caesar-cipher
advertisement

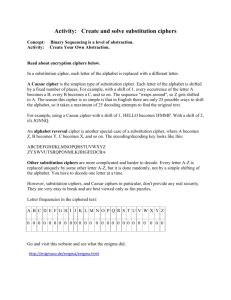
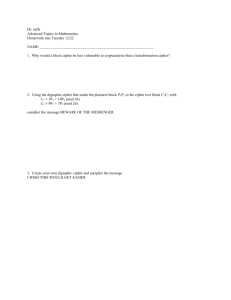
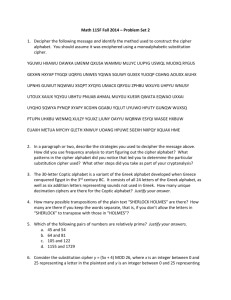
TA1 IDE 08 | Mathematics of Passwords Report CAESARS’ CIPHER MEMBERS: Avril Tay Yoong Xin Lorenzo Ong Wei Yang Yeo Tze Hern 1B|08 1 HISTORY & DEVELOPMENT Named after Julius Caesar. It was used during 50BC by notable Romans including Julius Caesar. In cryptography, the Caesar cipher is also known as Caesar’s shift or the Shirt Cipher. Julius Caesar used the Caesar cipher to communicate with his generals during military campaigns to protect and encrypt messages that were important to the military and the government. The Caesar Cipher is a type of substitution cipher. Each letter in the plaintext is replaced by a letter some fixed number of positions further down the alphabet. The Caesar cipher is a “monoalphabetic substitution cipher”, meaning only one letter is assigned to the alphabet it is supposed to represent According to Suetonius, who wrote the book Life of Julius Caesar, Julius Caesar used the substitution cipher to a shift of three; meaning shifted each letter 3 places further through the alphabet. a(plaintext) becomes D(cipher). “If he had anything confidential to say, he wrote it in cipher, that is, by so changing the order of the letters of the alphabet, that not a word could be made out. If anyone wishes to decipher these, and get at their meaning, he must substitute the fourth letter of the alphabet, namely D, for A, and so with the others” - Suetonius, Life of Julius Caesar 56 Julius Caesar’s nephew, Augustus, also used the Caesar cipher. However, he used it to the shift of one According to David Kahn’s book, The Code Breakers, lovers used the Caesar code to communicate secretly. In the Caesar Cipher, the plaintext is usually in lower case while the cipher text is in upper case. The ROT13 is an application of the Caesar cipher. ROT13 replaces each letter by its partner 13 characters further down the alphabet. As the alphabet consist of 26 letters, the “ROT13 function is its own inverse”, meaning C becomes P and P becomes C. 2 HOW TO USE The Caesar Cipher replaces each letter in the plain text (the alphabet) with a letter that has a fixed number of places down the alphabet. For example, the diagram below has defined its parameters with a shift of 3 also known as the Caesar shift. As such, the letter B in the plaintext becomes E in the ciphertext. Here is a sample of the revolvable cipher which makes encryption much more convenient by turning the inner and outer wheel. The outer wheel is the original alphabet or plaintext and the inner wheel is the ciphertext which can be adjusted accordingly. To encrypt a phrase or word, we could use the table above, where the letters in the dark blue boxes represent the plaintext or the alphabet while the letters in the boxes shaded light blue is the cipher text according to Caesar’s Shift of 3. Therefore, to encrypt the phrase ‘HELLO’, it would look like this: ‘KHOOR’. 3 PROS & CONS The good points of the Caesar cipher is that it is very simple to use. All a person has to do is to write out his message and then referring to his cipher, rewrite his message again, now encrypted. To give the recipient the key, one can just tell them for example “move back 3″ so ‘c’ would be represented by ‘z’, and ‘d’ would be represented by ‘a’. No machines or devices are needed to decode it. A paper and pen for convenience may be all that you need. The bad points are that due to the nature of the cipher, an encrypted text has only 26 possibilities, 25 not including the given text. Within 5 minutes, an experienced cryptobreaker could crack the code. Anyone else could crack the code in 10 minutes. With the revolvable cipher, anyone could crack the code in 4-5 minutes. The key could be obtained through trial and error. This is called a Brute Force Attack. To save time a series of strips could be prepared. Each with 52 letters, the letters would be in alphabetical order twice over. The strips would be aligned so that the ciphertext read in one position. They would then be scanned to reveal the plaintext. An alternative and quicker way to guessing/trial and error is through observing the frequency of the letters. Here is a diagram representing the frequency of the letters in the alphabet. 4 For example, if a certain letter ‘z’ for example is noticed to be repeated very oftenly in the ciphertext, you could start off by guessing that ’z’ represents e, the most commonly used letter in the alphabet. Subsequently you can use this method to determine the rest of the letters. BIBLIOGRAPHY http://en.wikipedia.org/wiki/Caesar_cipher http://www.murky.org/blg/the-caesar-shift/ Chris Savarese and Brian Hart, The Caesar Cipher, 1999 F.L. Bauer, Decrypted Secrets, 2nd edition, 2000, Springer David Kahn, The Codebreakers — The Story of Secret Writing http://www.spiritus-temporis.com/caesar-cipher/history-and-usage.html http://en.wikipedia.org/wiki/ROT13 http://all.net/BOOKS/IP/cHAP2-1.HTML 5