page for Education Scotland computing resources and documentation http://www.educationscotland.gov.uk/nationalqualifications/subjects/computing .asp Recommended books Below are some books that may help learners and staff in aspects of the Computing Science National 4 and 5 courses. Beginning Programming For Dummies (paperback), Wallace Wang. ISBN-13: 978-0470088708 Higher Computing (paperback), John Walsh. ISBN-13: 978-0340905630 How to Pass Intermediate 2 Computing (paperback). Frank Frame, ISBN-13: 978-1444108361 How to Pass Standard Grade Computing (paperback), Frank Frame. ISBN-13: 978-0340973912 Information Systems for You: Student's Book (paperback), Stephen Doyle. ISBN-13: 978-0748763672 Megabyte (paperback), Simon Cotton, Graham Teager and Robert Austin. ISBN-13: 978-0198328254 Pathways to Excellence: Level 3: Computing and ICT (paperback), Frank Frame and John Mason. ISBN-13: 978-1444110791 Pathways to Excellence: Level 4: Computing and ICT (paperback), Frank Frame and John Mason. ISBN-13: 978-1444110807 PCs For Dummies (paperback), Dan Gookin. ISBN-13: 978-0470465424 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 17 SUBJECT CONTENT Raspberry Pi User Guide (paperback), Eben Upton and Gareth Halfacree. ISBN-13: 978-1118464465 Scratch Programming for Teens (paperback), Jerry Ford Jr. ISBN-13: 9781598635362 Standard Grade Computing Studies (paperback), John Walsh. ISBN-13: 9780340885000 The BCS Glossary of IT and Computing Terms (paperback), British Computer Society. ISBN-13: 978-0131479579 The Game Maker's Apprentice (paperback), Jacob Habgood and Mark Overmars. ISBN-13: 978-1430213475 Visual Basic 6 For Dummies (paperback), Wallace Wang. ISBN-13: 9780764503702 Other resources There are other digital resources which at time of writing are available for Intermediate 1/2 Computing and Standard Grade and could provide additional exercises and theory for the Computing Science National 4 and 5 courses. These are listed below. Softplanet Intermediate 2 and Standard Grade http://www.softplanetgroup.com/study-software/businesscomputing/intermediate-2-computing http://www.softplanetgroup.com/study-software/business-computing/standardgrade-computing Webcal Intermediate 1/2 and Standard Grade http://www.webcal.esmartbiz.com/prod0405.htm Exercises and content To reduce the costs of reprographics and allow differentiation in a multi-level class, National 4 and 5 content is included in the same document. National 5 exercises are in bold and National 5 content is highlighted using shaded blocks. 18 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT What is a database? The contacts feature on a mobile phone and the products listed and grouped on a games, clothes or music website are all databases. A database is simply a list of items, all of the same kind, organised in a way that makes it easier to choose or read from the list. Most databases are stored electronically because this makes them quicker and easier to edit, search and sort, and they take up less physical space. Editing a database is when new details are added to the database or existing details are changed. Searching a database simply involves finding a particular set of information from the database, for example everyone whose surname is Smith. Sorting a database is the act of reorganising the database into another order, for example in ascending alphabetical order by surname from A to Z or in descending numerical order by age from oldest learner to the youngest learner. Databases are used by many groups of people, for example: by schools, so that they know which pupils are absent by supermarkets, so that they know what items are in stock by banks, so that they know how much money their customers have. A database application (such as MS Access) is required to create an electronic database. A database application is a program that organises the data entered into a computer. The computer user enters into the computer the data that he or she wants to keep, for example a list of customers or all the people in a club. The database application arranges the data into a table. Here is the data table from an example film database. Film Certificate Genre Goodfritters 18 Gangster Diary of a Lazy Kid PG Kids The Armwrestler 15 Drama Inglorious Bar Stewards 18 War Record Field INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 19 SUBJECT CONTENT All the data for one film is called a record (not to be confused with a row in a spreadsheet). The Armwrestler is suitable for people aged 15 years and over and is a drama. Each piece of data for a film – the name, the certificate and the genre – is called a field in the data table. When planning and designing a database the types of field used must be considered. There are a number of different field types to choose from: text numbers date time graphics calculated link Boolean eg Bob; DD3 O12; £20+VAT can be integers (whole numbers) or real (floating point), eg 1.34 eg 01/01/2013; 1 January 2013 eg 23:30:00 or 11:30 pm databases can hold pictures, eg employee photo or the picture of a product similar to a spreadsheet, calculated fields carry out a calculation on another field or fields and displays the result a hyperlink to a file outside of the database, eg a web page holds one of two values, eg Yes or No, True or False Types of database The two main types of computerised database are flat file and relational. Flat-file databases A flat-file database is like an electronic card index file. In this type of database, the data is stored in a single table. In the case of a games rentals system, the table would store data about both members and games, as shown in the table below. Cost Date rented Date returned Fallover 3 £2.50 03/09/12 05/09/12 Date membership started 03/09/11 003 GBH 5 £2.50 02/09/12 05/09/12 02/09/11 003 GBH 5 £2.50 10/09/12 14/09/12 10/09/11 £2.50 03/09/12 05/09/12 03/09/11 £2.50 12/09/12 14/09/12 12/09/11 £2.50 15/09/12 17/09/12 15/09/11 Game code Game title 001 011 Headband 4 Blacktops 2 011 Blacktops 2 008 20 Member name Telephone number Billy Whizz Beryl the Peril Desperate Dan Dennis the Menace Burglar Bill Bob Hoskins 123344 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 234454 545454 676767 876454 986453 SUBJECT CONTENT 014 015 Toilet Rim £2.50 03/09/12 06/09/12 03/09/11 Farmers Field 3 £2.50 06/09/12 09/09/12 06/09/11 Freddie Flintoff Tom Thumb 667854 454378 The flat-file database above contains one record for each computer game rental. Flat-file databases have a number of problems: Data can be duplicated. Because a new record is created for each game rented, the member details would have to be copied onto each new record, which is inefficient. Duplicating data increases the chance of human error when typing in the same customer’s details a number of times. It can then be hard to be sure which the correct entry is. It is not possible to store information about a member without entering details of a game rental. In other words a customer’s details can only be recorded once they rent something. Removing a game from the database may remove the only record that stores details of a member. Relational databases An improvement on flat-file databases is the use of a relational database. A relational database stores data in more than one table. The idea is to ensure that data is only entered and stored once, so removing the possibility of data duplication and inconsistency. In the above example this would mean that there would be a separate game table, rental table and customer table. Primary or key fields A key is a field or set of fields which uniquely identifies a record. For example in a customer database or file, there may be a number of clients called John Smith so to uniquely identify which John Smith it is there could be a key field called Customer ID. Foreign key A foreign key is a field that is not a primary key in its own table, but is a primary key in another table. Put another way, a foreign key in one table points to a primary key in another table. In the example above, if the DVD rental table was broken down into a customer table and rental table then the primary key in the customer table might be called Customer ID. This Customer ID field would also appear in the rental table as a foreign key. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 21 SUBJECT CONTENT Field length and range The length of a field refers to how many characters the database designer sets aside for a particular field to hold. The age field in a customer database should only need three characters, for example, because people do not live to be thousands of years old (this would require four or more characters) but they may live to be older than 99, thus requiring three characters. The range of a field refers to the acceptable range of values it will accept. An example of this might be if a field holds the month as a number from 1 (January) to 12 (December) then the range is 1 to 12. Input validation can be used to make sure that a user only inputs data in the correct format and if the user makes an error the database will display an error message and ask the user to re-enter, eg in the above scenario, if the number 13 was entered for a month. Similarly, validation could check that the data input is not too long, eg a user puts in an age of 12,000, or too short, eg a telephone number of 1234. 22 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Exercises 1. You own 100 computer games and you want to keep information about them all on computer. You should use a: (a) (b) (c) (d) 2. spreadsheet database word processing program drawing program. Here is part of a database where information about cars is stored. Name of field x Model of car Number of doors Type of field Text Text y Sample data Ford Focus 5 The letter x shows the name of a missing field. Study the sample data and decide on a name for field x: A B C D 3. In the database above, the letter y shows the missing type of field for the number of doors on the car. Choose the correct field type for y: (a) (b) (c) (d) 4. Bob colour of car car registration make of car. text number date graphic. You keep a database of film stars. When a new star appears in a film you need to: (a) (b) (c) (d) edit a star’s record add a new field add a new record create a new file. