Assignment2
advertisement

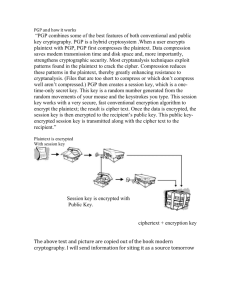
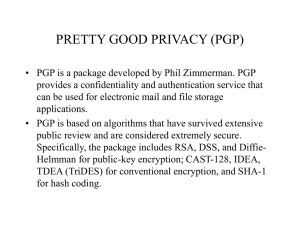
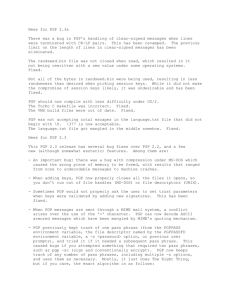
Homework#2 1. a. 48 bits keys are equal to 2^48= 281,474,976,710,656. Using the computer that can try 1,000,000Keys/Sec to get the total seconds. 281,474,976,710,656 Keys/ 1,000,000times/Sec. ≈ 281474977 Sec Convert Seconds to minutes , then to hours, then to days, and then to years 281474977/60/60 ≈ 78187 Hours 78187 H/24 ≈ 3258 Days 3258 Days /365 Days ≈ 8.9 Years It would take maximum about 8.9 years (107 months) to try all possible keys to execute a successful force attack against this cipher. On average : 8.9Years/2=4.45Years (53.4 months) b. If the first 4 digit are only ones, like 1111, then the algorithm can produce the number of keys 2^44=17,592,186,044,416 Keys Using the computer that can try 1,000,000Keys/Sec to get the total seconds. 17592186044416Keys/1,000,000Key/Sec.= 17,592,186Sec. Convert Seconds to minutes, then to hours, then to days, and then to months 17,592,186Sec/60/60/24/30=6.79 Months It would take about 6.79 months to try all possible keys to execute a successful force attack. On average: 6.79month/2≈3.4month c. (a) 64 bits keys are equal to 18446744073709551616 18446744073709551616 /1,000,000/60/60/24/365 = 584,942 Years(Maximum). On average: 58.492Years/2 = 292,471Years (b) 128 bits keys are equal to 3.4028236692093846346337460743177e+38 3.4028236692093846346337460743177e+38/1,000,000/60/60/24/365 = 10,790,283,070,806,014,188,970,529.Years (Maximum) On average: 10790283070806014188970529/2=5,395,141,535,403,007,094,485,264.5Years d. Total possible keys are 10,000*10*10,000=1,000,000,000 Keys 1,000,000,000/1,000,000Keys/Sec.=1,000Sec 1,000Sec/60Sec=16.666667 Minutes. It would take about 16.7 Min to try all available keys. On average: 16.666667/2=8.3333Minutes. 2. My original text a) Signed the messageLink b) The file encrypted for Professor Robin Burke rburke@cs.depaul.edu c) Here is my Signature for above file. d) I encrypted my Signature file and sent it to Professor Robin Burke by using Professor’s public key. Also I signed this file. Link to the file. 3. I tested the file “message.txt.asc” the test file is: Student progress will be assessed through a combination of regular homework assignments and exams. Class participation is also very important in this course and will be evaluated. These components will be weighted as follows: * Homework: 35% * Midterm: 30% * Final exam: 25% * Active class participation: 10%. c d ) I added the PGP public key into my key ring. When I verify the signature, I got message says “Invalid key” The key is signed on 9/18. The ID is OxD2A29123. The type is DH/DSS Expires: Never Cipher: IDEA e) After I altered the original message, I got “bad signature” message. 4 I tried to use PGP on shrike first, but it did not work. I installed the PGP program into my computer and tried to use its features. It is easy to install if you pick a right version for your operating system. After the message is signed, others can not make any changes. If a change has been made, the PGP will tell you that “ bad signature”. It is quite useful for protecting the original message. We can insert the PGP into the programs to ensure the security. But there is an issue. How about the license? We can not sell the program out side the North America. I like “Sing message feature” because in many case you do not want other alter your original message. If people do not have PGP in their computer, can they verify the message? I tried to find the description about this on the manual of PGP. But I did not find yet. I found this part of PGP is interesting so I copied it as following. The original source is from PGP program published by MIT. “About PGP data compression routines PGP normally compresses the plaintext before encrypting it, because it’s too late to compress the plaintext after it has been encrypted; encrypted data is not compressible. Data compression saves modem transmission time and disk space and, more importantly, strengthens cryptographic security. Most cryptanalysis techniques exploit redundancies found in the plaintext to crack the cipher. Data compression reduces this redundancy in the plaintext, thereby greatly enhancing resistance to cryptanalysis. It takes extra time to compress the plaintext, but from a security point of view it’s worth it. Files that are too short to compress, or that just don’t compress well, are not compressed by PGP. In addition, the program recognizes files produced by most popular compression programs, such as PKZIP, and does not try to compress a file that has already been compressed. For the technically curious, the program uses the freeware ZIP compression routines written by Jean-Loup Gailly, Mark Adler, and Richard B. Wales. This ZIP software uses compression algorithms that are functionally equivalent to those used by PKWare’s PKZIP 2.x. This ZIP compression software was selected for PGP mainly because it has a really good compression ratio and because it’s fast.”