Notes
advertisement

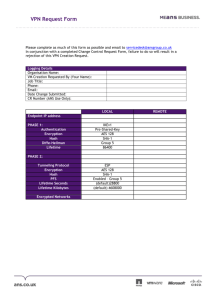
VIRTUAL PRIVATE NETWORK (VPN) An IP VPN is a private data Network built over a shared IP based backbone Employs advanced technology to provide enhanced security and privacy of data (either implemented by the user or provided by the ISP Provides: 1. 2. 3. 4. 5. 6. Remote access to the corporate LAN Site to site connectivity in conjunction with other WAN Technology An Extranet Authentication of remote users Encryption of corporate data Creates a private tunnel between corporate sites or between remote users and the corporate LANS In short, a VPN uses existing technology infrastructure to provide a secure, private and shared link between corporate sites, over the WAN, that appears to be dedicated to the user. See fig 6.3 P291N. Two most important components of a VPN are 1. Tunneling - provided through PPTP (Point –to-point Tunneling Protocol). 2. Security – of Private data through Encryption. Types of VPN: 1. Access VPN: Provides secure, shared access to a corporate intranet or extranet over analog, DSL, ISDN or cable Network 2. Intranet VPN: Provides secure links between corporate sites using shared infrastructure but dedicated connection. 3. Extranet VPN: Connects users to a corporate intranet using shared facilities but dedicated connections Tunneling: Is a process of encoding packets with a protocol in such a way that they can only be decoded at well-defined entry and end points. These tunnels are configured in software, although they represent hardwired interfaces. Types of Tunnels: There are two types of Tunnels: 1. Voluntary Tunnels: Created at the request of a user for a specific use. Used for secure access over Internet. Resides in the User’s computer Hyder Khoja Page 1 2/17/2016 2. Compulsory Tunnels: Created automatically by the ISPS Transparent to the user The Client end-point resides in a RAS (Remote Access Server) running in a Windows Server. See Fig 6.3 P 191 N. Tunneling Protocols: Tunneling requires 3 types of Protocols as shown in the Table 6-1 P192 N. Fig below shows a tunneled packet. Fig 6.4 P 192 N AH stands for Authentication Header and ESP stands for Encapsulating Security Payload. Security: VPN provides 1. 2. 3. 4. Authentication: Authorized users only Access Control: Keeps unauthorized users away Confidentiality: Protection from intruders Security: No tapping Security is implemented at Data Link and Network Layers through Digital Signatures and Encryption. Security can be implemented either end-to-end or Node –to Node. Fig 6.5 P193 N shows node –to node security implemented (such as a Firewall or at the Router. VPN Connectivity and Design: Fig 6-6 P194 N shows a VPN Network. Notice that IP based VPNS are cost effective, flexible, Scaleable, less complex, easy to maintain since ISPS assume most of the responsibility Hyder Khoja Page 2 2/17/2016 VPN Hardware and Software: VPN Hardware: Security Gateways Policy Servers Certificate Authority Holders Firewalls Routers. Mostly Firewalls and Routers implement Security See Fig 6-7 P197 N We shall look at some of the firewall techniques and Router Security implementations. There are 3 Types of Firewalls: 1. Packet Filter: Allows packets to pass only based on the IP Address or Protocols such as allow only FTP or SMTP and Block HTTP as shown in the fig below. Not very effective. 2. Application and Circuit Gateways (also Called Proxies): - - Hyder Khoja Uses a Proxy Server to communicate with secure systems Accepts a connection from the other side and if the connection is allowed, establishes a 2nd connection to the destination host on the other side thereby hiding the data Client does not have a direct connection to the destination Implemented in software through several Proxy Agents, one for each application Installed between the company’s Network Routers and the Public network Page 3 2/17/2016 - Only the Proxy Address is made public. Rest of the Company Address is masked Proxies recreate the IP Packets and relay them to the correct destination. 3. Stateful Multiplayer Inspection: - High level Security technique Better security, faster and easy to use firewalls Uses traffic screen algorithm Each packet is examined (from Application Layer to Data Link Layer) and compared against known states of familiar packets Closes all ports and opens up temporary dynamic ports for establishing temporary connection Works in conjunction with Proxy Servers ROUTERS: Since Routers operate at the Network Layer and examine each packet, it is cost effective to implement security software right inside the Routers or incorporate an additional encrypting co-processor on the Router. Routers are available in the Industry with security features and encryption capabilities and support both transport mode and Tunnel mode IP Security. They work with some kind of authentication system to create a secure VPN Only drawback is that if the Router fails, the access to the VPN is temporarily interrupted. Other Special Security Hardware: Another solution is to insert special tunneling and encryption hardware between the Network Routers and the WAN links. These devices are called Encrypting Bridges. They can be used