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 23 SUBJECT CONTENT 5. It is very common to find duplication of data in a flat-file database. This can lead to data becoming inconsistent. What type of database should be used to reduce duplication of data and inconsistency? 6. Using a database package that staff have shown you, create your own flat-file criminal database. First plan out on paper which fields you will need and which field types those fields will be. Then create and populate the database with fictitious criminals. 7. After staff have demonstrated how to create linked tables, take the flatfile database you designed and created in task 6 and design and create a relational database with multiple linked tables. 8. With a partner, research how databases are used in society. Pick a usage and create a presentation, podcast, poster or leaflet summarising your findings. 9. Evaluate another group’s submission for task 8. Give the group two pieces of positive feedback regarding areas you liked and offer one suggestion for improvement. 24 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT What are web pages? A website is a collection of web pages with information about a topic, person, place or organisation. Users interested in a topic can connect to the internet and visit a website to read the individual web pages about that topic. The ‘landing’ page of a website is called the home page. Home pages provide the user with links to other pages in the website. The home page has a web address such as www.bbc.co.uk. This web address is called a URL, short for Uniform Resource Locator. Web pages can be created in hypertext mark-up language (HTML) and can contain text, graphics, sound and video. The process of jumping from one page to another or from one part of a web page to another part of the same page is achieved by using hyperlinks. Hyperlinks can be internal within the same page or website, or external, linking to an entirely different website. A hyperlink could be a piece of text or a picture that is ‘clickable’; generally when the mouse pointer hovers over a link it changes from an arrow to a hand icon. Navigation Navigation is the term used to describe how a user moves from one part of a web page to another, from web page to web page and website to website. To view a web page requires software called a web browser. There are many of these on the market, including Safari, Internet Explorer, Chrome and Firefox. Browsers include features specially designed to make accessing, viewing and navigating web pages as straightforward as possible. Some of these features are listed below: Address bar: allows user to type in web address or URL directly. Backwards, home and forwards buttons: allow user to flick back and forward through web pages. Scroll bar: allows user to view web pages that are longer than the screen area. Favourites/bookmarks: allow user to save the website in the browser's memory so that on future occasions the user does not have to remember and type in the full address again. History: the browser keeps a record of past websites that have been visited, which allows users to back track to websites that they may have used previously but forgotten to bookmark. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 25 SUBJECT CONTENT Sequence In web page design, sequence refers to how navigation on a website is structured. There are three main ways to structure pages on a website: 1. Linear: web pages can only be accessed in order, perhaps by topic or chronologically. Page 1 2. Page 2 Page 3 Page 4 Page 5 Hierarchical: web pages are organised into groups and subgroups, and users ‘drill’ down through categories or groups to get to specific pages or subgroups. Home page Games PC 26 DVDs Books Console INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT 3. Web: web page navigation is designed in such a way as to let users get to web pages from a number of routes. Page 2 Page 1 Page 3 Page 4 Page 5 User interface The interface just means how a piece of software and the user communicate together, how the software gives the user feedback and how the user inputs data into the program. Most applications use a graphical user interface with windows, icons, menus and a pointer as this method is regarded as userfriendly. Target audience When creating an information system such as a web page it is important to consider the target audience. The target audience involves factors like: age group expertise in computer use level of education geographical location accessibility. If the design does not cater for the needs and preferences of the intended audience then users will choose not to use the information system. A website or presentation about computer games targeted at teenagers will look very different from a resource about cake-baking for adults. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 27 SUBJECT CONTENT Visual layout White space gives the reader‘s eyes a rest and separates one type of information from another. Too little white space makes for a crowded, unappealing page. Information should be organised so that there is space between items and the amount of text for the user to read on screen at once is reduced as much as possible. Navigation It can be frustrating for a web page user if they cannot figure out where to go or where they are on a site. Buttons to get around a site should be easy to find and clear to read. Any rollover submenu should be designed to give users time to drill down before they disappear. Users also want to know where in the site they are. Large sites use something called a breadcrumb trail usually at the top of the current page to allow a user to backtrack to previously visited pages further up the navigational tree. In web design there is a three-click rule which says that important information should be no more than three mouse clicks away at any time. Consistency Consistency means making everything on the page and website match. This includes the fonts, colours, button styles and spacing. Everything should have a similar theme to make the design look professional and easy on the eye. If a designer uses too many different types of font, graphics and button types over a website, the site will become more difficult to understand for the user and less appealing. Readability This involves making sure the page, including the typeface (font), is easy to read. This can be achieved by avoiding using all capitals, using large enough text and keeping text left aligned with a contrasting background colour for that page against the text colour. An example of this is that web designers don’t usually use pink coloured text on a red background because the text becomes hard to read. Interactivity An interactive site or information system is one which allows users to provide information as well as just be passive readers. Interactivity can be achieved through things like a built-in search engine facility, discussion areas, areas on 28 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT a page which change to reveal more information depending on where the user puts their mouse on screen etc. In general, interactive websites and information systems will be more appealing and engaging for a user. Exercises 1. Every web page is filled with dozens of these, each sending you to some related web page or picture/file. What am I? 2. Name three ways of navigating on a website. 3. What does URL stand for and what is it? 4. What are the three ways in which a website can be organised in terms of how the user moves from page to page? 5. What is the difference between an external hyperlink and an internal hyperlink? 6. When designing a web page what do we mean by target audience? 7. Name and describe three aspects of good web design. 8. With the web design program or editor that staff have shown you, create a simple web page about yourself, what you study, your hobbies and interests. 9. Swap over with a neighbour and read their web page. Evaluate the page, giving your neighbour two pieces of positive feedback regarding areas you liked and offer one suggestion for improvement. 10. With a neighbour, research what makes a good website and find examples of well-designed websites and examples of badly designed websites. After you have enough information, design and create a group of linked pages explaining your findings, with links to the example sites you have found. 11. Swap with another group and read their submission for question 11. As a larger group, prepare a report summarising the key points for good website design. Each person in the group should be ready to feedback their group's findings to the rest of the class. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 29 SUBJECT CONTENT Media types Multimedia combines different types of media such as text, audio, video and graphics into one system. By combining two or more types of media together in, for example, a presentation or website, the end result should be more eyecatching and engaging. Each media type has a number of different standard file formats. Standard file formats are file types that can be recognised, opened, worked with and saved by a number of different computers and applications. Text Txt The txt file format stores information about the characters in a document without any information about the styles or fonts, just the plain text. Its simplicity means that it is accepted by virtually all computer systems. Because txt doesn’t contain any formatting information (apart from paragraph spacing), it does not take up as much space on a hard disk and will take less time to transmit across a network, for example in an email. Rich text format (rtf) Rich text format files contain more formatting information than txt files, retaining information about indentation, styles, fonts and sizes. Compression Data files can be stored in uncompressed (full-fat version) or compressed (diet version) formats. Uncompressed files have all of the original data and are therefore high quality, but also have a large file size. Compressed formats have a reduced file size but as a result, in general, there can be a loss in quality. Files are compressed so that they take up less file space, thus allowing more files to be stored. Another reason for compression is so that files can be sent over a network quicker than sending an uncompressed file, eg web pages will load more quickly and emails with attachments will be sent and received more quickly and use less data bandwidth. Factors affecting file size The main factor that affects the size of a file, be it a graphic, sound or video file, is the quality or resolution that it is saved at. The higher the quality or resolution a file has, the better the quality but the more data is being saved. More data means more disk space, longer downloads from the internet and therefore more of a user’s data allowance being consumed. Taking a digital photo as an example, there are two factors affecting file size: 30 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT resolution – how many pixels are used to represent the picture colour depth – the size of the colour palette. Below are two examples of file size calculations for graphics: 1. A black and white graphic 4 inches by 4 inches and using 300 pixels per inch. (4 × 300) × (4 × 300) = 1440000 pixels For black and white only one bit is required per pixel (0 for blank, 1 for filled) so 1440000 bits. 1440000/8 = 180000 bytes. 180000/1024 = 175.78 kilobytes. 2. A true colour (24 bits used per pixel, allowing 16 million colours) graphic 4 inches by 4 inches and using 300 pixels per inch. (4 × 300) × (4 × 300) = 1440000 pixels For true colour 24 bits per pixel, therefore 1440000 × 24 = 34560000 bits. 34560000/8 = 4320000 bytes 4320000/1024 = 4218.75 kilobytes 4218.75/1024 = 4.12 megabytes Sampling/frame rate For video and sound, the frame or sampling rate has an effect on the quality and file size. The more snapshots or samples recorded per second the greater the quality, but the more data that has to be captured and therefore the greater the file size. Audio Wav Wav files are uncompressed files containing digitised sound data. They are often used in places such as digital telephone systems and CD players. MP3 A compressed file format for sound, the MP3 file uses lossy compression to reduce file size by taking out frequencies of sounds that the human ear cannot detect, so quality does not suffer. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 31 SUBJECT CONTENT Graphics Bitmap (bmp) This is an uncompressed file format with data being stored about each pixel (picture element) in an image. GIF A compressed file format using lossless compression. GIFs allow users to set a transparent colour in the image but only have a colour palette of 28 or 256 colours, so are best suited for cartoons, graphs and drawings rather than photos. JPEG A compressed file format that takes a bitmap and reduces the file size by cutting out data that the human eye would not notice, like subtle differences in shading. This file format is ideal for photos. PNG The portable network graphics (PNG) file format is an improved version of the GIF format. It is lossless but has a larger palette of colours and allows opacity (the user can decide how transparent a colour is). Video AVI Uncompressed file format for storing video. MPEG A lossy compression format for video that achieves a smaller file size by only storing some of the key frames of video. Spreadsheets XLS The default file format for Microsoft’s Excel spreadsheet package, which holds data in worksheets, charts and macros. CSV A comma-separated values (CSV) file stores tabular data (numbers and text) in plain-text form. Plain text means that the file is a sequence of characters. CSV is ideal for transferring data between different makes and types of applications, for example taking a list of names from a database and importing it into a spreadsheet without having to retype all the names again. 32 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT XML Extensible mark-up language (XML) is a mark-up language like HTML but XML was created to structure, store and transport information. HTML is about displaying information, while XML is about carrying information. PDF PDF (portable document format) is a file format for documents devised by a company called Adobe. To view a PDF requires the user to download and install Adobe’s free reader software. Many programs, such as Microsoft Word, allow users to save documents as PDFs instead of their own native format (eg .doc in MS Word). One of the advantages of saving a file as a PDF is that anyone with a computer and the free Adobe Reader program can view it, hence the word portable. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 33 SUBJECT CONTENT Exercises 1. Which of these file types is a sound file? A B C D 2. A video file needs to be _______________ to reduce the file size. A B C D 3. wav gif avi jpeg compressed saved edited deleted A txt file is used to store: A B C D video sound text graphic 4. What type of file is an avi? 5. Name two factors that affect the file size of a graphic. 6. Create a piece of media of your own choice, be that a sound file, graphic, video or animation. Save the file in its native version and note its file size. 7. Is there a method of compressing the size of the file you created in question 6 either in the package you are using or in another package? If so save the file in a compressed format and make a note of the new file size. If not explain what steps you took to come to this opinion. 34 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Macros, scripting languages and HTML Macros Small programs called macros can be written within some existing application packages rather than using a standalone programming environment. For example, a series of complex or frequently used actions in a spreadsheet or database package can be recorded and then repeatedly activated in the future by a single key press or combination. Macros save time by executing a complex set of frequently used instructions quickly, time and time again. An inexperienced user can use powerful tools without having to know the detailed steps behind them. Macros can be created within an application by selecting the macro function from the menu, giving the macro a name, assigning the key/keystrokes that will activate it and then recording the instruction/actions. Another way of creating macros is by using a scripting language. Scripting language There are two types: 1. 2. those built (embedded) into an application those which work with the operating system and across and between compatible applications. An expert user of an application package would use a scripting language to automate a repetitive task that had to be carried out frequently, thus saving time. Examples of scripting languages include VBScript, JavaScript and Perl. JavaScript is a simple scripting language invented specifically for use in web browsers to make websites more dynamic. On its own, HTML is capable of outputting more-or-less static pages. Once you load them up your view doesn't change much until you click a link to go to a new page. Adding JavaScript to your code allows you to change how the document looks completely, from changing text, to changing colours, to changing the options available in a drop-down list. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 35 SUBJECT CONTENT Example embedded script in JavaScript to write one line to the page: <script type="text/javascript"> <!-document.write("<i>Hello World!</i>"); //--> </script> The advantages of this type of language are as follows: User interface already exists so no need to create one. Ready-made, pre-tested functions already included as part of the language for programmers to use thus saving time and effort. Uses for scripts: – within a word processor – a script to insert a preformatted/customised header and footer on every page of a document – within a photo-editing program – a script to automatically apply pre-set colour levels and filters (eg sepia) to set of photos – within a database – a script to insert a customised company logo and contact details on every report generated by the database. Mark-up languages Mark-up languages are designed for processing, defining and presenting text. The language provides code for formatting the layout and style of a text file. The code used to set the formatting is called a tag. HTML is a popular markup language. Below is an example of some basic HTML: <!DOCTYPE html> < html> < head> < title>Title of the document</title> < /head> < body> The content of the document...... < /body> < /html> 36 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Exercises 1. Macros can be set up when using applications. Describe one method of activating a macro. 2. What type of language would be used to code a macro? 3. Name an advantage of using a macro. 4. Name a mark-up language commonly used to write web pages. 5. Using a text editor and with guidance from staff, write a basic web page in a mark-up language rather than using a graphical webdesign package. The web page can be on a topic of your choosing. Remember to save the file twice: once as the basic text file and once as an HTML file so that it can be viewed in a web browser. 