for either LAN-to-LAN configuration or Client to LAN tunneling. Fig 6-8 P200 N shows a Rack mounted Router and a desktop Firewall VPN Software: Several protocols are available today to provide VPN using the Internet as an Enterprise Networking backbone. These protocols establish private secure channels between the connected systems using Internet. Three of them operate at the Data Link Layer and one operates at the Network Layer Data link Layer Tunneling Protocols are listed below 1. Microsoft’s Point-to-Point Tunneling Protocol (PPTP) 2. Cisco’s Layer 2 forwarding protocol (L2F) Hyder Khoja Page 4 2/17/2016 3. A combination of two called Layer 2 tunneling Protocol (L2TP) Network Layer Tunneling Protocol: IPSec (IP Security) protocol developed by the Internet Engineering task Force (IETF) Fig 6-9 P201 N shows how tunneling Protocols are used to create secure VPNS. PPTP: ( See Fig 6-10 P202 N) Provides a secure dialed up connection between a Client computer and the Private corporate Network over the Internet through ISPS. First a PPP connection is made between the client and the Remote Host using PPP by dialing into an ISP The ISP then creates a second connection between the Client and the PPTP Server at the Remote site over the existing PPP connection. The Client runs PPP and PPTP and the ISP maintains a Windows NT Server running RAS (Remote Access Server). ISP then creates a secure virtual tunnel between the Client machine and the corporate private Network. A VPN can also be established permanently across the Internet by leasing dedicated lines to an ISP at each end of 2 way link and maintaining on-going PPTP based connection across the dedicated links on both sides ISP also uses RADIUS (Remote Authentication Dialed-in Users Service) for authentication. L2FP: Developed by Cisco Authentication is provided by the user not the ISP Corporation is responsible for managing Addresses Accounting is provided by both the User and the ISP The idea is to tunnel the user directly to the corporate site and let the corporate gateway perform most of the functions. ISP is given minimal responsibility See fig 6-12 P204 N Hyder Khoja Page 5 2/17/2016 L2TP: Next generation of VPN solution Combination of PPTP and L2F Can be used for other protocols as well such as ATM, FR etc. See fig 6-11 P203 N Provides 2 levels of Authentication, one at the ISP level by the ISP prior to setting up the tunnel and the second when the connection is set up at the corporate Gateway Provides multiple connections on the same tunnel Provides different QoS parameters for different tunnels for the same site Provides tighter security by incorporating IP Sec’s Encrypting Security Payload (ESP) for encrypting packets over PPP between the user and the ISP Most of the vendors today are incorporating L2TP in their products. IPSec (IP Security): Provides Data privacy, Authentication, integrity, management capability and Tunneling Uses 2 different Headers for IP Packets- An Authentication header (AH) for Authentication and an ESP (Encrypting Security Payload) for Encryption. Also uses an SA ( Security Association ) for Key Management. Exchanges keys to create Security associations between VPN sites based on Cryptographic Algorithms that will be used for a sessions Provides Internet Key Exchange (IKE) or ISAKMP/OAKLEY (Internet Security Association Key Management Protocol) for automatic Key management Resides in hosts, mobile clients (for clients to LAN connection), security gateways (for LAN-to-LAN connection VPN Deployments and Implementation: 1. Over a shared public ATM Network: See fig 6-13 P205 N 2. Virtual Dial Up: See fig 6-14 P207 N VPN Standards: 1. Microsoft has incorporated PPTP in its Windows NT Server which is usually installed on a Companies firewall 2. Cisco has implemented NAS (Network Access Server) in the IOS (Internetworking Operating System) on its Routers to provide a virtual dialed up functionality using L2FP VPN Applications: 1. Economical for large corporations with a lot of on-net calling ( eg over 200,000minutes/month) Hyder Khoja Page 6 2/17/2016 2. 3. 4. 5. 6. Multiple locations with T1-Lines Remote access ISP Access Mobile Workstations Tie line dialing such as extension number dialing VPN Providers 1. NetCom, UUNET, MCI, IPASS, GTE, AT&T VPN Vendors Lucient, Nortel, VPNet Technologies, Microsoft, CISCO, 3COM, IBM, NOVELL, NEC VPN Cryptography: I will present only an overview of Cryptography and IPSec as this is not a course in IP Security. IP Security is specified in RFC 2401 and a good discussion of Cryptography and IP Sec appears in Timothy, 2nd edition P 680-686. 1. Hashing: Refers to one way Key, common Protocols are HMAC, MD2, MD4, SHA 2. Key Cryptography: SKC- Secret Key Cryptography:- Two way symmetric cryptography used for privacy and confidentiality. Common Protocols employing this technique are DES, 3DES, RC4, RC5 and few others. 3. Public Cryptography: Uses 2 different Keys- one private used by the sender and one public used by the Receiver to decode. RSA (Rivest, Shamir and Alderman) is a popular protocol that uses public Cryptography 4. Authenticity Certificates 5. Digital Signatures Hyder Khoja Page 7 2/17/2016