6. Do some further research of your own and try to find and incorporate an additional feature into the web page you created in question 5. For example, can you add sound or embed an animation into the page? Do you know what a marquee is? Could you get a marquee working on your page? INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 37 SUBJECT CONTENT Design and testing Testing Testing an information system involves looking at each function, checking that it is of suitable quality and ensuring that all of the parts work on their own and also together, matching the original design. There are two main types of testing. Screen testing The tester looks at every screen to make sure it matches the design and works as it should. Some standard screen tests are: Do the buttons do what they are supposed to do? Do all the texts, fonts, colours and sizes match the original design specification? Does the video and audio run properly? Any spelling mistakes or typos? Navigation testing Some standard navigation tests are: Do all the internal links work? Do all external hyperlinks work? Purpose, features, functionality and users There must be a clear understanding of what a proposed information system will do before construction begins. This is called the analysis stage and involves answering questions such as the following: What is the purpose of the information system? Who will be using the information system? What are the specific requirements? What type of equipment will it run on? Purpose The designer of a new information system needs to consider what the system aims to achieve when it is complete, what sort of content the system will include and what type of user will be accessing it. For example, the purpose of the system refers to whether the system is for business, leisure or educational use and where the system will run, ie on the internet, on a mobile phone or on a desktop computer. 38 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Features and functionality A feature is what something has, and a function is what something can do. An information system should feature a user-friendly interface; the function would be to make it easier for the user to use that system. The features and functionality an information system will have depend on what type of information system it is, eg is it a website, presentation or mobile application? In general, however, the designer considers things like what type of interface the system will have (graphical or command line), whether or not the interface is customisable, whether the system works online or offline, whether the system uses video and/or sound, if the system is touch operated or uses a mouse or keyboard etc. Hardware and software requirements Whatever system is created will have to be compatible with the user’s system, therefore the designer will need to think about: what specification of computer the user audience will have what type of operating system the user computer will have whether the user computer has sound and video capability how much memory is installed and how fast the processor is. User/audience A new information system must meet the needs of the intended audience; if it is not user-friendly or appealing, people will not use it. The designer must consider the age, expertise, ability and language of the audience. A novice user is one who has little experience of using information systems and as such will require a simple ’cut-down’ user interface with clear icons and menus, and a built-in help system. An expert user will have lots of experience of using information systems and as such will be happy to have access to a more complex and detailed interface with more advanced features and the ability to use things like keyboard shortcuts and commands rather than having to drill down through menus and submenus. The age of the user will affect the design of the system as well. An example of this is that older users may be less dextrous and have poorer eyesight, requiring bigger icons and buttons, and a higher contrast display. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 39 SUBJECT CONTENT Exercises 1. What are the two main areas that should be tested when looking at an information system? 2. Swap with a neighbour and look at the web page they created in the previous section (questions 5 and 6). Create a checklist of things you will test and proceed to fill that list in, giving your neighbour a copy of the finished feedback and keeping a copy for yourself. 3. Using examples, describe the difference between the functionality and the features of a website. 4. Describe what is meant by the purpose of an information system. 5. Name and describe two factors a designer should consider when planning and creating an information system. 6. Take a well-known website of your choice and, on the computer or on paper, make a list of the features and functions on the site. 7. Swap with a neighbour and look at the website and list of features and functions that they have identified in question 6. Tick or highlight the ones you agree with and add any others you can think of. Keep your neighbour’s work and be prepared to share your findings with the class. 40 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Hardware and software requirements To be of use, a computer needs hardware and software. Hardware refers to the physical (tangible) parts of the computer system like the keyboard and mouse. Software refers to the programs or instructions that control the hardware. Hardware Hardware can be grouped into input and output devices. Input devices enable a user to interact with the computer. Brief descriptions of some common input devices are given below. Device Description Example of use Digital camera Captures light coming in from the lens Digital images can be taken of an and converts it into digital form and event such as a birthday party and stores it usually on SD memory card then be transferred to a computer, rather than traditional film. edited and shared online with others. Microphone Allows sound to be inputted to the Recording narration for a video. computer. Microphones are used to take Used in conjunction with voice a sound and convert it into an electrical recognition software to give signal for the computer. commands to the computer or to take the spoken word and convert to text on screen. Touchpad Scanner A small, flat pad which senses your Similar to a mouse it can be used finger movements and uses this to to select items from a menu or control the cursor on the screen and highlight objects on screen to be select icons and menus. edited. Used to input images to a system. A Digitising a traditional photo on light beam passes over the page or photo paper so that it can be edited photo and a sensor detects the light and shared with others, for being reflected. The image is then example on a website. stored in the system’s memory as binary numbers. Mouse A pointing device used to interact with Selecting items from a menu. graphical user interfaces on screen. Highlighting objects on screen to be edited. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 41 SUBJECT CONTENT Keyboard A normal keyboard has keys for the Typing an essay up in a word letters of the alphabet, keys to produce processor. the digits from 0 to 9, keys to produce Typing in numbers/data for a sales all punctuation marks and special spreadsheet. command and function keys. Typing in a web address (URL) for a website. Graphics A flat plastic pad with sensors Freehand drawing by artists into a tablet underneath the surface. The sensors graphics package. detect the movements of a pointing device or stylus and move the cursor on the screen accordingly. Output devices enable a computer to communicate with the outside world. Brief descriptions of some common output devices are given below. Device Description Example of use Inkjet printer Uses ink cartridges and sprays fine jets Home use to print off short letters of ink onto the paper. Inkjet printers can or colour photos. produce high-quality printouts and are quite cheap to purchase but are slower than laser printers and the cost of ink cartridges can be high. Laser printer Similar to a photocopier, a laser printer Business use to print out long uses electrostatically charged toner (ink documents or multiple copies of dust) cartridges instead of wet ink. Lser reports quickly. printers produce high-quality printouts quickly, but are expensive to buy and maintain. Monitor Used to display computer output. To watch a movie that is being Monitors can vary in size (measured in streamed over the internet. inches diagonally from corner to corner) To read the input from a keyboard and resolution (measured in amount of as an essay is being typed. pixels displayed on screen). The higher the resolution, the clearer the image. Monitors today are flat and can be LCD, TFT or LED. LED screens are the most efficient of the three in terms of electricity consumption. Speakers These are used for outputting sound; To provide sound for a multimedia how loud the speakers are is generally presentation. measured in watts. To allow the user to hear the dialogue in a DVD being played on the computer. 42 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Graphics These cards have on-board memory that Allows a user to play high-quality card is dedicated to handling graphics. This first-person shooter games. relieves the main CPU, allowing it to Allows a user to edit and produce concentrate on other tasks. The graphics high-definition video. card takes digital information about the graphics stored in the RAM then sends it out to control the colours and refresh the image on the screen. Sound card Similar to a graphics card, sound cards Allows a user to enjoy high-quality have on-board memory that is dedicated immersive surround sound whilst to handling sound, relieving the main playing first-person shooter games. CPU and allowing it to concentrate on Allows a user to edit and produce other tasks. The sound card takes digital high-quality audio. information about the sound stored in the RAM sends it out to speakers. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 43 SUBJECT CONTENT Exercises 1. What does the L in LCD stand for? A B C D 2. What is the smallest measure of storage size? A B C D 3. Kilobyte Megabyte Byte Bit Which of these is an input device? A B C D 4. Lighter Links Liquid Laser Speakers Monitor Digital camera Printer Which of these is an output device? A B C D Scanner Mouse Keyboard Monitor 5. In pairs, pick an input device of your choice and produce an animation, slideshow or podcast describing it. One person must do research and produce the information on the device description whilst the other should research and produce the information for possible uses for the device. 6. Pair up with another group who have picked a different device to you, watch each other’s pieces and be prepared for anyone in the new larger group to share what they have learned from one another with the rest of the class. 44 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Computer architecture Processor The processor is the brain of the computer, controlling everything that takes place on the computer. Most computers today have more than one processor working together to improve system performance. The processors on mobile phones and tablets will be different to the ones on a normal desktop. These mobile processors might not be as powerful as the desktop equivalent but will be designed to use less power so that the battery on the phone or tablet lasts longer. In addition to this, different companies compete with one another in the processor market and different computer manufacturers can use differing processor types, which can make comparing computers difficult. A basic measure of the power of a computer is processor or clock speed. Currently measured in gigahertz (1000 million pulses per second) this measures how many times per second the system clock pulses. If the computer carries out an instruction or calculation with every pulse of the system clock then the faster the system clock ticks or pulses, the more operations will be carried out per second. Unfortunately it isn’t as simple as just comparing clock speeds of computers because as mentioned earlier there are a wide number of processor types and manufacturers on the marketplace and they perform differently so other measures need to be taken into account as well, such as the amount of memory a computer has installed. Memory If the processor is the brain of the computer, the memory of the computer could be compared to its muscles. The main memory of a computer comprises RAM and ROM. Random access memory (RAM) is the largest part of the main memory, storing the operating system, programs and data while the computer is switched on. Read-only memory (ROM) stores a small part of the operating system called the bootstrap loader. When a computer is powered on, the bootstrap loader pulls the computer up by its bootstraps, finding the rest of operating system in backing storage and loading it into the faster RAM. The main differences between RAM and ROM are that ROM is small permanent memory that does not get written to by the user during normal operations whereas RAM is larger, temporary storage which loses its contents when the computer is powered down. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 45 SUBJECT CONTENT Exercises 1. Which part of the computer controls everything that happens within it? 2. What is the name of the basic measure of a computer processor’s performance? 3. What is the unit of measurement for the measure mentioned in question 2? 4. Research and list three different companies that manufacture computer processors. 5. Which one of these statements about RAM and ROM is true? A B C D Neither ROM nor RAM holds data when the power is switched off. RAM holds data when the power is switched off and ROM doesn't. The user can write data to RAM but not to ROM. The user can write data to ROM but not to RAM. 6. Which generally holds more data, RAM or ROM? 7. When a computer is first switched on, which type of memory is read from first and why? 46 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Types of computer Computers come in different shapes and sizes designed for different users and situations The main categories are listed below. Embedded These are small computers built into other devices, such as cars, mobile phones and microwave ovens. They can be controlled in some cases with simple touchpads or screens, such as the touchpad buttons on the front of a microwave oven. Some embedded systems might provide output, for example if the device is a microwave the output device might be the LED counting down the seconds of cooking time left on the front of the oven. The portability of an embedded system depends on the size and weight of the device the computer is embedded into. If the computer is inside a washing machine it won’t be portable. Smartphone Smartphones are mobile phones that contain a number of convergent technologies. Modern smartphones allow users to send and receive email, surf the world wide web, take and edit digital photos and videos, play MP3s, access e-books, watch movies, play games and carry out many other tasks that users might traditionally perform on a desktop computer. Smartphones have an LED touchscreen or mini qwerty keyboard and built-in speakers. Many have one or more built-in cameras. The phones are generally pocketsized but at the time of writing, a trend for slightly larger phones with larger screens is emerging. Smartphones run off a battery for a number of hours. Tablets These are book-sized computers with a touchscreen or attachable compact keyboard on some types. Many tablets have one or more built-in cameras for things like video conferencing. For output devices tablets have LED displays and built-in speakers. Tablets are light and portable but not pocket–sized, and they are able to run off a battery for a number of hours. Laptop Traditionally operated using a keyboard and track pad, many laptops have built-in webcams. Some new laptops now come with touchscreens as well. In terms of output devices, laptops have LED displays and built-in speakers. Laptops are portable enough to fit in a backpack or special laptop case, and run off a battery for a number of hours. Larger laptops will contain an optical DVD or blu-ray drive. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 47 SUBJECT CONTENT Desktop computer These computers are not portable and are powered by mains electricity rather than by battery. A desktop will have a monitor, full-sized keyboard, mouse and optical DVD or blu-ray drive. Mainframes and supercomputers These computers are very large physically, generally positioned in specially designed rooms with air conditioning, uninterruptable power supplies and enhanced physical and electronic security. Mainframes are used for large organisations like banks to perform a high volume of important tasks simultaneously, whereas supercomputers are generally used by scientists to crunch massive amounts of data to perform a specific complex calculation. Both types of computer have a massive amount of memory, multiple powerful processors and can allow a number of users to access the system at once. Server In client/server networks, one computer acts as a central resource for the others. A server is the central computer on this network. Servers generally have multiple fast processors, lots of RAM and a greater amount of backing storage (hard drive) than the client computers it serves on the network. Servers can have specific tasks on the network such as storing and backing up all of the files centrally for the users on the network and controlling access to the internet and email. Similar to mainframes, servers are generally located in a secure room or cupboard and combined with the additional networking racks the servers require they it can take up a substantial amount of physical space. 48 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Exercises 1. Which type of computer controls and distributes resources on a network? A B C D A server A tablet A palmtop A bottletop 2. What type of computer might be used for a large and complex scientific project? 3. Put the following devices in order of physical size with the smallest first: laptop, desktop, smartphone, tablet. 4. Using the internet research embedded devices and create a presentation, web page, podcast or poster on a particular kind of embedded device of your choice. What is it embedded into? What is its function? 5. Look at your neighbour’s submission for question 4. Is there any other information you would like to know that is missing? Feed back to your neighbour two things you liked about the piece and one area that could be improved on. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 49 SUBJECT CONTENT Operating systems Some people would say that the operating system is the most essential software on a computer system. The operating system is the first program to load up when a computer is powered up and contains a set of programs that control how the computer functions. Without an operating system installed the computer is just an expensive lump of metal and plastic. The operating system co-ordinates and manages all of the computer's activities, looking after things like where files are saved, how much RAM a program needs to carry out a task, customising the interface to suit the needs of the user and handling any hardware that is plugged into the system. Operating systems are large programs that can take up a large amount of disk space and require a lot of RAM. Different types of computer can require their own type of operating system, for example Apple computers use a different operating system to normal personal computers. In addition to this, some operating systems are called open source and can be freely downloaded and then re-programmed or customised whilst others have to be paid for and the source code is closed or locked down and can’t be reprogrammed by the user. The operating systems that run on mobile phones and tablets are a little different to the ones found on a normal desktop computer. A mobile phone or tablet operating system will have be able to run on different and in some cases less powerful processors. It will also have to deal with input from a different range of input devices and because the devices are battery powered, managing power consumption will be particularly important. Large organisations like banks and government departments will require an operating system that allows lots of users to communicate and share files over a network and will have to incorporate enhanced security, backup and user management features. Exercises 1. With a partner, research and list as many operating systems as you can. 2. Swap your list from question 1 with another group, tick the ones you had on their list and add any others they didn’t have. Make a note of any names you didn’t have on your list and make sure to add them to yours. 3. What must be taken into account when designing an operating system for smartphones and tablets? 50 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Backing storage devices Backing storage devices are used to store the programs and data that the computer can access. The contents of backing storage are not lost when the power to the computer system is turned off. There are two ways to access data on a backing storage device: randomly or sequentially. Random access means that particular files can be jumped to without having to read through all of the data, in the same way a user might select a track from a CD or a scene from a DVD. With sequential access, the user has to run through all of the data to find a file (similar to fast forwarding on an old video tape). Type of access Random/direct Sequential/serial Backing storage device Hard disk drive, memory cards, flash drive, CD, DVD and blu-ray drives Magnetic tape drive Hard disk drive – magnetic drive The hard drive is the main storage device for programs and files on personal computers. They have a very large storage space, usually measured in gigabytes (but some are now into terabytes). Traditional hard disks have spinning platters and a moving read head, but recently companies have started to produce solid state hard disks which do not have any moving parts and are therefore smaller, use less power and are more reliable. Flash drive Small and portable, this type of backing storage plugs into the USB port of a computer and can store gigabytes-worth of data, making them a convenient way of keeping a backup copy of files and of transferring files from one computer to another. Memory cards Mainly used in small electronic devices such as digital cameras, MP3 players and mobile phones, memory cards are usually read by connecting the device containing the card to the computer or by using a USB card reader. Memory cards are small, light and again have no moving parts. Despite the small physical size some types of memory card can hold many gigabytes worth of data. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 51 SUBJECT CONTENT Optical disks These disks use lasers to read data ‘burnt’ onto the disk surface. Disks can be ROM, recordable or rewritable. ROM disks can only be read from and can’t be written to, recordable disks can generally only be written to once and rewritable disks allow users to write over the disk multiple times as you might a flash drive. CDs store around 700MB of data, DVDs about 4GB and blu-rays about 25GB. Magnetic tape These small cassettes (similar to old 8mm video camera or audio cassettes) are mainly used as backup systems for large networks. The tapes can store a lot of data but retrieving data can be slow as the user has to fast forward and rewind through the tapes to get to the data. Interface type and speed When discussing backing storage, the interface refers to how the device communicates with the processor. The most common interface is USB. When looking at an interface it is important to consider the speed of data transfer, or how quickly data is sent to and from the device. The slower the interface speed the longer a user has to wait to copy or save files. 52 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Exercises 1. Which of these is a backing storage device? A B C D Scanner Flash drive Printer Speakers 2. What type of access is used by a magnetic tape drive? 3. Use the internet to research the current cost and capacity of the backing storage media mentioned on the previous page. Put your findings into a table, sort the table from lowest value storage to highest value storage, print this list out and save your table. 4. Using the table created in question 3, perform another sort but this time for capacity in descending order from highest capacity to lowest capacity. 5. What is meant by the term ‘solid state’? 6. Add two other columns to the table created in question 3, adding any information you can find about the interface type and speed of the backing storage types mentioned. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 53 SUBJECT CONTENT Networking/connectivity A network is two or more computers connected together. Networks commonly consist of a server computer that manages the network, and clients for users to connect to the network. Servers are special computers on a network that manage the running of the network resources; clients are any computers that can access the network. The other kind of network examined in this course is a peer-to-peer network. Peer-to-peer networks consist of between two and five computers connected together. Peer-to-peer networks don’t have the expense of a dedicated server. All machines on the network have equal status, with no one machine having any controlling role. Machines can share resources such as printers, folders on hard disks and an internet connection, but security and backups are more difficult to implement than they would be on a client server network. This kind of system works best in a home or small office. Advantages of networking Networks allow users to share data and programs. Data stored on one computer can be made available to all computers on the network. This saves time because files do not have to be individually placed on every single computer on the network. Also, parts of programs can be stored centrally on a server which saves storage space on the client computers. Peripherals can be shared more easily on a network. Some expensive hardware, such as colour laser printers, can be shared using a network. Instead of buying a printer for each individual workstation one fast printer can be bought and shared by the clients. A big advantage of networks is that clients can easily communicate electronically with other clients on the network. Scale of a network Networks can be categorised into two main types based on their scale or size. There are local area networks and wide area networks. Local area networks (LANs) are groups of computers in close proximity to each other, such as in an office building, a school or at home. Wide area networks (WANs) cover a large geographic area, such as a city, county or country. The internet is a global network of networks where many LANs and WANs are interconnected. 54 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Wired, optical and wireless networks Wired networks use cables to transfer data between computers and devices. The type of wire used can have an effect on how fast the data can be sent and received. The most common type of networking cable is twisted pair or ethernet cabling, which can support quite high transmission speeds, but the fastest type of cabling is fibre-optic, which uses light signals. The downside to fibre-optic cabling is that it is more expensive than twisted pair. Wireless networking involves computers and devices communicating with one another without any cabling. Common types of wireless networking methods are Bluetooth and wi-fi. Wireless technology allows you to move around a building and still be connected to the network. A wireless network requires each computer to be fitted with a wireless network card and to be within range of a wireless hub or router. The downside to wireless networking is that the bandwidth or speed of transmission is generally slower than a wired connection. Bluetooth is a wireless network technology that allows devices like mobile phones, printers, headsets and laptop computers to form mini-networks when they are in close proximity to each other. Cloud computing Cloud computing involves renting computer storage and power from large multinational companies with special facilities. With cloud computing, the user accesses data and applications over the internet from their supplier rather than from the backing storage of the local computer or device that is currently being used. The advantages to this are many but include the convenience to the user of always being able to access their data wherever they are as long as they have an internet connection and the added security of the user data being stored safely and securely on a state-of-the-art server. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 55 SUBJECT CONTENT Exercises 1. When two computers are linked together it is called: A B C D 2. A server controls: A B C D 3. the world wide web the internet a server a network switching on a computer the running of a network switching off a computer the running of computers A network with a small geographical spread is called: A B C D a LAN the internet a WAN the world wide web 4. Name two advantages of setting up a network. 5. Name two types of wireless network technology. 6. Name two kinds of network media. 7. Research a company that provides cloud computing services and produce a report or presentation profiling that company. 8. With a partner, create a presentation, poster, animation or podcast detailing the advantages and disadvantages of cloud computing. One team member should be responsible for the advantages and another should be responsible for the disadvantages. When you are both finished have a discussion and try to agree as a pair whether the advantages outweigh the disadvantages. 56 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Security risks When computers are connected together in a network the benefits are numerous. However, there are risks to computers being interconnected. A major problem can be viruses. A virus is a program that when run infects a computer system, causing damage or disruption to the system. As well as viruses there are two other types of file that can cause disruption on a network: worms and trojans. Worms, once activated, copy themselves automatically and very quickly between computers on a network, causing a bottleneck on the network. Trojans are programs that might perform a normal process on the computer but underneath secretly perform another, possibly harmful, process at the same time. Denial of service attacks are when individuals target networks and try to bring them to a standstill by activating programs like worms or bombarding the network with bogus requests, both of which keep the network so busy that the normal activity on the network cannot continue. A denial of service attack can cost organisations lots of money in terms of lost business, damaged reputation and wasted manpower. Hacking Hackers can be likened to digital burglars using a network to gain unauthorised access to other people’s computer systems in order to place viruses, copy or delete data. Spyware Spyware is software that secretly records the activities of an unsuspecting computer user. The majority of spyware is malicious, aiming to capture passwords, banking and credit card details, and send them over the internet to fraudsters. Keylogger A keylogger is a type of surveillance software that can record every keystroke made by a user and save it to a file. A keylogger recorder can record instant messages, email and any information typed at any time on the user’s keyboard. The file created by the keylogger can then be sent back over the network to, for example, a fraudster. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 57 SUBJECT CONTENT Phishing Phishing is the act of fooling a computer user into submitting personal information by creating a fake website that looks like a real (and trusted) site. It is a hacking technique to ‘fish’ for passwords and other secret financial information. Software security measures Antivirus software A group of programs devised to stop or find and remove viruses from computer systems. To be most effective, antivirus software should be running all the time, scanning the system, checking for tell-tale virus signatures or suspicious virus-like activity. Firewalls A firewall is a program or piece of hardware that helps stop hackers, viruses and worms from entering a computer over the internet. Security suites A collection of programs controlled by a single control panel that provides the user with a number of functions in one place, including antivirus, firewall, antispam, parental controls, website authentication, password storage and protection against identity theft. Some security suites also include backup and computer tune-up services. User identities (IDs) and passwords Only authorised users are issued with the IDs and passwords that are needed to gain entry to the network. When users log on, the computer system checks their IDs and passwords, and tries to match them with those on file. Users only gain access to the network if the IDs and passwords they have entered match those kept on the system. Biometrics Some systems use biometric technology to ensure that only authorised users gain access to a network. Biometric security involves storing data about fingerprints, voices or people’s eyes on special smart cards. Encryption Encryption is the encoding of data held on the system. This means that if the network is hacked into the data are meaningless to the hacker because they do not have the security key to unlock or decipher the encrypted data. 58 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Exercises 1. Which statement about viruses is true? A B C D Only networked computers can be affected by viruses. The best method of avoiding viruses is to use antivirus software. All viruses delete data from the user’s hard disc. Viruses can only be spread by sharing USB flash drives. 2. State one way of spreading computer viruses. 3. Describe one common symptom of a computer virus. 4. What is the name given to gaining unauthorised access to another person’s computer? 5. Apart from hacking and viruses, name two other threats to computer systems. 6. Name two kinds of biometric security measure. 7. If a computer has been hacked and data has been stolen how else could that data be made secure? 8. Name three services that could be included in a security suite. 9. Describe what is meant by a denial of service attack. 10. Research a recent news story about computer security. Was there any damage or loss of data? Who was involved? Was the issue resolved? Write a short report or presentation detailing your findings. Swap with a neighbour after you have finished and read their piece. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 59 SUBJECT CONTENT Computers and the law With the advent of computers new laws were created to tackle issues that arose. The Data Protection Act Companies and organisations like the government hold a lot of personal data about individuals. To protect this data and people’s rights, the Data Protection Act was passed by Parliament to protect peoples’ privacy. In short the law states that: all data held on a computer must be registered with the Data Protection Agency if a data subject wishes to inspect data held about themselves they can request to see their own personal data if data held about data subject is incorrect they can demand it is changed the data user is obliged to keep the data safe, secure and up to date, and not to hold the data for longer than is necessary. The Computer Misuse Act This law makes it illegal to gain access to a computer without permission from the owner. The Act also makes it illegal to create or deliberately spread viruses that cause deliberate damage to computers. Copyright Designs and Patents Act The Copyright Designs and Patents Act makes it illegal: to make unauthorised copies of software that is copyright protected to send software over a network and copy it without the permission of the licence holder to run unauthorised copies of software on a computer or network. Health and safety There are a number of health problems that can arise when working at a computer for long periods. Repetitive strain injury (RSI), backache, headaches and eyestrain are all conditions that can occur. By using the correct equipment, good working practices and good posture these conditions can be avoided. 60 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Repetitive strain injury RSI occurs when the joints in the fingers constantly tap away at the keyboard. The symptoms of RSI are pain in the joints of the hand. RSI can be avoided by using an ergonomically designed keyboard in a good position coupled with frequent breaks from typing and a good typing technique. Computer users can also purchase gel wrist pads which support the typist at the keyboard. Eyestrain The symptoms of eyestrain can be blurred vision and irritated eyes, and can be avoided by the computer user looking away from the screen at regular intervals and focusing on a distant object. Health and safety law Because of the health issues mentioned above employers are now required by law to provide the following: training – employees should have access to training on health and safety issues eye tests – computer users should receive regular free eye tests with spectacles provided at the employer’s expense if required inspections – chairs, computers and work areas should be regularly inspected to make sure that they are up to standard tasks – employers should design their employees’ working day so that workers can have regular breaks from computer-based activity. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 61 SUBJECT CONTENT Exercises 1. Name the law that makes hacking and creating viruses a crime. 2. Name and describe a health and safety measure employers must take to help their employees when using computing equipment. 3. State the law that protects a company logo from being used by another company without permission. 4. Name and describe a health problem that can occur when using a computer. 5. Research a piece of hardware or equipment that prevents a particular health issue when using computers. Present your findings in a presentation or report. 6. Describe what a company must do to adhere to the Data Protection Act. 62 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Computers and the environment Carbon footprint A carbon footprint measures the amount of greenhouse gases emitted during the production and use of a product, in this case computer equipment. Using the internet consumes energy at the user end but also involves electricity usage and therefore carbon emissions by the companies that run the websites users view. On the plus side, computers can help reduce carbon emissions by making equipment more efficient. An example of this would be modern enginemanagement systems on cars that control the car engine to make it more fuel efficient. Modern manufacturers of IT equipment are constantly looking for ways to reduce the energy consumption of devices from low–power-consumption processors to low-energy-rated LED monitors. With modern advances in networking, employees can telecommute, which means that they can work from home without having to physically commute by car, bus or train. Similarly, organisations can save money and the environment by holding meetings using teleconferencing. Teleconferencing involves people meeting together using webcams and microphones instead of having to leave their normal office and travel to another city or country to meet with colleagues or customers. Disposal of IT equipment What is WEEE? WEEE is waste electronic and electrical equipment like TVs, fridges and computers. Many smaller items slip through the net and are not treated or recycled and get buried in landfill sites. This wastes resources and puts a major strain on the environment. Stores that sell electrical equipment should provide facilities to take back WEEE. They must either offer in-store take-back or be a part of a distributor take-back scheme (and so tell customers where to take it). There should also be information in stores about the environmental impact of WEEE and what customers can do to help reduce the impact their purchases make on the environment. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 63 SUBJECT CONTENT Consumers should consider the environmental consequences before replacing mobile phones, computers or other gadgets. Could the equipment be upgraded or a refurbished product be bought instead? Computer equipment can contain lead and other hazardous materials such as mercury and cadmium . Among the risks when exposed to these materials are lead poisoning, high blood pressure, iron-poor blood, liver disease, nerve and brain damage, and cancer. Because of the dangers involved with having these devices lying around in public landfills, it is important to dispose of equipment responsibly. Besides environmental concerns, a risk of not disposing of equipment properly is identity theft. Identity theft is one of the fastest growing crimes, involving information such as names, addresses, bank and credit card information, and social security numbers being illegally obtained from, for example, old computer systems not properly disposed of. Identity theft can result in damaged reputation and credit rating. Victims of identity theft may have to deal with such effects as denied loans or credit, lost job opportunities, being harassed by credit agencies and even being arrested for crimes they did not commit. Recovering from identity theft can be both time-consuming and costly. Exercises 1. What does a carbon footprint measure? 2. Name two risks when disposing of old computer equipment. 3. Research on the internet or using computing magazines to find an energy efficient computer. Produce a poster, animation or presentation advertising the energy-efficient features of the computer you have found. 64 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Glossary Below is a glossary of common computing terms that you may come across during your studies. Analysis The analysis stage involves reading and understanding a problem. Animation File made up of moving images. Application software Comprises all the programs you apply to a task such as writing a report or sending an email. Applications package Software that performs a particular task such as word processing or desktop publishing. Arithmetic/logic unit(ALU) Component of the processor of a computer that does the calculations and makes the decisions. ASCII A 7-bit code allowing 128 different characters to be represented. Back up A second copy, kept separate from the original, of a program or file made in case the original is lost or damaged. Backing storage Permanently holds data on media such as disk or memory card. Backing storage medium The physical item which holds data such as USB pen drive. Binary Counting using two digits, 1 and 0. Binary language Machine language represented using a series of 0s and 1s. Biometrics Security method using physical characteristics to identify a user such as fingerprints, retinal scan or voiceprint. Bit A binary digit, either one (1) or zero (0). Broadband connection A high-speed internet connection. Byte A collection of eight bits. Central processing unit (CPU) The hardware component that processes data. Computer system A combination of all the components required to process and store data using a computer. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 65 SUBJECT CONTENT Control unit Controls parts of the processor and ensures instructions are in the correct order. Cropping Taking away part of a graphic. Debugging The process of finding and correcting program errors. Documentation All the supporting paperwork for a program. DTP Desktop publishing. Embedded system Minicomputer inside another piece of equipment such as a car or a mobile phone. Encryption Formatting a message into a secret code so that it can’t be understood by anyone who is not authorised to view it. Evaluation Evaluation involves reviewing a solution against a checklist of requirements, highlighting any strengths, weaknesses and improvements needed. Exceptional test data Test data that should be rejected by the program. Extreme test data Test data that is on the limit of acceptability. Field A single item of data stored in a record. File management A function of an operating system dealing with how files are held, controlling the process of saving or loading files from disk. File server Central disk storage for users' programs on network. Flowchart A pictorial representation of the logical steps it takes to solve a problem. Graphical user interface (GUI) Allows users to interact with a program in a graphical environment. Hardware The equipment or physical devices that are associated with a computer. 66 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Hotspot An area of a graphics or piece of text that performs a function when selected. Hot spots are particularly common in multimedia applications, where selecting a hot spot can make the application display a picture, run a video or open a new window of information. HTML Hypertext mark-up language – the language used to write web pages. Human computer interface (HCI) The means by which a computer and user communicate. Hyperlink Links between web pages, documents or files activated by clicking on text or on a particular area of the screen, such as a graphic. Icons Symbols or pictures on a screen. Import To bring in data from one program file to another. Information Data that has been processed. Inkjet printer Reproduces images using dots produced by tiny jets of inks. Input Describes the entry of data items into computer memory using hardware devices such as a keyboard or mouse. Input device Allows data to be entered, such as a scanner or a mouse. Interface Part of a computer system that allows different devices to communicate with the processor by compensating for any differences in their operation. Internet Area network spanning the globe. LCD Liquid crystal display. Local area network (LAN) A network within a single room or building. Macro A set of commands activated by a single keystroke. Mailbox Where electronic mail is stored while waiting to be read/downloaded. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 67 SUBJECT CONTENT Menu List on-screen from which choices may be made by the user. Monitor Output device to view computer activity. Non-volatile Describes storage whose contents are retained when power is lost. Online help Help available in the form of information screens built into the program being used. Online tutorial Step-by-step lessons on how to use a computer program. Operating system Programs which control the operation of a computer system. Optical character recognition (OCR) Characters on paper can be digitised into an editable document for use on a computer. Optical storage A form of non-magnetic storage read by a laser beam being reflected off the pits and bumps on the disk surface. Output Describes the operation of retrieving information from memory and sending it to a device, such as a monitor or printer, so people can view, interpret and use the results. Output device A device which displays data from a computer system, such as a printer. Palmtop A hand-held computer with an LCD screen using a stylus and touchscreen for input. Password A secret code used to gain access to private information on a computer system or to log on to a network. Peripheral A device attached to a computer for input, output or backing storage. Pixel Short for picture element; small dots used to make up a picture on a screen. PPM The speed at which a printer can output pages of print, measured in pages per minute. Processing data items May involve organising items, checking them for accuracy or performing calculations with them. 68 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Processor The part of a computer that carries out the process. Program A list of instructions that tell the computer what to do. Random access Files are accessed directly. Random access memory (RAM) Computer chip that stores data temporarily; data are lost when the computer is powered down. Read-only memory (ROM) Computer chip that stores data permanently: data are not lost when the computer Is powered down. Record Data structure consisting of multiple fields of information. Registers Fast-access memory locations inside a processor. Resolution Quality of a picture: more pixels mean better quality. Rich text format Stores information about text, including formatting. Rotate Turn a graphic or picture around. Scale Making a graphic smaller or bigger. Scanner Input device that allows printed text/graphics to be digitised. Scrolling Moving the display on the screen using cursor keys or mouse. Sequential access Files are accessed one after another. Software Instructions that tell the hardware what to do. Speaker Output device allowing sound to be produced by a device. Spellchecker Software feature that compares the words in a document with the words in an electronic dictionary and offers alternatives if no match is found. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 69 SUBJECT CONTENT Spreadsheet A program used for numeric data, calculations and graphs divided into rows and columns. The individual cells in a spreadsheet can contain text, numbers and formulae. Standard file formats A way of storing data for use by a number of different application packages. Technical guide Contains the installation instructions and technical requirements of a piece of software. Template Ready-made structure/layout for a document. Text editor Allows source program code to be entered and changed. Transition How one slide, page or scene changes to another. Translator Converts a high-level language program into low-level machine code so the processor can use it. User guide Explains the functions and features of a piece of software. Username The means of identifying a user on a computer system or network. Validation A check carried out by the computer on any data to see if it is unreasonable or incomplete, for example to see if a value is within a range (range check). Viruses A harmful piece of software that attaches itself to a file, reproduces and spreads. 70 INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 SUBJECT CONTENT Qualifications The requirements for a qualification in Computing Science National 4 or National 5 are laid out in the SQA documentation, which can be accessed from http://www.sqa.org.uk/sqa/48477.html. To gain a course award, a learner must pass all units as well as the Value Added Unit at National 4 or the course assessment at National 5. The course assessment will contain the Added Value Unit and will consist of a question paper and an assignment. The assignment will be assessed under controlled conditions and marked externally. INFORMATION SYSTEM DESIGN AND DEVELOPMENT UNITS (COMPUTING SCIENCE NAT 4/5) © Crown copyright 2013 71